Securing ERP and HCM requires more than monitoring infrastructure logs. As AI agents, service accounts, employees, partners, customers, and job applicants around the world perform sensitive transactions in Oracle Fusion Applications, security teams need to harden their cybersecurity posture at the application layer, helping prevent and detect breaches while providing demonstrable assurance to executives.
This requires a practical five-step approach: (1) monitor sensitive transactions and account activity across payments, invoices, payroll, supplier bank account changes, customer master data, and HR setup changes, especially for IT superusers and service accounts; (2) certify privileged access and confirm whether high-risk activity was authorized and compliant; (3) surface toxic combinations and separation of duties (SoD) violations; (4) evaluate risky access before it is granted; and (5) route high-risk findings to business owners and SecOps for rapid review.
The CIS Oracle SaaS Cloud Applications Benchmark v1.0 provides practical guidance for Oracle Fusion Cloud. Risk Management, a fully integrated Fusion module, helps automate that guidance with more than 100 prebuilt security algorithms aligned with CIS Critical Security Controls, including access revocation (6.2), role-based access control (6.8), and detailed audit logging (8.5).
These algorithms help CISO teams move beyond log parsing to application-aware posture management. Traditional methods often apply the same type of analysis across very different types of workloads, from infrastructure (storage, virtual machines, networking) to SaaS tools like Slack and Zoom, and SaaS business applications like ERP and HCM. However, for ERP and HCM, this approach can increase alert volume without providing clear signals for sensitive data exposure, privilege misuse, and configuration drift.
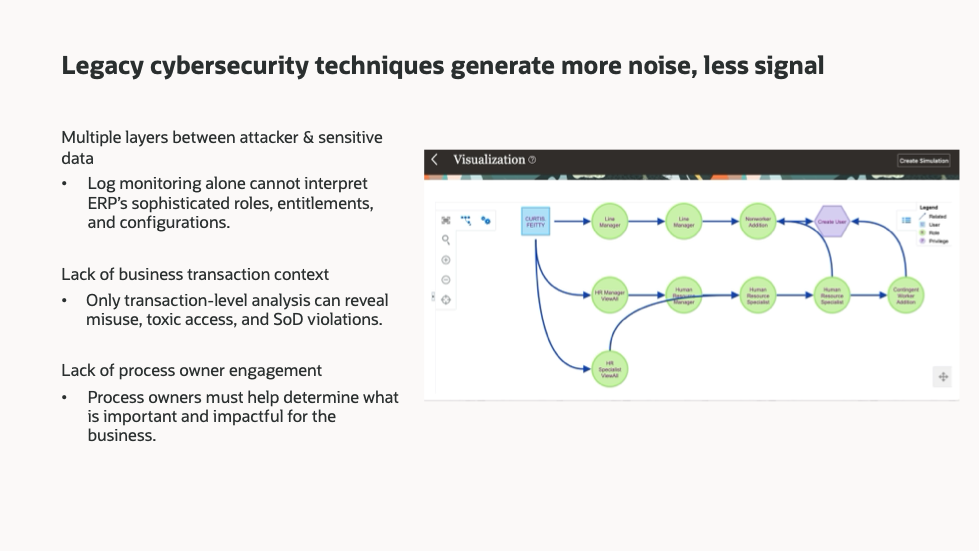
This gap exists because structural and architectural differences are not always accounted for. SaaS business applications such as ERP and HCM have sophisticated functional and permission models, distinct usage and configuration patterns, and multiple layers of structure between attackers and sensitive data. These differences make infrastructure-style log monitoring difficult to operationalize for credible assurance. Oracle Fusion Cloud Risk Management’s prebuilt algorithms analyze Fusion ERP and HCM data, which represents the innermost layer in a defense-in-depth model. This application-aware analysis is supported by a security graph that ingests more than 30,000 attributes to build millions of connections for analysis.
