How role based access control, auditability, and enterprise governance work together in Oracle AI Data Platform Workbench
Enterprise AI programs do not fail because teams lack access to data. They fail because access is too broad, too manual, too opaque, or too hard to govern once multiple teams begin sharing the same platform. In Oracle AI Data Platform Workbench, governance is built into the operating model through layered security, fine-grained role-based access control (RBAC), and platform audit logs. That matters because Oracle AI Data Platform is not just a storage layer. It is a shared environment for notebooks, workflows, compute, catalogs, schemas, tables, volumes, and other governed assets used by data engineers, analysts, data scientists, and stewards.
Governance Starts with a Layered Security Model
The first thing to understand is that Oracle AI Data Platform Workbench uses two layers of security. The first is OCI IAM, which controls access to OCI resources. The second is the AI Data Platform object permissions model, which governs what users can do inside the platform. This separation is important. Infrastructure access and platform collaboration access are related, but they are not the same. A user may have permission to reach the environment at the OCI layer and still have tightly scoped permissions inside the workbench.
This design gives enterprises a practical control point. Central cloud administrators can manage coarse-grained access to platform resources, while platform owners and data domain leaders can manage day-to-day collaboration at the object level. That becomes increasingly important as organizations move from a single team experiment to a shared enterprise platform with multiple projects, personas, and governance requirements.
RBAC Is Applied Where Teams Actually Work
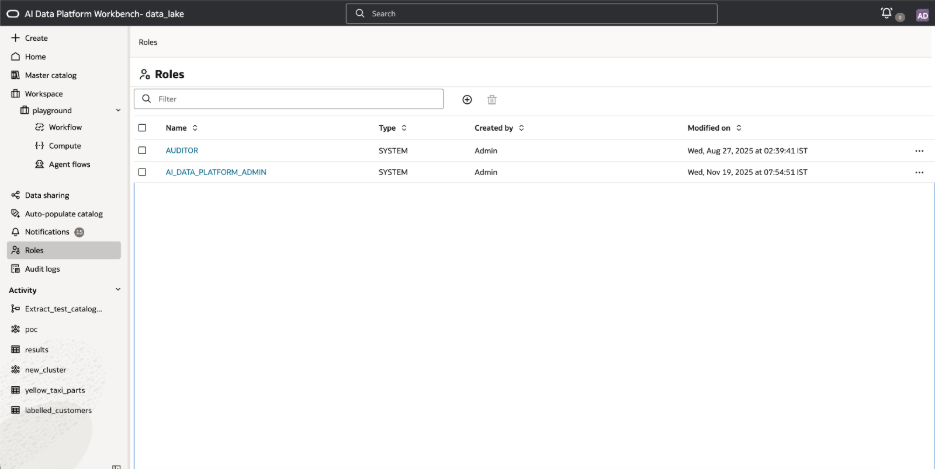
A useful governance model should map to the real surfaces where collaboration happens. Oracle AI Data Platform Workbench does that by applying role-based access control across both collaborative assets and data assets. Administrators can create and manage roles, assign them to users and groups, and separate day-to-day operational access from oversight responsibilities. Out-of-the-box, the platform includes system roles such as AI_DATA_PLATFORM_ADMIN for administrative control and AUDITOR for full audit visibility.
The permissions model spans workspaces, folders, notebooks, jobs, compute clusters, catalogs, schemas, tables, and volumes. That scope matters because governance breaks down when it only exists at one layer. A user who can run notebooks but should not modify shared datasets needs a different permission profile from a data engineer who builds pipelines, or an auditor who needs visibility into operational history without broad write access. In AIDP, those distinctions can be modeled directly in the platform.
