As data platforms evolve, so do the ways teams collaborate. Data scientists experiment in notebooks, data engineers productionize pipelines, and platform teams ensure everything runs reliably. While this collaboration accelerates innovation, it also introduces a persistent challenge: access sprawl.
Without a structured access model, users accumulate permissions over time, leading to excessive privileges, security risks, and operational confusion. The question is not just how to collaborate, but how to collaborate safely at scale.
Oracle AI Data Platform Workbench addresses this challenge through a robust Role-Based Access Control (RBAC) model. It enables teams to work seamlessly across shared workspaces, notebooks, and jobs—while maintaining precise control over access.
Understanding the AI Data Platform Workbench security model
AI Data Platform Workbench operates on a layered security approach that separates platform access from resource-level control.
At the top level, OCI Identity and Access Management (IAM) governs who can access the AI Data Platform Workbench instances. Once inside the platform, Workbench access control takes over, controlling what users can do within specific resources.
This separation is critical. It ensures that gaining access to the platform does not automatically grant unrestricted access to all resources.
Architecture overview
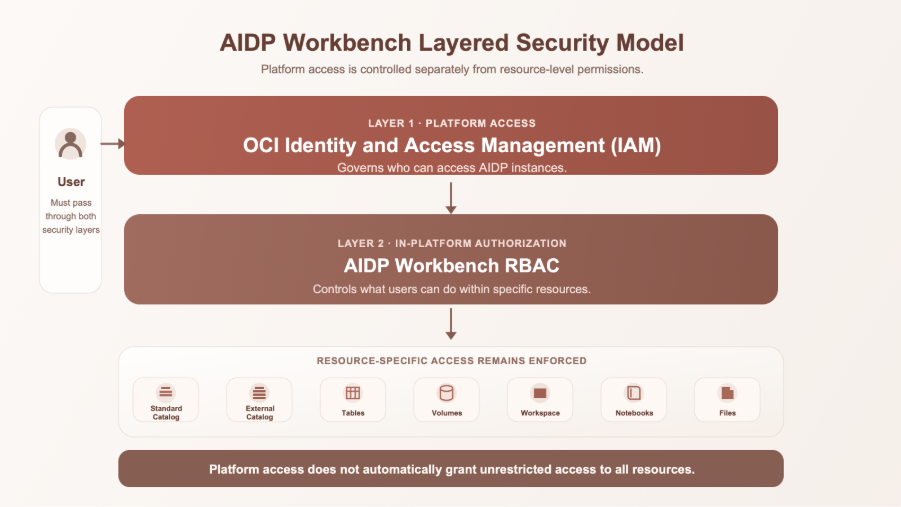
Within Workbench, permissions are applied at the object level and follow a hierarchical model, where workspace administrators have the option to cascade workspace permissions down to all contained resources or apply the permission only on an object.
Workspaces: The foundation of secure collaboration
Workspaces act as the central boundary for collaboration in AI Data Platform Workbench. Every notebook, job, and workflow exists within a workspace, making it the primary unit of access control.
Instead of managing permissions individually for every resource, teams can define access at the workspace level and let it propagate automatically or apply the permissions only on an object.
Workspace roles
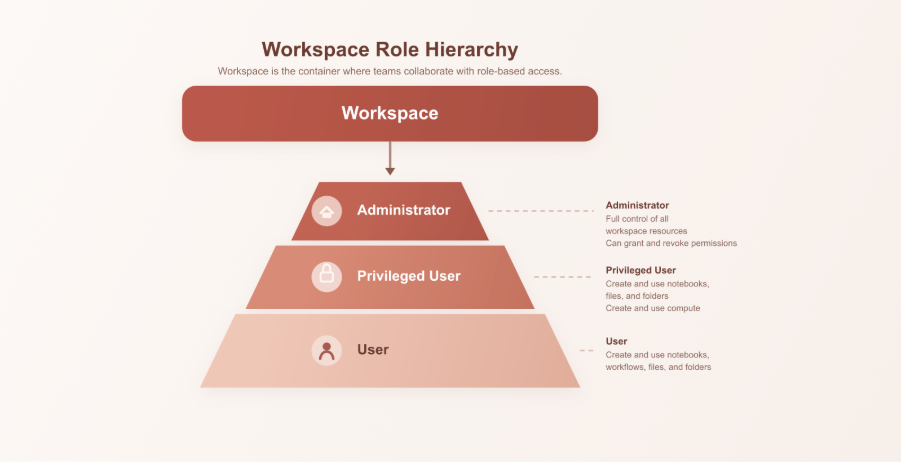
This structure ensures that each participant in a workspace has a clearly defined role. A data scientist may work as a User, while a data engineer might require Privileged User access to manage compute and pipelines.
