Low tech hacking or Tales of the Social Interloper
Hard drive takeover
\If you walk through most office environments, particularly after general office hours, you will see many work stations unattended. There’s an invisible army of people who visit the office after hours:
– maintenance personnel
– subcontracted janitorial staff
– even actual staff “working” after hours
 Most desktop cases have a tab which can be used to physically lock the cases as shown in the image to your left, but many are not locked.
Most desktop cases have a tab which can be used to physically lock the cases as shown in the image to your left, but many are not locked.
For those cases which don’t have a tab, there are “locking” screws available.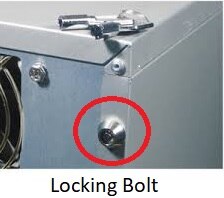
For cases with no locking installed, it is relatively trivial to open the case and temporarily remove the hard drive.
Once the drive is removed, files can be copied from the drive to the hacker’s laptop, they can also add malware, without any “phishing” or other means.  The connector cable with drive adapter is readily available. In extreme cases, if the drive is fully encrypted, a bit copy can be taken and the drive image subsequently analyzed for the type of encryption, and data retrieval.
The connector cable with drive adapter is readily available. In extreme cases, if the drive is fully encrypted, a bit copy can be taken and the drive image subsequently analyzed for the type of encryption, and data retrieval.
Obviously, the work needed in this case by the hacker requires a determined effort, and deep pockets on someone’s behalf.
When the drive is replaced and the system rebooted, it will not be obvious to the user that anything has occurred.
Mitigation in this type of attempt requires that the case is locked, and that the computer is also locked in place.
See also “Security by Walking Around” below.
System Takeover
Multiple USB types are available
– Bootable USB
– Auto execute USB
 With the “Bootable USB” the hacker inserts the USB into an available port and simply reboots the PC from the USB. These type of USB’s are available with Windows, or more frequently with a version of Linux, typically with many tools for system manipulation.
With the “Bootable USB” the hacker inserts the USB into an available port and simply reboots the PC from the USB. These type of USB’s are available with Windows, or more frequently with a version of Linux, typically with many tools for system manipulation.
Again, the hacker simply reboots the PC from the inboard disk and in general the user will not suspect any wrong doing if the system is at the sign-on screen when they return to the system.
 With the “Auto Execute” USB, inserting the USB, even with screen lock, will allow the code on the USB to execute, potentially installing malicious code or sniffers. Remember Stuxnet?
With the “Auto Execute” USB, inserting the USB, even with screen lock, will allow the code on the USB to execute, potentially installing malicious code or sniffers. Remember Stuxnet?
Again, in both these cases, the hacker simply removes the USB when they have completed their activities.
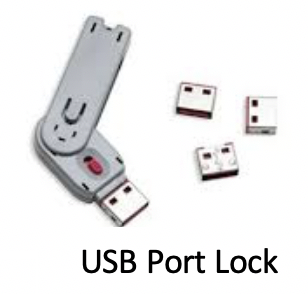 One relatively trivial mitigation in this case is to use USP Port locks.
One relatively trivial mitigation in this case is to use USP Port locks.
User PC’s should not allow local user administer access, and the organization should regularly run an asset audit to report on unapproved installed software.
Shoulder Surfing
 A regular tactic used by the Social Interloper is “Shoulder Surfing.”
A regular tactic used by the Social Interloper is “Shoulder Surfing.”
 Users working on sensitive development, or often critical financial data, should be aware of any reviewing the contents of their screen. This is often the case when the user is focused on the task in hand.
Users working on sensitive development, or often critical financial data, should be aware of any reviewing the contents of their screen. This is often the case when the user is focused on the task in hand.
Mitigations here are the screen filter, which makes the screen unreadable except from the direct viewing angle or a monitor corner mounted mirror.
Dumpster, and Trash Can, Diving
One trick that never gets old for the hacker is Dumpster Diving!
 This, and Trash Can diving, is of value to the hacker because of the large number of documents discarded without being shredded, particularly since dumpsters are difficult to oversee areas of the facility.
This, and Trash Can diving, is of value to the hacker because of the large number of documents discarded without being shredded, particularly since dumpsters are difficult to oversee areas of the facility.
Mitigation here is maintaining a secure shredding process before documents can be discarded.
In addition to mitigations already described, another method is “Security by Walking Around.”
This and the mantra “If you See Something, Say Something” is put in action by senior managers and supervisors occasionally visiting the facility out of hours and questioning those they encounter for their purpose on the premises. Of course, there are many ways to approach the ensuing interviews and conversations.
Interloper Crowd Mingling and Tail-Gating
“Security by Walking Around” and “If you See Something, Say Something” also comes into play with another tactic by the Social Interloper.
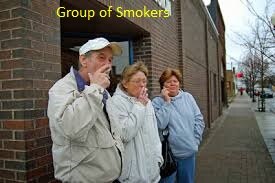 Many organizations have “unofficial” smoking areas where groups gather. The Social Interloper takes his place with the group, chatting and smoking in the way these groups interact generally.
Many organizations have “unofficial” smoking areas where groups gather. The Social Interloper takes his place with the group, chatting and smoking in the way these groups interact generally.
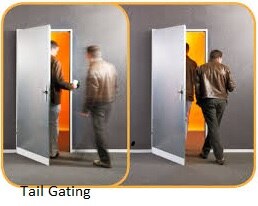 He may build up the confidence of the group over time until he is eventually able to join the group as they enter the building, tail-gating with the group. It is only vigilance on the part of the group and an anti-tail-gating culture, even anti-tail-gating technology which can reduce the risk if this type of intrusion occurs.
He may build up the confidence of the group over time until he is eventually able to join the group as they enter the building, tail-gating with the group. It is only vigilance on the part of the group and an anti-tail-gating culture, even anti-tail-gating technology which can reduce the risk if this type of intrusion occurs.
Further Reading:
You should also review “Securing Your PeopleSoft Application Environment (Doc ID 747524.1)“
(login required)
[NOTE] This recent copy is dated 2016, and it is currently in review for an update. There are multiple copies of the older version, dated 2010, copied numerous times on the Internet.
