Overview
Some MySQL distribution packages, such as the generic Linux build, bundle an OpenSSL dependency within the same .tar.gz archive.
With the new MySQL 8.0.46, 8.4.9 and 9.7.0 releases, we are upgrading those bundled packages from using OpenSSL 3.0 to the new OpenSSL 3.5 LTS branch.
Native OS packages, such as .rpm and .deb, continue to use the OpenSSL version provided by the target operating system, which may already be newer than 3.0 depending on the distribution.
OpenSSL upgrade involved no functional TLS code changes within MySQL code, except for 8.0.x (when built with OpenSSL >= 3.5) – in this particular configuration we are now blocking Key Exchange Diffie-Hellman set of ciphers (considered weak), as was already done for other MySQL branches.
Benefits
OpenSSL 3.5 branch has replaced 3.0 as a new long term stable (LTS) release, so moving to it is a logical step.
Why this change:
- previous OpenSSL 3.0 LTS branch has already moved out of full-support phase (although it will receive security fixes until September 7, 2026)
- OpenSSL 3.5 brings performance improvements compared to 3.0 (test results below)
- OpenSSL 3.5 introduces implementation of Post-Quantum Cryptography (PQC) algorithms, a feature expected to be critical for protecting confidentiality of our communication against being broken by quantum computers
Note that the OpenSSL upgrade will not automatically enable PQC support in MySQL, this implementation is being scheduled for a future release.
Performance testing
Dimitri Kravtchuk measured the MySQL performance difference when compiled against a number of different OpenSSL versions:
- OpenSSL-1.1.1L — the most efficient and the fastest OpenSSL so far (EOL)
- OpenSSL-3.0.19 — the latest in 3.0 series, old LTS branch
- OpenSSL-3.3.6
- OpenSSL-3.4.4
- OpenSSL-3.5.5 — the target release, the latest LTS branch
- OpenSSL-3.6.1 — the current development series release
The tests were selected with criteria to help exposing TLS overhead (by hiding the other possible bottlenecks):
- use CPU-bound tests
- having short and fast SQL queries
- favor local execution (test client and server on the same host)
This led to selection of the following two tests:
- Sysbench Point-SELECTs: fastest OLTP Read-Only workload based on Primary Keys (PK) lookups.
- Sysbench Re-Connect SELECTs: same workload as above, except after each SELECT query we’re reconnecting to MySQL Server to stress-test the TLS code and evaluate connection initiation overhead.
In this evaluation, we’ve used the following systems to execute test workloads:
- BM.48: 48cores-HT Intel, 192GB RAM, OL7
- BM.44: 44cores-HT Intel, 512GB RAM, OL7
- OCI VM X9.16: 16cores-HT Intel, 256GB RAM, OL8
- OCI VM E4.16: 16cores-HT AMD E4, 256GB RAM, OL8
The results below are just a selection of broader testing scope done by Dimitri, focusing on local tests using 8.4 and the latest 9.7.0 innovation release, i.e. omitting 8.0 (similar to 8.4) and over-network results.
For more detailed results, see the following post by Dimitri:
http://dimitrik.free.fr/blog/posts/mysql-perf-openssl355-evaluation.html
Testing Results
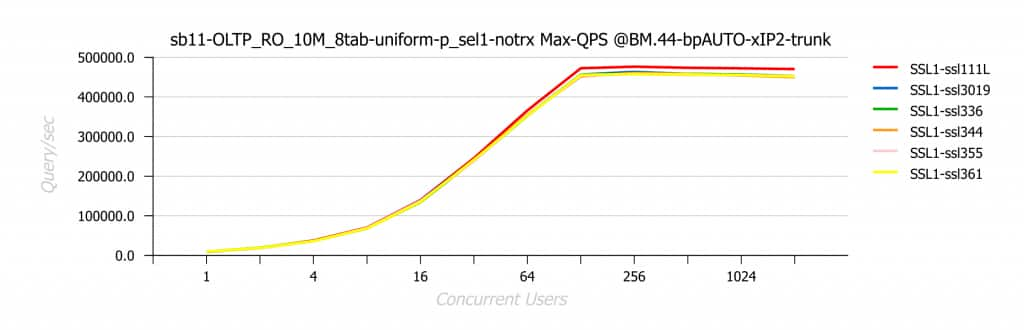
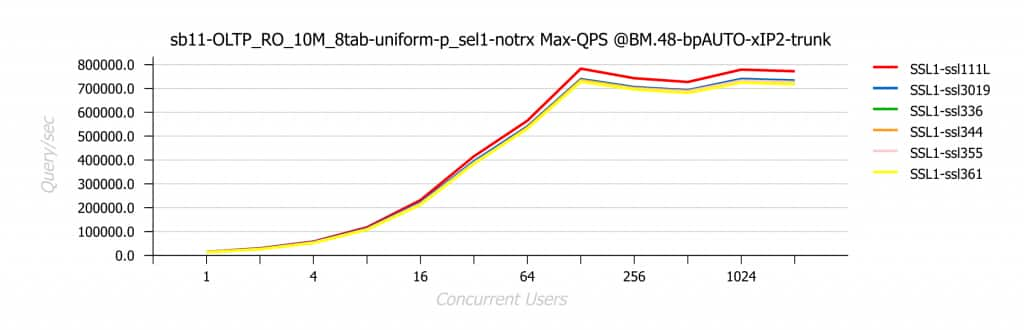
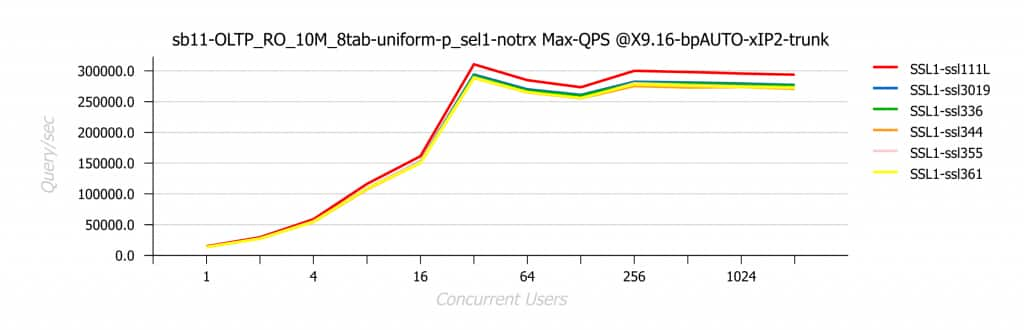
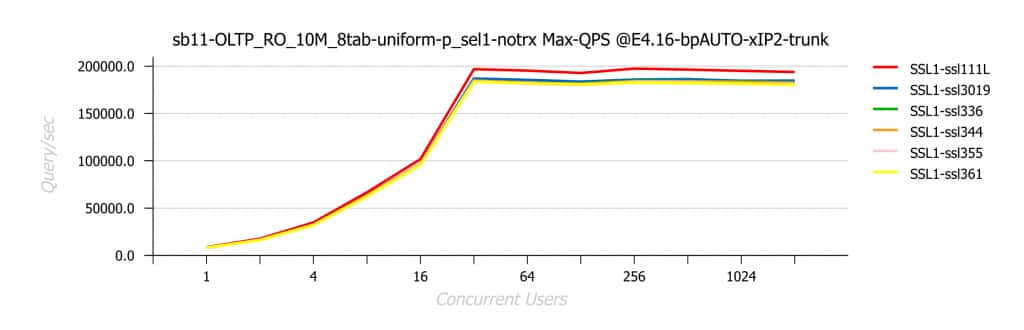
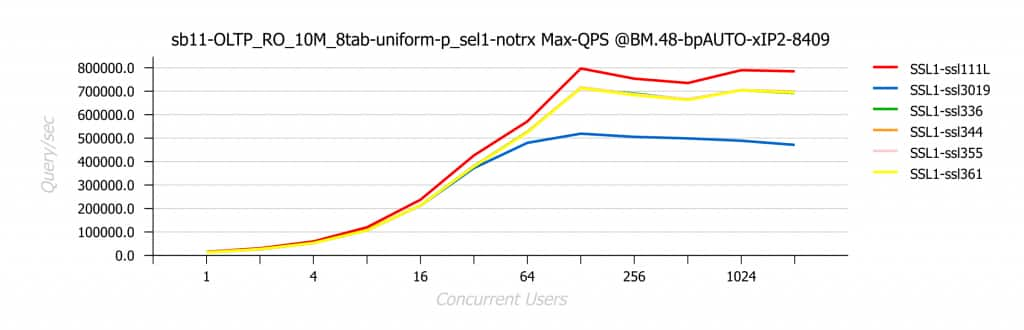
Point-SELECTs Workload | Local-IP
The following are the test results obtained on Point-SELECTs workload executed locally on each server and using local IP-port (loopback 127.0.0.1):
MySQL 9.7 (trunk)
BM.44
BM.48
OCI VM X9.16
OCI VM E4.16
MySQL 8.4.9
BM.44
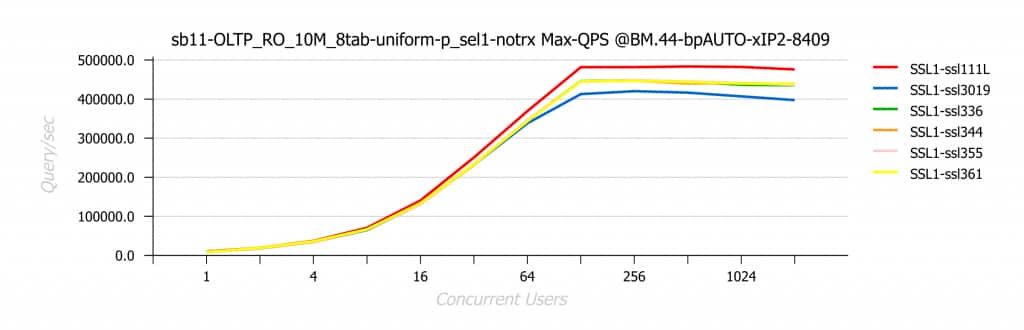
BM.48
OCI VM X9.16
OCI VM E4.16
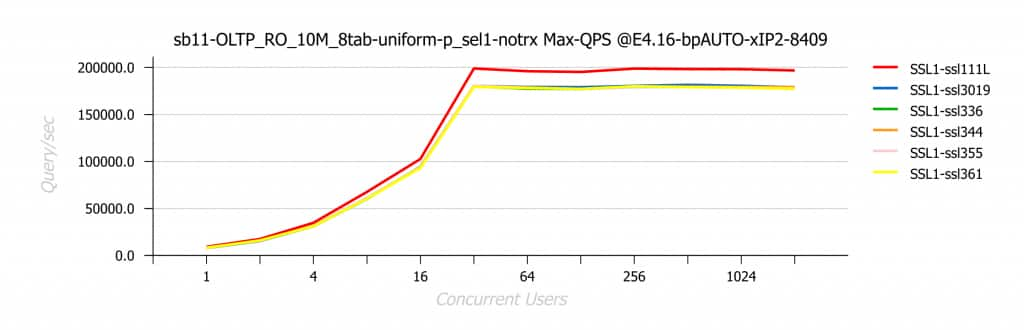
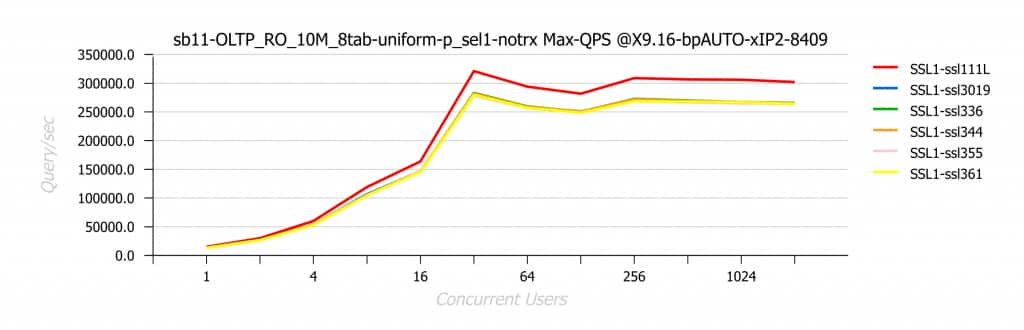
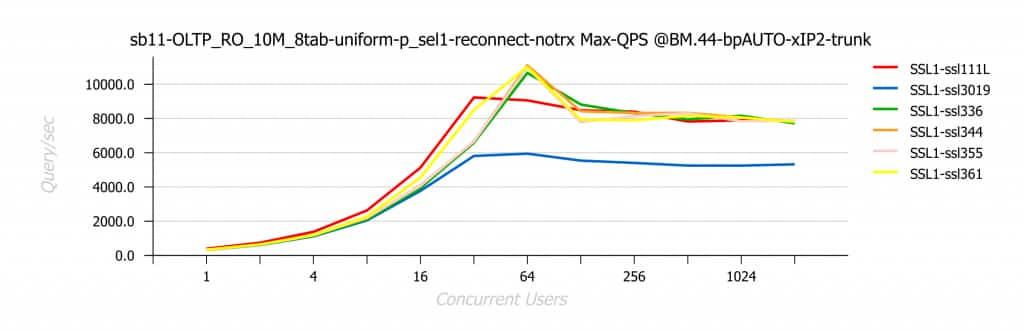
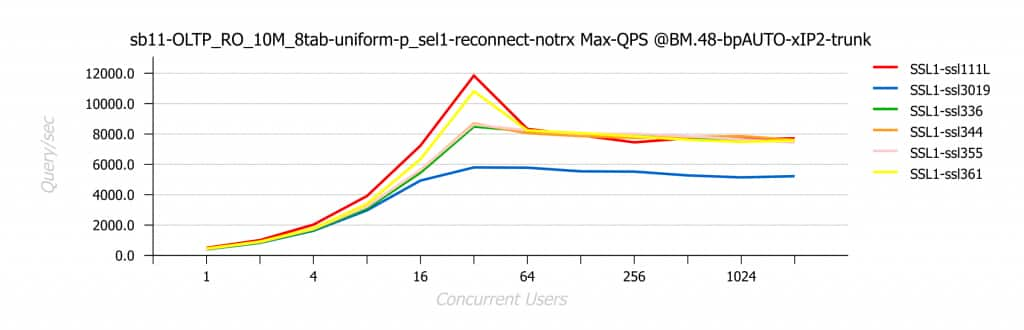
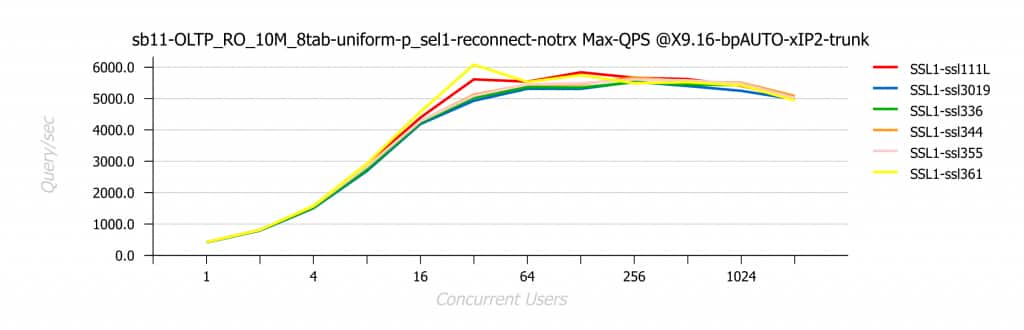
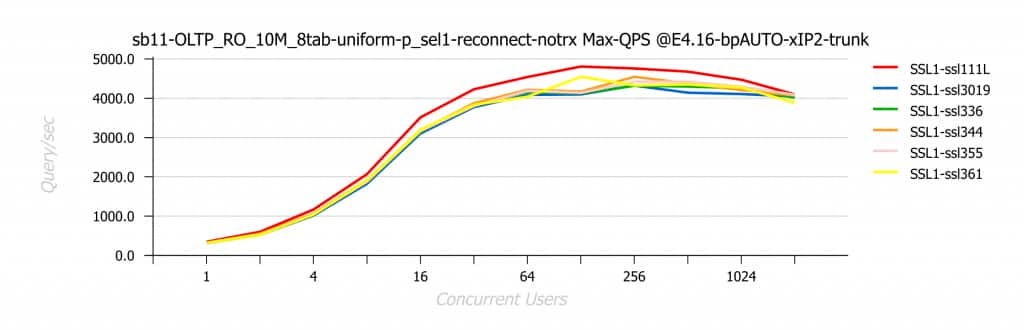
