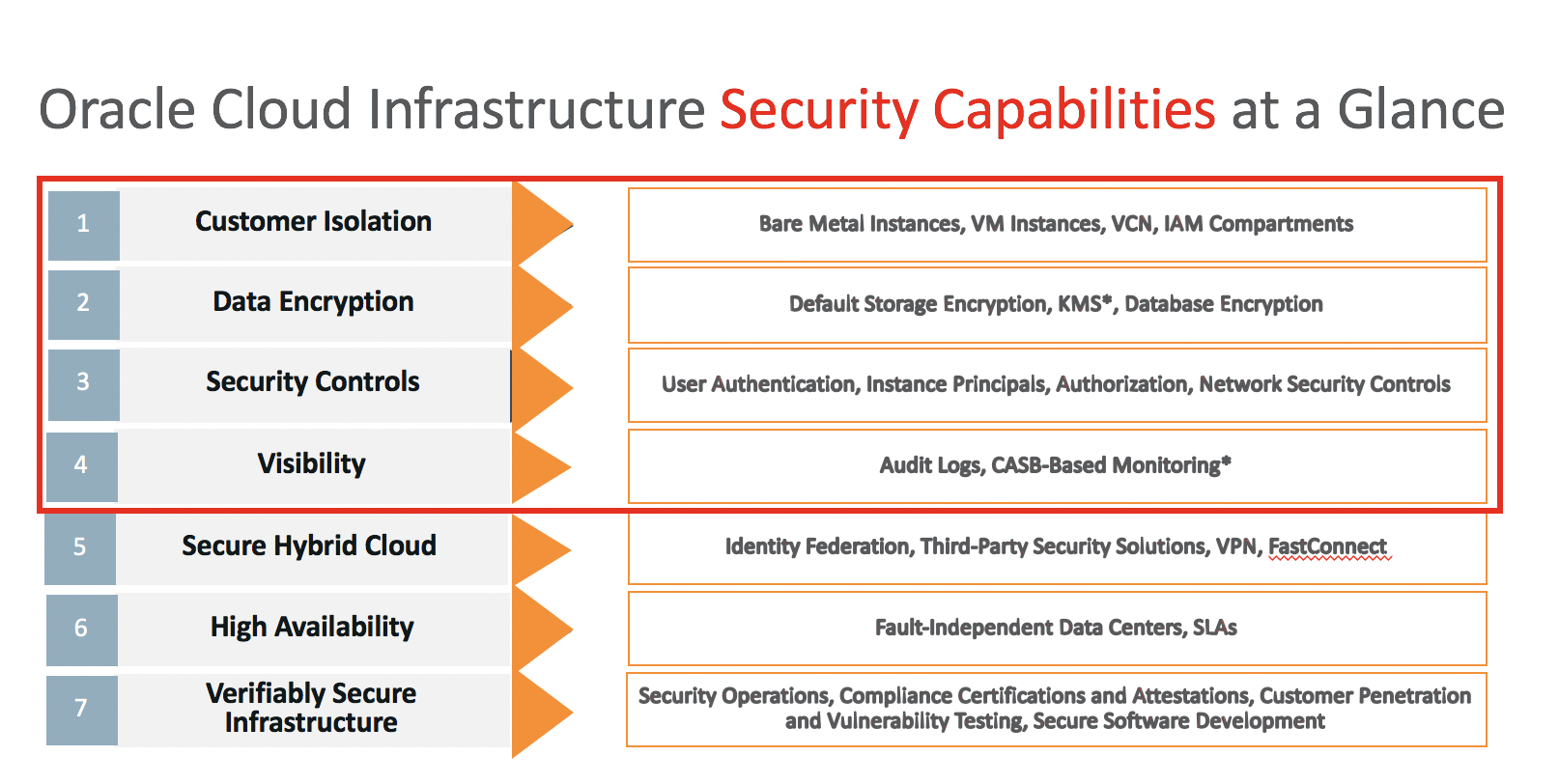
Oracle Cloud Infrastructure’s security approach is based on seven core pillars. Each pillar has multiple solutions designed to maximize the security and compliance of the platform. You can read more about Oracle Cloud Infrastructure’s security approach here.
The seven core pillars of trusted enterprise cloud platform are:
- Customer Isolation
- Data Encryption
- Security Controls
- Visibility
- Secure Hybrid Cloud
- High Availability
- Verifiably Secure Infrastructure
Oracle employs some of the world’s foremost security experts in information, database, application, infrastructure, and network security. By using Oracle Cloud Infrastructure, our customers directly benefit from Oracle’s deep expertise and continuous investments in security.
In this blog (Part 1), I am going to explain how Oracle Cloud Infrastructure security services map to our first two pillars – Customer Isolation and Data Encryption. In the next blog (Part 2), I will cover the next 2 pillars.
1. Customer Isolation
Customer isolation allows customers to deploy application and data assets in an environment that commits full isolation from other tenants and Oracle’s staff. Let’s dive into how we offer isolation at different resource levels.
Compute
At the Compute level, we offer two types of instance isolation.