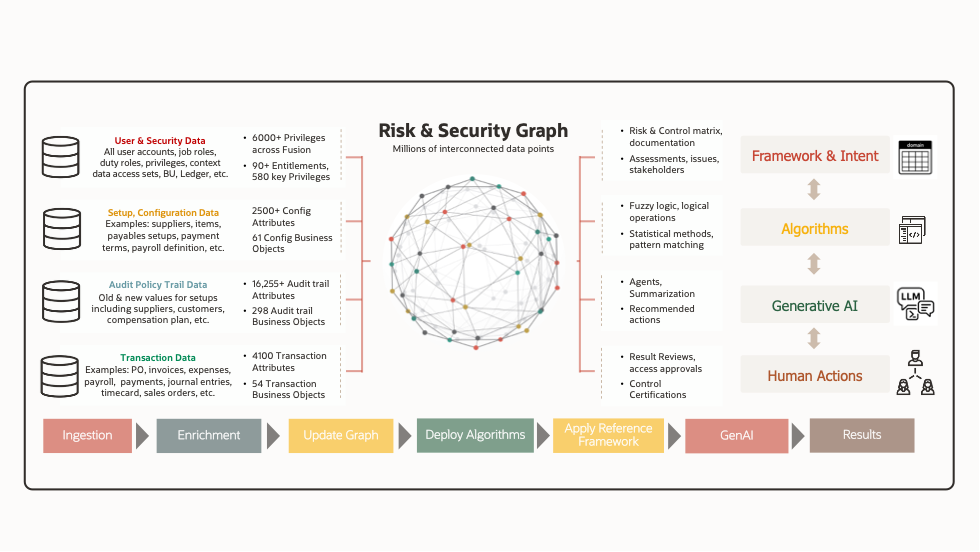
Monitoring business transactions and actual access usage provides clearer cybersecurity signals to track sensitive or restricted access concerns, privilege escalation, configuration drift, toxic combinations, and separation of duties (SoD). It also helps organizations demonstrate assurance with evidence to business executives and external auditors.
Five Steps to Strengthen Fusion Security Posture
Step 1: Track IT administrator transactions
CIS recommendation: 5.1.1
Effort to activate: 4 to 8 hours
IT administrators need elevated permissions to keep ERP and HCM environments running, but that access can become more sensitive when it overlaps with business-critical permissions such as payments, supplier management, or payroll. As organizations expand automation and integrations, the same visibility also needs to extend to non-human accounts, including integration and service accounts.
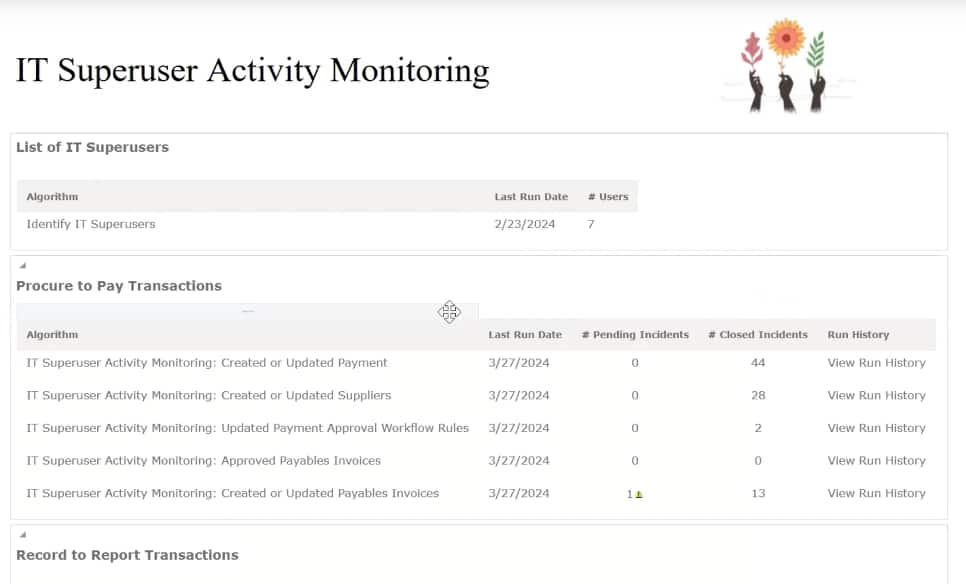
Oracle Fusion Cloud Risk Management includes prebuilt algorithms that help continuously monitor users with elevated IT administrator permissions, including users with combined Fusion and Oracle Cloud Infrastructure (OCI) administrator access. These algorithms track business transactions performed by IT administrators, flag changes to audit configurations, and create issues for tracking and closure when policy violations are detected.
