This blog post is included as part of our Oracle Defense Ecosystem member spotlight series and is written in collaboration with American Binary.
Imagine if threat actors were to quietly steal sensitive data today and simply wait to decrypt it in the future as capable quantum computers emerge. Harvest Now, Decrypt Later (HNDL) is a known cybersecurity threat for governments and critical industries in which adversaries intercept encrypted data now intending to decrypt it once quantum computing makes current encryption obsolete. In other words, any sensitive information that will be vulnerable after quantum computing’s arrival is at risk now. To help address these quantum threats,Oracle is committed to providing the United States and our allies with advanced technology to help deter and defeat their adversaries.
As part of this commitment, Oracle created the Oracle Defense Ecosystem, where members like American Binary can collaborate on solutions to help strengthen national security interests. American Binary’s pioneering post-quantum network security products are designed to defend sensitive information against quantum threats.
The Oracle Defense Ecosystem and American Binary
The Oracle Defense Ecosystem helps emerging defense technology companies navigate the complex defense market with practical tools and resources. In partnership with American Binary and other innovators, Oracle accelerates the fielding of advanced capabilities that support U.S. and allied defense missions.
American Binary has partnered with Oracle to offer their post-quantum encrypted VPN, Ambit Client, on Oracle Cloud Marketplace for deploying on Oracle Cloud Infrastructure (OCI)’s distributed cloud solutions, including Oracle US Government Cloud, Oracle US Defense Cloud, Oracle National Security Regions, Oracle Cloud Isolated Region, and Oracle Roving Edge Infrastructure.
Preparing for the digital battlefield
Quantum computing offers exciting possibilities for mission-critical workloads. However, securing defense technologies that have relied on pre-quantum public-key cryptography and other established authentication processes for years presents a major concern. Quantum computers are expected to have the capability to break public-key cryptographic algorithms far more efficiently than classical computers. If our adversaries acquire these capabilities, they could potentially decrypt sensitive data and compromise secure communications and authentication processes. This issue forces innovation and the recognition that in a post-quantum world, quantum-resistant cryptography systems are a necessity and migration must begin now.
The US government has identified quantum technology and battlefield information dominance as critical technology areas that emphasize the need to modernize vulnerable technology. In November 2025, the Department of War directed military components to prioritize the adoption of post-quantum cryptography (PQC) and phase out certain legacy protocols by 2030. Commercial National Security Algorithm Suite 2.0 (CNSA 2.0) defines strict standards for National Security Systems and requires that traditional networking solutions, such as VPNs, must support and prefer CNSA 2.0 PQC beginning in January 2026. Older public-key algorithms vulnerable to quantum computers must be replaced by PQC solutions that address new standards that help protect against the threat of future quantum computers.
While organizations today are increasingly recognizing the significance of PQC, American Binary has been preparing for a post-quantum world for seven years. The company designed their VPN, Ambit Client, using NIST Level 5 cryptography that adheres to CNSA 2.0 standards and Federal Information Processing Standards (FIPS) 140-3 and 203. Ambit Client, when deployed on OCI, helps authenticated users securely access their OCI tenancies, while data transiting to and from OCI is protected by PQC. American Binary’s technology also serves customers in financial services, healthcare, legal, insurance, and telecommunications. Ambit Client is available today on OCI Marketplace and all major mobile device app stores for direct download on end user devices.
Ambit Client can be used to help secure data between end user devices and OCI, Roving Edge Infrastructure, and more, supporting 20 different architectures. It also supports completely private connections, meaning that endpoints should remain undetectable unless connected to through Ambit Client.
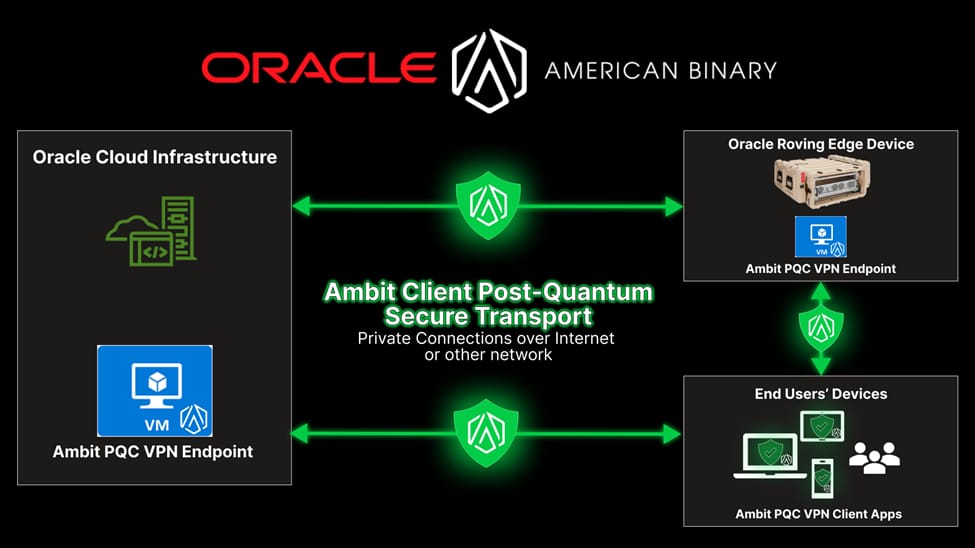
The following figure illustrates a typical deployment of Ambit Client. Ambit Client is a purely software-based solution. Three software components are required: (1) Ambit Client VPN applications on users’ devices; (2) Ambit Client Tunnel Server software on OCI, Roving Edge Infrastructure, or other server; and (3) Ambit Client Controller Server software on OCI, Roving Edge Infrastructure, or other server.
Oracle Cloud Infrastructure: a security-first approach
OCI was built from the ground up with a security-first approach that includes built-in security services and zero-trust architecture. Additionally, OCI’s distributed cloud offerings across government, defense, and isolated regions help to support a range of government compliance standards and customer requirements, facilitating the operation and deployment of advanced VPN solutions:
- Oracle US Government Cloud: authorized to operate at a FedRAMP High JAB and Impact Level (IL) 4, providing compliant, highly secure, and resilient infrastructure and solutions for U.S. federal agencies, state and local offices, and government-affiliated entities.
- Oracle US Defense Cloud: authorized for DISA IL 2, IL4, and IL5, and in full compliance with DISA Security Requirements Guides (SRGs), with connections to DISA Boundary Cloud Access Points (BCAP) and the Defense Research and Engineering Network (DREN).
- Oracle National Security Regions: air-gapped environments authorized at DISA IL6 and Intelligence Community Directive (ICD) 503, supported by government -cleared US Citizens. National Security Region operations are performed from securely managed Cloud Network Operations Centers (CNOCs) by US Government cleared engineers.
- Oracle Cloud Isolated Regions: designed for global customers, these regions are disconnected, air-gapped environments with dedicated operations teams that help address each customer’s citizenship and security clearance requirements.
Delivering future-ready solutions
As capable quantum computers emerge, defending long‑lived data and mission systems demands quantum‑resistant protections now. By combining OCI’s security‑first, distributed cloud with American Binary’s PQC‑enabled Ambit Client, defense organizations can harden communications, help protect sensitive data in transit, and help accelerate compliance with emerging standards. The result is a resilient foundation for secure operations, today and in the post‑quantum future.
Learn more about the Oracle Defense Ecosystem
To learn more about how Oracle supports defense organizations in scaling operations and engaging customers, or to apply to the Oracle Defense Ecosystem, visit Oracle Defense Alliances or reach out to your Oracle representative. Oracle offers many hyperscale core-to-edge cloud solutions for governments and defense partners. We’re ready to support organizations seeking to innovate with OCI.
Resources