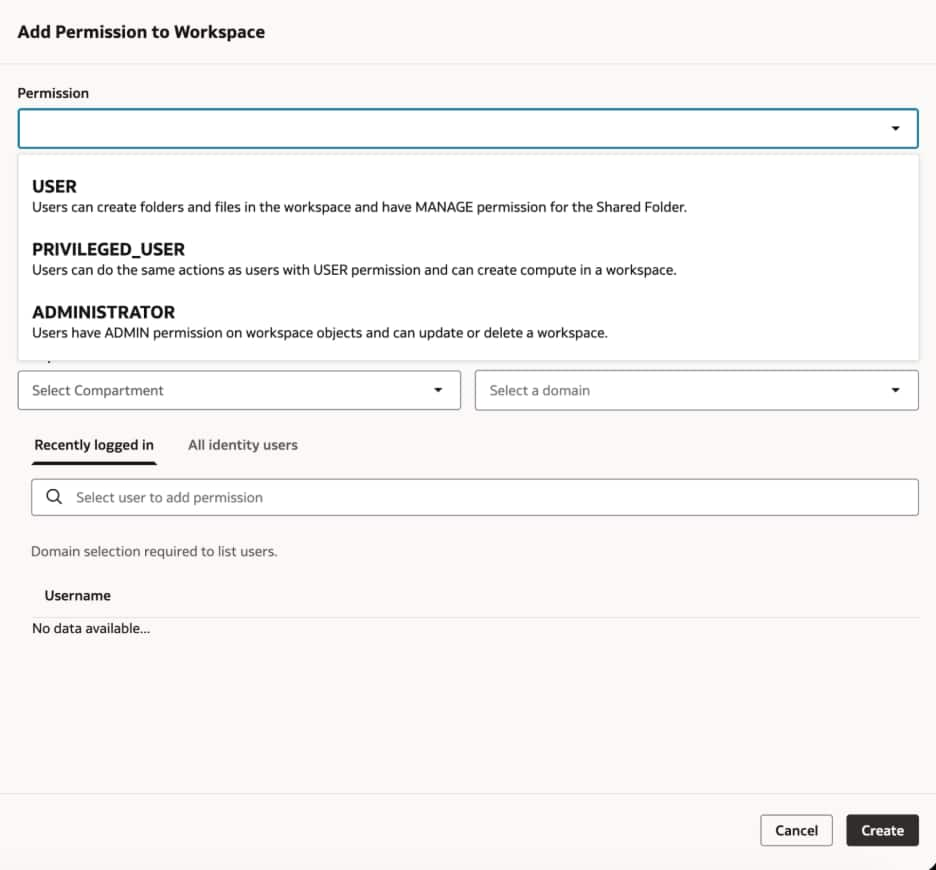
For example, workspaces support distinct levels such as USER, PRIVILEGED_USER, and ADMINISTRATOR. Folders and notebooks expose finer controls such as read, use, manage, and admin. Compute clusters similarly distinguish between reading metadata, using the cluster, and administering it. On the data side, permissions become even more granular. Catalogs, schemas, and tables can be governed independently, with controls for reading, writing, creating derived objects, altering structures, and managing permissions.
Hierarchical Permissions Reduce Friction Without Expanding Access
One of the more important design choices in AI Data Platform governance is the ability to define hierarchical permissions on catalog objects. Permissions do not operate as a flat list of unrelated grants. Instead, they follow parent and child relationships between objects. Permissions granted at a parent level can cascade down to child objects, which simplifies administration for domain-level access patterns. At the same time, child-level permissions can expose only the minimum parent path needed for a user to reach the authorized object.
This is a practical answer to a common enterprise problem. Without hierarchy, administrators often have to choose between over-granting access or making objects difficult to discover and use. With inheritance and controlled expansion, teams can grant access to a single table, schema, or notebook without opening unrelated assets. That makes least-privilege collaboration more realistic in large, shared environments.
In operational terms, this means governance can align with how a business is organized. A domain workspace can be broadly shared for collaboration while sensitive production tables remain tightly controlled. An analyst can receive read access to trusted data products without getting write privileges in upstream schemas. A data engineer can be empowered to build and run workflows without inheriting administrative rights over every governed object in the platform.
Auditability Completes the Governance Model
Preventive controls answer one question: who is allowed to do this? Audit trails answer a different one: what actually happened? Oracle AI Data Platform Workbench includes audit logs that capture activity across major platform object types, including external catalogs, roles, standard catalogs and their child objects, workspaces, files and folders.
This audit record is useful because it goes beyond a generic event stream. Operational entries can include the object name, object type, operation, request details, timestamp, initiating user, source of the action, and final status. For platform operators, this creates a reliable record of how changes were made and whether they succeeded. For compliance and internal governance teams, it creates accountability and traceability across a shared platform.
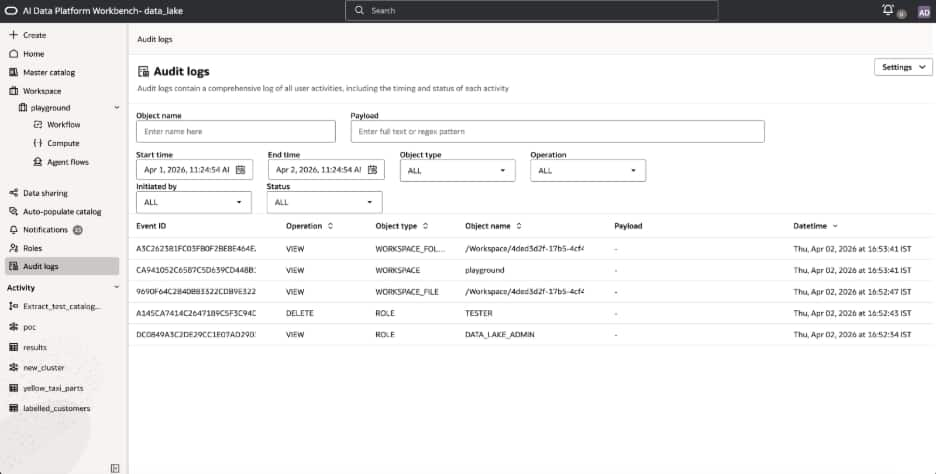
Search and filtering are just as important as raw capture. In real enterprise environments, nobody wants to inspect a flat log dump when they are investigating a failed change, validating an access review, or responding to an internal audit request. Being able to narrow results by object, payload, or time period is what makes auditability operationally useful rather than merely available.
Why This Matters for Customers
AI data platform customers are usually trying to solve two problems at once. They need to increase the speed of analytics and AI development, and they need to avoid creating a governance gap as more teams adopt the platform. Oracle AI Data Platform Workbench is designed for that balance. Governance is embedded into the same surfaces teams use for data engineering, notebook development, data sharing, and metadata management.
That has practical implications. Teams can create governed workspaces for specific business domains, apply data permissions at the right level of granularity, and maintain oversight through dedicated audit capabilities. The result is a platform where collaboration does not require giving up control, and where compliance does not depend on stitching together controls from disconnected tools.
Practical Operating Model for Governance Enforcement
For customers implementing Oracle AI Data Platform, a pragmatic starting point is to use OCI IAM for coarse environment access and use AIDP roles and object permissions for platform-level governance. Keep the administrator role narrowly assigned. Use group-based access wherever possible so domain ownership scales with the organization. Apply permissions at the parent level when a team should inherit broad access across a governed area, and use object-specific grants when least-privilege exceptions are needed. Finally, treat audit logs as part of normal platform operations rather than a tool that is only consulted after an incident.
This approach works because Oracle AI Data Platform does not treat governance as a separate afterthought. It is part of the platform’s core operating model. Role-based access control establishes the right boundaries for secure collaboration. Audit trails provide the visibility needed for accountability and compliance. Together, they make the platform more predictable, more defensible, and more enterprise-ready for production AI and analytics workloads.
Conclusion
Governance should not slow down AI development. It should make shared work safer, clearer, and easier to scale. Oracle AI Data Platform Workbench gets there by combining IAM-backed access, object-level RBAC, hierarchical permissions, and searchable audit trails into one operating model. For customers building shared enterprise data, that is what turns a technically capable platform into an enterprise-ready one.
For more information:
