Over the weekend we rolled out an update to Oracle Developer Cloud – your DevOps and Agile platform in the Oracle Cloud. A key new capability we added is security checks for your Java apps as part of our DevOps pipelines. Read below to learn more about this and other features available for you.
DevSecOps – Automate Code Security Checks
Keeping up to date with the latest information about security risks in your code can be a challenge, but not doing this can put your company and your customers at risk. We all heard stories about hackers leveraging well known security breaches that companies forgot to patch. As your application grows this becomes even more challenging as you struggle to keep track of the set of public libraries you are using.
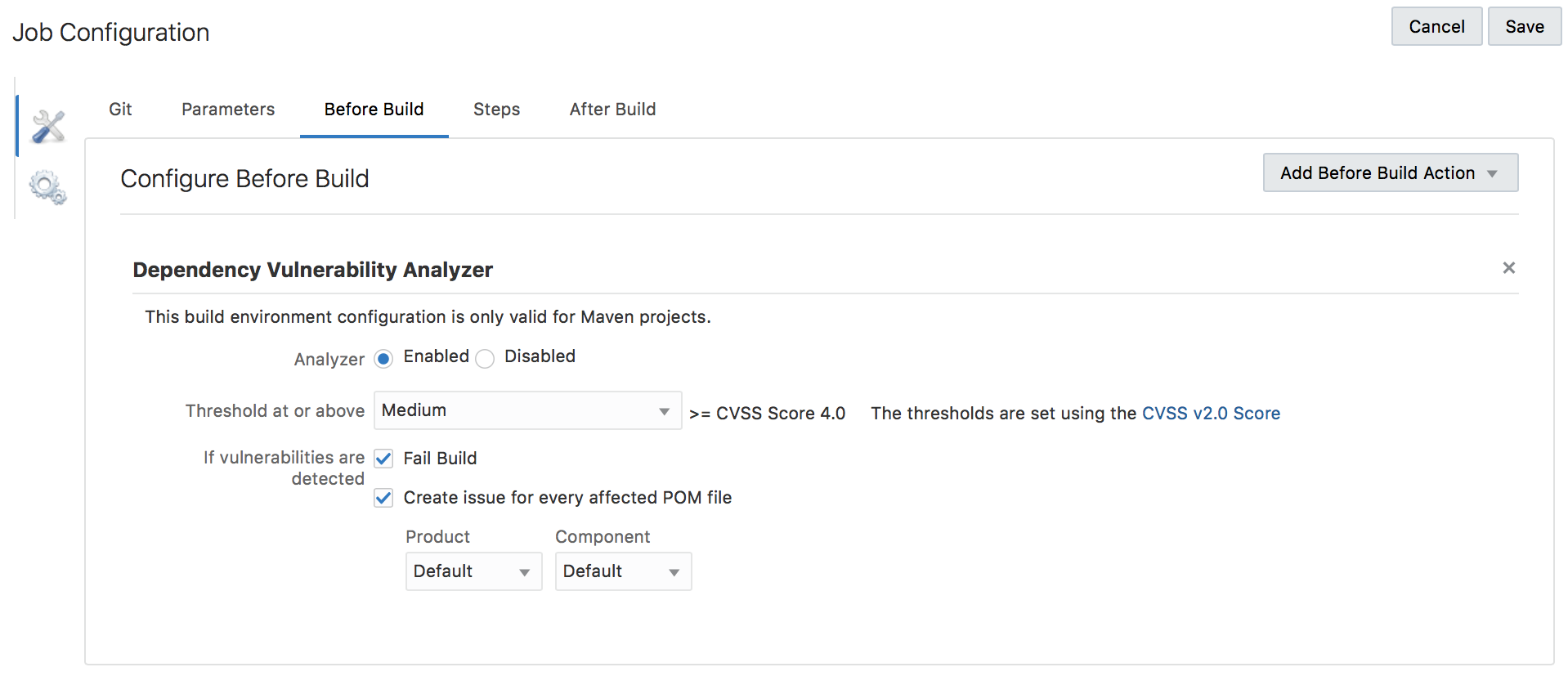
With the new version of Oracle Developer Cloud we add DevSecOps functionality that scans your code against a database of known security vulnerabilities and alerts you if your code is using libraries with known security issues. In our first release we scan Java code for projects that leverage Maven as their build framework.