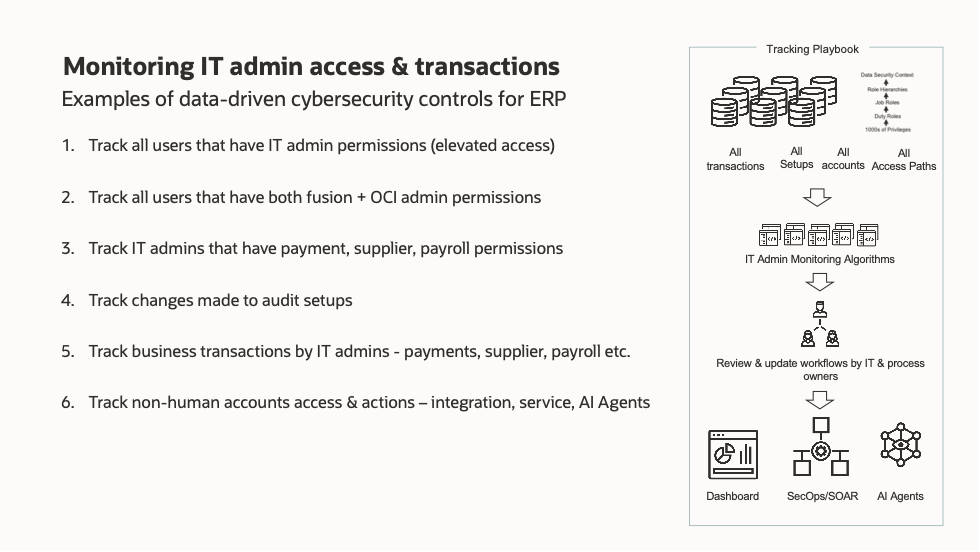
This helps teams maintain visibility across both human and automated access, with an audit trail that can support investigation, remediation, and evidence needs. Once configured, results are shared through dashboards with drill-down capabilities for detailed review and end-to-end issue management. Alerts can also be sent to security orchestration, automation, and response (SOAR) systems through representational state transfer (REST) web services, connecting Fusion application-layer findings with broader security operations workflows (see Step 5).
Step 2: Ensure privileged access is certified periodicall
CIS recommendation: 1.7
Effort to activate: 15 minutes
Privileged access can change as employees change jobs, take on new responsibilities, or support different business processes. Periodic and targeted access reviews help organizations validate that user role assignments remain appropriate over time and align with security and compliance expectations.
Oracle Fusion Cloud Access Certifications enables organizations to review and validate user role assignments through certification campaigns, drawing on data from Oracle Fusion Cloud Applications, Oracle Enterprise Performance Management (EPM), and OCI.
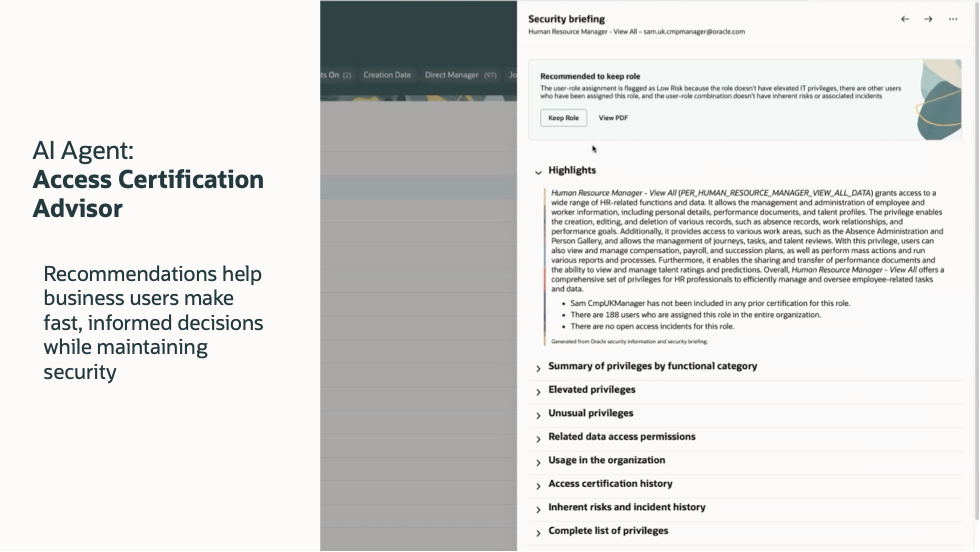
For each user-role combination, Access Certification Advisor uses generative AI to create a detailed Security Briefing that supports the certification decision. The briefing can include a recommendation to keep or remove the assignment, a justification comment, and a one-click option to accept the recommended action.
This helps reviewers make informed decisions more efficiently, while helping teams maintain evidence that privileged access is reviewed and governed on a periodic or targeted basis.
Step 3: Ensure sensitive access and toxic combinations are monitored
CIS recommendations: 5.2.1 and 5.3.1
Effort to activate: 15 minutes
Sensitive access in ERP and HCM is often more complex than a single role assignment. A user may have access to high-value business functions, hold privileges that create separation of duties concerns, or perform transactions that require review based on internal policy.
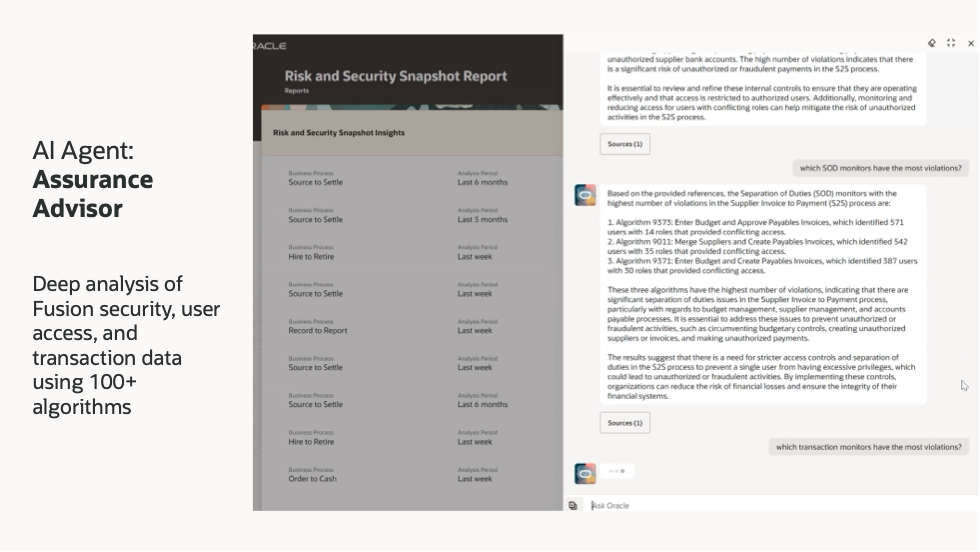
The Oracle Risk and Security Snapshot Report gives organizations a fast, comprehensive view of access and transaction risk across key business processes. It uses more than 100 Oracle-developed algorithms to identify accounts with sensitive access, roles with inherent toxic or separation of duties risk, and transactions showing evidence of fraud or policy violations, with no custom risk logic required.
