Authors: Mr. Enrico Ronchetti, R&D Director, Skybackbone, and Rebecca Righetti, Skybackbone apprentice, M.S. in Computer Science
Blog Contributor- Erika Sciunzi, Observability and Manageability Specialist
This blog highlights Skybackbone’s use of Oracle Cloud Infrastructure Logging Analytics. Mr. Enrico Ronchetti, R&D Director, shared his experience and some of the key benefits they are working toward at Skybackbone.
Describe Skybackbone’s business and your role in implementing the solution.
Skybackbone was founded in 2011 by a team of skilled Senior Professionals with decades of working experience in the world of IT. The company sets out to be your strategic Consulting Partner offering know-how in the management of Corporate Information Systems with a particular focus on ERP / CRM and e-commerce applications, especially in the Cloud. Enrico Ronchetti describes how he recently rebuilt the Internal Logging Solution around Oracle Logging Analytics for Skybackbone.
Our solution requirements were driven by our customers’ need to have a record of administrator access required by the General Data Protection Regulation [GDPR: Regulation (EU) 2016/679 of the European Parliament and of the Council of 27 April 2016] and Measure About Data Protection [G.U. 2008/300 of 24 December 2008]. When Skybackbone’s original eSiem named solution was first built, it reached more than 60 customers across Europe and the US with over 1,000 servers involved. We have one environment that pulls data from across all individual servers wherever they are, forwards data to our data center, and shares it with each customer in pixel-perfect PDF documents, mostly used for compliance purposes. Today, Skybackbone pulls 240GB per day resulting in 160M Log entries per day.
Why is Oracle part of the solution Skybackbone offers its customers?
We believe in the power of the cloud. We also believe that security is paramount, and our data must be secure and scalable by design in our data centers. We manage many customers’ data centers that are running Oracle. Many of our customers have Oracle as their foundational technology or are looking at moving to the Cloud. Oracle Observability & Management services proved to be more mature than other cloud providers. For example, we have benefited from the built-in capabilities that Logging Analytics provides such as pulling in streams of data from various log sources and making it easy for us to understand severity (Info, warning, critical). In addition, we are provided with out-of-the-box source information (operating systems, databases, firewalls). We can compare logs from the past to the present to determine security issues.
Most of the information that we can extract from a Log Entry comes from capabilities that are embedded within Oracle Logging Analytics. We have not found those capabilities in other Cloud Providers’ or On-Prem Logging Solutions. A single log entry having a “Logon Failure” is not a problem. For example, a user can type the wrong password, however, the same user may have several logon failures from different devices. This logon history is valuable information for the CISO because it tracks the number of login attempts from various devices. Logging Analytics highlights this important information quickly and reduces time to resolution.
With Oracle, we have one architecture that suits different customer needs. We can focus on many more log sources across multiple industries and can leverage hundreds of new sources. Meanwhile, Oracle continuously provides the latest version updates to us automatically. Thus, we provide updated services and larger coverage without a change in cost. We have expanded our offerings and can track data from other sources like MySQL, Postgres, Mongo, and many more solutions that were not available in the past. Now, we accept Customer Home-grown Application Logs and apply them to the same workflow we devised for standard logs. This added functionality helps us provide higher value to our customers with the production of Pixel Perfect PDF Documents, Timestamped Digital Signatures, and added Threat Analysis. Our customers are asking for us to track more and more data and now we are ready! Today we provide data for compliance purposes with added Security at no additional cost.
Skybackbone’s 5 key solution benefits:
1. We can map digital fingerprints from the Logs we collect to threats using security knowledge bases from both Open-Source Community and Commercial Products. The image below is a view of raw customer-matched vulnerabilities / Attack Paths concerning the Open Source Security Events Metadata (OSSEM). The larger and darker the cluster indicates that the occurrence count is higher.