By anchoring permissions at the workspace level, organizations create a clean and scalable collaboration model.
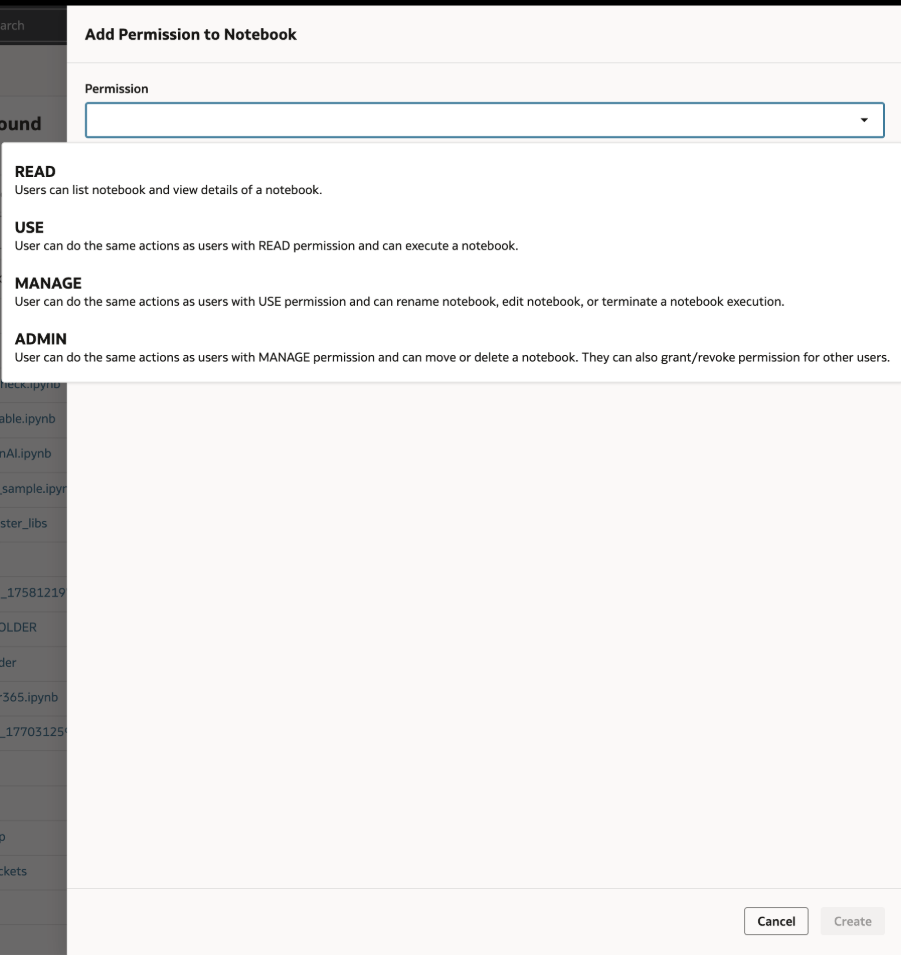
Notebooks: Controlled flexibility for development
Notebooks are where ideas take shape, experiments are run, models are built, and insights are generated. Naturally, they require flexibility. But without controls, they can also become a source of risk.
Role based access control (RBAC) ensures that notebook access is governed appropriately:
- READ: Some users can only view notebooks
- USE: Users can execute notebooks
- MANAGE: Users can edit and execute them
- ADMIN: Move, delete and grant/revoke permissions
This layered control allows multiple users to collaborate without stepping on each other’s work or exposing sensitive logic.
Jobs and Workflows: securing execution at scale
As projects mature, notebook experiments evolve into production jobs and workflows. These pipelines often handle critical data processing tasks, making access control even more important.
Role based access control (RBAC) ensures that only authorized users can:
- Execute jobs
- Modify workflows
- Schedule recurring runs
AI Data Platform’s permission model enforces a clear separation between development and execution. For example, a data scientist may design a workflow, but only an authorized engineer can operationalize it.
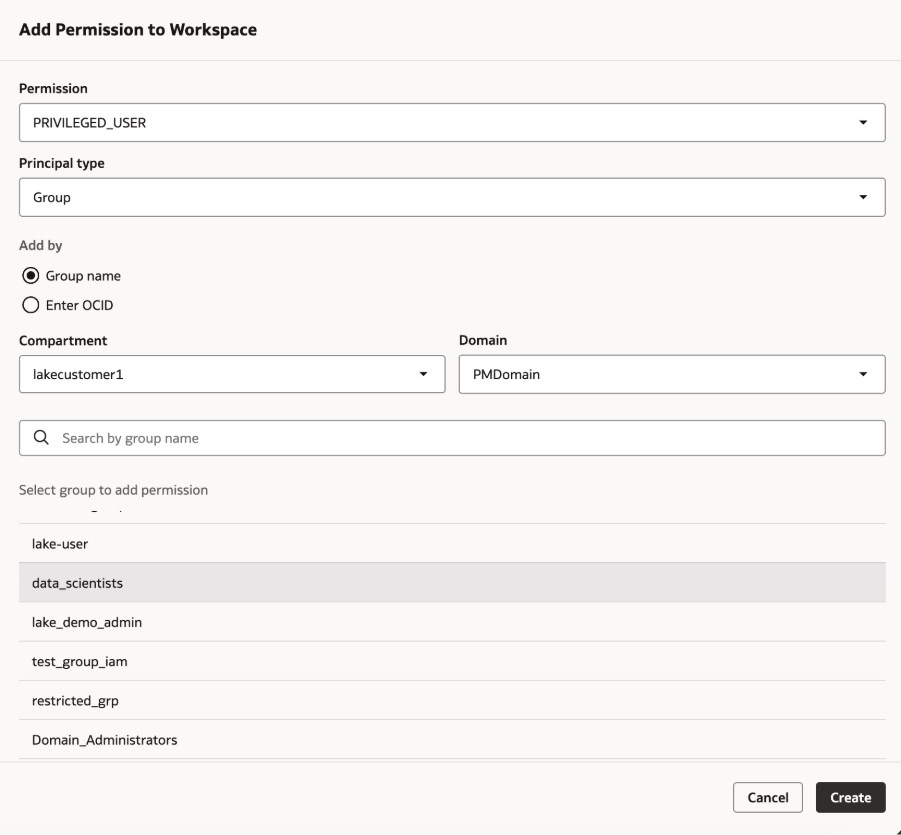
Managing access: Users, groups, and roles
A key strength of AI Data Platform Workbench access control lies in how access is granted. Permissions can be assigned to:
- IAM users
- IAM Groups
- AI Data Platform Workbench roles
While assigning permissions to individuals may work initially, it quickly becomes unmanageable at scale. Instead, best practice is to rely on groups and roles.
Recommended access model
The three-level workspace role hierarchy, with Administrator permission at the top being granted to data stewards, Privileged User permission can be granted to data engineers in the organization, while User permission can be granted to the data scientists, this reflects a good access-control practice because permissions are grouped by responsibility, so only a small number of people have full administrative control while most users get only the access they need to do their work. This structure supports the principle of least privilege, reduces security risk, makes permission management easier, and creates a more scalable way to govern collaboration as teams grow and simplifies onboarding, ensures consistency, and prevents the gradual buildup of unnecessary permissions.
Governance with admin and auditor roles
Beyond collaboration, enterprises require visibility and control.
The Administrator role provides full authority over workspace configuration, including permissions and resource management. This role is critical but should be assigned sparingly. The AUDITOR role, on the other hand, enables role members to inspect resources and track activity.
Audit logs provide a complete record of actions such as resource creation, permission updates, and job executions. This ensures accountability and supports compliance requirements.
Bringing it all together: A collaboration scenario
Consider a typical team working in AI Data Platform Workbench.
A workspace is created for a machine learning project. The administrator assigns roles to groups: data scientists receive User access, data engineers are granted Privileged User access, and the admin retains full control.
Data scientists begin developing models in notebooks. Once ready, data engineers convert these into production workflows and schedule jobs. Throughout this process, access remains tightly controlled, and all actions are logged.
No one has more access than necessary, yet everyone can collaborate effectively.
Preventing access sprawl: Design best practices
A well-designed access control model is not just about assigning permissions, it is about maintaining them over time.
To prevent access sprawl:
- Define access at the workspace level whenever possible
- Use groups instead of assigning permissions to individuals
- Limit administrative privileges
- Separate development and production responsibilities
- Regularly review audit logs and access patterns
These practices ensure that the system remains secure even as teams grow.
Conclusion: Secure collaboration as a First-Class feature
In modern data platforms, governance cannot be an afterthought. It must be built into the way teams collaborate.
AI Data Platform Workbench’s role based access control model achieves this by combining hierarchical permissions, role-based access, and comprehensive auditing. The result is a system where teams can move quickly, without sacrificing control.
By structuring access thoughtfully, organizations can eliminate access sprawl and enable secure, scalable collaboration across notebooks, jobs, and workspaces.
Secure collaboration isn’t about restricting users, it’s about empowering them with the right access at the right time.
For more information:
