Executive Summary
Agentic systems turn cost control from a reporting problem into a runtime execution problem. A single run can consume meaningful resources through model calls, retrieval, tool invocations, retries, delegation, repair loops, and replanning. In production, the risk is often not just budget overrun, but inefficient execution while the system is still running.
Traditional cost controls are no longer enough on their own. Billing dashboards, monthly spend reports, and coarse project budgets act too late: they show that spend occurred, but not whether the current execution path is still efficient, safe, or worth funding.
Budget guardrails address that gap by turning cost control into a runtime governance capability. Given the current execution state, observed usage, and expected remaining work, they help decide whether the system should continue, narrow, degrade, reroute, escalate, or stop.
Consider an enterprise procurement agent asked to compare vendors and prepare a recommendation. The run begins within budget, then enters a low-yield pattern: repeated retrieval retries, premium-model calls, delegation, and replanning that consumes budget without materially reducing uncertainty. A billing dashboard will eventually show the spend; a runtime budget guardrail can decide earlier whether that execution path still deserves more budget.
In agentic systems, budget is no longer just a financial outcome; it is a runtime control signal for execution in motion. This is not governance instead of budget control; it is budget control implemented as runtime governance because agentic systems spend through behavior, not static allocation. Figure 1 summarizes this shift from retrospective cost visibility to runtime budget governance.
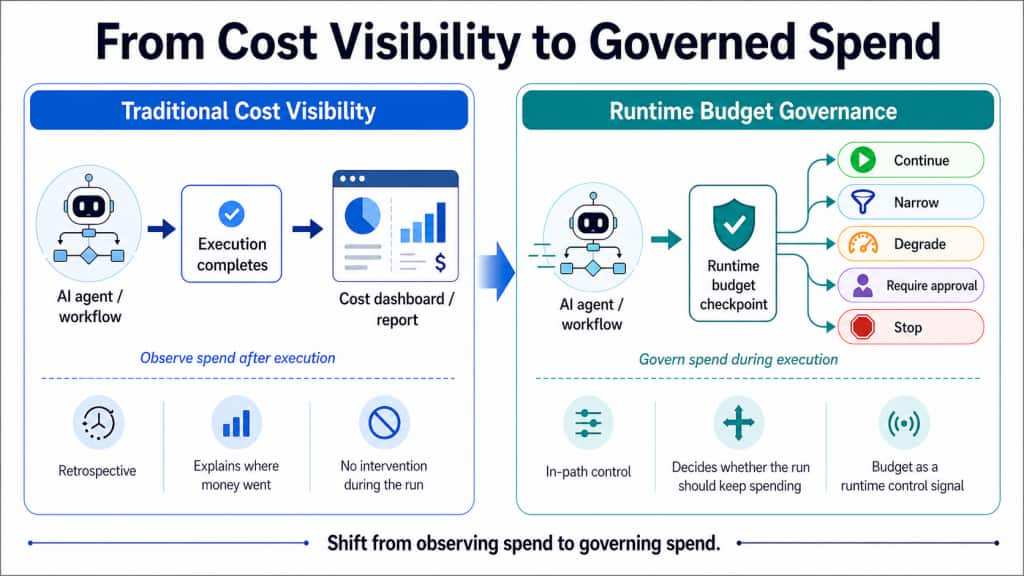
Figure 1: From Cost Visibility to Governed Spend. Traditional controls explain where money went after execution. Runtime budget governance decides whether the current execution path should keep spending more while the run is still in motion.
OCI’s opportunity is not just to help customers see where agentic spend went, but to help them govern where it is allowed to go.
1. When Behavior Becomes Spend: The Agentic Shift
Modern GenAI systems do not behave like simple request-response applications. Once a workflow becomes agentic, cost is no longer created by a single model call. It is created by a sequence of runtime decisions across planning, model invocation, retrieval, tool use, retries, delegation, recovery, and replanning.
That shift matters because the real problem is not simply high spend; it is inefficient execution while spend is still accumulating. When a system consumes budget without improving task state, reducing uncertainty, or moving closer to completion, the cost problem and the execution problem become the same problem.
This is the new cost-control failure mode. A procurement or research agent may keep retrieving, retrying, delegating, and replanning long after the run has stopped making useful progress. The issue is not only that spend is high; it is that the execution path continues to consume budget without generating commensurate value.
2. Why Retrospective Cost Visibility Is Not Control
Budget guardrails are runtime controls that decide whether an agentic run still deserves more budget. Their purpose is not merely to measure usage. Their purpose is to detect and contain wasteful or infeasible execution before it turns into avoidable spend.
The control model depends on two concepts:
- Budget controls define how far a run is allowed to go.
- Circuit breakers define what the runtime must do when a run goes too far.
A budget without intervention is only monitoring. A circuit breaker without explicit triggers is improvised stopping logic. Runtime budget governance requires both: defined limits and deterministic remediation.
The goal is not to stop runs aggressively at the first sign of cost pressure. Poorly tuned guardrails can create false-positive terminations, premature downgrades, and degraded user outcomes. The design challenge is to intervene early enough to contain waste, but not so early that the system abandons feasible work.
Budget guardrails should therefore sit inside the governed execution path, alongside pre-execution veto, approval-aware execution, safe degradation, and evidence-linked observability. They are best understood not as a reporting feature, but as a budget-specific control-plane capability for governed agentic execution.
3. Operational FinOps: Managing AI Execution in Motion
This is not simply AI cost optimization. It is Operational FinOps for agentic systems: runtime budget governance applied to execution in motion.
Traditional FinOps explains where spend went. Operational FinOps for agentic systems governs whether the current execution path is still worth funding. That is the key shift.
Teams still need monthly visibility, allocation, chargeback, and forecasting. But for agentic systems, they also need runtime budget controls that decide whether a workflow should continue, narrow, degrade, require approval, or stop while the run is still executing.
As budget guardrails mature, they can extend cost management from retrospective visibility toward governed spend, where budget policy is attached directly to agentic workflows and evaluated step by step at runtime. That makes budget guardrails a foundation for a more operational form of FinOps in agentic systems.
4. Runtime Signals: Observability for Budget Control
Budget guardrails only work if the runtime can see what the system is doing while it is doing it. In practice, that means operating over live observability artifacts: metrics, logs, and traces.
- Metrics detect budget pressure. They surface rising spend, excessive retries, abnormal tool usage, deteriorating burn posture, and growing latency early enough for the system to react.
- Logs preserve budget-intervention history. They record which policy fired, what triggered it, what action was taken, and what outcome followed.
- Traces reveal budget-consuming execution context. They show what happened, where it happened, and how one step led to the next. That path-aware view is what allows budget guardrails to become more than disconnected alerts.
Metrics show pressure, logs preserve intervention history, and traces explain where and why budget was consumed. Budget governance becomes operational only when these signals stay connected. Without that connection, budget guardrails degrade into disconnected alerts rather than trace-linked runtime decisions.
5. The Runtime Policy Surface: Minimum Viable Budget Guardrails
To move from passive budget awareness to active runtime control, budget policy must be defined across explicit, versioned limits. Rather than a flat list of alerts, a well-governed system should use a Minimum Viable Budget Guardrail (MVG) set that contains waste while preserving the agent’s ability to complete complex tasks.
5.1 Policy Signals and MVG Implementation
| Signal category | Policy signal | Minimum viable implementation |
| Consumption | Token budget | Define a hard cap for total tokens per run to prevent runaway spend. |
| Efficiency | Normalized cost units | Use normalized units for expensive model paths or tool invocations where raw tokens do not fully reflect risk or cost. |
| Temporal | Wall-clock runtime | Set execution-duration limits to detect hanging processes, stalled workflows, or infinite loops. |
| Behavioral | Iteration, tool-call, and retry caps | Establish caps on loop counts, tool calls, and retries to detect low-yield execution patterns. |
| Architectural | Delegation depth | Limit sub-agent delegation depth to prevent exponential complexity and cost. |
| Predictive | Pre-step reservation | Reserve budget against expected worst-case cost before executing expensive actions. |
5.2 Deterministic Circuit Breakers: From Limits to Action
A budget limit without an intervention mechanism is merely monitoring. When a hard limit or critical threshold is breached, the runtime must trigger deterministic circuit-breaker actions:
- Degrade to safe mode: Narrow execution to read-only tools, no external writes, no further delegation, capped retries, or restricted model paths.
- Require human approval: Require explicit approval before re-entering premium model paths, invoking high-cost tools, or executing sensitive actions.
- Terminate infeasible execution: Stop runs that are forecasted as infeasible or are failing to make measurable progress.
This structured policy surface turns budget policy into a runtime control signal, ensuring that agentic behavior remains aligned with economic and operational constraints.
6. A Runtime Budget-Control Loop for Governed Spend
Once the policy surface is clear, the next question is how those policies should be enforced during execution. A useful way to think about budget guardrails is as a trace-linked runtime control loop rather than a threshold or alerting feature.
In production, governed spend requires five linked elements:
- Execution layer: planning, model calls, retrieval, tool use, retries, delegation, and recovery.
- Observability and evidence layer: metrics, logs, and traces that capture what the workflow is doing in real time.
- Budget ledger: the state store for cumulative usage, reserved usage, actual usage, forecasts, and remaining budget.
- Budget policy layer: the logic that evaluates limits, thresholds, infeasibility conditions, and remediation actions.
- Runtime action layer: the mechanism that applies deterministic outcomes such as continue, narrow capability, require review, switch to safe mode, reroute, or terminate execution.
In well-governed systems, this control logic should sit close to execution, especially near expensive decisions and external side effects. Budget interventions should be recorded in the same execution trace as the workflow itself, so cost governance becomes part of the operational record rather than a separate financial afterthought.
A practical implementation often follows four stages:
Admission. Before execution begins, evaluate whether the task appears feasible within the assigned budget and execution constraints. If completion is clearly unlikely within policy bounds, the right response may be to deny, reroute, or escalate before meaningful cost is incurred.
Pre-step reservation. Before an expensive model or tool step, reserve the budget against the expected worst-case cost of that action. This helps prevent oversubscription and makes the control loop more realistic about what the next step could consume.
Post-step reconciliation. After the step completes, replace the reservation with actual usage, update the forecast, recompute remaining budget, and emit a structured budget event. Metrics update counters and rates, logs preserve the event record, and traces attach actual spend to the exact step that incurred it.
Replan or enforce. If remaining budget becomes tight, forecast completion deteriorates, or recent execution shows wasteful behavior, policy should intervene immediately. Useful progress should mean that the workflow is changing task state, reducing uncertainty, improving evidence quality, or moving measurably closer to completion. If execution continues to consume budget without doing those things for a bounded number of steps, policy should narrow capability, escalate, reroute, or stop.
In the procurement-agent example, this is the point where repeated retrieval retries, premium-model escalation, and delegation without meaningful progress should stop being treated as ordinary execution and start being treated as governed spend pressure.
Figure 2 turns this pattern into a runtime budget-control loop. The important point is that budget governance is not a detached alert; it is a closed loop that connects execution state, observability signals, budget ledger updates, policy evaluation, and deterministic runtime action.
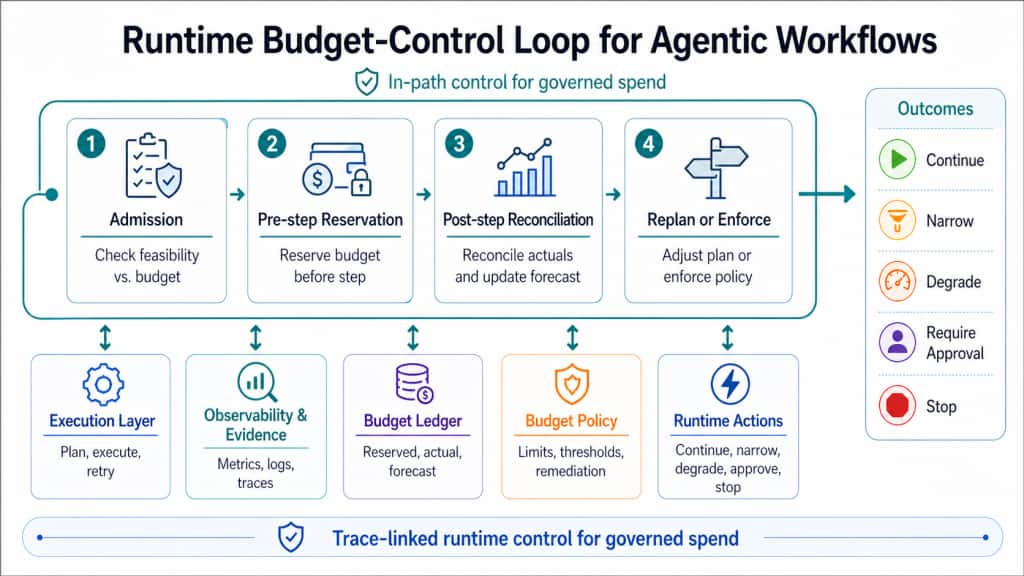
Figure 2: Runtime Budget-Control Loop for Agentic Workflows. Admission, reservation, reconciliation, and enforcement decisions are linked through observability, budget state, policy evaluation, and runtime action.
This loop is what allows the runtime to move from passive budget awareness to governed spend: each expensive step can be reserved, reconciled, evaluated, and either allowed, narrowed, escalated, or stopped based on the current execution state.
6.1 Example: From Trace Signal to Budget Intervention
A trace-linked intervention sequence could look like this:
| Step | Runtime observation | Budget signal | Policy decision | Runtime action |
| 1 | Agent starts vendor-comparison workflow | Initial budget reserved | ALLOW | Start run |
| 2 | Retrieval retries exceed expected count | Retry burn rate rising | ALLOW_WITH_WARNING | Continue, record pressure |
| 3 | Premium model path requested | Forecasted remaining budget deteriorates | RESERVE_AND_CHECK | Reserve worst-case cost |
| 4 | Delegation requested after low-yield replanning | Progress score remains low | REQUIRE_REVIEW or NARROW | Disable delegation or require approval |
| 5 | Another expensive tool call is proposed | Budget threshold breached | SAFE_MODE | Switch to read-only tools and lower-cost model |
| 6 | Execution still fails to improve task state | Infeasible completion forecast | TERMINATE | Stop run and emit budget event |
This pattern turns “the run became expensive” into evidence: why, which policy fired, what action was taken, and whether intervention happened at the right point.
7. The Evidence Layer: Making Budget Decisions Auditable
Budget guardrails become auditable when each intervention is attached to the span or step it evaluated and records the policy identifier, version, trigger, observed values, decision, reason, and outcome.
Trace-linkage is what turns a budget intervention from an alert into an auditable runtime decision.
Without trace-linkage, cost controls degrade into disconnected alerts. A team may know that a run was expensive or that a threshold was crossed, but it will not have enough operational context to understand why the system behaved that way, whether policy should have fired earlier, or which part of the workflow was actually responsible.
With trace-linkage, teams can see not only that spend was high, but which step triggered intervention, which policy version fired, what condition was observed, and whether the runtime responded too late, too early, or correctly. That makes interventions easier to debug, review after incidents, explain to governance teams, audit, and improve over time.
Trace-native budget guardrails do not just stop waste. They preserve a complete operational record of what happened, where it happened, and why the system responded as it did. A budget intervention record can be compact but decision-grade:
{
"trace_id": "trace-123",
"span_id": "step-5",
"policy_id": "budget.retry_burn_rate.v1",
"decision": "SAFE_MODE",
"trigger": "retry_burn_rate_exceeded",
"observed": {
"retry_count": 5,
"remaining_budget_pct": 18
},
"runtime_action": "disable_delegation_use_lower_cost_model",
"reason": "Low progress with rising forecasted cost"
}The point is not the exact schema. The point is that every budget intervention should be trace-linked, reason-coded, and reviewable.
8. Enterprise Utility: Scaling Governed Spend
For OCI customers, the value is not only lower waste; it is a more governable execution model for agentic systems. Premium-model usage becomes easier to constrain, retry storms easier to contain, infeasible execution easier to narrow before side effects occur, and every intervention traceable to runtime evidence. That makes budget guardrails more than a cost feature; it makes them part of a broader governed execution layer for enterprise AI.
As this capability matures, budget guardrails can improve unit economics, reduce runaway executions, and make premium model usage, tool behavior, and retry patterns more governable across agentic workflows. For governance and platform teams, they also represent a runtime safety capability: they can stop pathological execution earlier, narrow unsafe behavior before side effects occur, and create a more consistent enforcement model across applications.
Teams should evaluate budget guardrails with a small operational metric set: avoided runaway-run rate, cost per successful task, intervention rate, false-positive termination rate, downgrade rate, budget-policy compliance rate, and time-to-detect infeasible execution.
These metrics should feed guardrail tuning: threshold adjustment, safe-mode calibration, false-positive reduction, under-enforcement detection, and validation that interventions improve unit economics without degrading task success unnecessarily.
For OCI, this is a stronger platform direction than generic AI cost optimization alone. Budget guardrails fit naturally within a broader governed execution layer that also includes approval-aware execution, pre-execution veto, safe degradation, observability, policy enforcement, and evidence-backed runtime control.
Conclusion: Governed Spend Is the New Runtime Control Plane
The industry shift is fundamental: in the era of agentic AI, spend is no longer just a financial metric to be audited after the fact. It is a runtime signal that must be governed during execution. Relying only on retrospective reporting creates an architectural gap, leaving enterprises exposed to pathological execution and hidden inefficiencies long before a billing alert ever fires.
The path forward is a governed execution layer in which budget guardrails are not treated as a standalone cost feature, but as part of the runtime control plane itself. By moving budget policy from the dashboard into the execution path, platforms can detect wasteful loops earlier, apply deterministic remediation, and ensure that cost, safety, and execution quality are managed together rather than in isolation.
The most mature agentic platforms will not treat spend as a number to analyze after execution ends. They will treat it as a runtime signal to govern while execution is still in motion. In the agentic era, the platforms that control spend best will enforce it, explain it, and audit it at the point where budget is consumed.
