Introduction
One of the more useful custom fields is the Password field. A popular use case is storing credentials to an external system within a Transaction or Entity record for use with integrations.
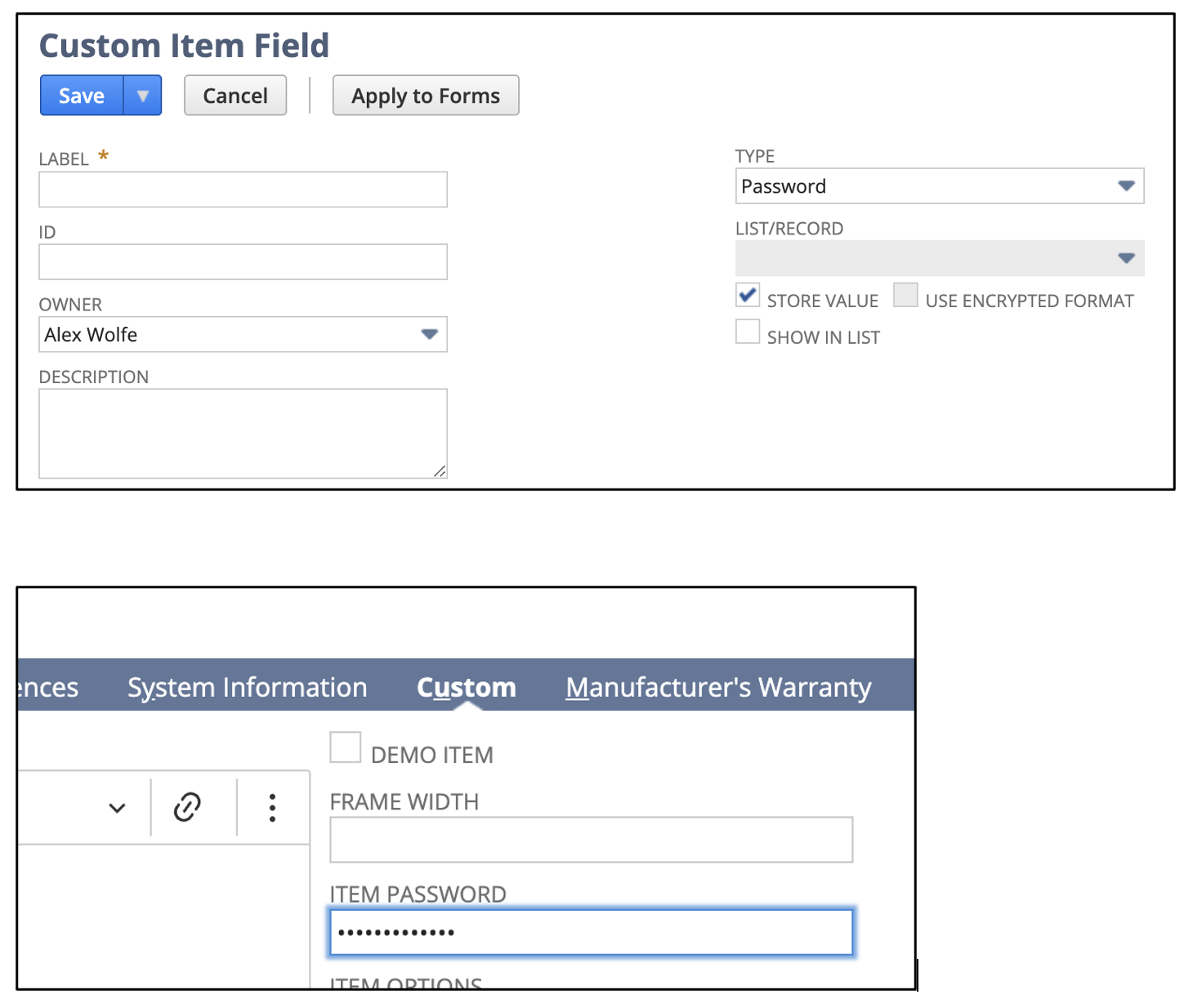
Custom passwords can be logged and stored within NetSuite records through the user interface or via SuiteScript/Web Services. To ensure security, these passwords are irretrievable in plaintext form to maintain their integrity. NetSuite, prioritizing data protection, never stores the actual plaintext passwords but instead keeps only encrypted hashed representations.
In the past, it was possible to access a hashed version of a password field using methods like Record.getValue(options) or CurrentRecord.getValue(options) for custom password fields. However, current best practices discourage the use of these methods for password fields as they now return obfuscated strings, not the original hashed values, enhancing security by minimizing the risk of password exposure.
While NetSuite enforces this limitation on extracting plaintext passwords, it provides a secure alternative for validation. The crypto.checkPasswordField method allows for the verification of a password’s validity without exposing the actual password, aligning with NetSuite’s robust security framework.
How to check passwords
The crypto.checkPasswordField method enhances the security of validating custom password fields by returning a Boolean value—true or false—when a plaintext string is provided for verification. This method is particularly useful when comparing passwords stored in NetSuite against plaintext passwords retrieved from an external system.
It’s important to note that when using crypto.checkPasswordField, the plaintext password string should be part of an array structure. This array is used to compare the provided plaintext password against the encrypted password stored within NetSuite. In the structure of the options parameter, you specify the location of the custom password field within the NetSuite record, and the value parameter carries the plaintext password to be validated. The function will then return true if there’s a match or false if there isn’t, without revealing any password details, thereby maintaining security and confidentiality.
Sample Code
...
const options = {
recordType: record.Type.SALES_ORDER,
recordId: 6,
fieldId: 'custitem1',
sublistId: 'item',
line: 0,
value: 'plaintextpassword'
};
if (crypto.checkPasswordField(options)) {
log.debug('True');
} else {
log.debug('False');
}
...