Almost every major enterprise is considering, or in the process of, moving their sensitive workloads to the cloud.
Within the next 18 months, the amount of enterprise workloads running on the cloud will surpass those living on premises for the first time ever, according to IDG, increasing from 47% to a whopping 69%. This means the internet will be part of the enterprise network.
To be completely confident about this “new network,” enterprises need to have complete visibility into the internet — or at least the portion through which their messages pass. The internet is a core component of the cloud’s physical infrastructure, with its own nuances around reliability, performance, volatility, and security issues. You can’t really fix how the overall internet behaves, but you should be aware of these nuances and how they affect your network.
When enterprises built their networks, they always assumed that everything inside the firewall was secure, controlled, monitored, measured, and metered, and that the entire network was visible all the time.
But when sales, marketing, and support organizations tried to move their applications to the cloud, more often than not, IT had neither the inclination nor the bandwidth to support them. This gave birth to the shadow IT concept. Those organizations had money but no patience or time to waste, waiting for the enterprise IT department to come around. They tried to replicate corporate security, compliance, and privacy standards the best that they could.
Today, with the need for faster innovation, combined with the cost, scalability, and availability benefits of the cloud, enterprises are building cloud native applications that are either cloud-first or cloud-only concepts. More and more workloads will live entirely in the cloud, without ever touching the corporate network. In these scenarios, organizations need complete visibility from edge to core. But how?
Enterprise IT, security, and compliance teams have a choice to make: either completely trust the standards and services supported by their cloud provider of choice at the infrastructure level, or build everything from the ground up on the cloud that can mimic the standards they are used to.
Most cloud providers provide basic infrastructure performance details but not broader insights into internet performance, largely because they are not measuring, collecting, or analyzing the relevant metrics. Not only should this insight be made available, but it should be available on a real-time basis via a dashboard or APIs. In addition, these insights should be able to enable performance optimization of cloud workloads through integration into other tools.
Key insights and services that should be provided by your cloud provider should include:
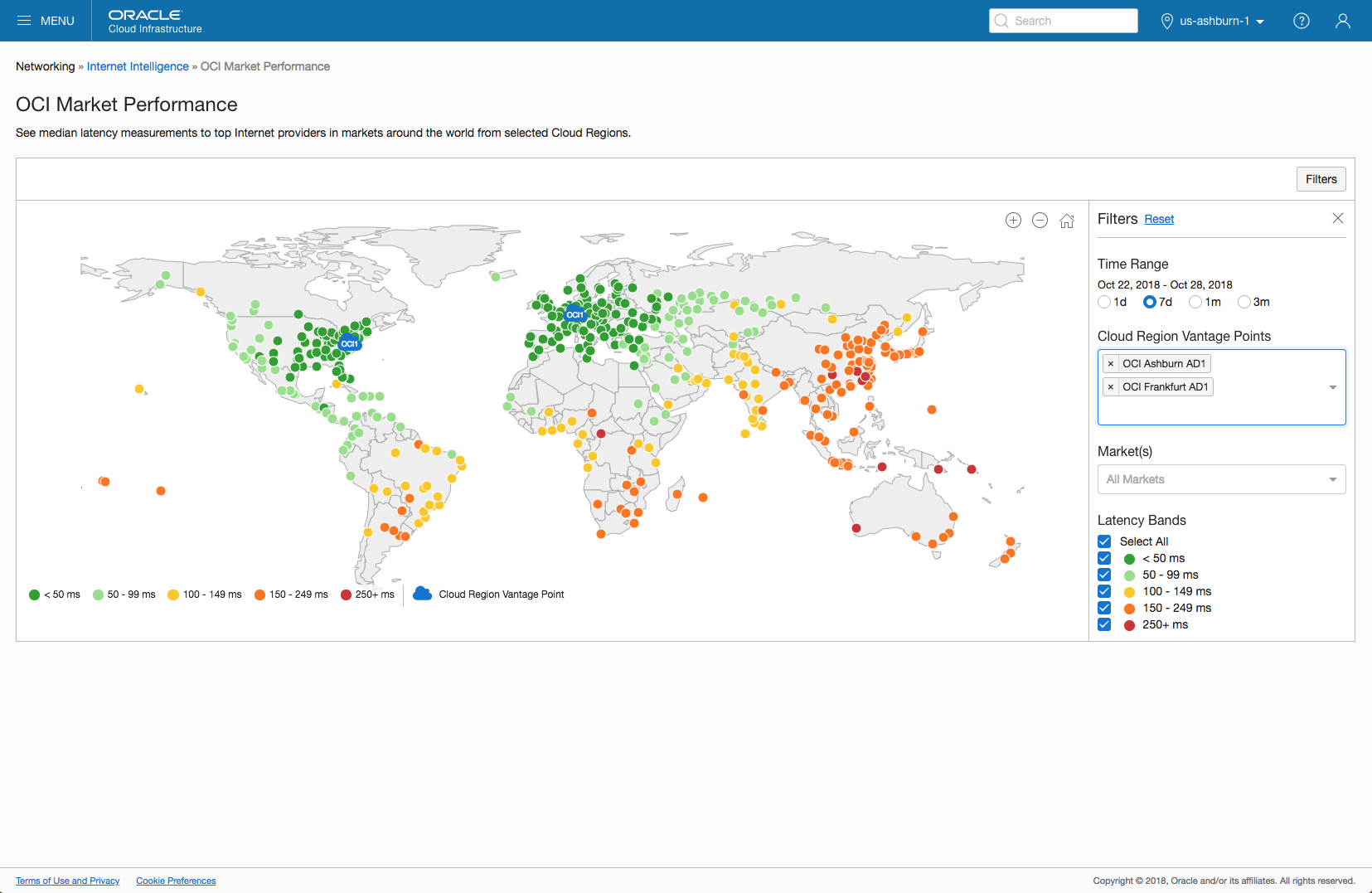
Internet telemetry: Understanding historical internet performance between multiple worldwide locations and your cloud infrastructure, and being able to test that performance in real time, can help ensure that your users are experiencing the best possible application performance. In addition, this performance data can be used for dynamic steering of inbound traffic, enabling you to direct or balance incoming traffic across multiple cloud locations.