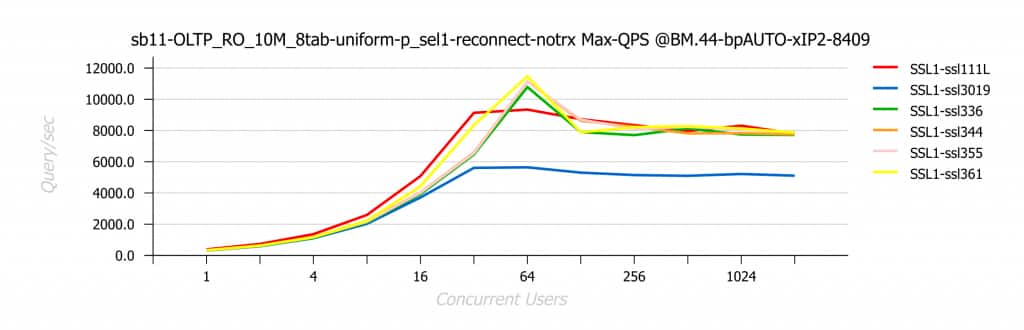
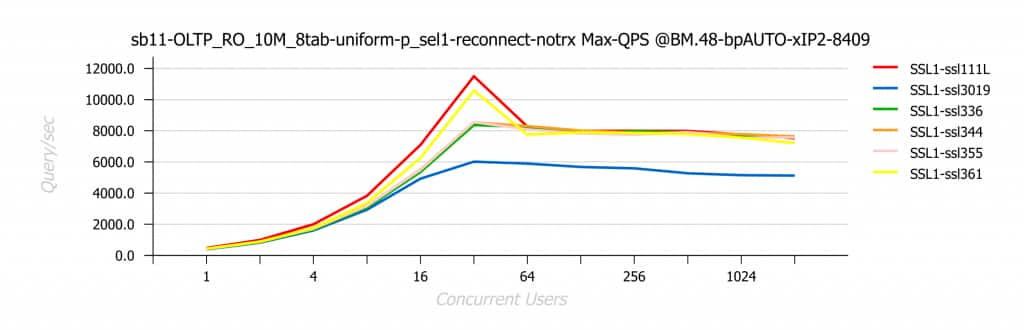
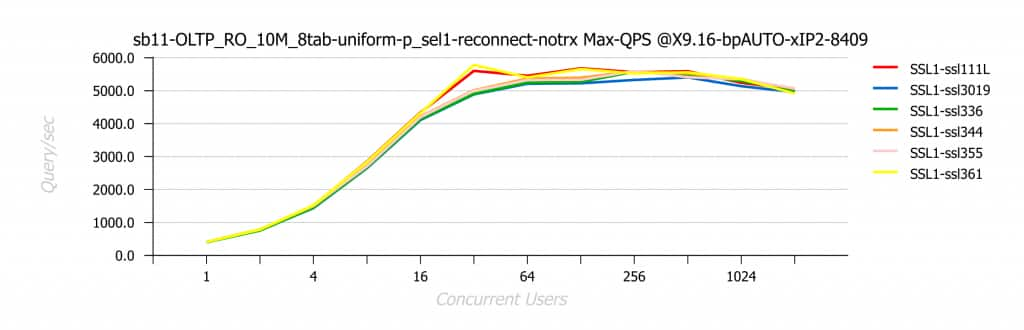
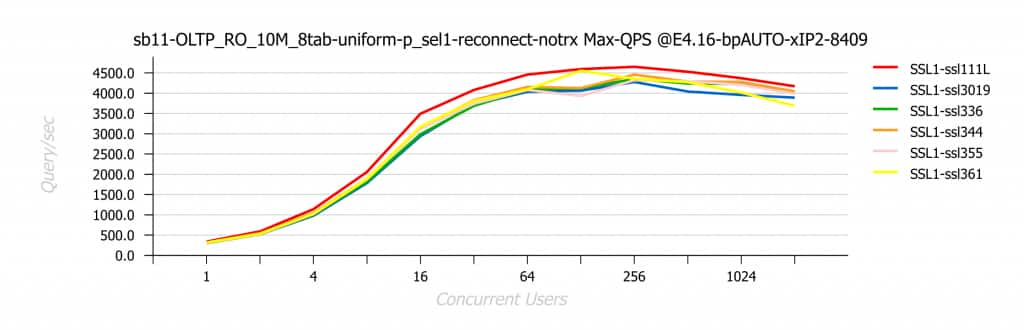
Re-Connects SELECTs Workload | Local-IP
The following are the test results obtained on Re-Connect SELECTs workload executed locally on each server and using local IP-port (loopback 127.0.0.1):
MySQL 9.7 (trunk)
BM.44
BM.48
OCI VM X9.16
OCI VM E4.16
MySQL 8.4.9
BM.44
BM.48
OCI VM X9.16
OCI VM E4.16
Conclusion
From performance perspective, OpenSSL-1.1.1 is generally still the best release delivering highest throughput in majority of cases (but being End-of-Life since 2023).
The good news is that OpenSSL 3.5 shows an improvement over the OpenSSL 3.0, and it’s quite significant in some cases.
Looking at the future, OpenSSL-3.6.1 is giving a hope to see more performance improvements in the next releases, and maybe one day it will catch up to OpenSSL-1.1.1.
Thank you for using MySQL!
