Although Oracle Cloud Infrastructure includes firewall capabilities, some customers prefer to run their own custom firewalls. This post describes how to deploy vSRX Virtual Firewall, a Juniper virtual security appliance that provides security and networking services for virtualized private or public cloud environments.
In a public cloud environment, vSRX provide benefits like stateful firewall protection, and application and content security features like IPS, antivirus, web filtering, and antispam.
This post covers the following topics:
- Configuring Oracle Cloud Infrastructure for vSRX
- Launching a vSRX instance in a virtual cloud network (VCN)
- Configuring vSRX
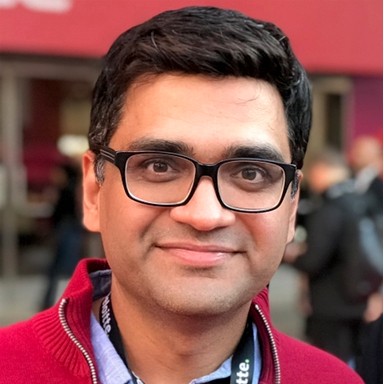
Configuration Diagram
The following diagram shows a high-level architecture of the proposed setup: 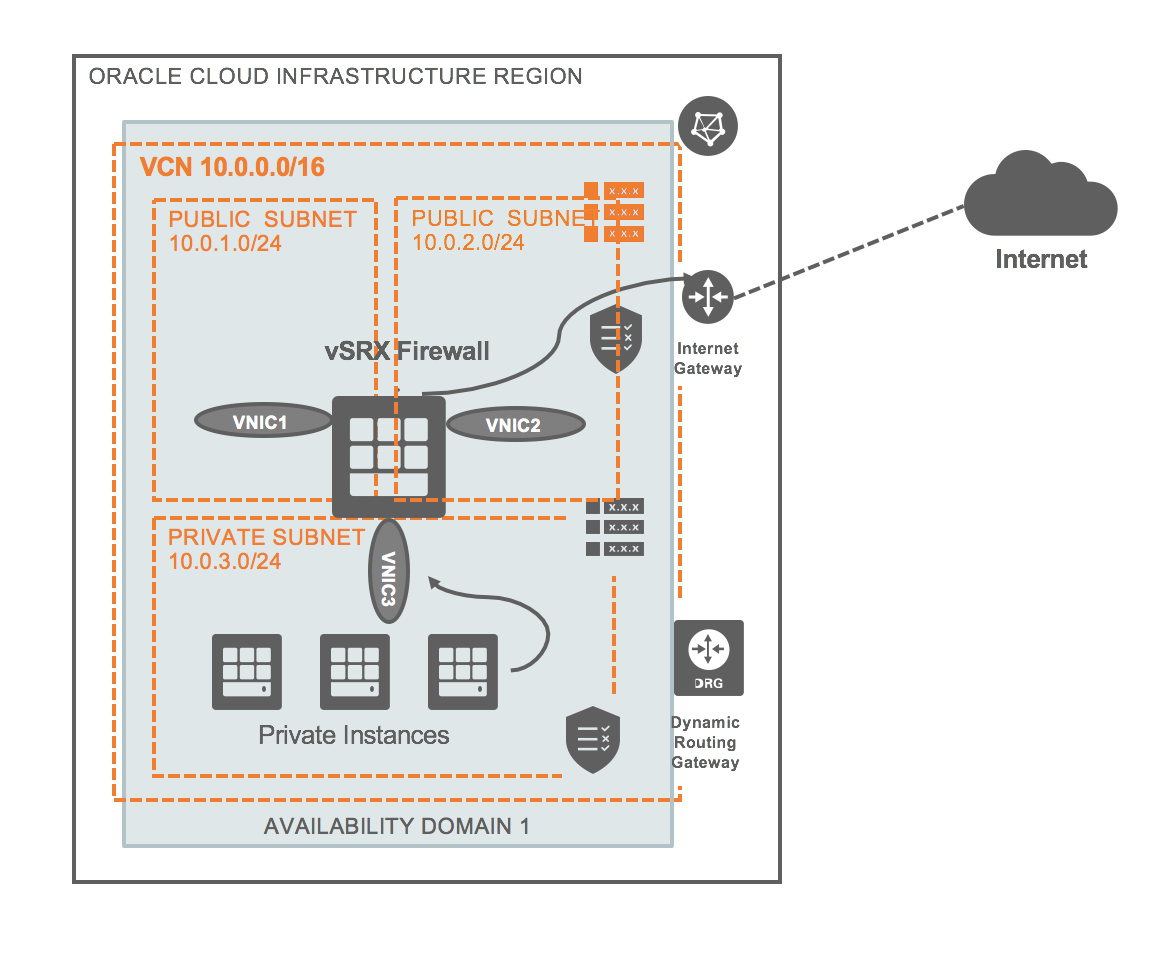
The diagram shows a VCN with three subnets:
-
Public (10.0.1.0/24), for management interfaces with access to the internet through an internet gateway
-
Public (10.0.2.0/24), for revenue (data) interfaces with access to the internet through an internet gateway
-
Private (10.0.3.0/24), a private subnet with no access to the internet
1. Configuring Oracle Cloud Infrastructure for vSRX
The following procedures outline how to create and prepare an Oracle Cloud Infrastructure VCN for vSRX.
Create a VCN
In the Oracle Cloud Infrastructure Console, create a VCN without any resources. The VCN will have a default empty route table, a default security list, and DHCP options. In this example, the VCN is called DataCenter-1.
For information about how to create a VCN, see the VCN Overview and Deployment Guide.
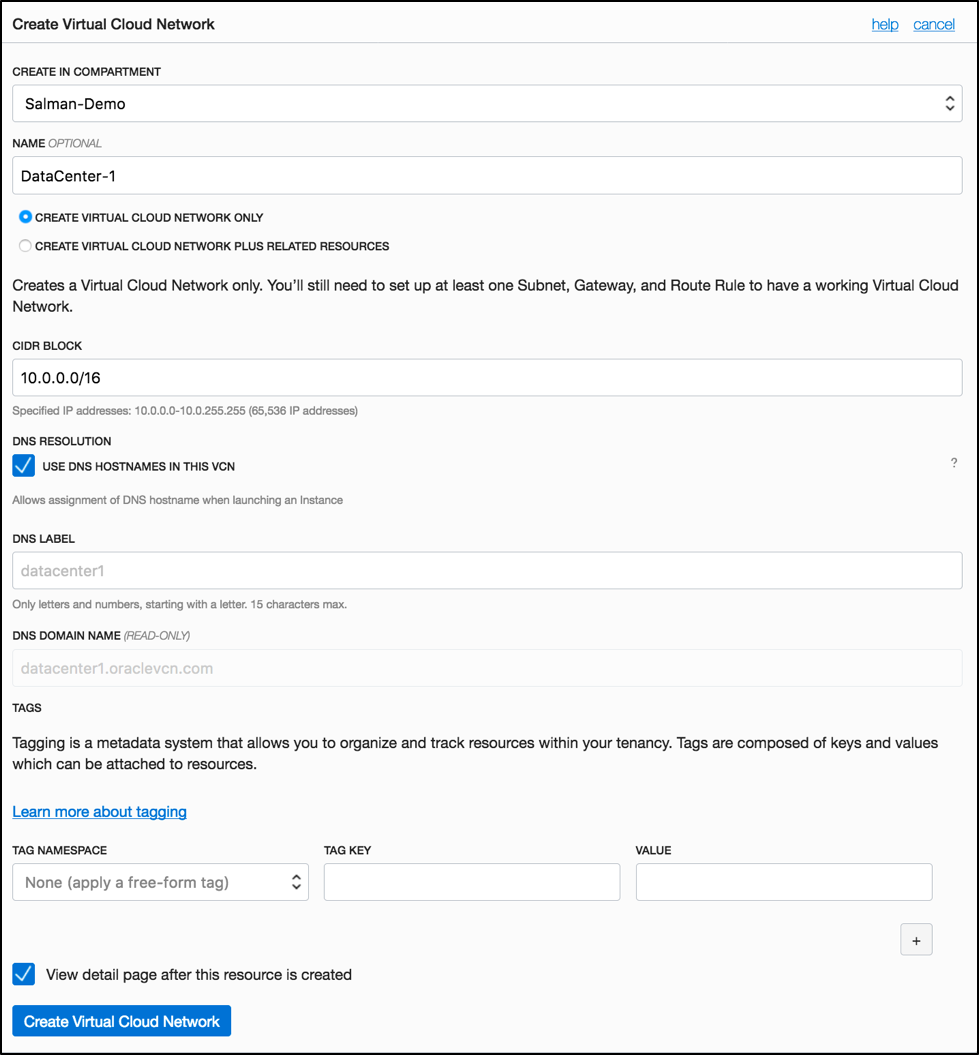
Create an internet gateway and assign it the name IGW.
Create Subnets for vSRX
vSRX requires two public subnets and one or more private subnets for each individual instance group. One public subnet is for the management interface (fxp0), and the other is for a revenue (data) interface. The private subnets, connected to the other vSRX interfaces, ensure that all traffic between applications on the private subnets and the internet must pass through the vSRX instance.
Configure the Public Subnet (Management Interface)
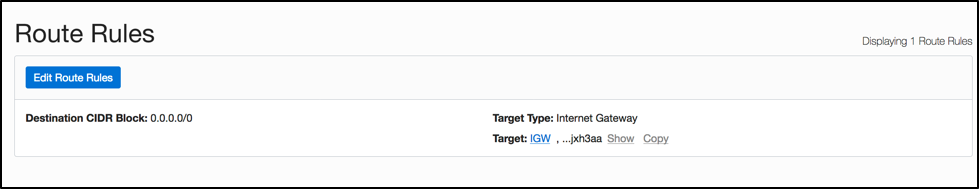
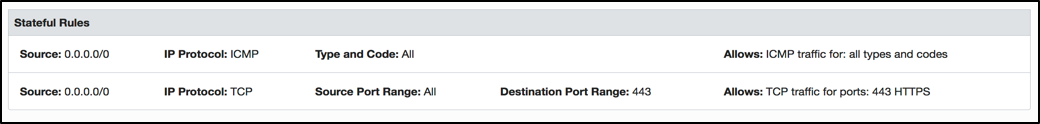
Create this public subnet, and define a route rule for the route table Default Route Table in which the internet gateway is configured as the route target for all traffic (0.0.0.0/0). For details about how to create subnets, see VCNs and Subnets.
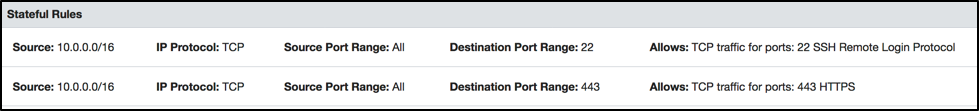
For the subnet’s security list Default Security List, create an egress rule to allow traffic to all destinations. Create ingress rules that allow access on TCP port 22 from the public internet and on TCP port 80/443 for accessing the web application from the public internet.
Configure the Public Subnet (Revenue Interface)
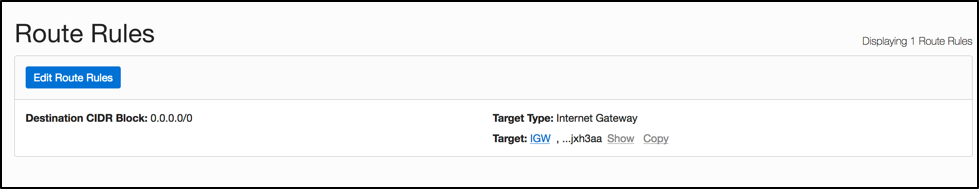
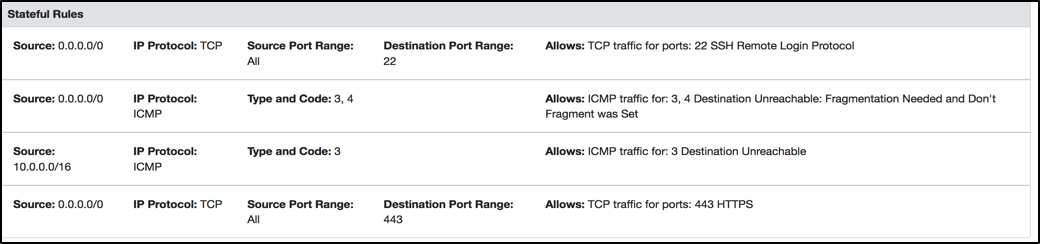
Create this public subnet, and define a route rule for the route table Public RT in which the internet gateway is configured as the route target for all traffic (0.0.0.0/0).
For the subnet’s security list Public Subnet SL, create an egress rule to allow traffic to all destinations. Create ingress rules that allow access on TCP port 80/443 for accessing the web application from the public internet and on ICMP if needed to check the connectivity.