These same algorithms can be activated for continuous monitoring, with findings automatically sent to SOAR platforms for incident tracking and response.
Four Assurance Advisor AI agents extend this further: Source to Settle, Order to Cash, Record to Report, and Hire to Retire. They allow security teams and process owners to query findings in natural language. This helps accelerate risk identification and executive reporting across the organization.
Step 4: Enable access requests with preventive controls and AI
CIS recommendations: Multiple – see appendix
Effort to activate: 15 minutes
Manual ERP role provisioning can create delays, inconsistent approvals, and limited visibility into separation of duties risk before access is granted. Preventive controls help organizations evaluate access earlier in the request process.
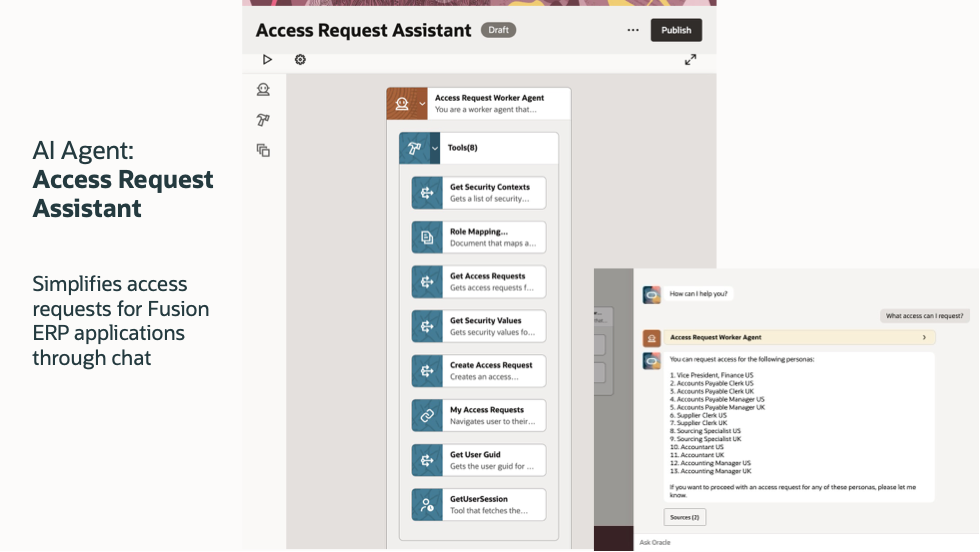
Advanced Access Requests replaces manual ERP role provisioning with a single automated workflow covering role assignment, data security, separation of duties analysis, and business-owner approval.
The Access Request Assistant uses generative AI to let users request access in natural language. This eliminates the need for business users to know cryptic role names or security context values, and it automatically triggers the full provisioning and separation of duties analysis workflow upon submission.
Step 5: Integrate ERP and HCM security signals with SecOps
CIS recommendations: Multiple – see appendix
Effort to integrate: A few hours to days
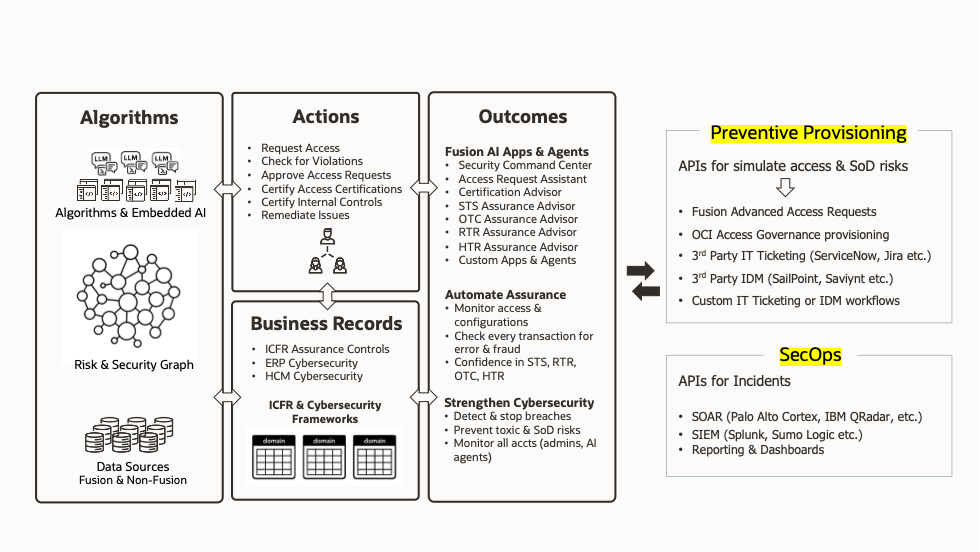
ERP and HCM security findings are most useful when they can flow into the systems that cybersecurity teams already use to review, track, and resolve issues. Oracle provides REST-based application APIs for both preventive provisioning and security operations integration.
