Web services provided by Oracle E-Business Suite Integrated SOA Gateway are secured at the transport level through SSL and at the message level through authentication tokens – Username Token and SAML Token (Sender Vouches). I will discuss SAML Token (Sender Vouches) here.
Brief on SAML, SAML Token, SAML Token Profile
Security Assertion Markup Language (SAML) is a XML-based framework to exchange security related information between Service Consumer, Identity Provider and Service Provider. The security information is expressed in terms of assertions. Statements about the subject or user form the SAML Token.
WS-Security defines a set of security token profiles for different types of tokens embedded within the SOAP message as headers. SAML Token Profile is one of the WS-Security Token Profiles that describe the syntax and meaning of SAML Tokens. SAML Tokens are embedded within SOAP messages by placing assertion elements inside the SOAP Header.
As per WS-Security, there are three common methods to assure the Service Provider that the SOAP message came from the subject referenced in the token. The three common subject confirmation methods are Sender Vouches, Holder of Key, and Bearer. As of Oracle E-Business Suite Release 12.1.3, web services provided by Integrated SOA Gateway (inbound) support SAML Token using the Sender Vouches subject confirmation method.
SAML Token – Sender Vouches
SAML Tokens assert that the subject or user has already been authenticated. As the name suggests, in the Sender Vouches case, the Sender or SOAP web service client that sends the SOAP request message to SOAP web service vouches for the identity of the assertion’s subject.
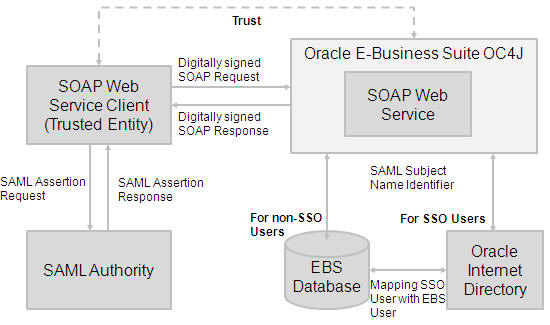
The SAML assertion may be provided by an external Identity Provider — a SAML Authority or SAML Issuer. In this case, a client sends a SAML assertion request to a SAML Authority. The SAML Authority identifies the client, authenticates the subject, and sends SAML assertion as response to client. The client’s private key is used to sign both the assertion and the SOAP message body.
The E-Business Suite’s Integrated SOA Gateway uses Oracle Application Server’s Web Services Security framework. It verifies the digital signature in a SOAP request and extracts the SAML Token. It validates the SAML assertion such as the issuer, validity period, and authentication statement. It extracts the SAML Subject Name Identifier and verifies the same with registered Oracle Internet Directory (OID) for single sign-on users or with FND_USER table in Oracle E-Business Suite (EBS) database for non-single sign-on users. It uses Oracle Internet Directory to map the single sign-on user with the equivalent EBS user. The EBS username is then used for the authorization check for the web service execution.
When to use SAML Sender Vouches based authentication for web services provided by Integrated SOA Gateway?
SAML Token with Sender Vouches is best used for following scenarios:
- Single Sign On: As part of your business process, you may want to authenticate once and propagate the authenticated identity as a SAML assertion to subsequent EBS web service calls.
- Subject or user needs to be authenticated locally (at web service client end) or centrally by Identity Provider (or SAML Authority), and propagate the assertion to an EBS web service.
How to use SAML Token Sender Vouches in Integrated SOA Gateway?
The steps to expose an EBS API as web service are described in Oracle E-Business Suite Integrated SOA Gateway Implementation Guide and Developer’s Guide:
- Create Grant for EBS API methods that you want to expose as web service operations
- Generate and Deploy the EBS API as web service with SAML Token (Sender Vouches) authentication type
- Configure client and EBS (server) for SAML
See Setting Up SAML Token Security for Oracle E-Business Suite Integrated SOA Gateway Release 12.1.3 [Note 1144313.1]
This Note describes the steps to configure SOAP Web Service Client as well as Oracle E-Business Suite (SOAP Web Service Provider). In Integrated SOA Gateway, a SAML Token Sender Vouches policy is applied at the web service level or port level. You may have to configure EBS for SAML for all web services that are deployed with Authentication Type as SAML Token (Sender Vouches).
- Invoke web service with SAML Token
The Note also describes steps to test web service invocation with a SAML Token. Depending upon the client program, you may programmatically insert SAML assertions or let web service security policy enforcement products such Oracle Web Services Manager (OWSM) insert a SAML Token in a SOAP request message.
References
- Oracle E-Business Suite Integrated SOA Gateway Implementation Guide [Part No E12169-06]
- Installing Oracle E-Business Suite Integrated SOA Gateway, Release 12 [Note 556540.1]
- Setting Up SAML Token Security for Oracle E-Business Suite Integrated SOA Gateway Release 12.1.3 [Note 1144313.1]
Related Articles
- New Whitepaper: Primer on Integrating with EBS 12 with Other Applications
- Securing E-Business Suite Web Services with Integrated SOA Gateway
