Security is a high priority for all customers. At Oracle Cloud Infrastructure, we are constantly building new capabilities to enhance cloud security. This post discusses network security groups (NSGs), which provide granular controls to help you define the security posture for your resources in a virtual cloud network (VCN).
You can now create an NSG as a logical group of resources with a common function and then apply minimal ingress and egress security rules specific to that function. These resources can exist in any subnet within a VCN.
At a high level, this feature enables:
- Simplified security configurations with the introduction of an NSG as a source or destination for a security rule
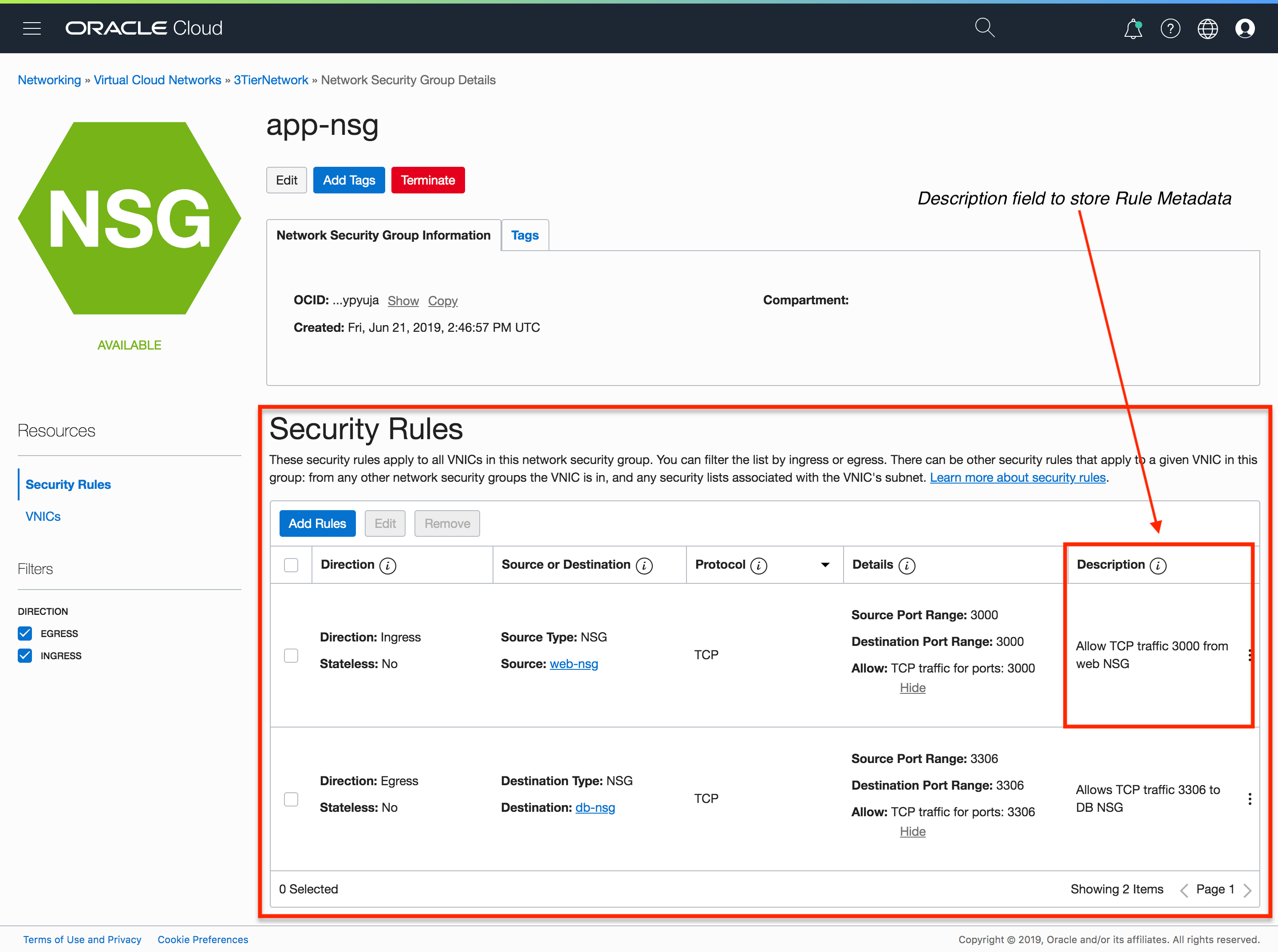
- Rule sets with a description field for storing metadata
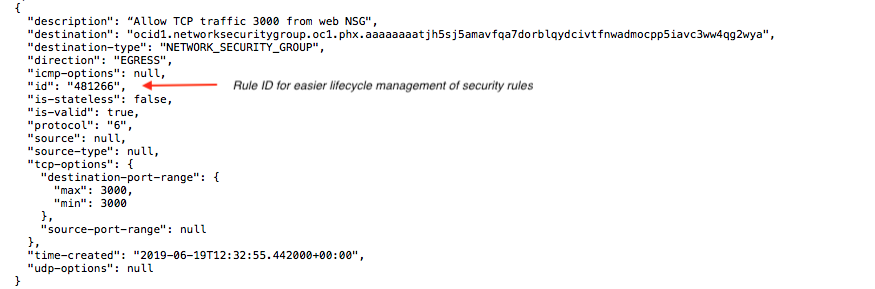
- Improved lifecycle management of security rules with the introduction of a rule ID and a last-modified timestamp
- Capabilities to set up granular Identity and Access Management (IAM) policies that enable enterprises to configure granular access control to users
How Do NSGs Improve Security Lists?
Security lists let you define a set of security rules that apply to all the VNICs in a subnet. To use a given security list with a particular subnet, you associate the security list with the subnet either when you create the subnet creation or later. Any VNICs that are created in that subnet are subject to the security lists associated with the subnet.
NSGs let you define a set of security rules that apply to a group of VNICs that belong to a compute instance, load balancer, or DB system. For example, you can add the same NSG to a list of compute VNICs that require the same security posture. Any VNIC added to that group is subject to that group’s security rules.
Note: When both a security list and an NSG are created and added to a compute VNIC, the VNIC is subject to the union of the rule. For example, if the security list allows SSH traffic and the NSG allows HTTP traffic, both SSH and HTTP traffic are allowed by Oracle Cloud Infrastructure.
When to Use an NSG
Security lists provide comprehensive security to applications with security rules applied at every subnet. But if you have multiple resources that require different security postures within a given subnet and you need to control traffic at a more granular application level, an NSG lets you create these granular rules and add multiple resources to them.
For example, consider a three-tier web application in which the web/proxy tier is deployed in the public subnet, and the application and database tiers are deployed in the private subnet. To secure the application tier, you can create granular security rules to control the traffic that enters the application and then apply the same rules to the application VNICs.
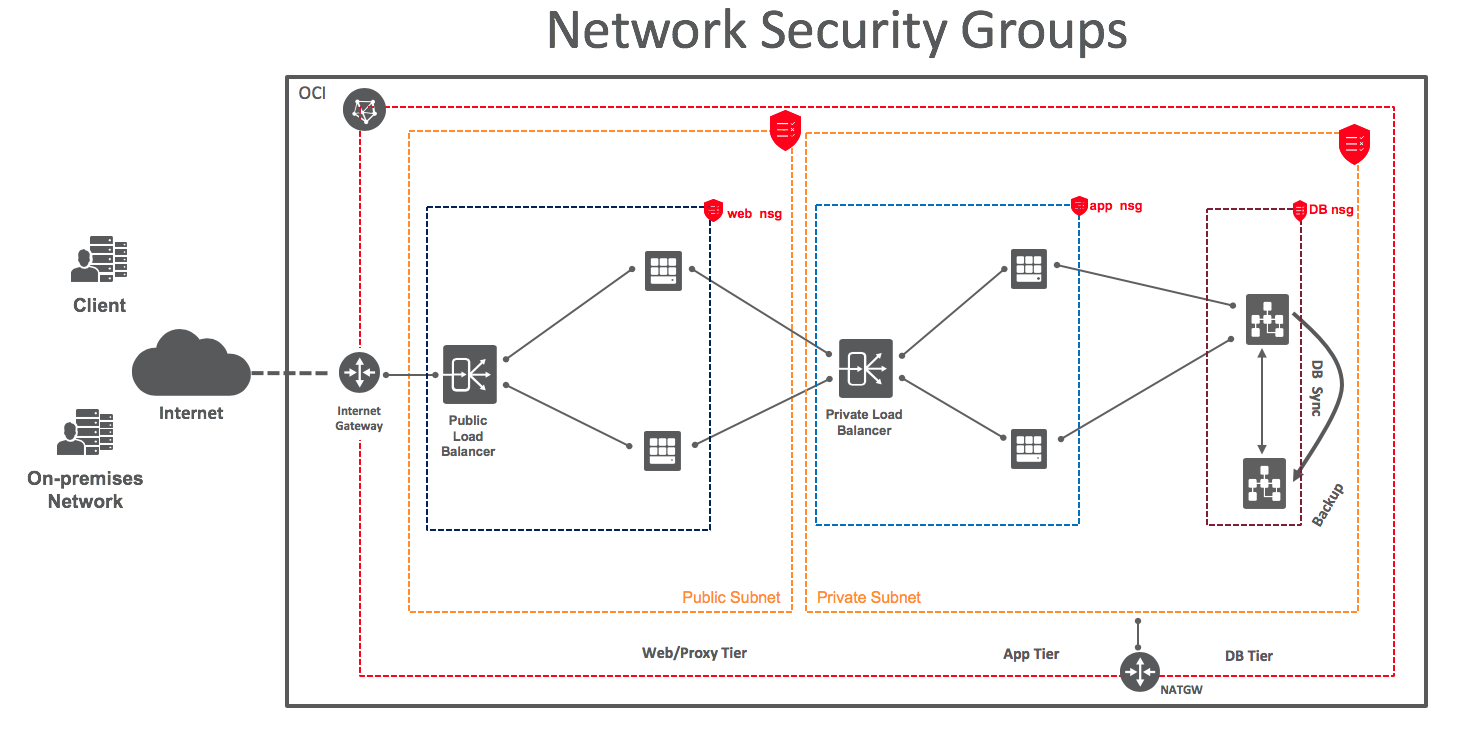
Note: Multiple resources that belong to a single subnet or different subnets can be a member of the same NSG if they belong to the same VCN.
Configuring and Associating an NSG with an Application
This section walks you through the steps to configure an NSG and add it to a three-tier application. We are using the 3Tierapp Terraform template to deploy the application.
Here is a quick view of the steps involved:
- Create the NSG
- Create Security Rules and Add Them to the NSG
- Add an Instance VNIC to an NSG
Step 1: Create the NSG
Using the Oracle Cloud Infrastructure CLI, you can create the NSG as follows. OCIDs are Oracle Cloud Identifiers.
oci network NSG create --compartment-id <compartment_ocid> --vcn-id <vcn_ocid> --display-name app-NSGTo use the Oracle Cloud Infrastructure Console instead of the CLI, follow these steps:
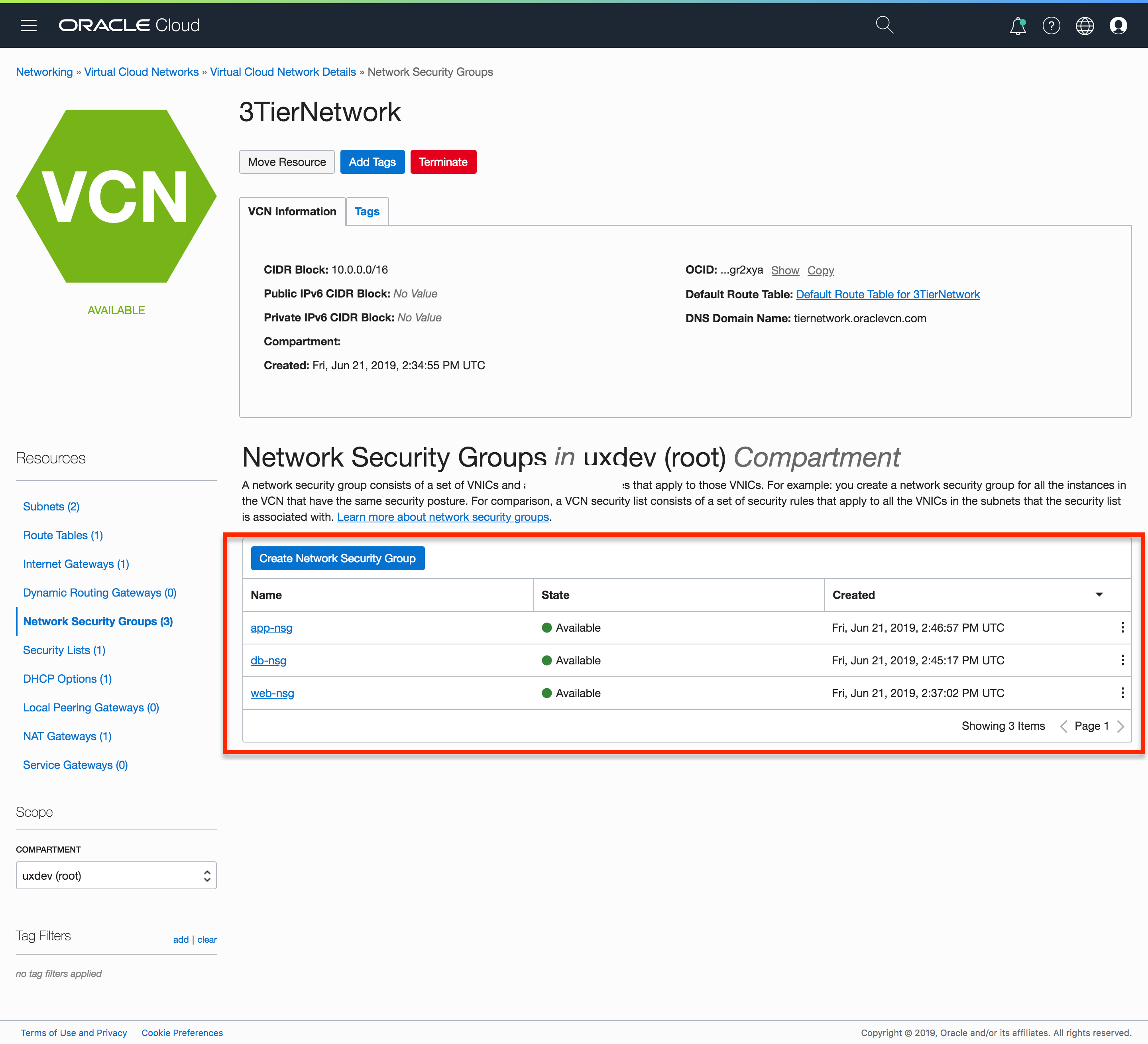
- Open the navigation menu. Under Core Infrastructure, go to Networking and click Virtual Cloud Networks.
- Click the VCN you’re interested in.
- Under Resources, click Network Security Groups.
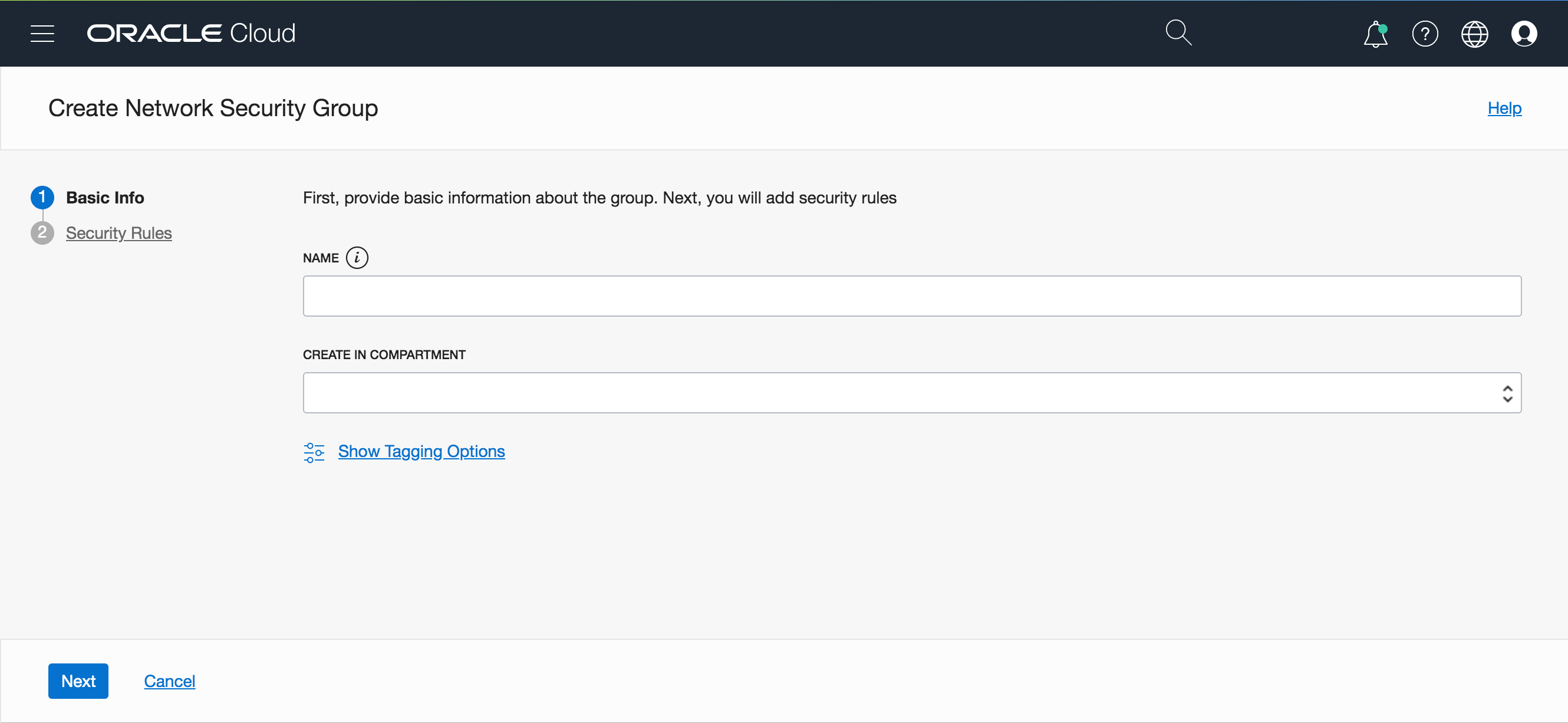
- Click Create Network Security Group.
- Provide the basic information, click Next, and then click Create.
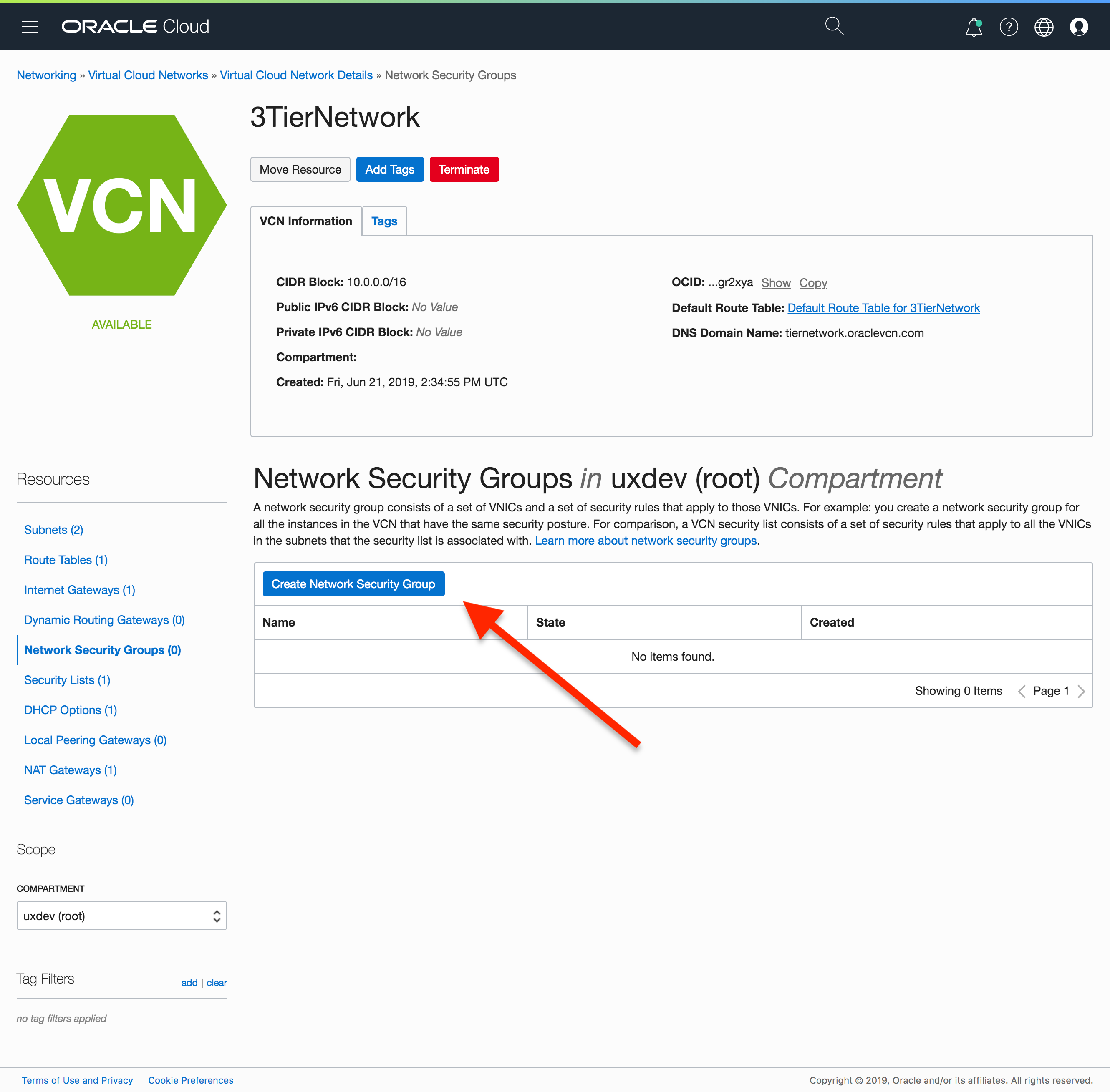
Follow the previous steps to create the web tier and database (DB) tier NSGs before proceeding to the next step.