On the provisioning side, APIs simulate access and separation of duties risks before roles are granted. These signals can feed workflows across Fusion Advanced Access Requests, OCI Access Governance, third-party IT ticketing systems such as ServiceNow and Jira, identity management platforms such as SailPoint and Saviynt, and custom workflows.
For security operations, APIs push incidents directly into SOAR platforms such as Palo Alto Networks Cortex XSOAR, security information and event management (SIEM) tools such as Splunk, and reporting dashboards. This enables end-to-end integration across the security operations stack.
Conclusion
Security posture management for Fusion ERP and HCM is most effective when application-specific controls are easy to activate, review, and connect to existing security workflows. Oracle Fusion Cloud Risk Management helps organizations put CIS Benchmark guidance into practice with prebuilt algorithms, access certification, preventive controls, AI-assisted analysis, and security operations integration.
For a deeper view of the recommended controls, refer to the CIS Oracle SaaS Cloud Applications Benchmark v1.0 and identify which recommendations strengthen security posture using automation and AI for Oracle Fusion Cloud ERP and HCM.
Additional Resources
This table maps each CIS Benchmark recommendation that has an “Automated method” to the specific prebuilt algorithms in Oracle Fusion Cloud Applications (including EPM and OCI).
| CIS Recommendation Section | # Algorithms | Example Algorithms |
| 1. Identity & Access Management | All | Advanced Access Requests checks all relevant algorithms below; Access Certifications with open incidents from the algorithms below |
| 4.1 Security Configuration Changes | 8 | 60019 Track When Audit Policy is Disabled; 60008 Additions and Deletions to Data Roles; 60015 Additions and Deletions to Security Profiles; 80001 Custom Roles Not Used |
| 4.2 High-Risk Business Transactions | 6 | Examples: 60002 Frequent Changes to Supplier Bank Account Details; 60007 Changes to Supplier Bank Accounts on a Weekend; 30009 Suppliers with No Invoice Activity; 33004 Customers With No Invoice Activity |
| 4.3 IT Superuser Role Changes | 1 | 60024 New Users Assigned to Application Implementation Consultant Role |
| 5.1 IT Administrator SoD | 22 | Examples: 41001 Approved Payable Invoices by IT Superusers; 42001 Created or Updated Employee Job Assignments by IT Superusers; 9361 Sensitive IT Security Privileges; 4608 Sensitive EPM ARCS Superuser roles |
| 5.2 Application Superuser SoD | 8 | Examples: 4079 Sensitive Human Resource Privileges; 4080 Sensitive Payroll Privileges; 9800 Sensitive Customer Privileges; 9802 Sensitive Payment Privileges |
| 5.3 Application Business User SoD | 60 | Examples: 4051 Manage Employee and Manage Payroll; 5800 Approve Payables Invoices and Create Payables Invoices; 40001 Supplier and Payables Invoices Created by the Same User; 50003 Employee New Hire Created by Same User Managing Personal Payments |
| TOTAL | 105 |