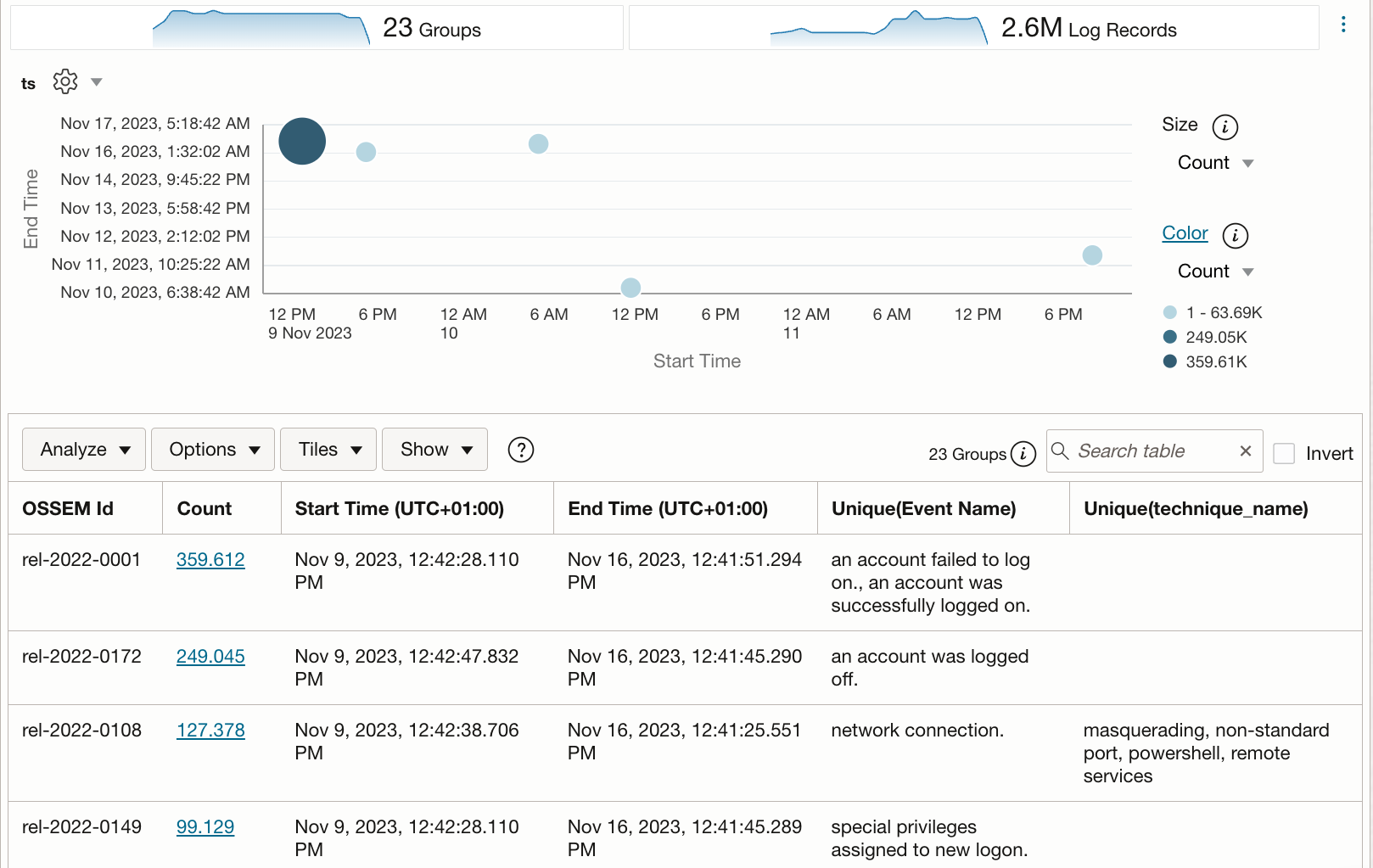
Using the OCI lookup function we correlate the IDs found from OSSEM with common vulnerabilities and exposures (CVEs), extracted from the National Institute of Standards and Technology (NIST – https://nvd.nist.gov/vuln).
With this feature, we add Security to Raw Log Data already collected for compliance purposes. By adding these Features, Skybackbones’ Logging Solution has addressed the CIO’s perspective for taking security seriously. For example, from the same Logs, we now provide:
- The most exploitable Attack Paths (OSSEM IDs) that can easily be matched with MITRE ATT&CK Framework
- The most common Vulnerabilities (CVE IDs)
2. We mapped every customer to an OCI compartment and provided each customer with hierarchically refined data. Customers can access their data at sub-company hierarchical levels. Each sub-customer or customer has their dashboard with access to only their specific data.
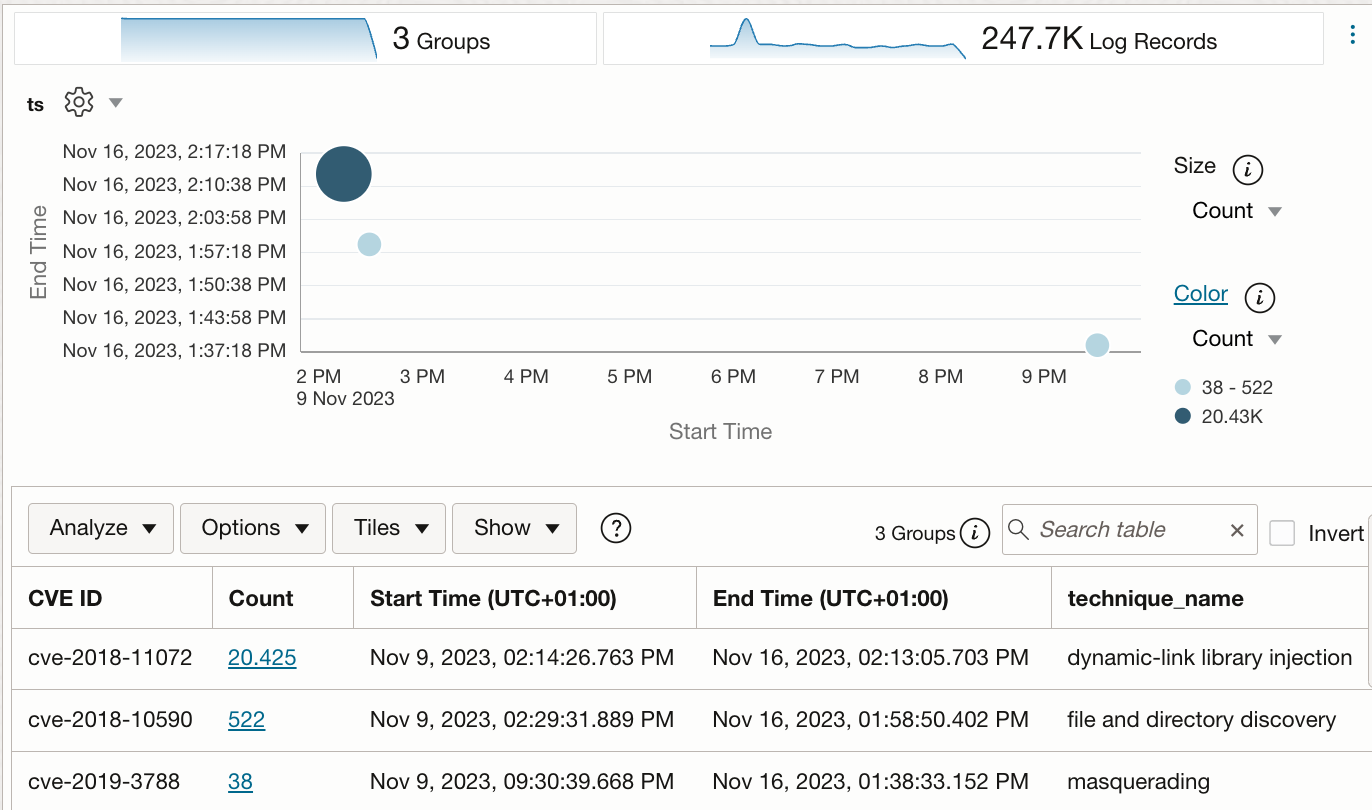
3. Access to data from REST API within Logging Analytics allows us to extract data and turn events grouped by server and day into pixel-perfect PDF documents with a digital signature and an external timestamp provided by a trusted authority.
Each PDF Document contains:
(1) Valid record of signature
(2) Digital Signature Details with external Timestamp
(3) Confirmation details that validate the signature
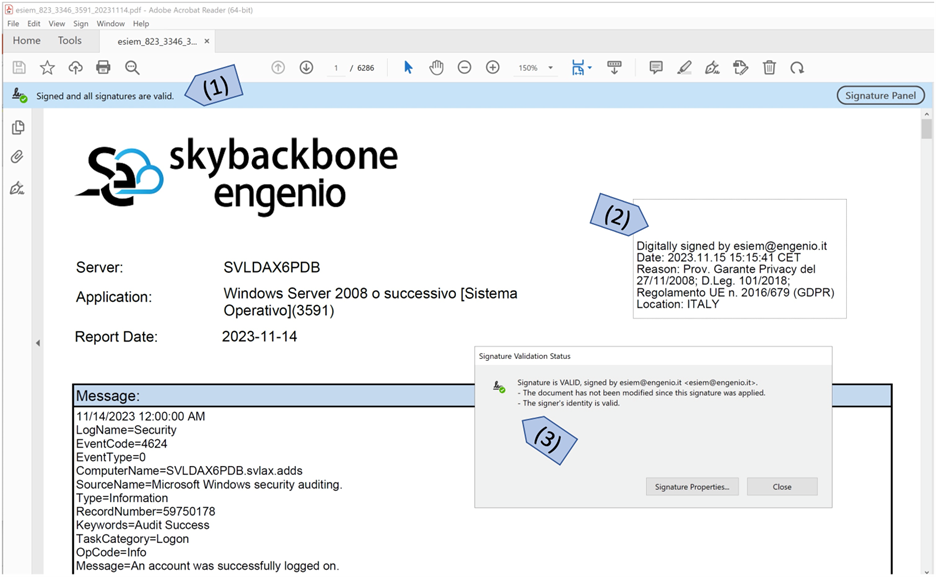
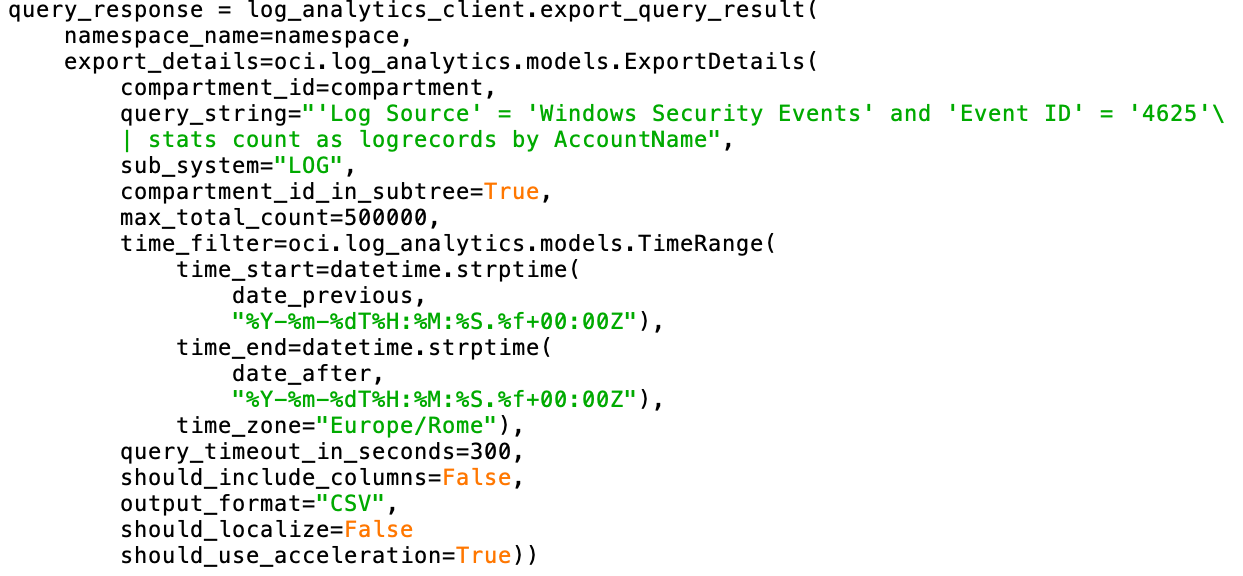
As you can see from the images below, it is simple to transform a query executed in the provided Graphical User Interface into a query from the REST API. This gives us the flexibility to address each customers’ unique security requirements.
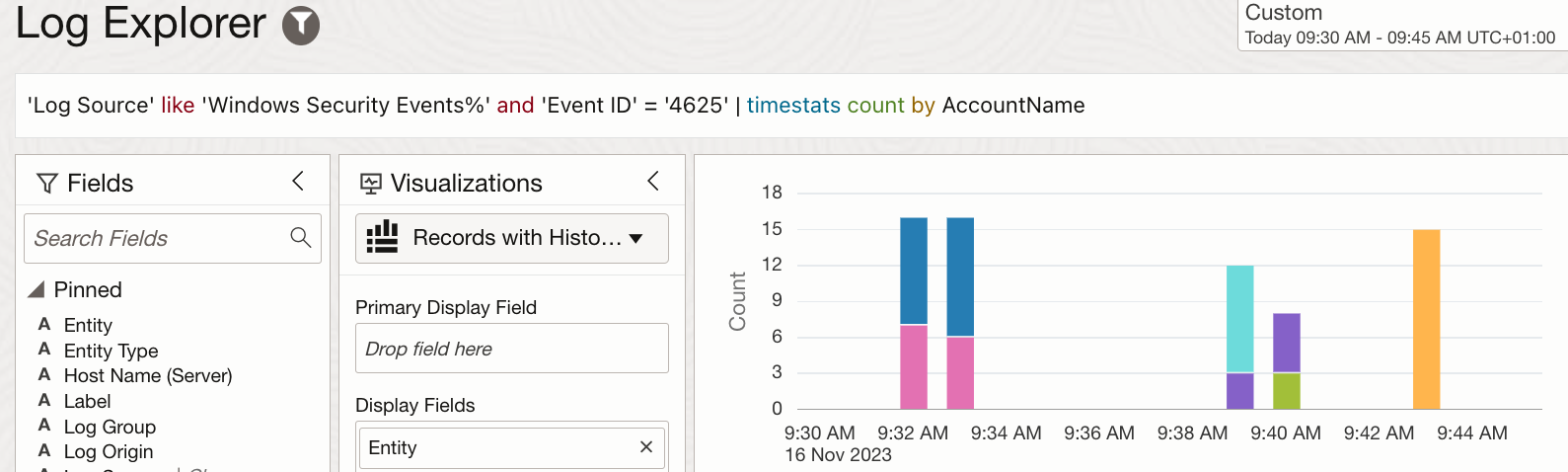
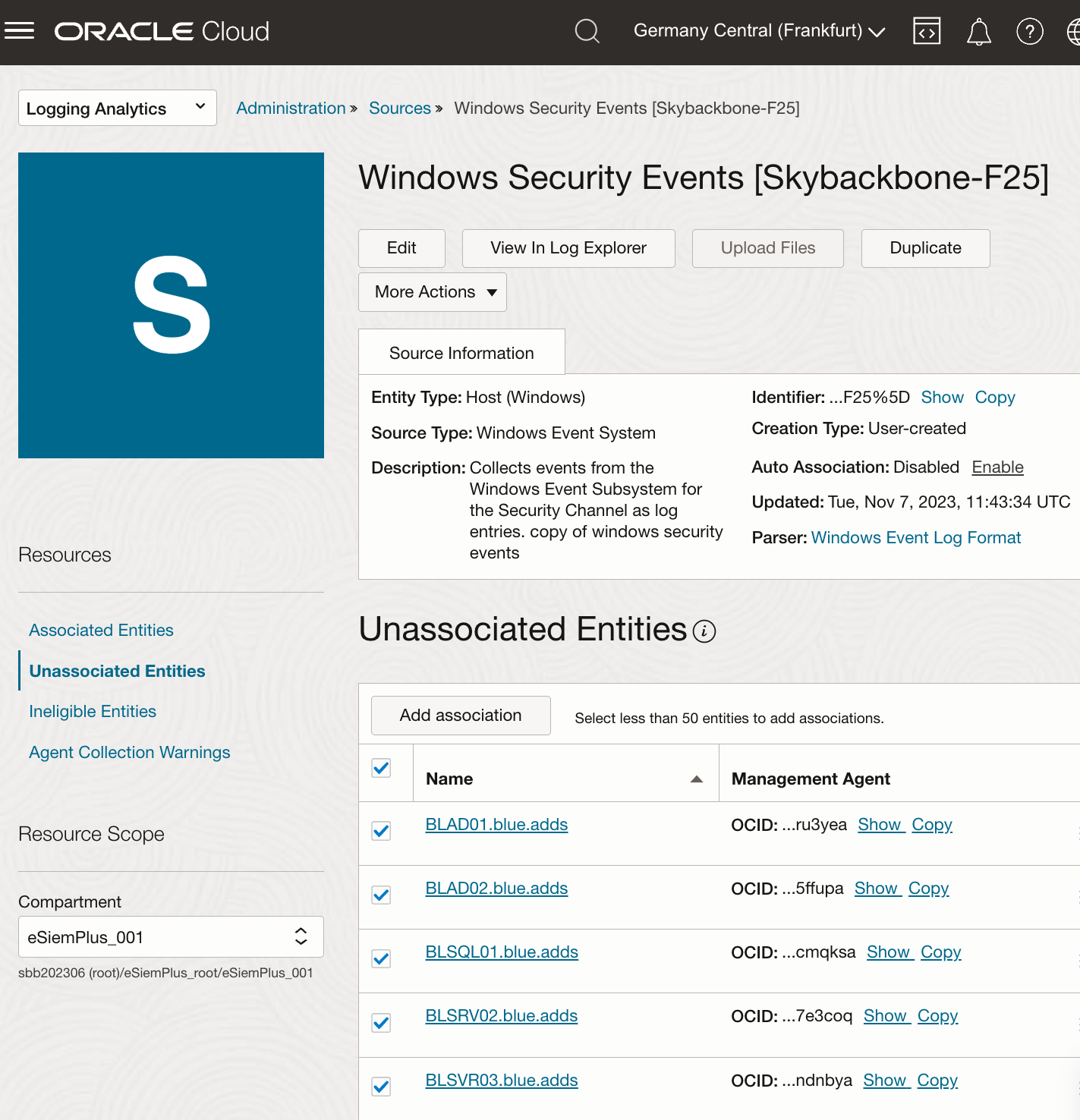
4. We can now enable additional Log Sources from each Server without asking Customer Engineers to assist. We no longer need to access the Operating system. Everything can be done from the OCI Logging Analytics Web Application. Extracting server logs from another data source is just one click away. Furthermore, it is possible to automate the process of log forwarding and the entire installation of the agents by available API or through the GUI. In the image below we can associate and then extract Windows Events from 5 Servers at once with the GUI.
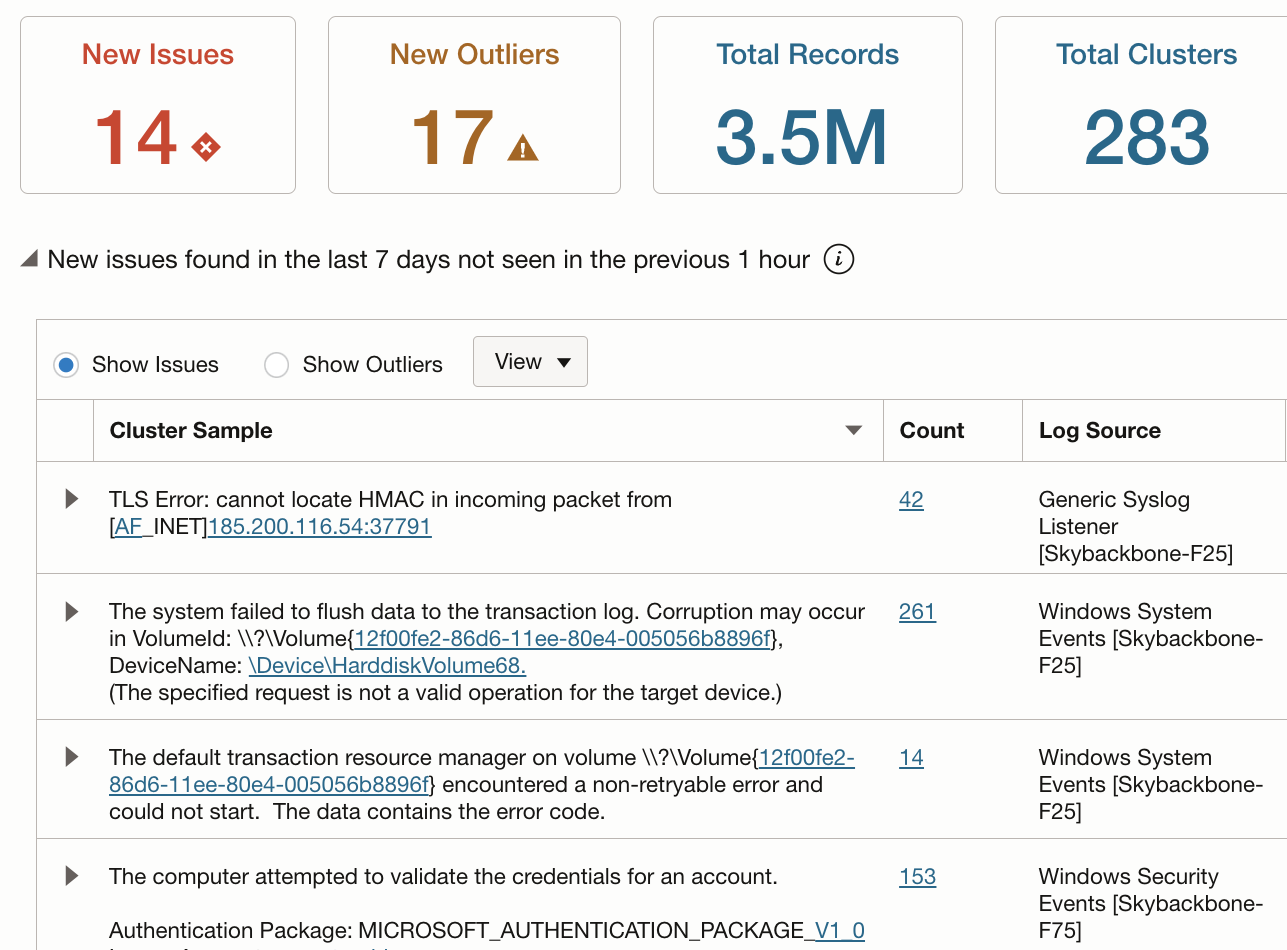
5. Lastly, new visualization features (made available during the CloudWorld 2023) will provide clear views of anomalies within the monitored network to allow specialists to intervene promptly and analyze only the suspicious logs. In particular, 2 facets are gathered and highlighted in one panel:
- Data from a Custom Time Range selected by the user (today) concerning an accepted Baseline
- Keywords and Labels (for example- Error, Failure, Exception) can be extracted from the logs and highlighted by Logging Analytics
How has Skybackbone cloud adoption evolved since you transitioned to the cloud/offering these services?
The way we look at Monitoring and Log Management has completely changed. We can detect early when something is wrong. We leverage the REST APIs in OCI to check at regular intervals for multiple agents at once. This is completely different for our monitoring staff who no longer spend all day watching each agent individually. Now, they are alerted whenever something interesting is triggered. We have been freed up to focus on other concerns, which has improved our operations and lowered our monitoring cost.
How does Skybackbone differentiate its services in the marketplace using Oracle Logging Analytics?
We leverage our solution across small, medium, and large enterprises. We serve cross-industry leaders with large server deployments, and we do it with one solution. Moreover, we can provide different billing profiles based on customer requirements and scale to their budgets. We manage more data and build more solutions for our customers’ unique needs.
What advice do you have for someone who is new to the cloud and how can they best start building a solution that suits them?
Think big. Whenever companies look for a compliance solution, they want Security included. Skybackbone has added that security to our eSiem solution. IT managers are faced with threats, ransomware, and other security issues daily. They want more from a solution and understanding their security profile along with their compliance requirements drives a more successful dialogue.
What is Skybackbone doing next to build upon its Logging Analytics solution?
Skybackbone is leveraging our Logging Analytics experience with open source and other commercial projects to build additional solutions, even adding AI Features. We are leading with a Security foundation with all we do. We want to inject, correlate, and analyze data coming from other security tools to offer our customers a more complete solution.
Resources
Try Oracle Cloud Infrastructure for free
