Establishing a security operations center (SOC) is one of the primary requirements for managing cybersecurity-related risks in the current information age. This post provides general DIY guidance for building a SOC primarily for Oracle Cloud, including both platform-as-a-service and infrastructure-as-a-service offerings. This general guidance is also applicable to hybrid cloud environments.
As more businesses are relying on interconnected technologies, like IoT sensors and cloud-based platforms, it’s becoming unmanageable to respond to cyberthreats and resulting incidents without having proper visibility across the cyberthreat landscape. So it’s an imperative for enterprise information security organizations to build (in-house or outsourced) a cloud-centric SOC (cSOC) to address the following broad types of cyberthreats, based on HarvardX’s categorization:
- Unintentional external threats
- Malicious external threats
- Malicious internal threats
- Unintentional internal threats
| Internal Actors | External Actors |
|---|---|
| Unintentional Threats: Regular usage of systems by internal employees may result in discovering bugs or exploits hitherto unknown. These are always leveraged by the internal security teams to remediate the issues. | Unintentional Threats: Regular usage of systems by external agencies may result in discovering bugs or exploits hitherto unknown. This may result in loss of reputation and loss of revenue. |
| Malicious Threats: Internal agencies like employees, contractors or vendors having privileged access intentionally targets internal systems for information theft, financial gains and / or for pure malevolence. | Malicious Threats: External agencies like individuals, cyber criminals or enemy nation states intentionally targets corporations for information theft, financial gains and wide range disruptions. |
Outsourced or In-House
First, let’s tackle the issue of building a cSOC. The question is whether to outsource the SOC functionality to a managed security service provider (MSSP) or to have the functionalities in-house. From experience and some research, following are the disadvantages of outsourcing:
- Not aligned with the enterprise’s business vertical
- Limited services and capabilities
- Systems optimized for scaling across a large number of customers
- Lacks intimate knowledge because of the large number of customers
- Lack of dedicated resources
- Focused on maximizing profit
- Provides standard security services, not customized ones
- Lack of specialization
- Short lifespan of outsourced threat intelligence
- Minimal opportunities for correlation unless all data is sent to the MSSP
Following are the advantages of employing an MSSP:
- Potential cost savings (building a cSOC is expensive)
- Fully trained and qualified stuff
- Experiences in handling stressful situations
- Experience in addressing all types of security incidents effectively and efficiently
- Keeps the organization current on emerging threats (threat Intelligence)
- Wide industry experience
- Helps an organization to focus on core business
- 24x7x365 availability
- Provides an SLA
- Maintains and updates runbooks
- Automates and maintains incident response playbooks
cSOC Components
To build a cSOC or to take the service from an MSSP, ensure that the following components are in place:
- Command center
- Environment security monitoring
- Incident response
- Threat intelligence
- Forensics
- Environment assessment and verifiability
The rest of this post briefly describes these components.
Command Center
The following diagram depicts the relationships between the command center and other internal or external agencies or services:
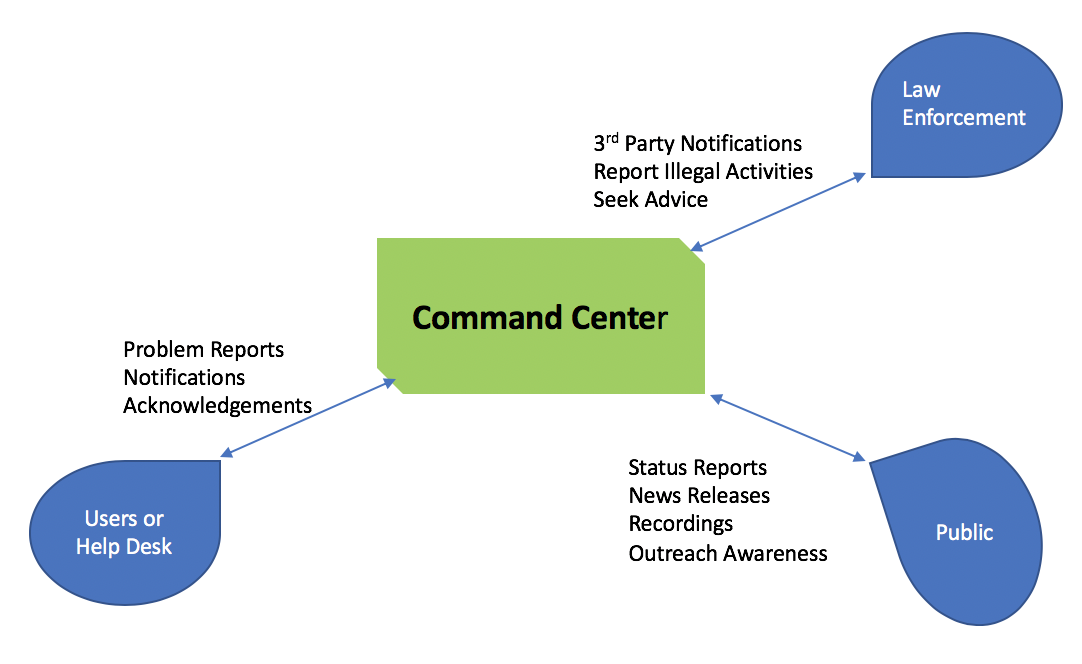
Oracle Management Cloud (OMC) with custom dashboard capabilities, makes perfect sense for the cSOC Command Center tooling for Oracle Cloud IaaS.
Following additional components of OMC are targeted towards SOC:
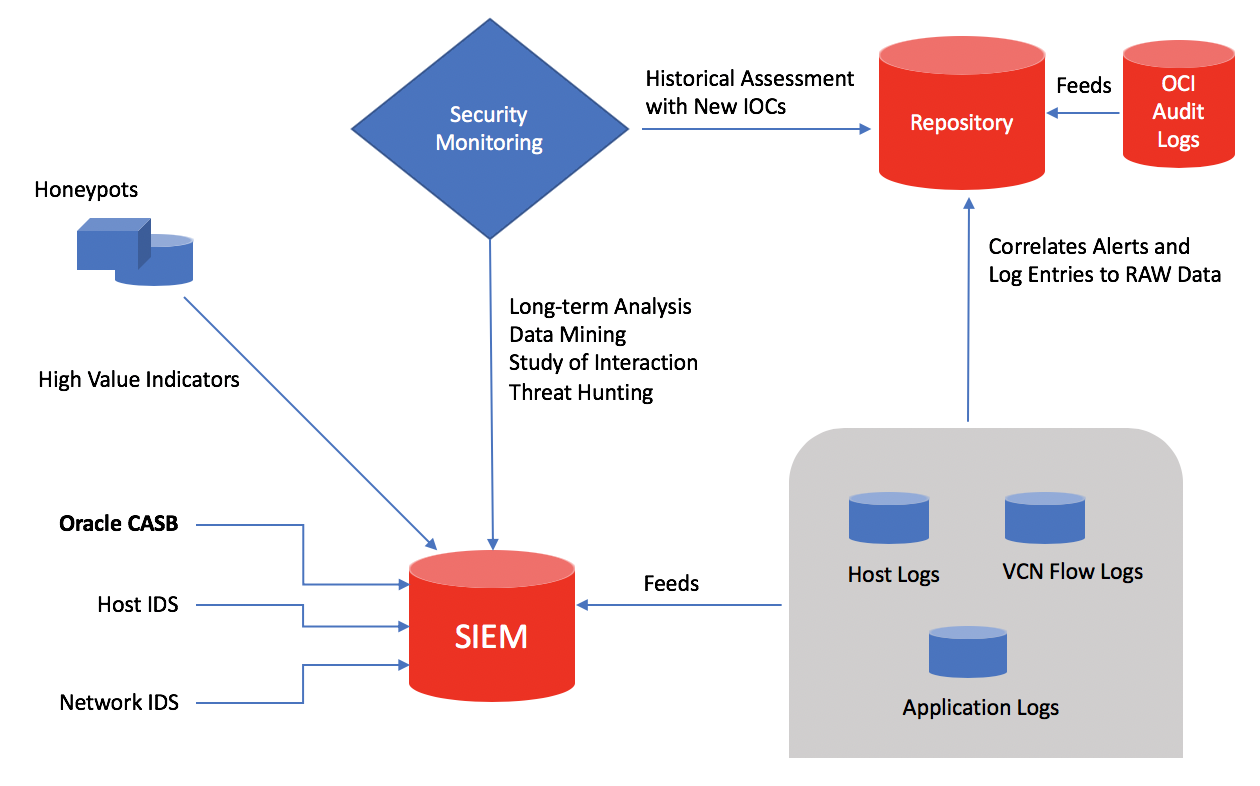
Environment Security Monitoring
Environment security monitoring should have the following components:
- Oracle Cloud Access Security Broker services
- Network logs (Oracle Cloud Infrastructure VCN flow logs)
- Host logs
- Application logs
- Network IDS
- Host IDS
- Malware detection feeds
- Security information and event management (SIEM)
- IOC (indicators of compromises) comparing tool
- Honeypots (optional)
The following diagram depicts the relationships among these components
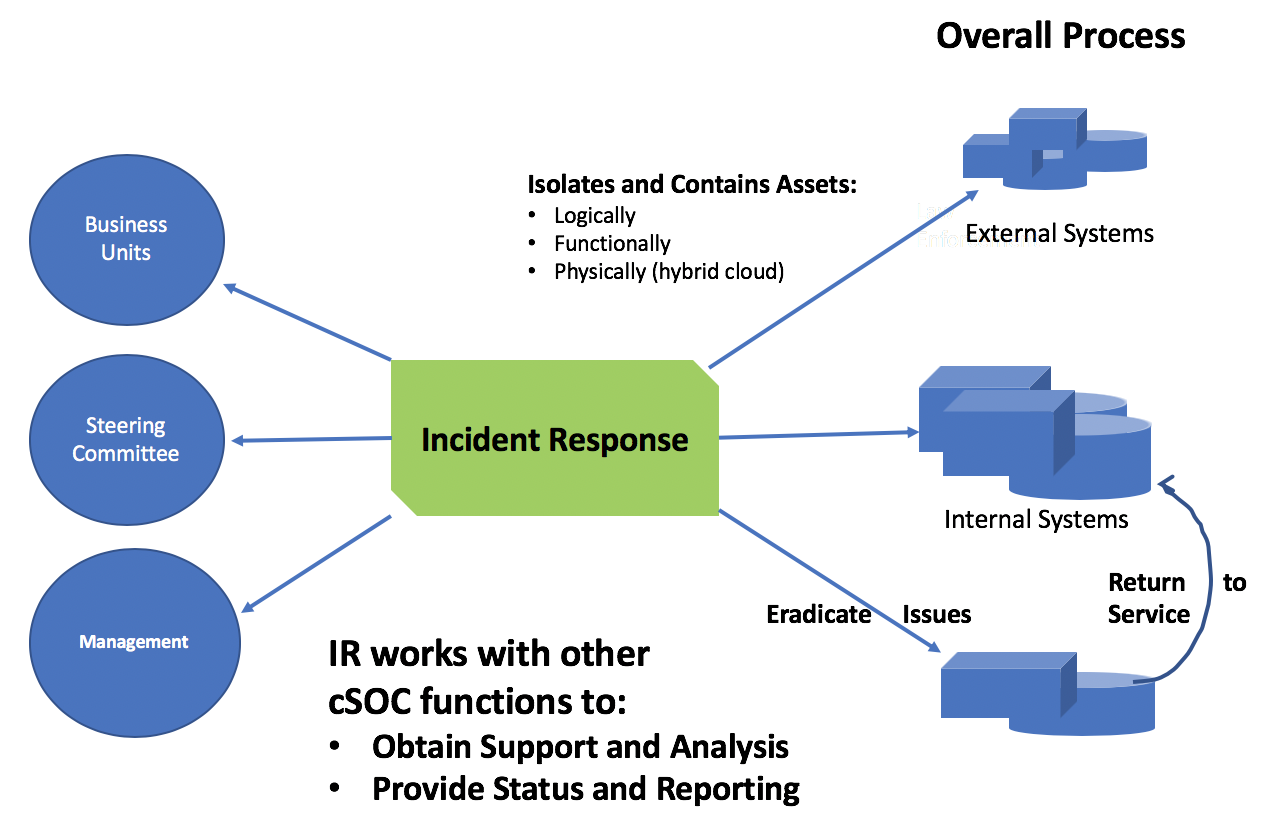
Incident Response
Incident response (IR) is the central part of the cSOC. The IR team interacts with the business units, steering committees, and management while responding to a security incident by eradicating issues so that the affected system can return to service.
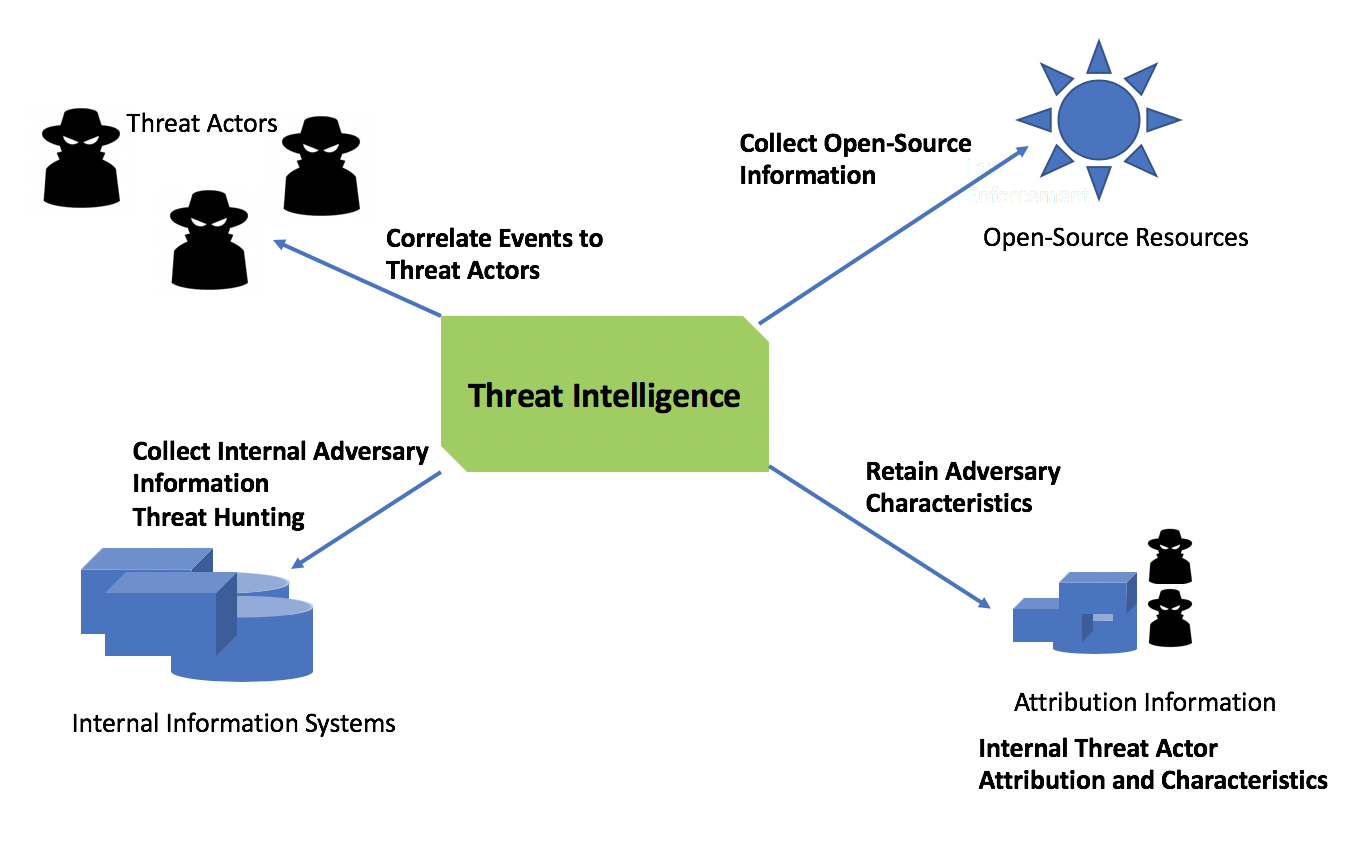
Threat Intelligence
The threat intelligence component comprises the following functions and process:
- Internal information systems
- Threat actors
- Open-source resources (Oracle’s approach)
- Attribution information
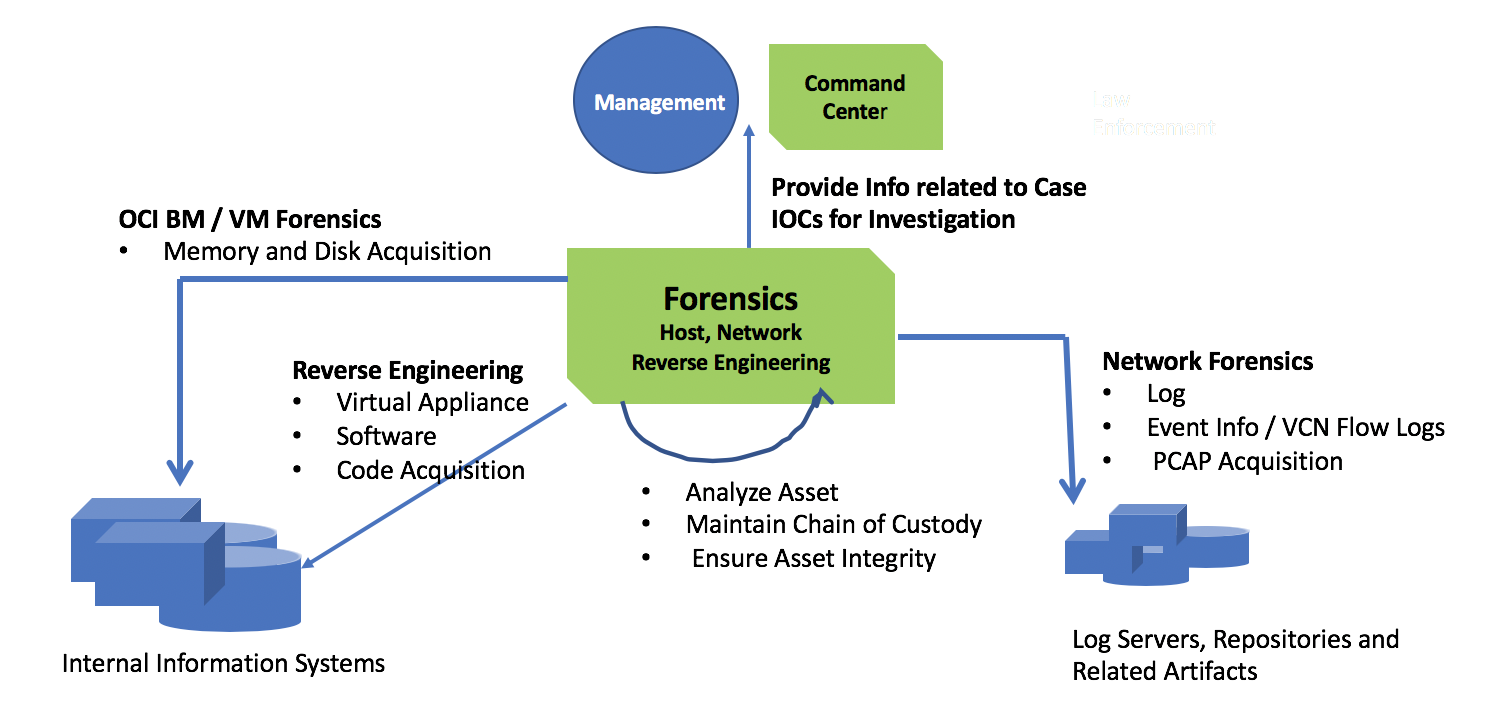
Forensics
Cloud systems forensics can be carried out internally by the cSOC or can be further outsourced. For the purpose of this post, I am showing the relationship between the components within the cSOC.
The main forensics processes are as follows:
- Host forensics
- Reverse engineering
- Network forensics
- Communication with management and the command center
- Maintaining the chain of custody
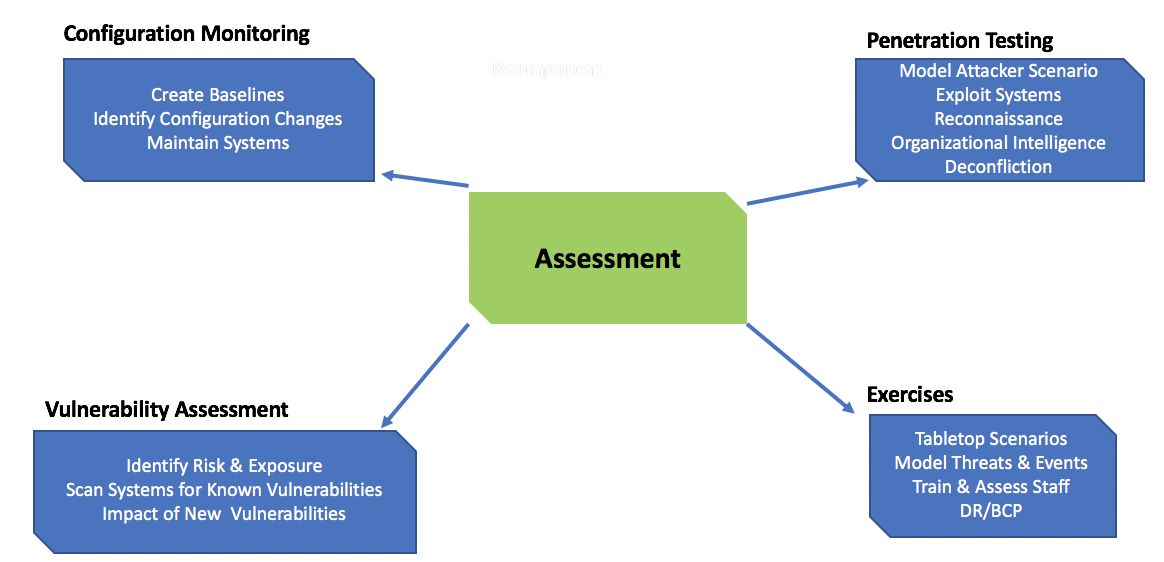
Environment Assessment and Verifiability
This component used to be the most ignored aspect in the traditional SOC. With the advent of cSOCs, this component is the pattern that connects a cSOC to the agile DevSecOps practice. The subcomponents, such as penetration testing and vulnerability assessment, can be integrated as an on-demand service with the organization’s CI/CD pipeline.
I hope that this short, visuals-heavy post will help you to establish your cloud security operations center.
For more helpful information, see the following resources:
- MGT517: Managing Security Operation: Detection, Response and Intelligence
- PCI Compliance on Oracle Cloud Infrastructure blog post
- Oracle Cloud Infrastructure Security white paper
Disclaimer: All diagrams / visuals were created using PowerPoint and no shapes were harmed (sic).