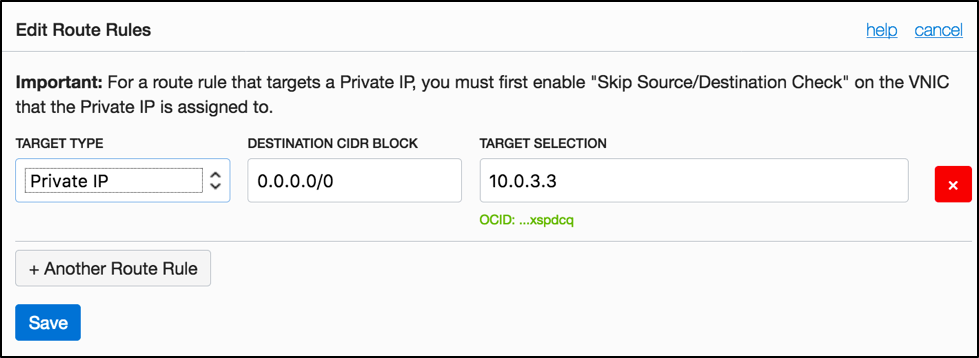
Configure the Private Subnet
Create this private subnet, and define a route rule for the route table Private RT in which the vSRX second vNIC’s private IP address (10.0.3.3) is configured as the route target for all traffic 0.0.0.0/0.
Note: Configure the route rule after you create and attach the secondary VNICs.
For the subnet’s security list Private Subnet SL , create an egress rule to allow traffic to all destinations. Create ingress rules that allow only specific address ranges (like an on-premises network or any other private subnets in the VCN).
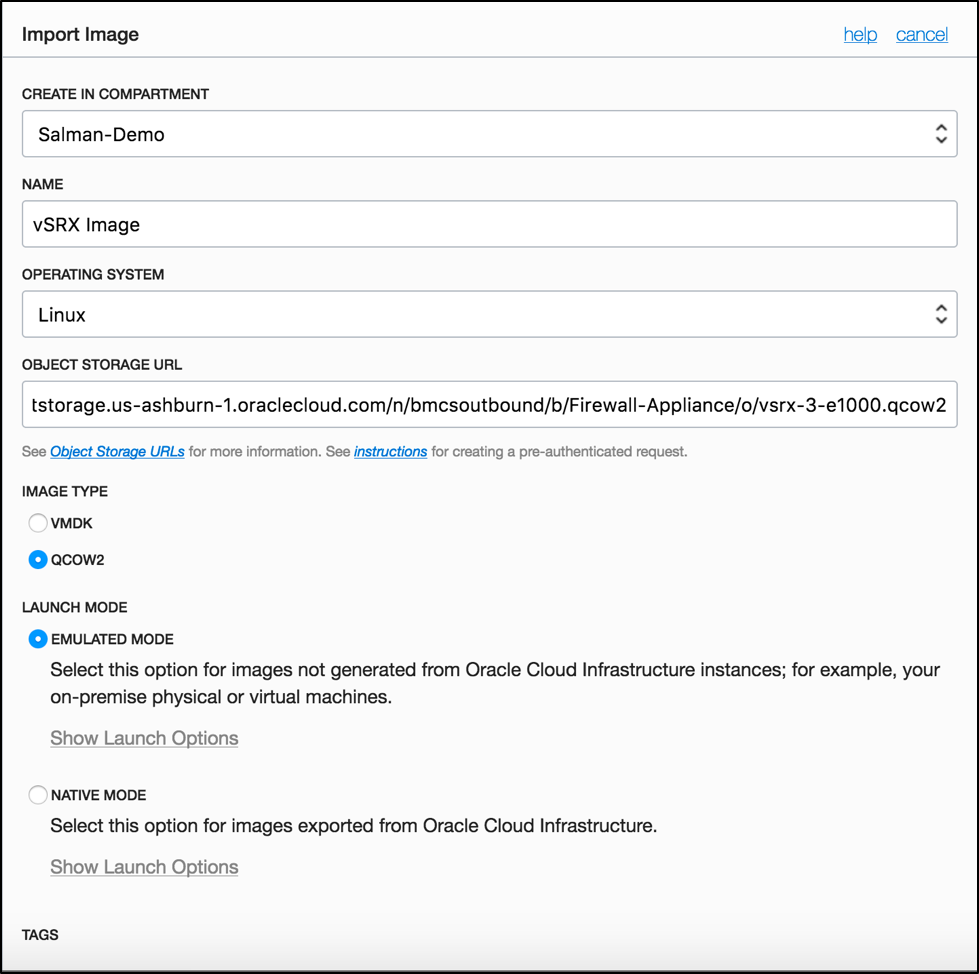
Import the Image by Using the Console
The next step is to upload the vSRX image file to Oracle Cloud Infrastructure Object Storage and import the image by using the Console. For information about how to import custom images, see the Deploying Custom Operating System Images white paper.
2. Launching a vSRX Instance in a VCN
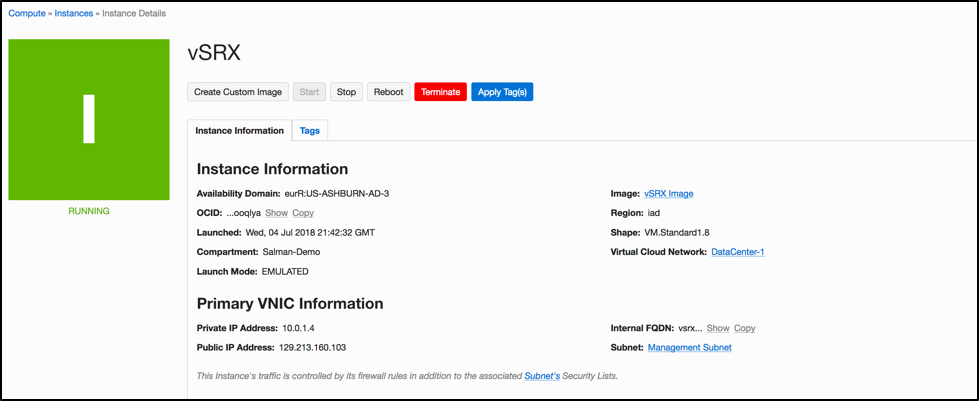
Launch the vSRX instance in the management subnet (public subnet). This example uses the VM.Standard1.8 shape. For details, see Launching an Instance.
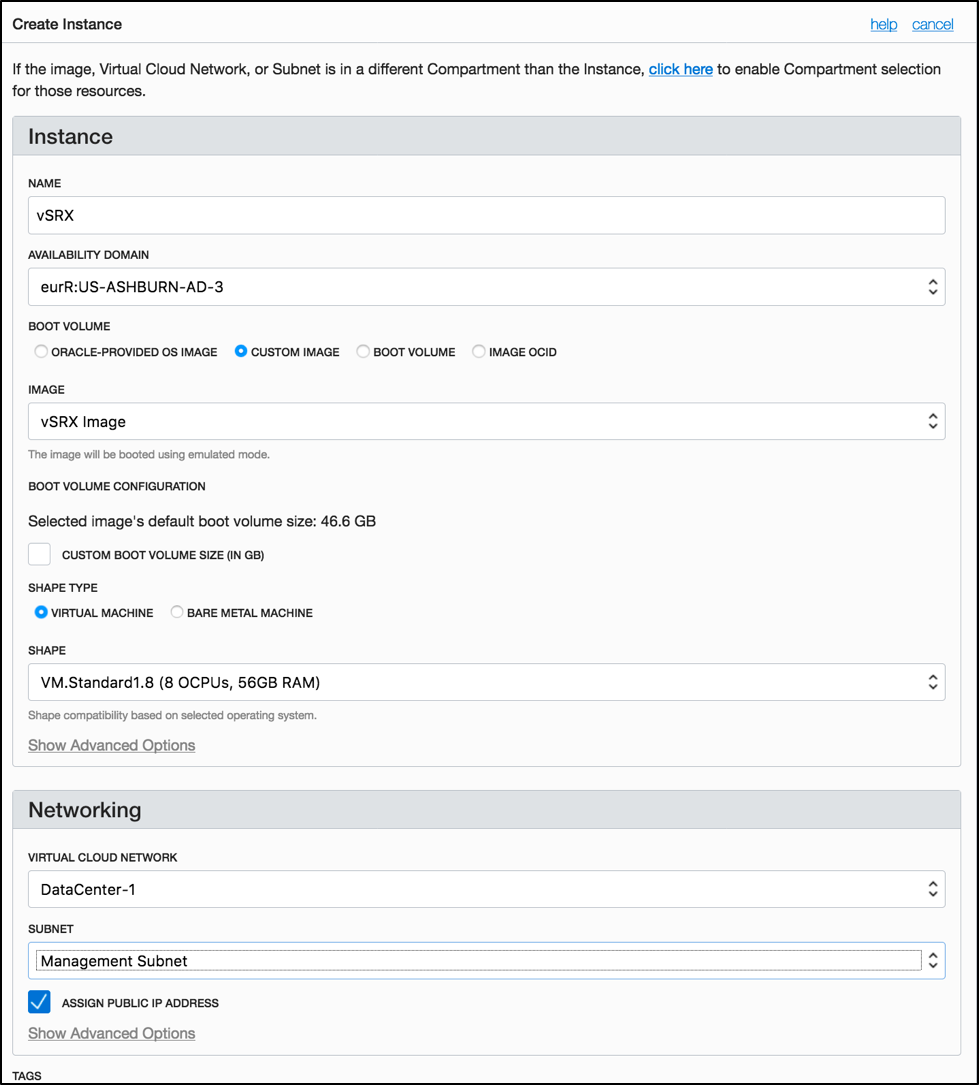
After the instance is provisioned, details about it appear in the Instance list.
Create and Attach Secondary VNICs
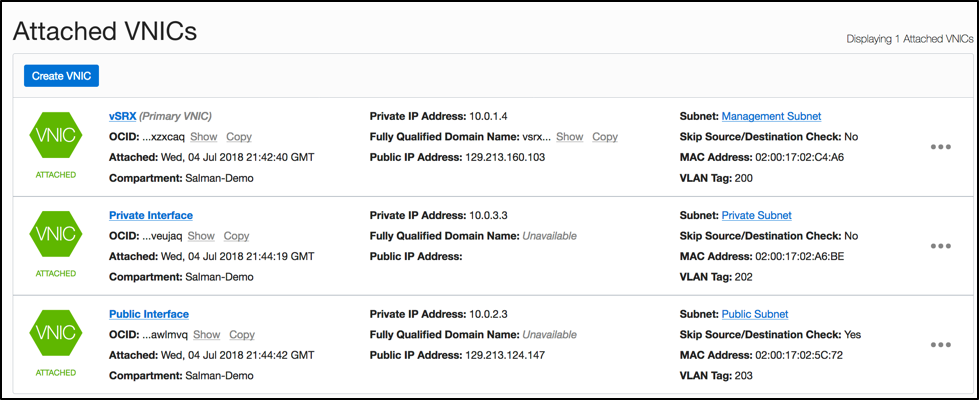
Create two VNICs. Deploy one in the public subnet (revenue data interface), and the other in the private subnet. For details about how to create and attach a VNIC, see Virtual Network Interface Cards (VNICs).
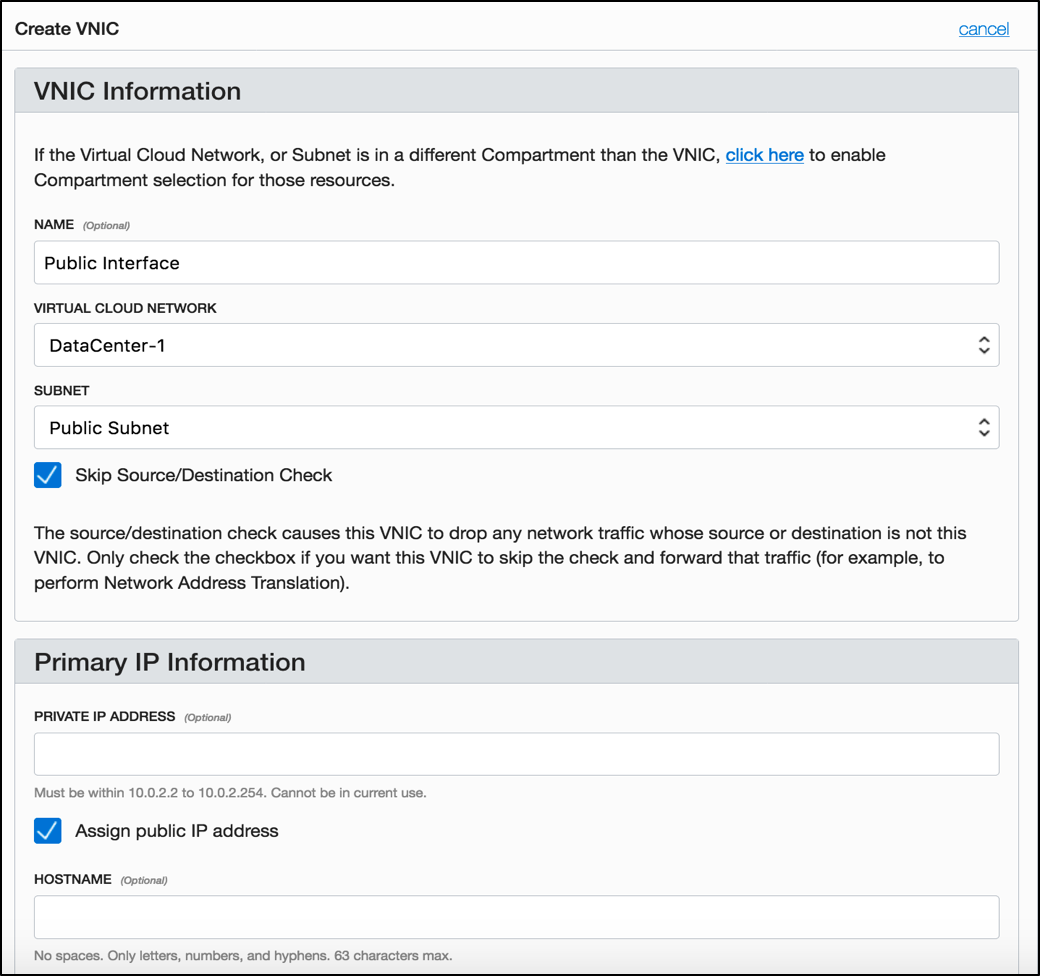
After the VNIC is created and attached, details about it appear in the VNICs list.
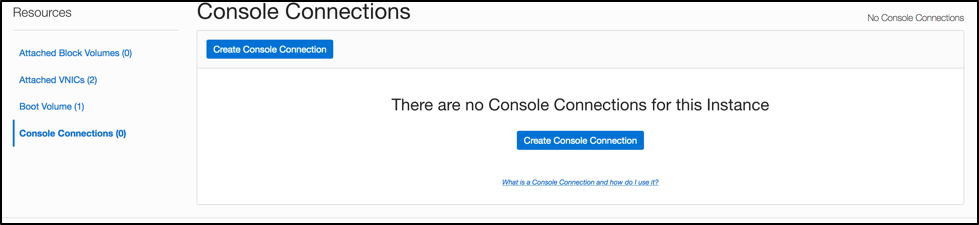
Create a Console Connection
To access the vSRX instance, create a console connection. For more information, see Instance Console Connections.
3. Configuring vSRX
Through the Console connection, connect to the vSRX instance.
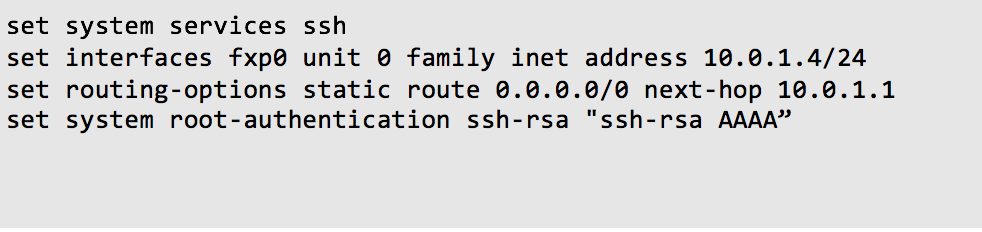
Configure the management interface, the SSH password, and the SSH RSA key, and enable root authentication:
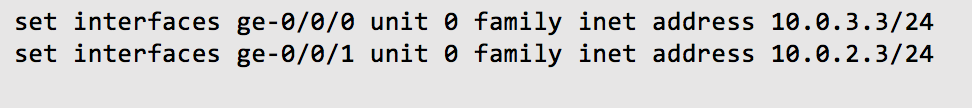
Assign IP addresses to the revenue public and private interfaces that you created using VNICs:
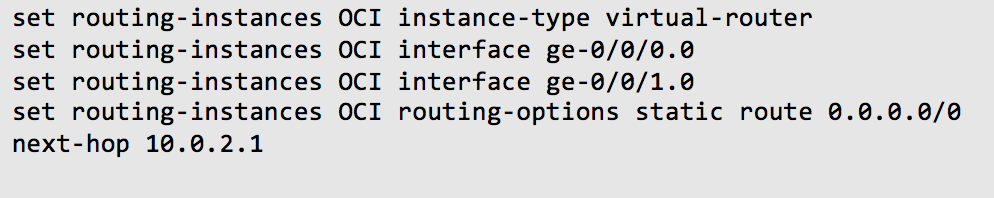
Configure routing to add a separate virtual router and routing option for the public and private interfaces.
Note: We recommend putting the revenue (data) interfaces in routing instances to avoid asymmetric traffic/routing.
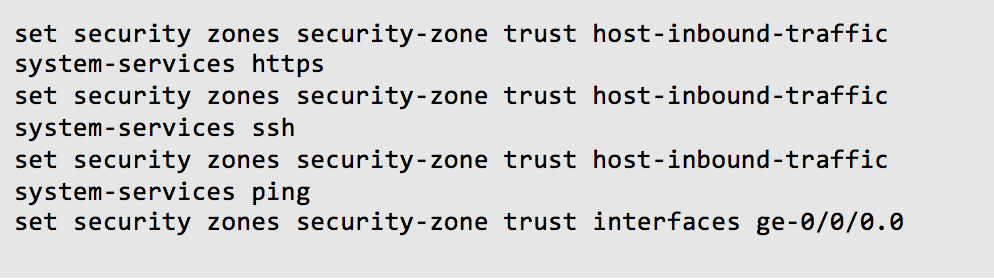
Set up the trust zone, and configure the revenue private interface in the trust zone:
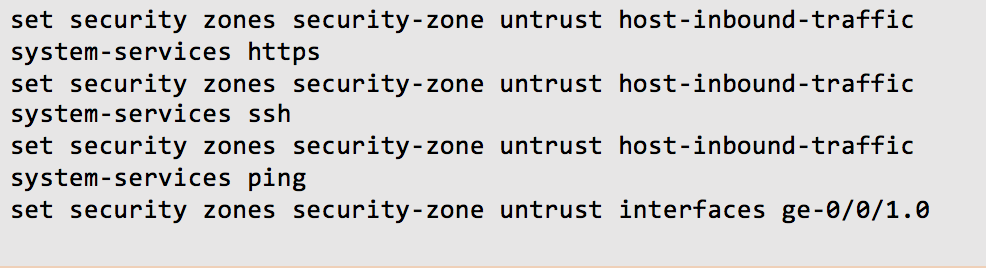
Set up the untrust zone, and configure the revenue public interface in the untrust zone.
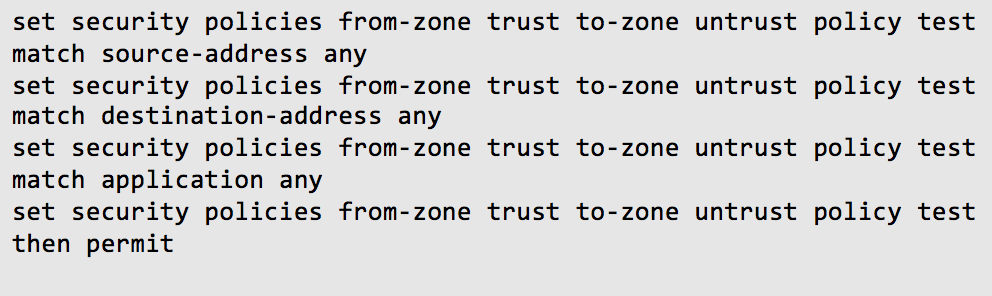
Set up security policies:
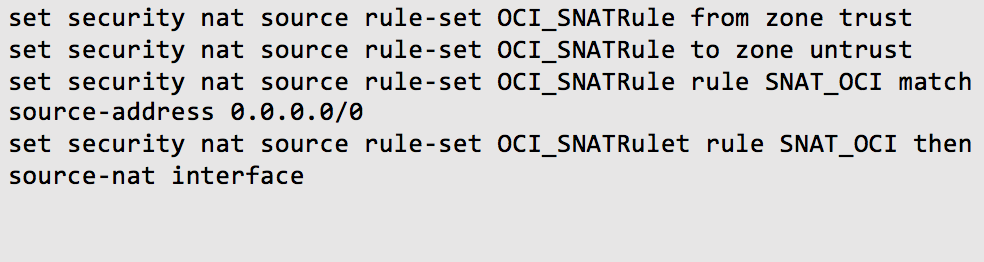
Configure NAT:
Verification
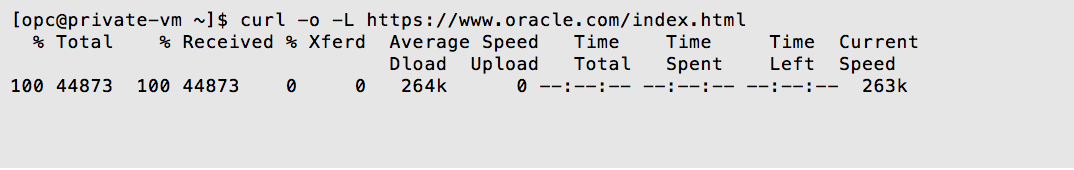
Launch a host instance by using any operating system in the private subnet. It can connect to the internet without a public IP address assigned, and no connections originated on the internet are possible directly to your server.
For more information about vSRX, see the Juniper website.
Conclusion
This post explained how to launch a virtual firewall appliance on Oracle Cloud Infrastructure that can provide you benefits such as antivirus, web filtering, and antispam.