You can setup automatic jobs to review your code, report the results, and stop the roll out of vulenrable apps. You can also automatically add a task to the issue tracking system in DevCS to help the team keep an eye on fixing the issue.
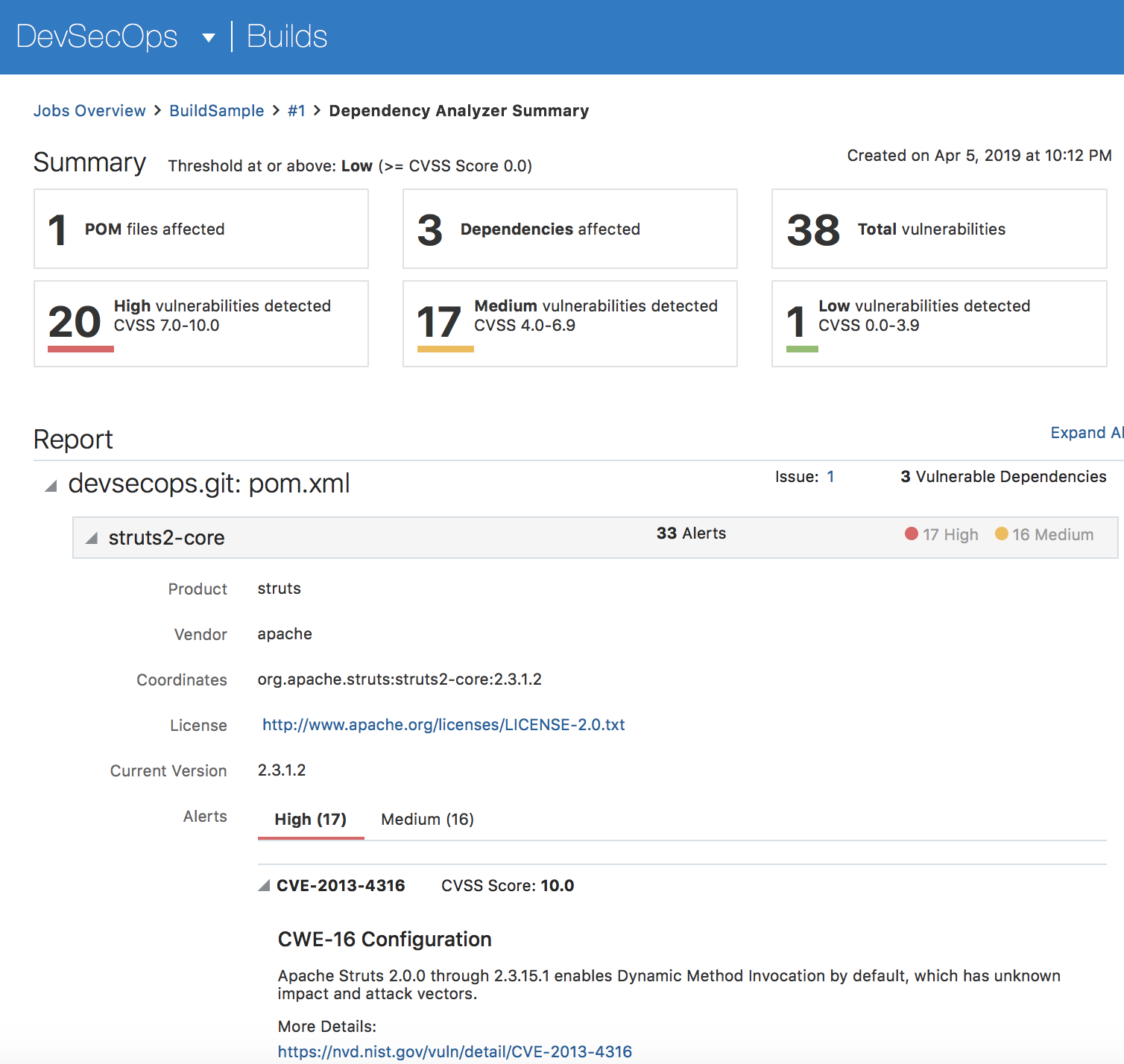
The build job will give you a detailed report with links to more information about every vulnerability we identify in your code.
YAML Based Build and Pipeline Definition
Following the “Infrastructure as Code” approach Developer Cloud now allows you to define build jobs and pipelines using YAML files. These files can be stored in the Git repositories in DevCS, and versioned like the rest of your code. DevCS scans your git repositories for these files (specific directory), and creates or updates jobs and pipelines automatically when those are changed (in the master branch). This provides a compliment approach for defining your CI/CD in parallel to the visual approach using the DevCS interface.