The NSG doesn’t have any security rules added to it, so let’s create security rules next.
Step 2: Create Security Rules and Add Them to the NSG
To secure an application, you define a set of rules to control the traffic to and from the application.
The 3Tier application that we deployed using the Terraform template consists of a web-tier application that listens to all incoming traffic on port 9000. It proxies requests to the app tier on port 3000, which in turn queries the database on port 3306 to display the content on the web application.
The security rules for the three tiers are as follows:
| Direction | Type | Source/Destination | Port |
|---|---|---|---|
| Ingress | CIDR | All Traffic | 9000 |
| Egress | NSG | OCID of App Tier NSG | 3000 |
| Direction | Type | Source/Destination | Port |
|---|---|---|---|
| Ingress | CIDR | OCID of Web Tier NSG | 3000 |
| Egress | NSG | OCID of DB Tier NSG | 3306 |
| Direction | Type | Source/Destination | Port |
|---|---|---|---|
| Ingress | CIDR | All Traffic | 3306 |
Use the following steps to create the rules for the app tier applications, using the CLI or the Console.
Using the CLI
When you use the CLI to create a security rules and associate the rules with the NSG, you need to define the rules by using a JSON language. You can find sample JSON NSG rules at app.json.
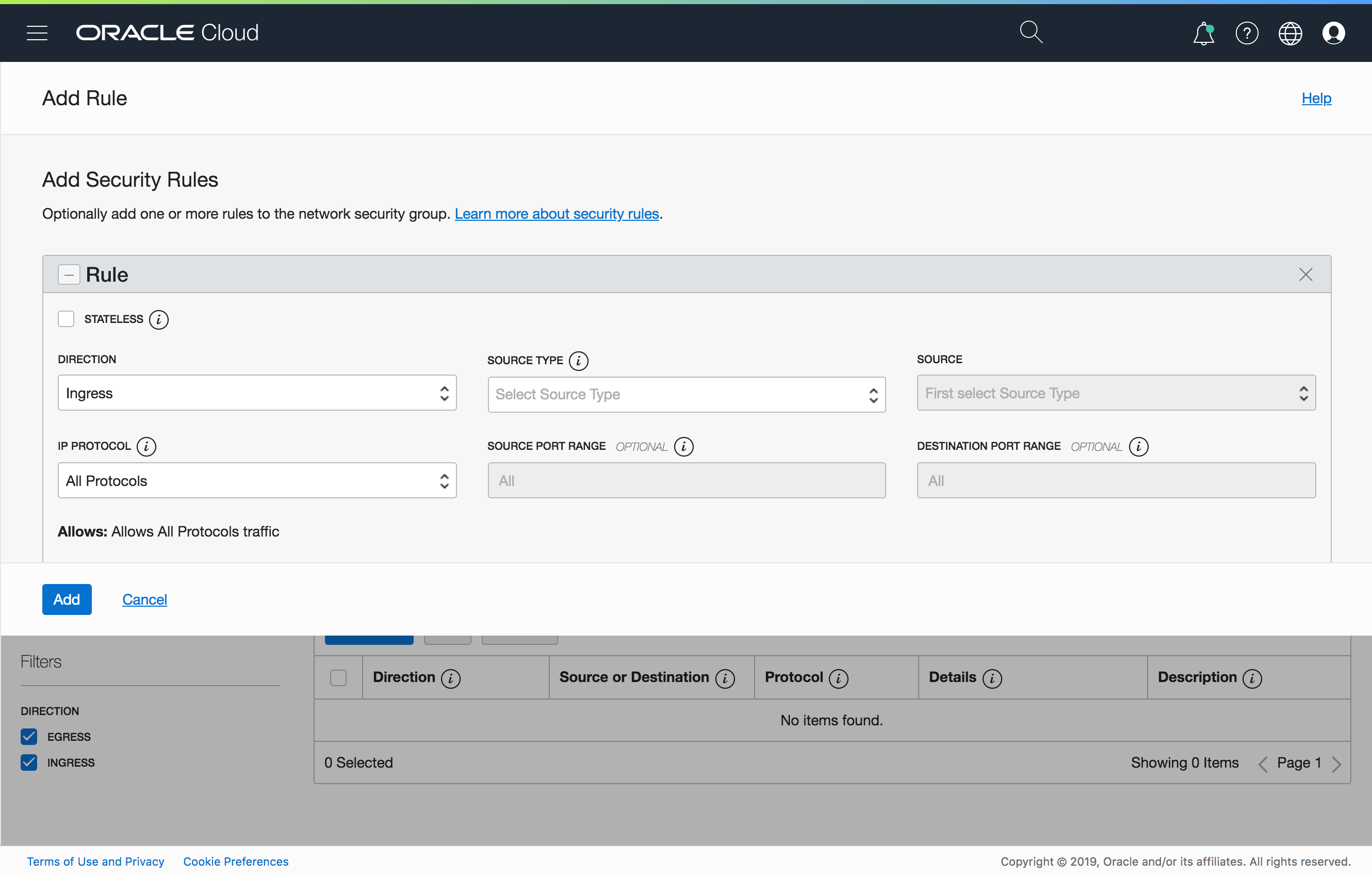
oci network NSG rules add --NSG-id <app_nsg_ocid> --security-rules file://app.jsonUsing the Console
- Navigate to the NSG that you created in Step 1.
- Click Add Rules, and create app-specific security rules based on the previous table. You can also define a rule metadata by using the description field.
Follow similar steps to create the web tier and DB tier security rules. See sample web and DB security rules.
Step 3: Add an Instance VNIC to an NSG
Now that you have deployed the three-tier app and created the NSG rules, you can add the NSG to the compute VNIC.
Using the CLI
oci network vnic update --vnic-id <app_vnic_ocid> --NSG-ids <app_nsg_id>Using the Console
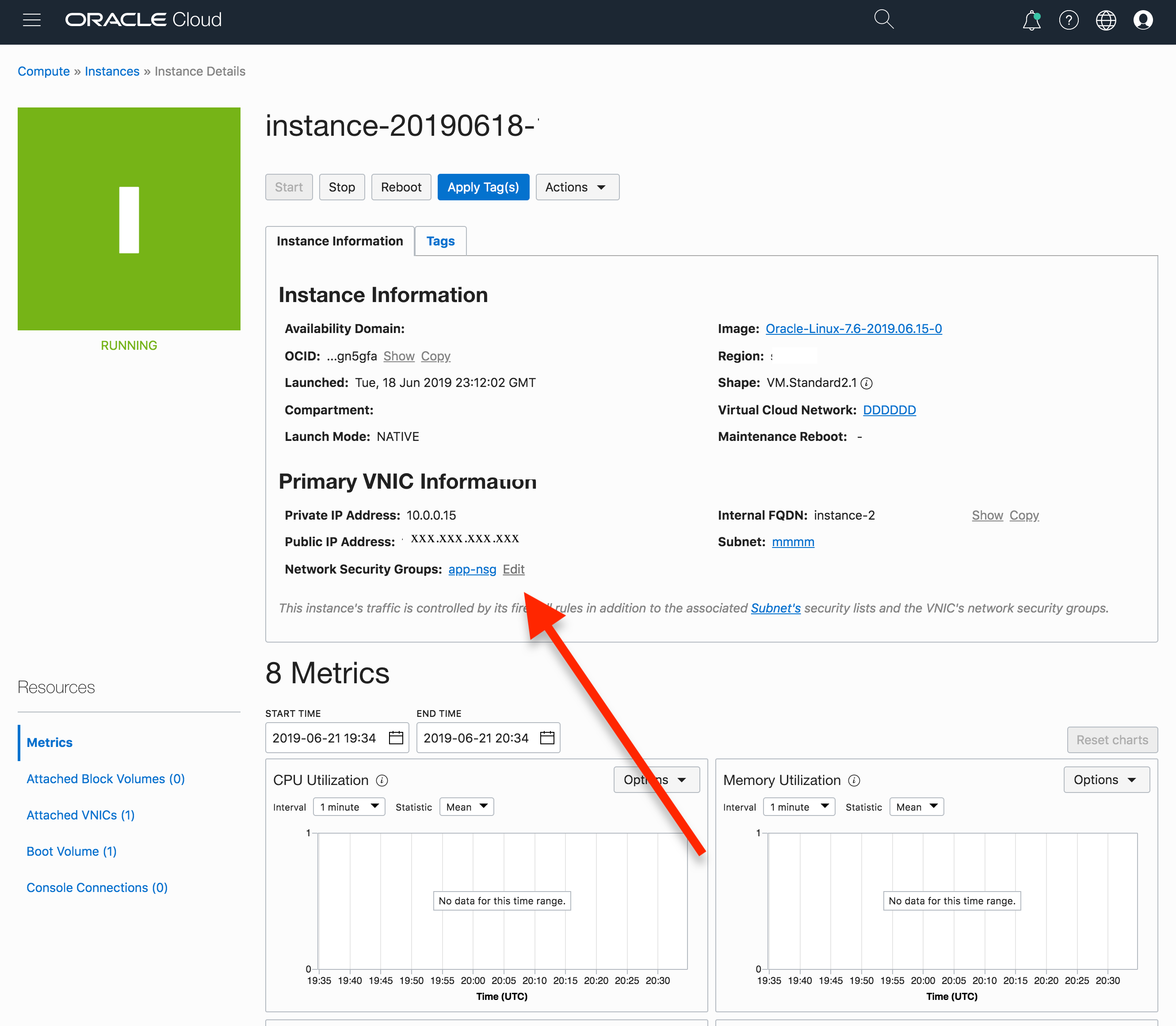
- Navigate to Compute > Instances, and click the instance. The network security groups are shown in the Primary VNIC Information section of the details page.
- Click Edit, select the NSG from the list.
Now you have created the NSG rules and have added the app tier compute instance to the app NSG. Follow the same steps to create the web tier and DB tier NSG rules and add the respective app tier resources to the NSG (if you haven’t created the web and DB NSG rules yet).
If you want to use an automated script to guide you through the process of creating the NSG and putting the resources into the NSG, you can use a sample script.
Verification Steps
After the NSG is created and the VNICs are added to the NSG, you can verify all the resources created by using the CLI or the Console.
Step 1: Verify the List of NSGs
Using the CLI
oci network NSG rules list --NSG-id <nsg_rule_ocid>Using the Console
- Navigate to Networking > Virtual Cloud Networks.
- Click the VCN.
- Under Resources, click Network Security Groups.
Step 2: Verify That the Rules Are Added to the NSG
Using the CLI
oci network NSG rules list --NSG-id <nsg_rule_ocid>Using the Console
Click the name of the NSG to view the security rules.
Step 3: Verify That the VNICs Are Put into the NSG
oci network NSG vnics list --NSG-id <nsg_rule_ocid>Step 4: Verify That the Security Rules Are Enforced
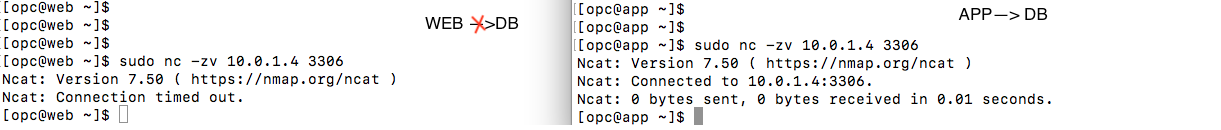
To verify security rule enforcement, verify that app tier VM can connect to port 3306 on the database tier, but the web tier can’t connect to the same port on the database tier.
Conclusion
I hope that you enjoyed this introduction to network security groups! Now when you design your applications on Oracle Cloud Infrastructure, you can leverage a holistic suite of security features that let you secure the network at VCN/subnet level or the VNIC level.
Feel free to use the Terraform template that creates the three-tier app and adds the network security groups to the application tiers.
You can find more information regarding NSGs in the NSG documentation