Ransomware attacks aren’t just about data theft — they’re about denying access to your most critical systems until you pay. And when both production and disaster recovery environments are compromised, traditional backup strategies often fall short.
So what actually works?
The answer is a cyber resilient architecture built around two key components: a Cyber Vault and Clean Room as shown below.
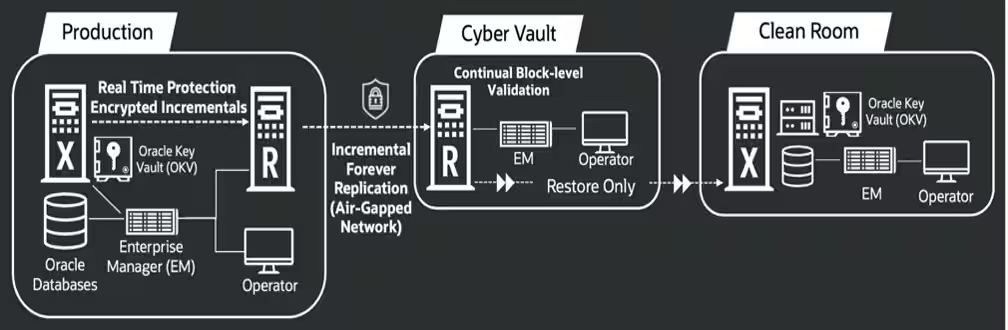
For Oracle databases, especially environments with large numbers/sizes ranging into 100s of databases totaling several PBs or more, effectively managing backup replication process into the vault, validating their recoverability, and driving performance during recovery at-scale can be a challenging proposition. With Oracle’s Zero Data Loss Recovery Appliance, these activities are handled much more efficiently with much better recoverability by design through unique, database-integrated capabilities.
Read on for a short discussion of key considerations in a cyber vault and clean room architecture, and how Recovery Appliance adds value.
Protect What Matters with a Cyber Vault
A Cyber Vault is your last trusted copy of data, isolated from compromises that could impact production and network-connected DR environments.
Unlike standard backups, it is:
- Physically or logically isolated (air-gapped)
- Accessible only through tightly controlled, temporary connections
- Protected with immutable backup policies and strict access controls
In Oracle’s architecture, backups are replicated into the vault only during short, controlled windows, minimizing exposure. This ensures that even if attackers compromise production systems, they cannot reach or corrupt vault data. The vault isn’t just storage—it’s your anchor of trust when everything else fails.
The Recovery Appliance offers a built-in Virtual Air Gap capability, where backups are efficiently replicated with incremental forever strategy, dramatically reducing transfer time and storage consumption compared to full backups, in some cases 10X savings or more. This strategy minimizes the time the vault must be open to synchronize with production backups and thus minimizes potential exposure to network attacks.
Replication network access to the vault is based on a user-specified time interval when it needs to be open (e.g. 2 hours for each access window). Normally, access to the vault is closed. When open, queued backups on the source appliance are immediately replicated to the vault appliance. When the time interval expires (e.g. 2 hours), the replication process is paused and network closed. The source appliance communicates with the vault appliance to track which backups have successfully replicated and which are queued to be replicated the next time the network opens. Review this blog for a walk through of the Virtual Air Gap setup and operational steps, in addition to this documentation section for further details on the management commands.
Rebuild Safely in a Clean Room
Once a breach occurs, the challenge isn’t just restoring data—it’s restoring trusted data.
That’s where the Clean Room comes in.
A Clean Room is an isolated recovery environment where:
- Backups are restored from the vault
- Data is validated and scanned
- Critical applications are brought online safely
It acts as a temporary production environment, allowing businesses to resume minimum viable operations while the compromised systems undergo forensic investigation before they can be reverted back to production usage.
For a clean room, critical assets and infrastructure to consider are:
Database
- Exadata: Oracle enterprise database platform that runs Oracle Database workloads of any scale and criticality with high performance, availability, and security. It serves as the foundation of Oracle’s Exadata Database Service, offered in OCI and Cloud@Customer.
- Exadata Cloud@Customer: on-premises offering that brings the performance, automation, and economics of Exadata Database Service and the fully managed Autonomous Database into enterprise data centers.
- Oracle Database Appliance: affordable database platform for small and mediumsized organizations and business units, including those with distributed locations, to deploy and manage their databases, applications, and infrastructure.
Applications
- Compute Cloud@Customer (C3) – designed for scalable application server performance with convenient, subscription-based usage. C3 allows customers to activate server resources only when needed.
- ZFS – high-performance network attached storage system for application data, consolidating file, block, and object storage on a single platform.
Backup/Recovery
- Recovery Appliance – the appliance in the vault continuously validates incoming replicated backups and after they are stored on-disk. This process checks integrity of all database blocks and verifies that all files required for complete recovery are available.
Databases in the clean room are restored by simply connecting to the Recovery Appliance whose catalog tracks all the stored backups. Each incremental backup replicated yields a new virtual full backup on the appliance in the vault, which is equivalent to a physical full backup from restore perspective. This unique database optimization means that multiple days of incrementals are no longer needed during the recovery process. With just a one-step restore and recovery of the virtual full backup, the database can then be opened for access shortly thereafter.
A separate Recovery Appliance in the Clean Room can protect databases after being recovered and opened for workloads. Once production has been analyzed post-compromise and returned back to usable state, these appliances can be setup for replication – again with efficient incremental forever – so that production appliance is readily synchronized with latest backups from the activated clean room environments.
Controlled Recovery Process
Finally, a vital part of the architecture design is to think through key phases of the overall recovery process:
- Containment
- Isolate compromised systems
- Shut down access and close vault connectivity
- Eradication
- Remove threats and disable compromised accounts
- Recovery to Clean Room and Activation
- Restore data from the vault
- Validate consistency across databases and applications
- Bring critical services online
- Rebuild Production
- Restore full systems after forensic validation
- Sync clean data back into production
This structured approach ensures that recovery is secure, verified, and controlled, not rushed or risky.
The Real Insight: Recovery Is the New Security Boundary
Ultimately, this architecture is much more than just what tools to use — it’s about mindset.
Traditional thinking centers around:
- Prevent breaches
- Protect production
The modern reality is:
- Assume compromise
- Design for recovery
Resilience isn’t defined by whether you get attacked — it’s defined by how quickly and safely you can come back. A cyber vault and clean room environment built on Oracle’s Zero Data Loss Recovery Appliance as the foundation for database protection and recovery offers unique capabilities for fast, efficient replication into the vault based on incremental forever strategy, continuous Oracle block-level recovery validation of backups, and to drive performance during recovery at-scale through innovative virtual full restore technology.
For more information, check out Oracle AI Database Protection and Resiliency solutions overview, Zero Data Loss Recovery Appliance product central, and the Zero Data Loss Recovery Appliance Deployment with Cyber Vault and Clean Room technical brief.