- Bare metal instances offer complete workload and data isolation. Customers have full control of these instances. Every bare metal instance is a single-tenant solution. Oracle personnel have no access to memory or local storage while the instance is running, and there is no Oracle-managed hypervisor on bare metal instances.
- Virtual machine instances are a multi-tenant solution. VM instances run on an Oracle-managed hypervisor and come with strong isolation controls.
Both instances offer strong security controls. Customers who want to have higher performance instances and complete workload and data isolation often prefer bare metal instances.
Networking
Next, the Oracle Cloud Infrastructure Networking service offers a customizable private network (a VCN, or virtual cloud network) to customers. VCNs enforce the logical isolation of a customer’s Oracle Cloud Infrastructure resources.
Oracle’s VCN gives you the complete set of network services you need in the cloud with the same network flexibility you have today on-premises.
- You can build an isolated virtual network with granular controls, including subnets and security lists.
- We provide secure and dedicated connectivity from your data center to the cloud through FastConnect with multiple providers like Equinix and Megaport.
- You can provide end-customers high performance and predictable access to your applications with services like provisioned bandwidth load balancing.
- All networking services are API-driven and programmable for more automated management and application control.
As with an on-premises network in a data center, customers can set up a VCN with hosts and private IP addresses, subnets, route tables, and gateways using VCN. The VCN can be configured for internet connectivity using an Internet Gateway, or connected to the customer’s private data center through an IPSec VPN gateway or FastConnect. FastConnect offers a private connection between an existing network’s edge router and dynamic routing gateways. In this case, traffic does not traverse the internet.
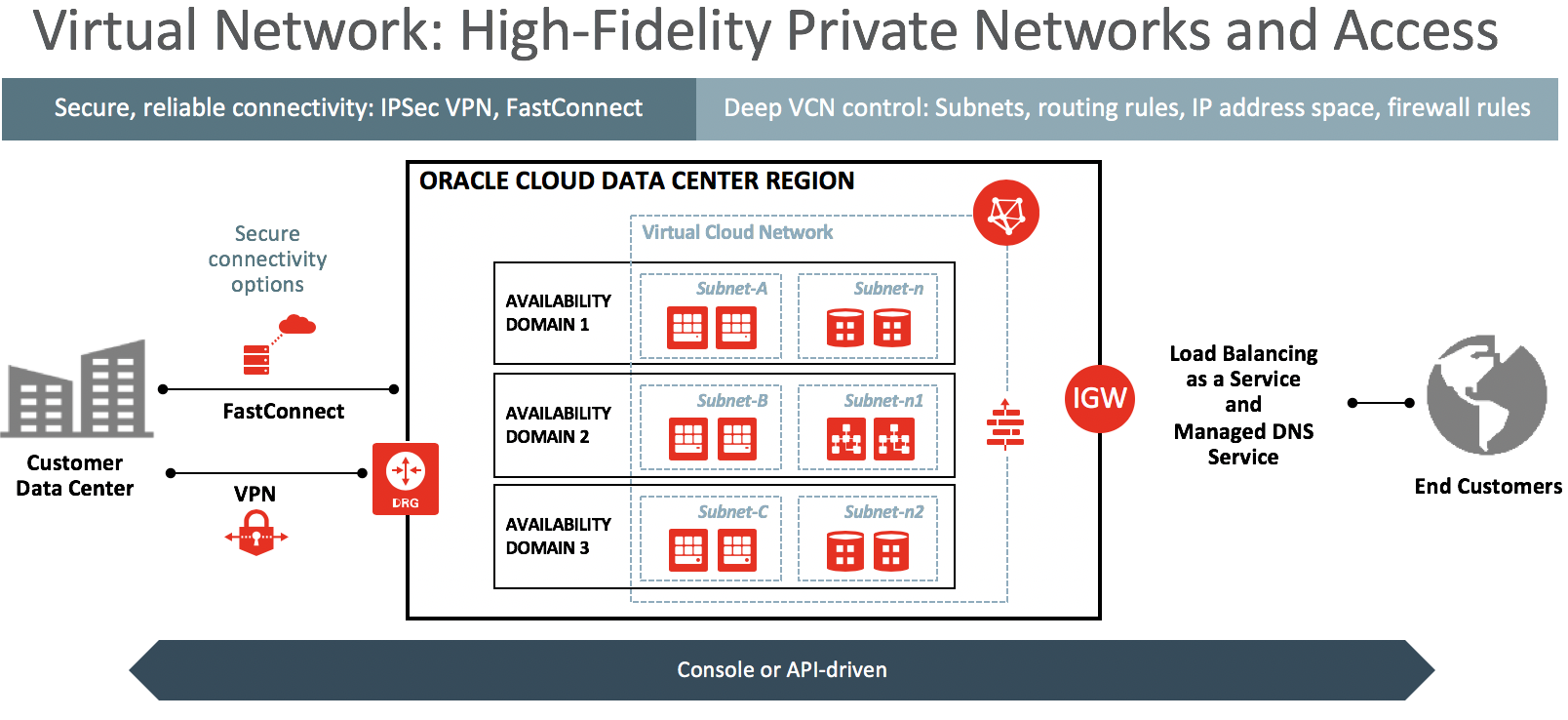
Subnets, the primary subdivision of a VCN, are specific to an availability domain. They can be marked as private upon creation, which prevents instances launched in that subnet from having public IP addresses.

Compartments and Policies
From an authorization perspective, Identity and Access Management (IAM) compartments can be used for isolation. A compartment is a heterogeneous collection of resources for the purposes of security isolation and access control.
All end-user calls to access Oracle Cloud Infrastructure resources are first authenticated by the IAM service and then authorized based on IAM policies. A customer can create a policy that gives a specific set of users permission to access the infrastructure resources (network, compute, storage, and so on) within a compartment in the tenancy. These policies are flexible and are written in a human-readable form that is easy to understand and audit. The easy-to-understand syntax include verbs which define the level of access given to end-users.
2. Data Encryption
Our second core security pillar, data encryption protects customer data at-rest and in-transit in a way that allows customers to meet security and compliance requirements with respect to cryptographic algorithms and key management.
Block Volume Encryption
The Oracle Cloud Infrastructure Block Volumes service provides persistent storage that can be attached to compute instances using the iSCSI protocol. The volumes are stored in high-performance network storage and support automated backup and snapshot capabilities. Volumes and their backups are accessible only from within a customer’s VCN and are encrypted at-rest using unique keys. For additional security, iSCSI CHAP authentication can be required on a per-volume basis.
Object Storage Encryption
The Oracle Cloud Infrastructure Object Storage service provides highly scalable, strongly consistent, and durable storage for objects; ideal for media archives, data lakes, and data protection applications like backup and restore. API calls over HTTPS provide high-throughput access to data. All objects are encrypted at rest using unique keys. Objects are organized by bucket, and, by default, access to buckets and objects within them requires authentication. Users can use IAM security policies to grant users and groups access privileges to buckets. To allow bucket access by users who do not have IAM credentials, the bucket owner (or a user with necessary privileges) can create pre-authenticated requests that allow authorized actions on buckets or objects for a specified duration.
Alternately, buckets can be made public, which allows unauthenticated and anonymous access. Given the security risk of inadvertent information disclosure, Oracle highly recommends carefully considering the business case for making buckets public. Object Storage enables you to verify that an object was not unintentionally corrupted by allowing an MD5 hash to be sent with the object (or with each part, for multipart uploads) and returned upon successful upload. This hash can be used to validate the integrity of the object.
In addition to a native API, the Object Storage service supports Amazon S3 compatible APIs. Using the Amazon S3 Compatibility API, customers can continue to use existing S3 tools (for example, SDK clients). Partners can also modify their applications to work with Object Storage with minimal changes to their applications. Their native API can co-exist with the Amazon S3 Compatibility API, which supports CRUD operations. Before customers can use the Amazon S3 Compatibility API, they must create an S3 Compatibility API key. After generating the necessary key, customers can use the Amazon S3 Compatibility API to access Object Storage in Oracle Cloud Infrastructure.
Key Management Service
In addition, Oracle provides an enterprise-grade Key Management service with following characteristics:
- Backed by FIPS 140-2 Level 3 HSMs
- Tightly integrated with Oracle Block Volumes and Object Storage
- Full control of key creation and lifecycle (with automatic rotation options)
- Full audit of key usage (with signed attestation by HSM vendor)
- Choice of key shape via Advanced Encryption Standard (AES) keys with three key lengths: AES-128, AES-192, and AES-256
Load Balancer
For data at-transit, applications should use TLS-based certificates and encryption. Oracle IaaS load balancer services support customer-provided TLS certificates.
In addition, the Load Balancing service supports TLS 1.2 by default, and prioritizes the following forward-secrecy ciphers in the TLS cipher-suite:
- ECDHE-RSA-AES256-GCM-SHA384
- ECDHE-RSA-AES256-SHA384
- ECDHE-RSA-AES128-GCM-SHA256
- ECDHE-RSA-AES128-SHA256
- DHE-RSA-AES256-GCM-SHA384
- DHE-RSA-AES256-SHA256
- DHE-RSA-AES128-GCM-SHA256
- DHE-RSA-AES128-SHA256
Many customers prefer EC cipher suites due to high performance. However, customers can add weaker cipher suites changes via a support ticket if their legacy clients need them.

Database Encryption
Database encryption is achieved by using Transparent Data Encryption (TDE).
In the second part, I will cover the next 2 pillars. In the meantime, please use these resources to learn more about Oracle Cloud Infrastructure Security:
• Oracle Cloud Infrastructure Security White Paper
• Oracle Cloud Infrastructure GDPR White Paper
• Oracle Cloud Infrastructure Security Best Practices Guide
• Services Security Documentation
Blogs:
- Guidance for PCI Compliance
- Guidance for cSOC
- Guidance for Security Checklist for Application Migration
- Guidance for third party firewall installation on Oracle Cloud Infrastructure – Checkpoint, vSRX
- Guidance for IAM configuration for MSPs
- Guidance for IAM Best Practices
- Guidance for Migration and DR using Rackware