This Oracle Internet Intelligence dashboard shows historical latency to multiple global markets within the Oracle Cloud Infrastructure customer console:
Security: It is critical to incorporate the same security measures that your enterprise IT built for over the years when shifting workloads to the cloud. Your cloud provider should support tightly integrated web application firewall, DDoS mitigation, bot management, and API protection services. Insights from these services should be easily accessible through the customer console, and the underlying data available for security information and event management ingestion and security operations center analysis.
Routing: Monitoring and alerting on routing announcements associated with your organization’s address space enables immediate responses to accidental leaks or malicious hijacks, limiting the effects and lowering the risk that user traffic is sent to fake sites or applications designed to steal information. If you are using a cloud provider, confirm that they are taking these steps for the address space in which their critical service platforms (compute, storage, DNS, etc.) reside, and that they have a plan for immediately addressing issues should they arise. Additionally, your cloud provider should have visibility into network paths to and from their regions to ensure traffic isn’t taking circuitous routes, increasing latency, or transiting through hostile nation-states.
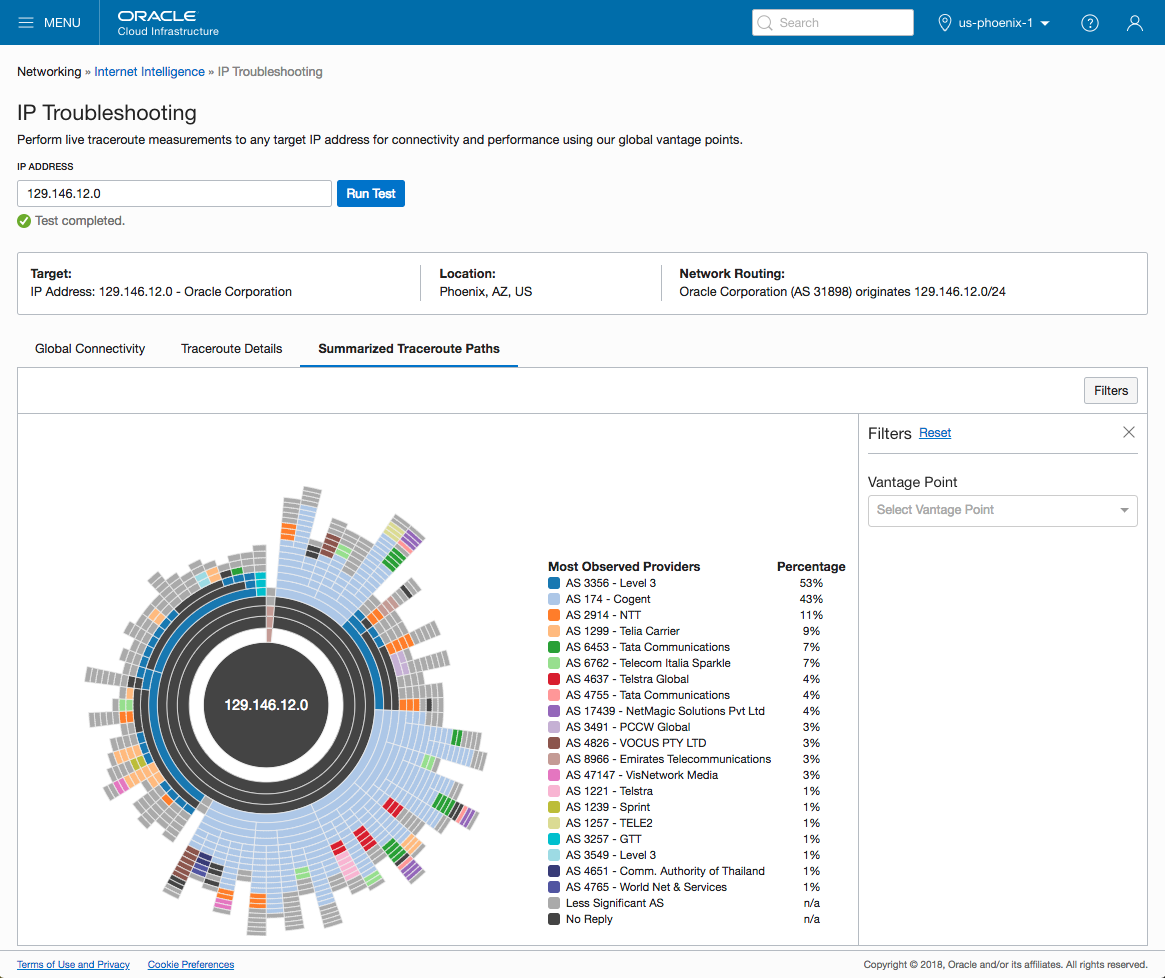
Performance issues in real time with measurements from a global network of vantage points
Moving to the cloud is a big deal for most organizations. When making a choice on cloud provider, ask some tough questions about whether or not they will give you visibility into both their infrastructure and the performance and visibility of the broader internet.
Oracle Cloud Infrastructure offers better performance at a lower price point than competing infrastructure as a service providers. And because it can isolate customers from one another using bare metal compute, it avoids the risk and exposure that comes with shared instances.
In other words, Oracle Cloud Infrastructure is built for the enterprise from the ground up, with security from edge to core. As you move your enterprise network to the cloud, make sure your provider is enterprise grade.