Continuing our commitment to openness and open source software, today we’re announcing the general availability of Resource Manager, a fully managed service that makes it significantly easier to use HashiCorp Terraform on Oracle Cloud Infrastructure.
This is especially true for large or distributed enterprise development teams that share common infrastructure. Teams can use Resource Manager’s deep integration with the Oracle Cloud Infrastructure platform by, for example, creating policies to constrain the operations that different users and groups can perform. We previewed Resource Manager at KubeCon + CloudNativeCon North America in December 2018.
This article provides a high level overview and steps to get started. To get the most out of this walk-through, the reader should understand the basics of Terraform and have some experience using it to manage cloud infrastructure. If you need a refresher, take a moment to review the basics. If you don’t have an account on Oracle Cloud Infrastructure and want to work through these examples, you can create a free account and get started with up to 3,500 free hours.
When migrating their Terraform workflows to use Resource Manager, developers will be happy to know that all of the Oracle Cloud Infrastructure Terraform Provider functionality is completely supported. Resource Manager is the latest example of Oracle Cloud Infrastructure’s commitment to openness by building on top of powerful open source software technologies like Terraform and honoring Oracle’s commitment to preserving our customers’ choice to migrate their workloads with minimal impact to their business, code, and runtime.
“We are excited to partner with Oracle on Resource Manager and have it power the core infrastructure provisioning on Oracle Cloud Infrastructure. With Resource Manager, HashiCorp Terraform becomes accessible to even more users who care about open source standards and are looking to deploy their applications consistently on Oracle Cloud Infrastructure.”
–Burzin Patel, VP, Worldwide Alliances, HashiCorp
This post provides a high-level overview and steps to get you started. To get the most out of the walkthrough, it’s helpful to understand the basics of Terraform and have some experience using it to manage cloud infrastructure. If you need a refresher, take a moment to review the basics. If you don’t have an account on Oracle Cloud Infrastructure and want to work through these examples, you can create a free account and get started with up to 3,500 free hours.
Overview
At the highest level, Resource Manager is an orchestration service for managing Oracle Cloud Infrastructure resources by using Terraform. Using Resource Manager introduces many benefits, for example:
- Improves team collaboration: Securely manages Terraform state files and provides state locking when needed. Terraform uses state files to map resources and track metadata when creating, modifying or destroying infrastructure. This enables teams to understand existing infrastructure and see any changes when running a Terraform plan.
- Enables automation: Unlocks infrastructure automation capabilities by using its fully supported SDKs, APIs, and CLI tooling.
- Integrates seamlessly with the platform: Enables developers to leverage the entire Oracle Cloud Infrastructure API catalog (for example, authentication). For example, you can create policies that govern access to Resource Manager stacks and jobs (more about those later).
- Provides a familiar console experience: Conveniently manage Oracle Cloud Infrastructure resources and other services that also leverage identity federation.
The Resource Manager workflow is straightforward: you upload a bundled Terraform configuration file set, associate the bundle with a user-defined stack, and then run a job’s Terraform action against the stack. A stack defines a distinct set of cloud resources within a compartment, and a job is the set of Terraform commands that can be executed against a stack. The Terraform commands supported include plan, apply, and destroy. After you perform a Terraform action, the refreshed Terraform state file is securely managed by Resource Manager and is subsequently referenced for each Terraform action coordinated by Resource Manager. By managing the Terraform state file for you, Resource Manager ensures a single source of truth for the current state of the infrastructure.
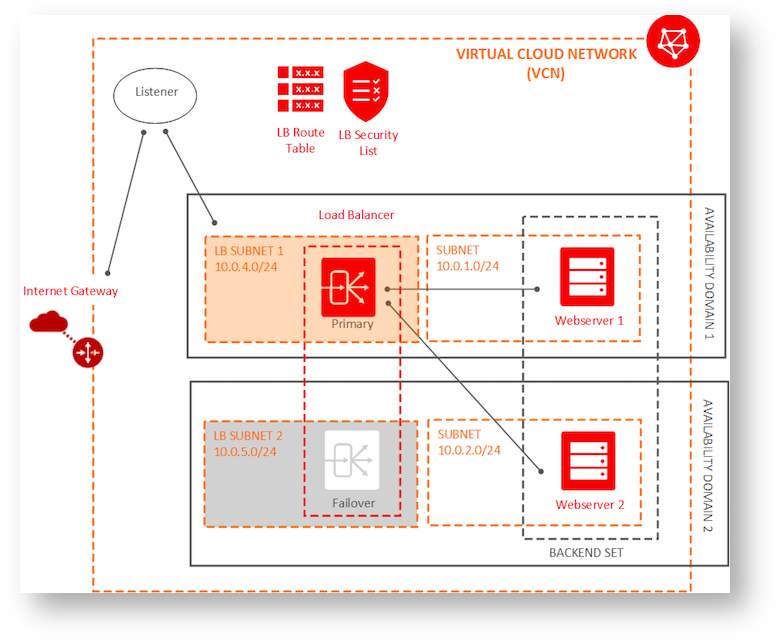
Target Architecture
The source code for this walkthrough is available on GitHub. It deploys a public regional load balancer on Oracle Cloud Infrastructure as described in the Getting Started with Load Balancing tutorial. The resources defined in the Terraform configuration files are as follows:
- A compartment, and a virtual cloud network in a single region that contains an internet gateway
- A regional load balancer in a public subnet, a listener, and a failover load balancer also within a public subnet
- Two backend sets each with a single compute instance in separate private subnets within a different availability domain
The following diagram shows the target architecture:
In this post, we manage Oracle Cloud Infrastructure resources with Resource Manager in the Oracle Cloud Infrastructure Console.
Walkthrough
This walkthrough assumes that you’ve created a compartment named orm-demo-cmpt and a group named orm-demo-admin-grp, and added a user to that group. If you need help creating these, see the documentation on managing compartments, users, and groups.
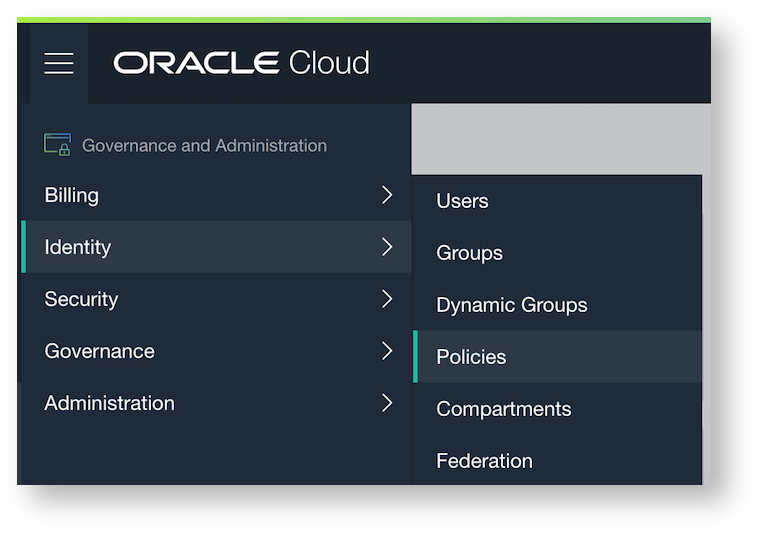
Step 1: Create an IAM Policy
-
In the Console navigation menu, select Identity and then click Policies.
-
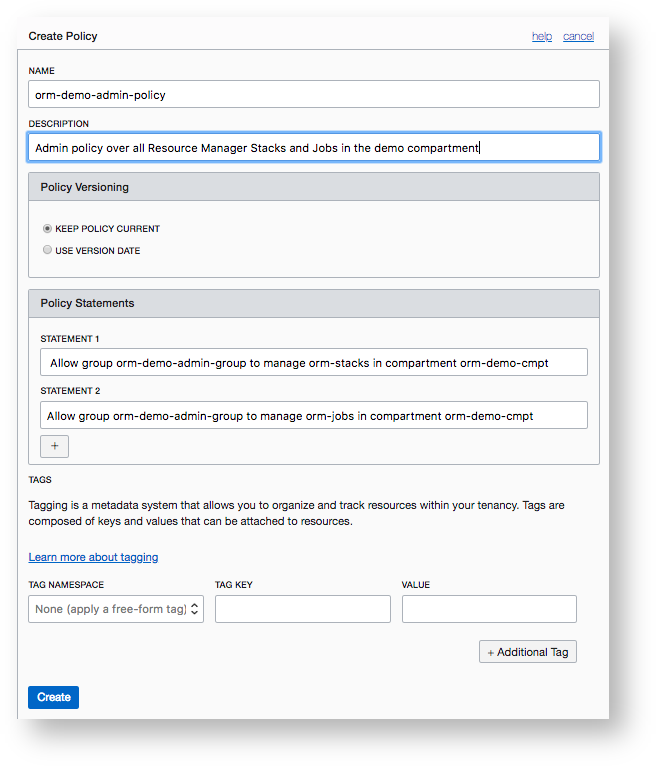
On the Policies page, click Create Policy.
-
In the Create Policy dialog box, name the policy orm-demo-admin-policy. This policy gives the orm-demo-admin-grp group the permissions to manage all Resource Manager stacks and jobs in the orm-demo-cmpt compartment.
-
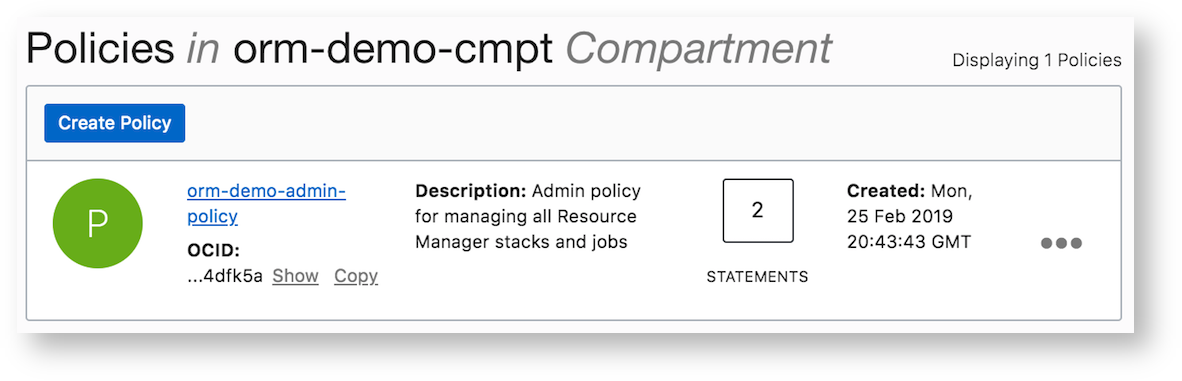
Click Create. The policy is listed on the Policies page.
Note: In a production system, it’s both more secure (principle of least privilege) and practical to create additional groups with more granular permissions. For example, it’s likely that we’d need to create a development team group that can only use predefined stacks and run jobs against it (use-orm-stack and use-orm-job, respectively).
Step 2: Create the Stack
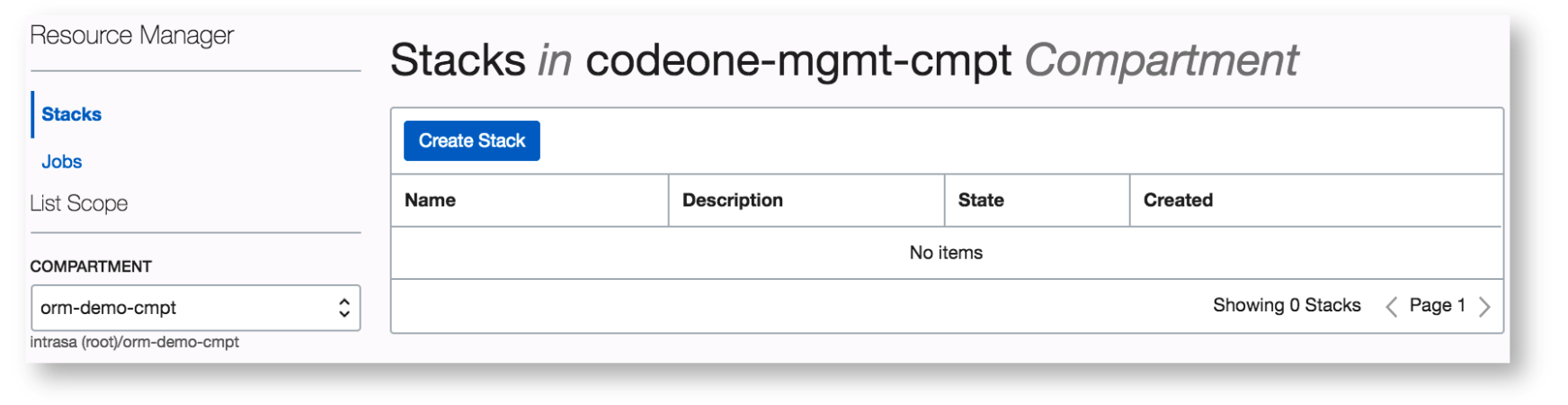
As mentioned earlier, a stack represents definitions for a collection of Oracle Cloud Infrastructure resources within a specific compartment. In this step, we configure a new stack in the orm-demo-cmpt compartment in the us-phoenix-1 region and name it HA Load Balanced Simple Web App. As the stack’s name suggests, its configuration files define the load balancing, networking, and compute resources to deploy the target architecture plus an HTTP server.
-
In the Console navigation menu, select Resource Manager and then click Stacks.
-
Click Create Stack.
-
Before you upload the Terraform files to Resource Manager, bundle them into a zip archive.
-
In the Create Stack dialog box, verify the compartment (and change it if necessary), provide a meaningful name for the stack and a description, upload the Terraform configuration file zip archive, and add the keys and values for any Terraform variables referenced in the uploaded bundle.
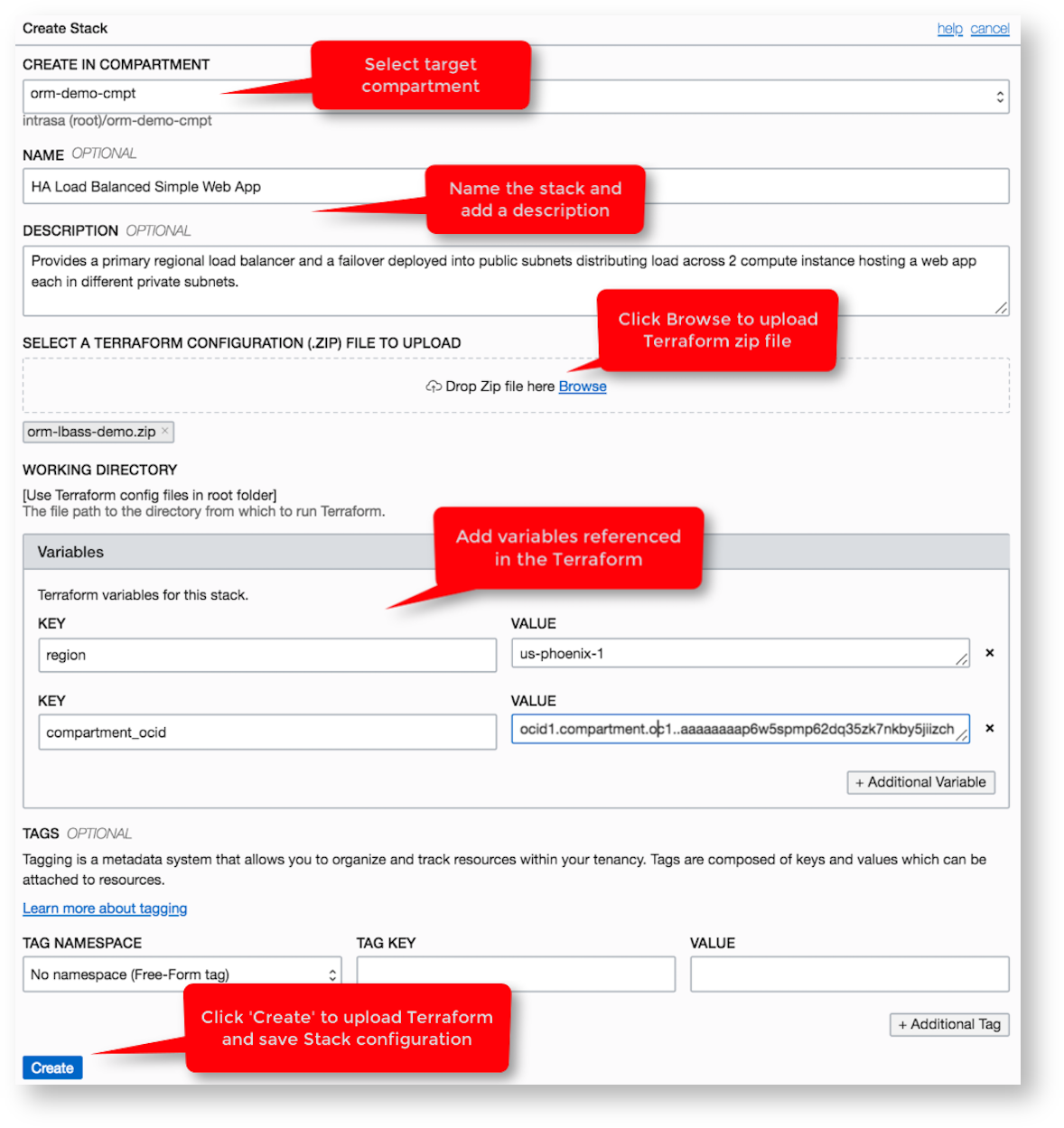
Important: Don’t include confidential information (for example, SSH private key values and authentication credentials) in variables, tags, or descriptions. Depending on the context, consider using a secret vault like the Oracle Cloud Infrastructure Key Management service or HashiCorp Vault, as appropriate.
A description can help teams quickly identify a stack’s use and purpose, which is especially helpful as the infrastructure increases in complexity. Also, when Resource Manager uploads the zip archive, it looks in the root directory for all *.tf files. If the Terraform files are not located in the root directory, add the relative path to the subdirectory that contains those files in the Working Directory field. Lastly, tags address many use cases, from associating stacks with environments in a CI/CD build pipeline to enterprise cost-center allocation. For more information about tagging, see Managing Tags and Tag Namespaces.
-
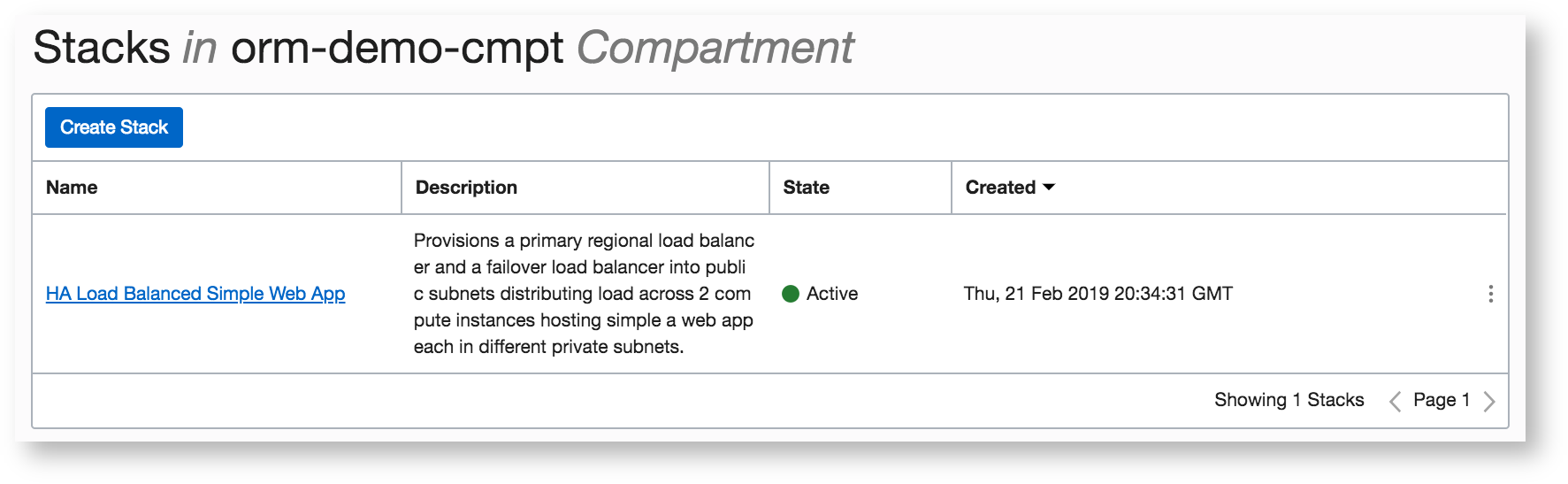
Before moving on to running a job, quickly review the new stack and then click the hyperlinked stack name.
Step 3: Execute Jobs: Plan, Apply, and Destroy
As previously mentioned, jobs perform actions against the Terraform configuration files associated with a stack. The Terraform actions that a job can perform are plan, apply, and destroy. Because Terraform command execution is not atomic, it’s crucial to prevent any race conditions or state corruption from occurring because of parallel execution. To prevent this, Resource Manager ensures that only one job can run against a stack at a given time against a single state file.
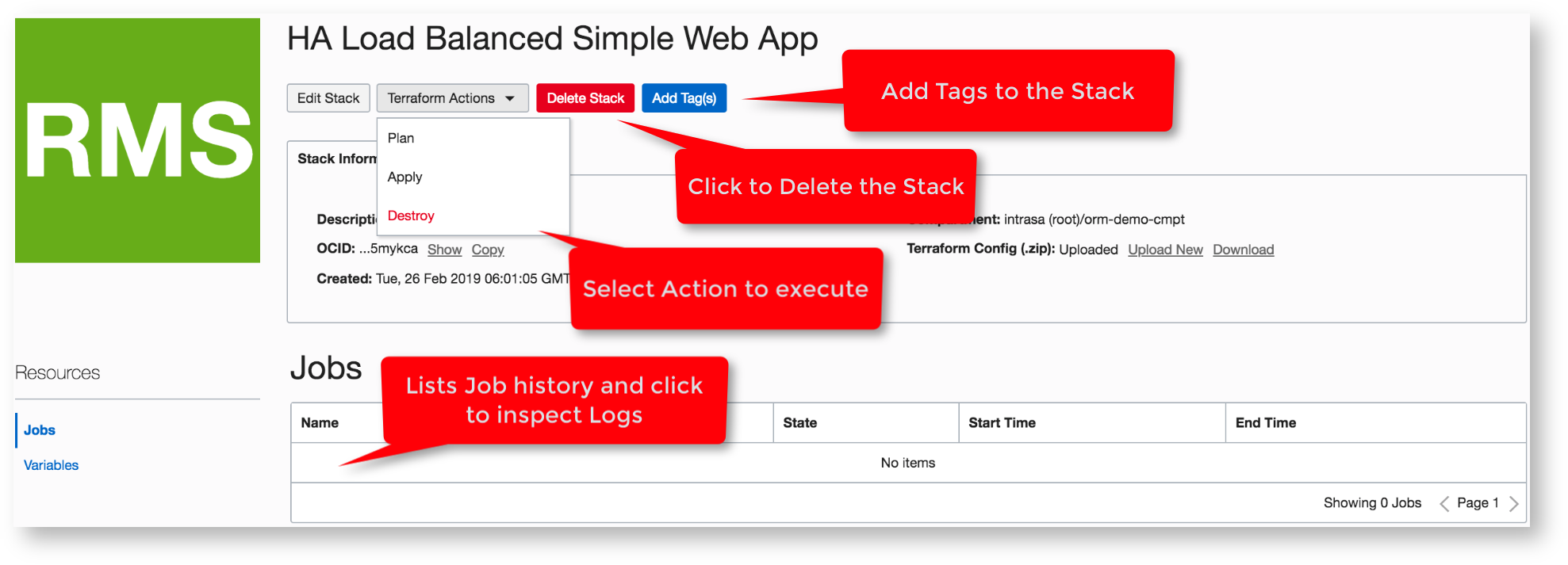
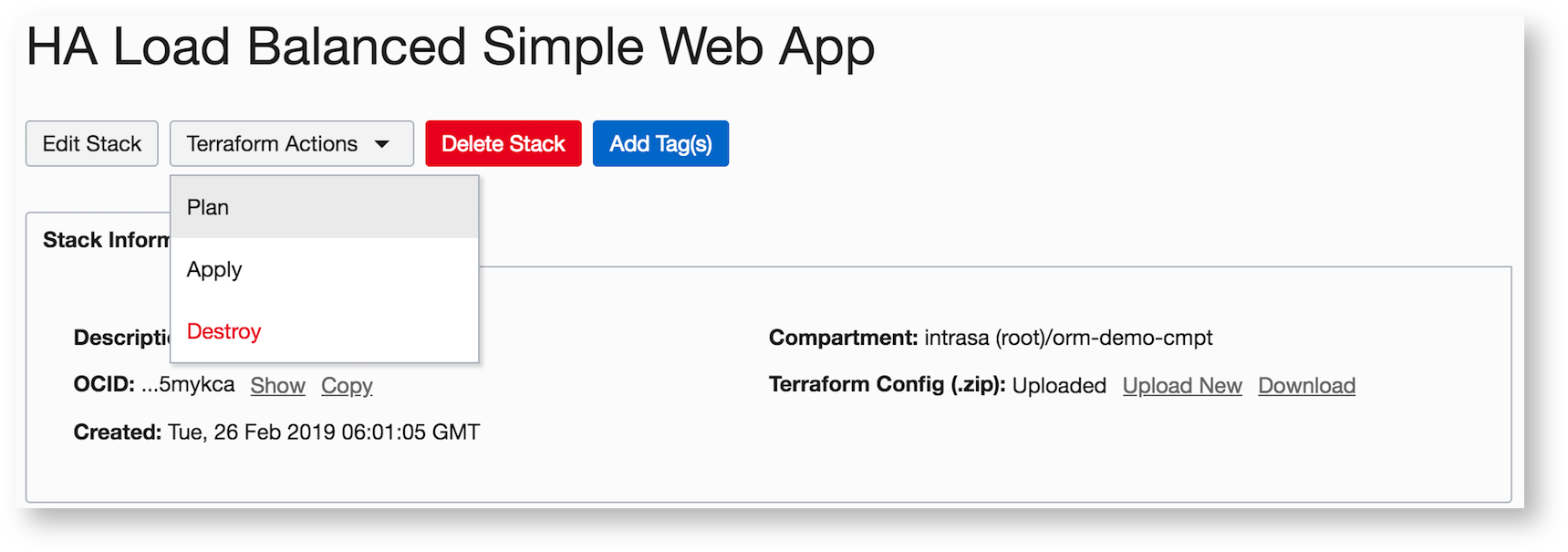
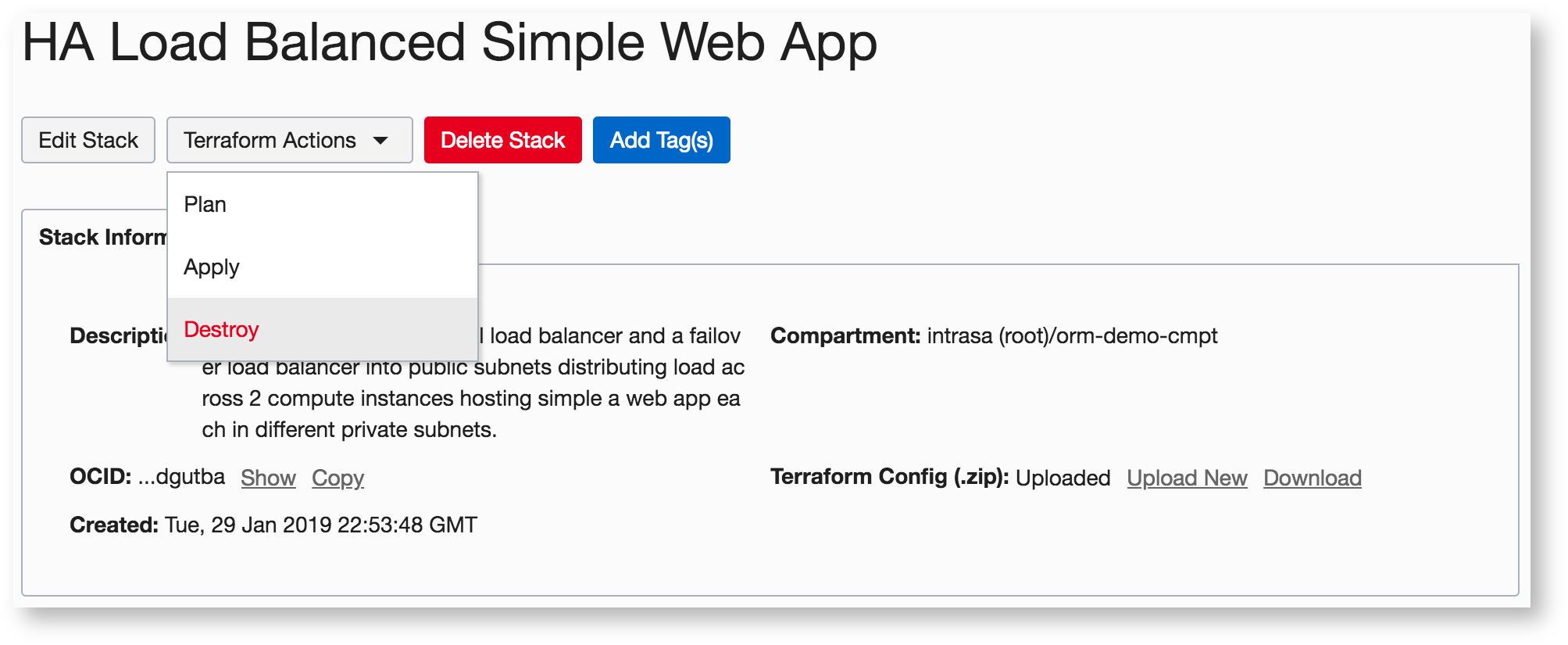
On the Stack details page, you can completely manage the stack’s configuration (for example, update and delete the stack, add tags, and edit variables) and also download the zip archive that contains the latest Terraform configuration (which can be especially helpful when troubleshooting).
-
From the Terraform Actions menu, select Plan.
-
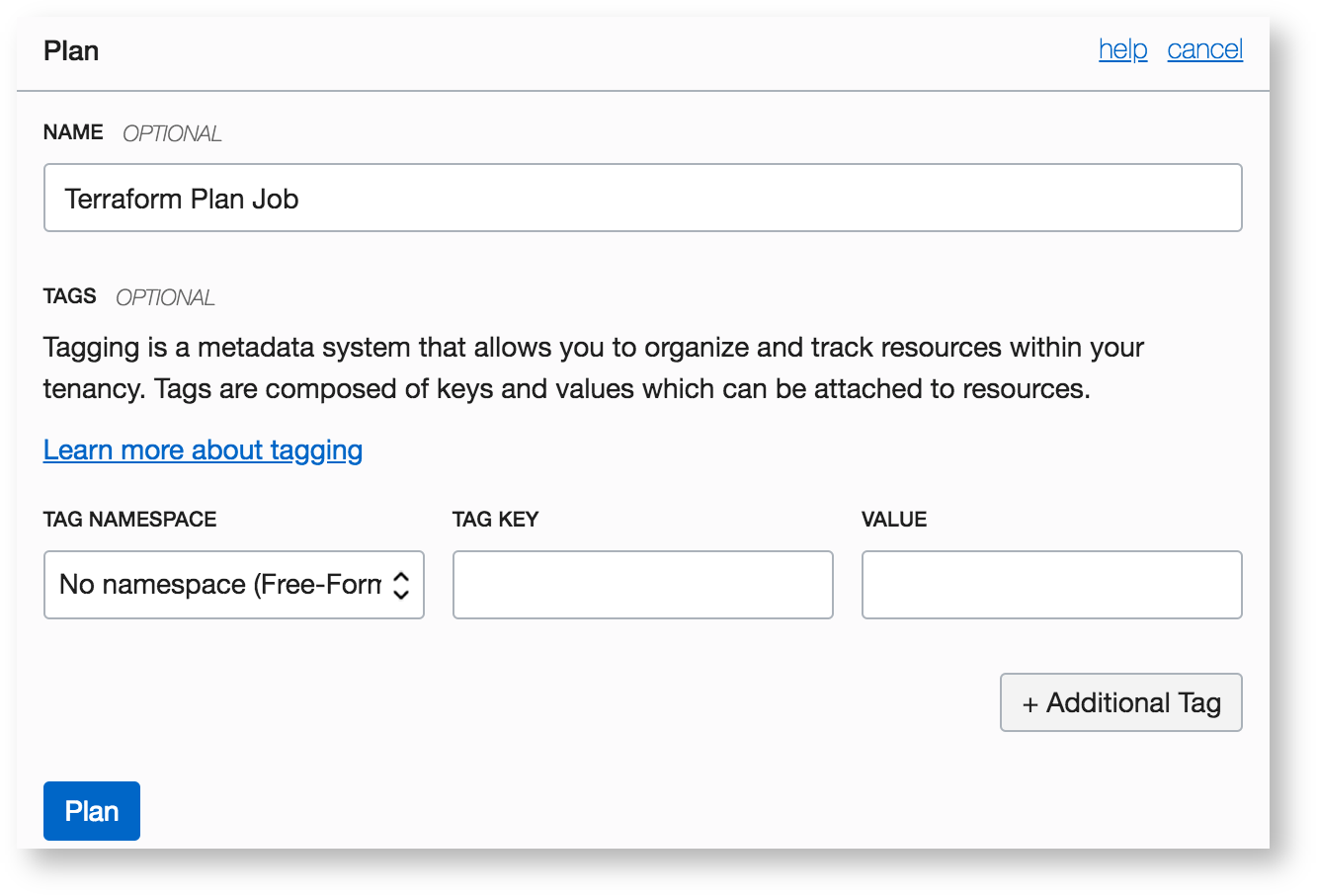
In the Plan dialog box, optionally provide a more readily identifiable name and specify a tag to associate with this action. Then, click Plan to run the job.
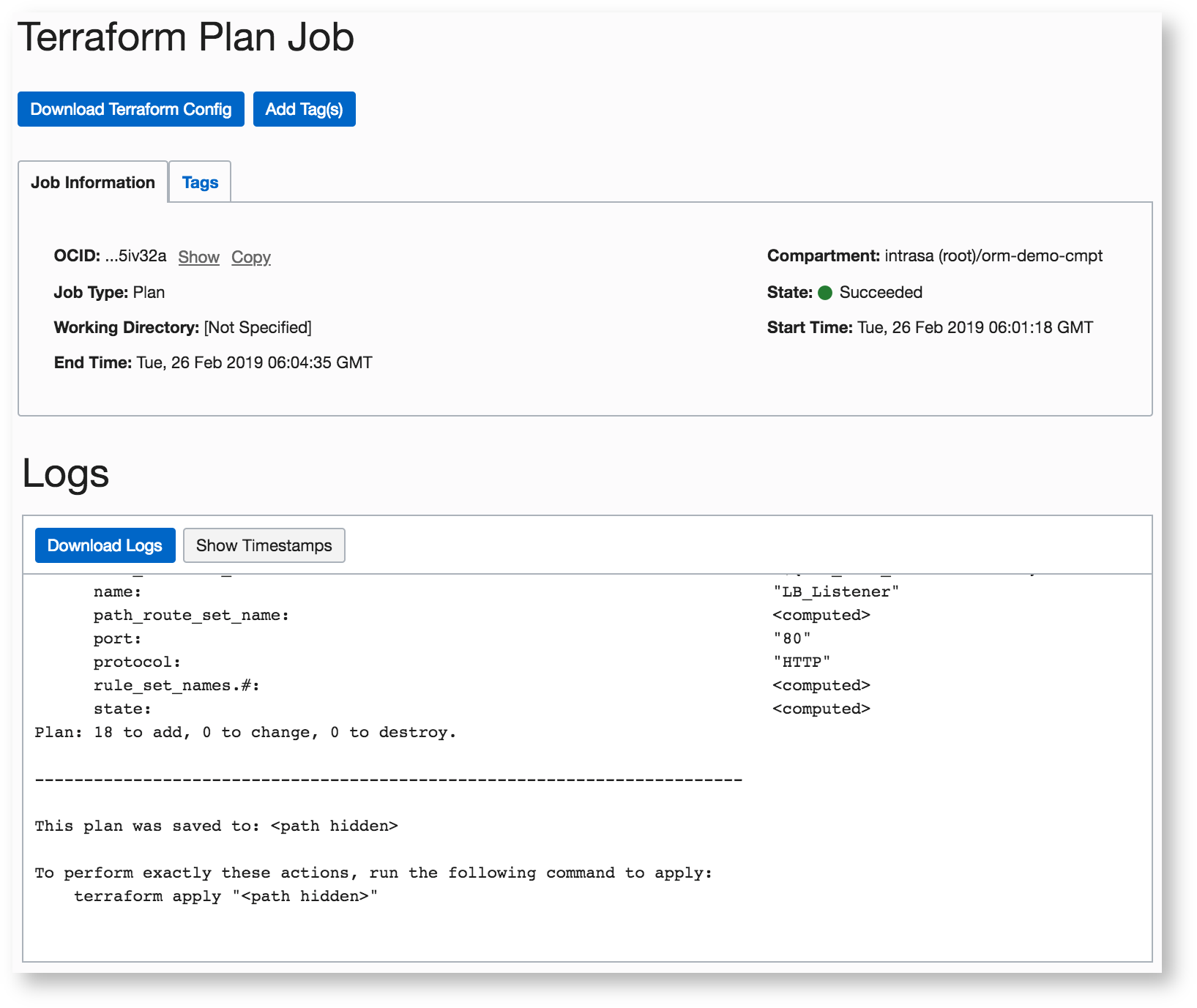
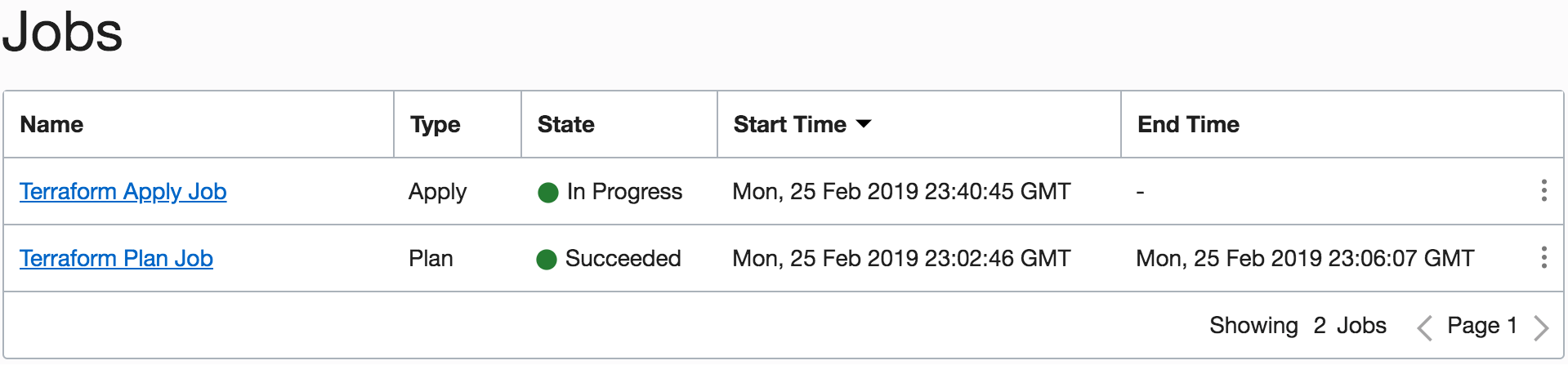
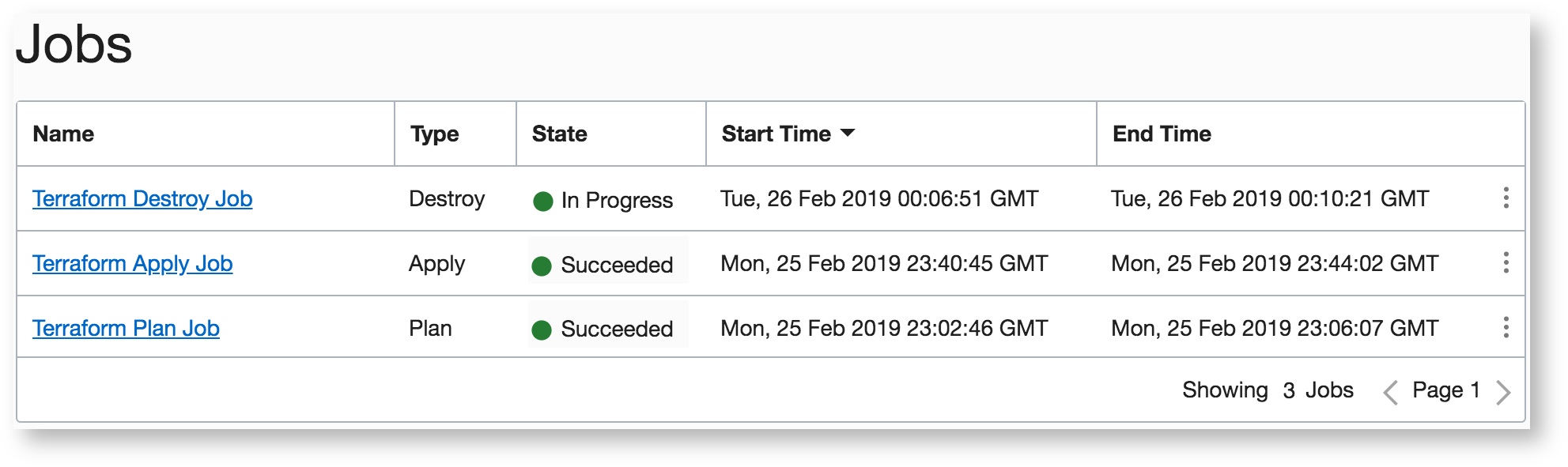
In the Jobs section of the stack’s details page, the job’s state appears as Accepted, which indicates that the platform is spinning up the necessary resources to run the command. The state changes to In Progress and then to either Succeeded or Failed. Click the Actions menu (three dots) to display actions related to the job.
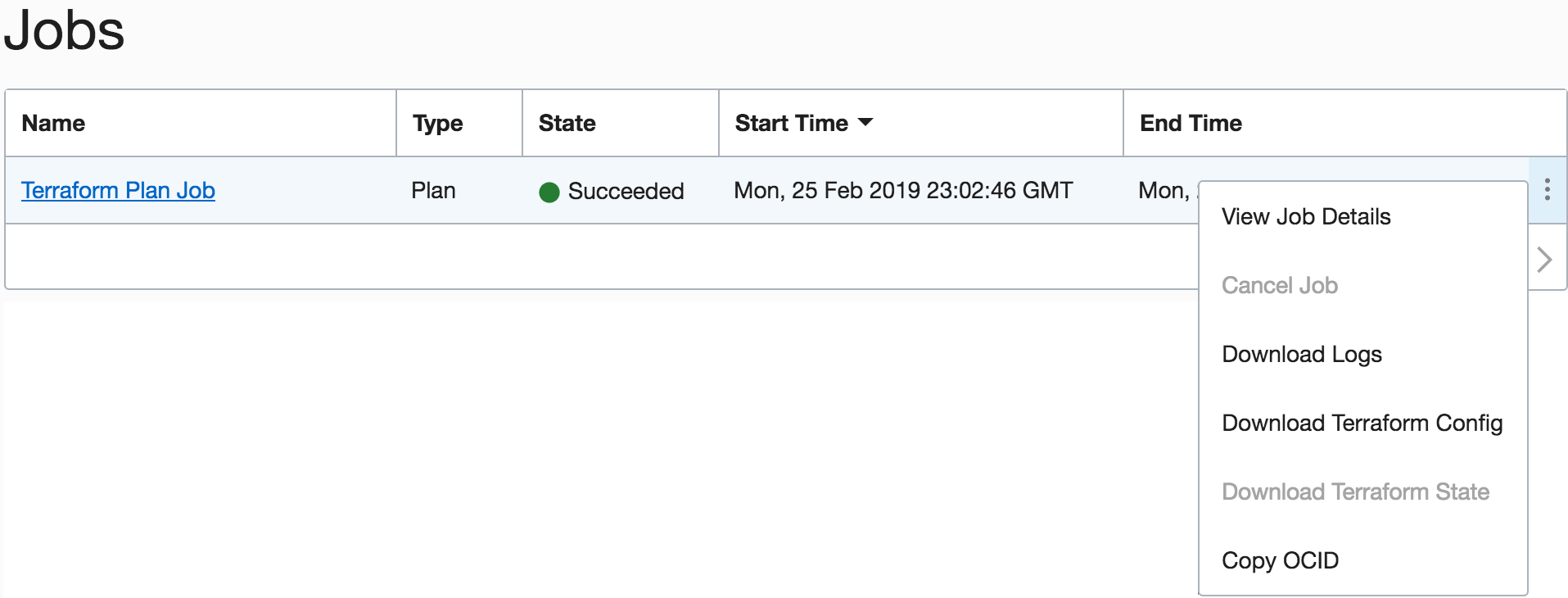
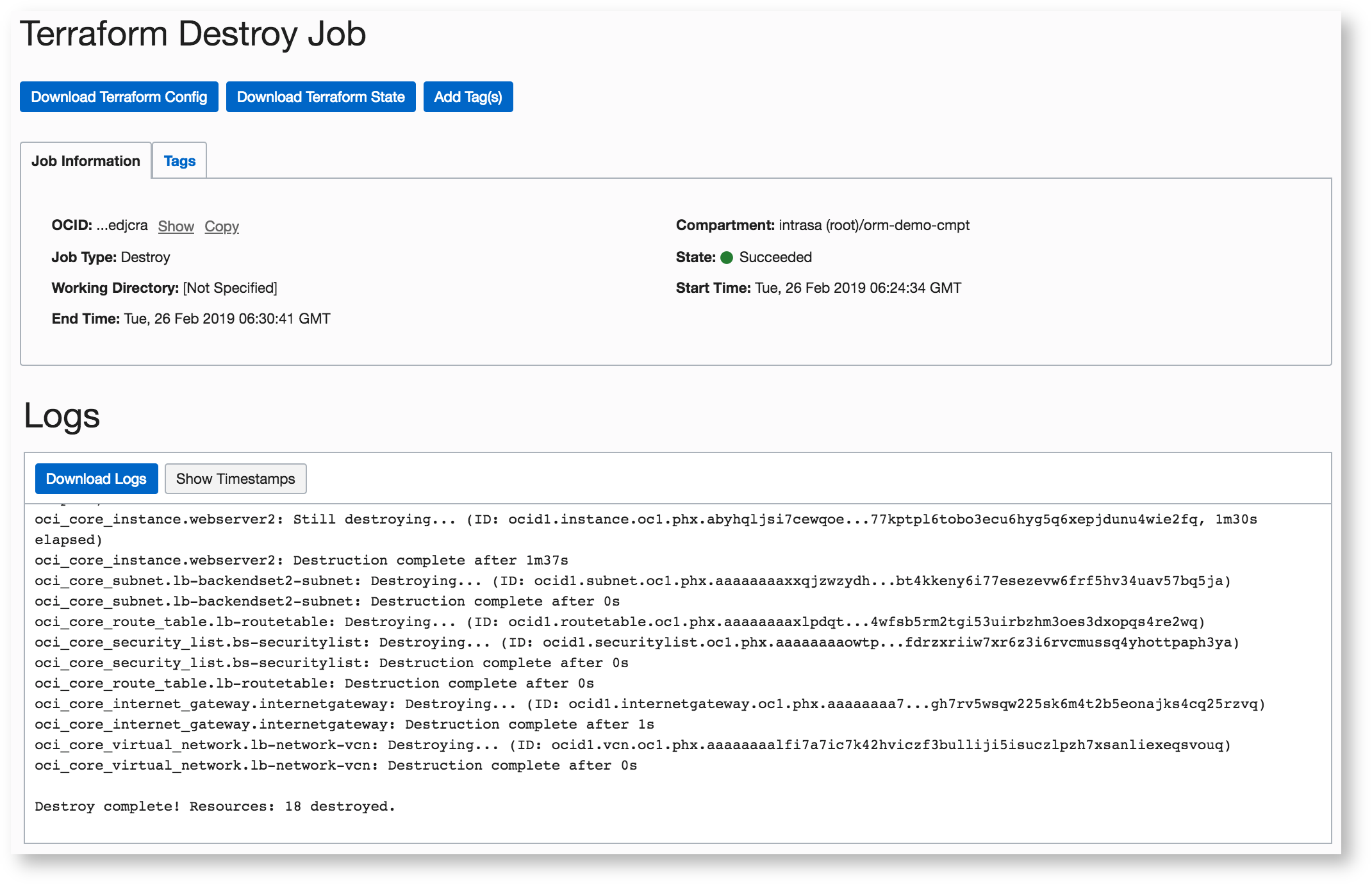
You can also click the job name to view the job’s details and its logs containing, which contain the Terraform output. You can scroll through the logs or download them.
-
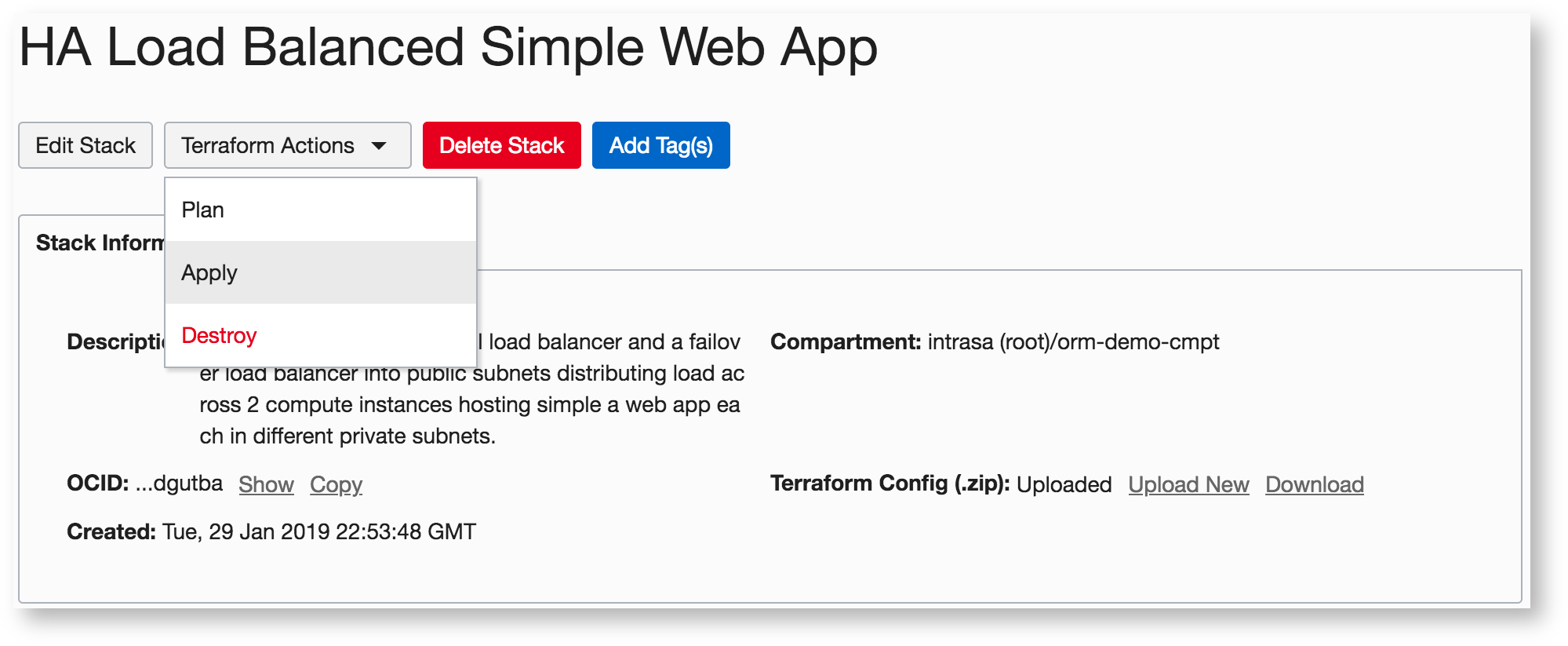
Because the previous plan action succeeded, select the Apply from the Terraform Actions menu.
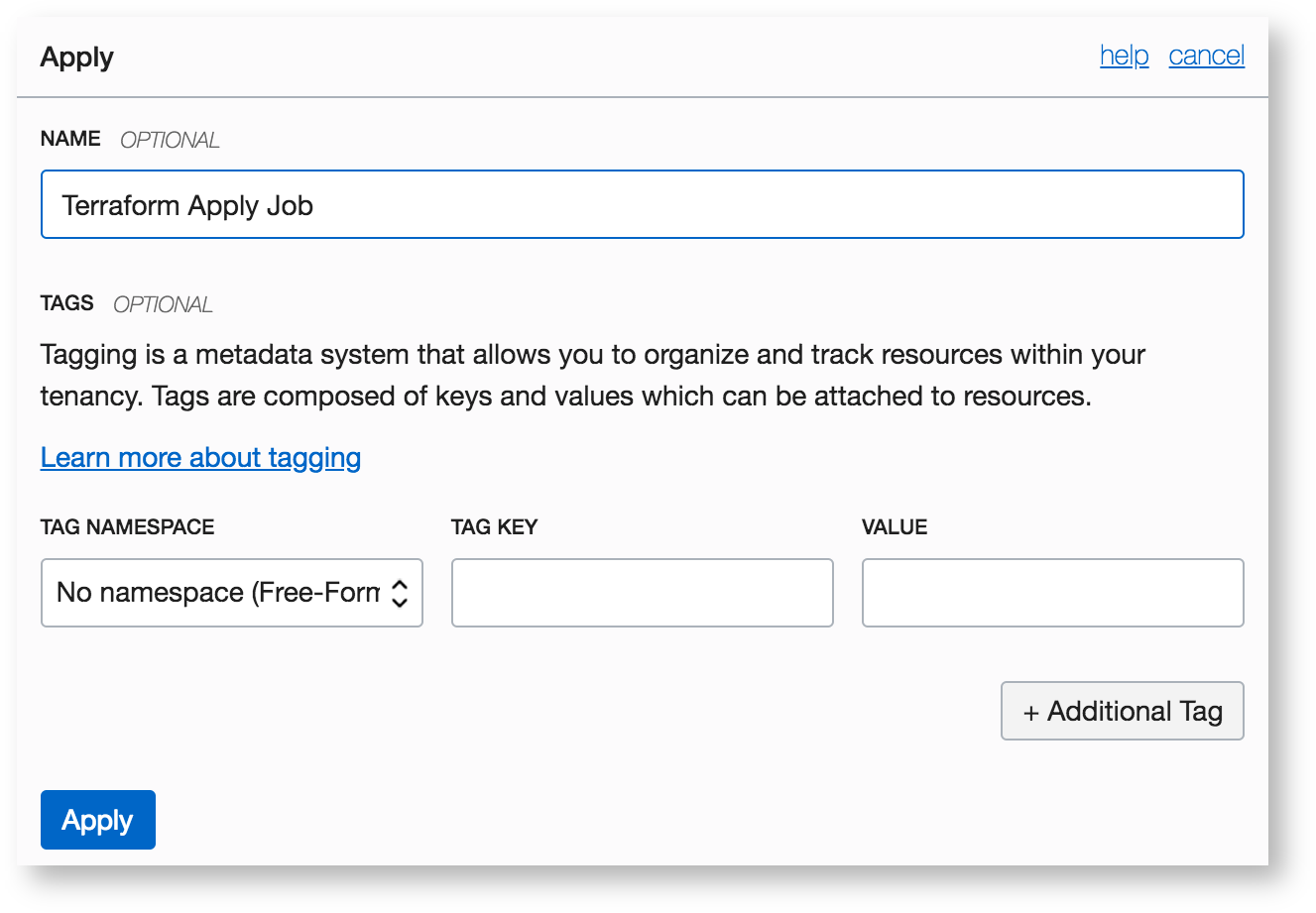
-
Make any necessary changes in the dialog box, and then click Apply.
The job’s state is updated as the job execution nears completion.
-
After the apply action succeeds, verify that the resources have been provisioned by reading the Terraform output contained with the logs. You can also navigate to the Networking section of the Console to view the different resources that now exist (VCN, load balancer, subnets, and so on), and to the Compute section to view the two instances.
Now that we’ve successfully applied Terraform to build some cloud resources, we can use Resource Manager to release them.
-
From the Terraform Actions menu, select Destroy.
-
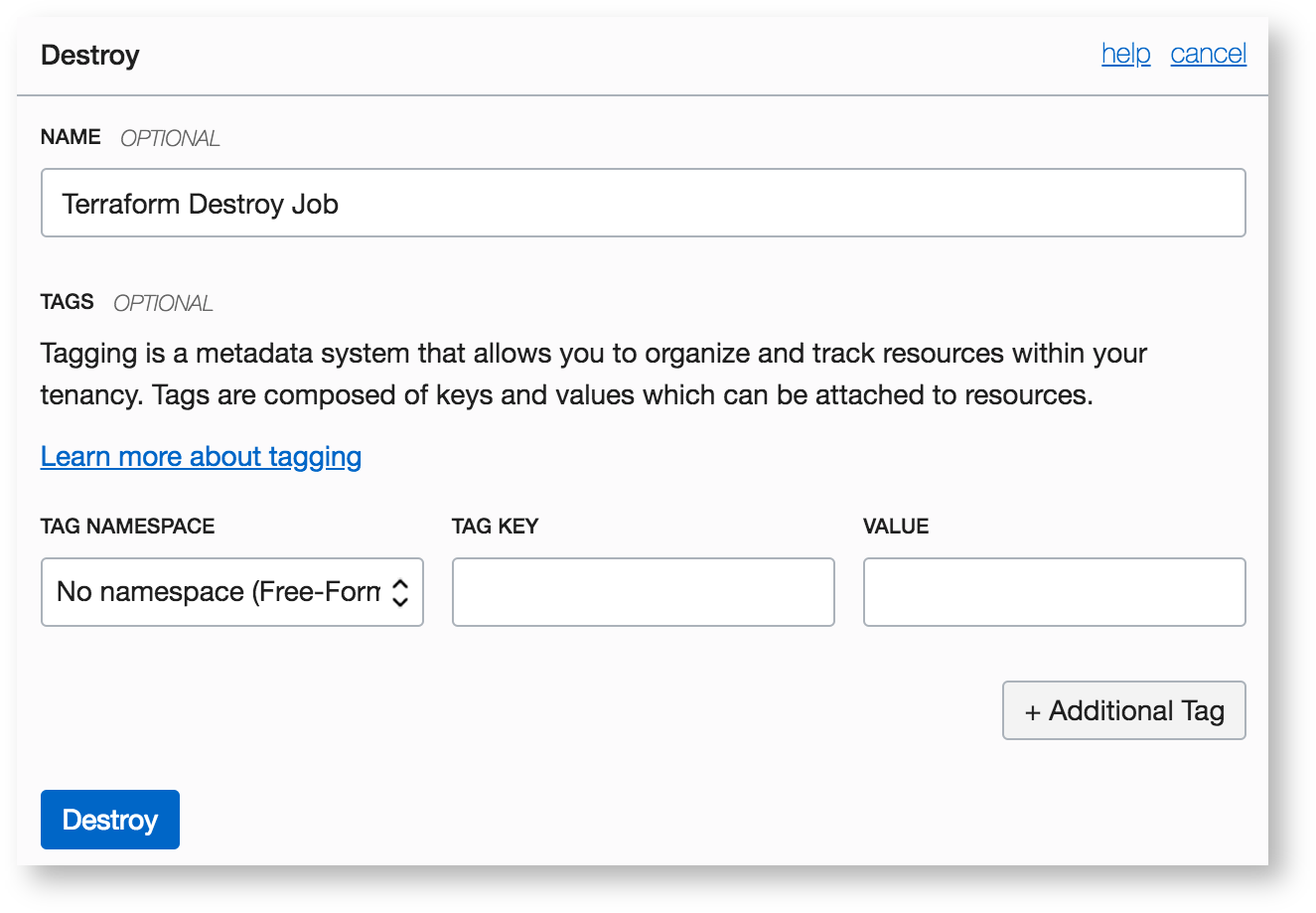
In the Destroy dialog box, accept the defaults (or customize the values) and then click Destroy.
The state change is reflected in the console.
-
To verify that the command completed successfully and that all resources are released, click the job name and view the Terraform output in the logs.
Step 4: Delete the Stack
On the Stack details page, click Delete Stack. In the confirmation message that appears, click Delete to confirm the action.
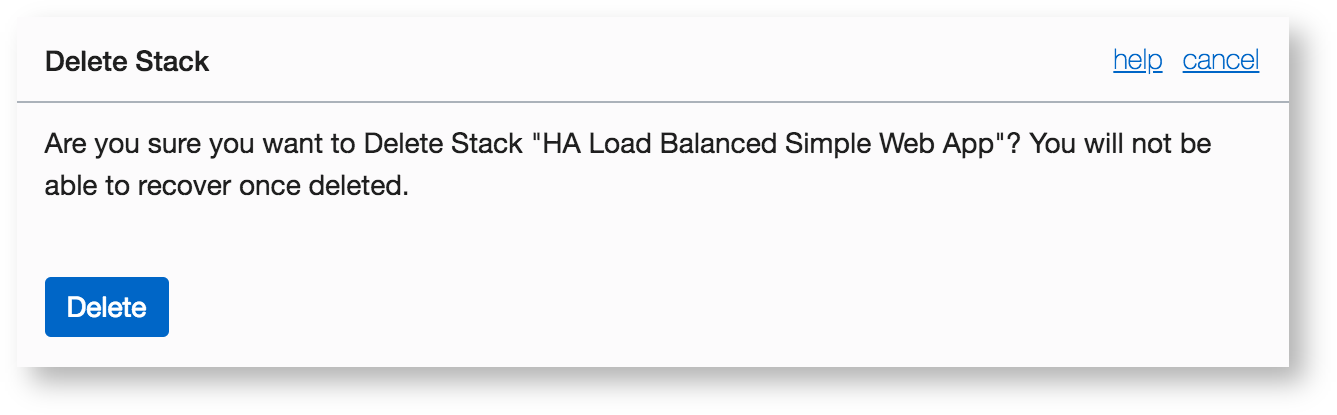
The stack disappears from the list of stacks.
Wrapping Up
There is a lot of history and momentum behind Oracle’s commitment to open source, and Oracle Cloud Infrastructure is making rapid progress in building out a truly open public cloud platform. See it yourself by creating a free account with up to 3,500 free hours.