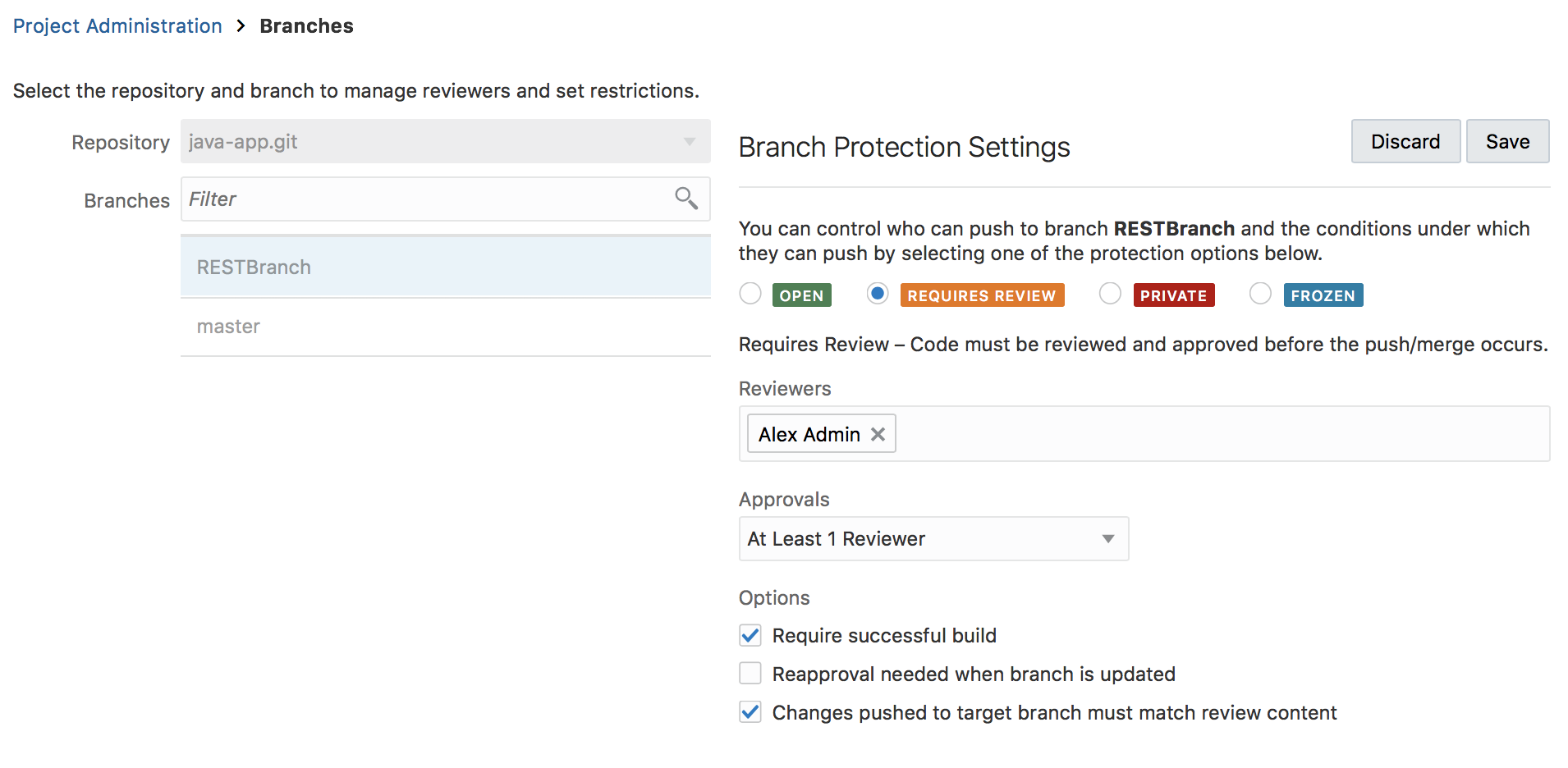
Enhanced Git Branch Protection
You now have more capabilities to restrict what changes can be done to specific code branches. New branch types include branches that require review, are private, or frozen. For example, a branch that is marked as “requires review” limits the ability to push changes by requiring code review by other team members, successful build job, and other combinations of conditions.
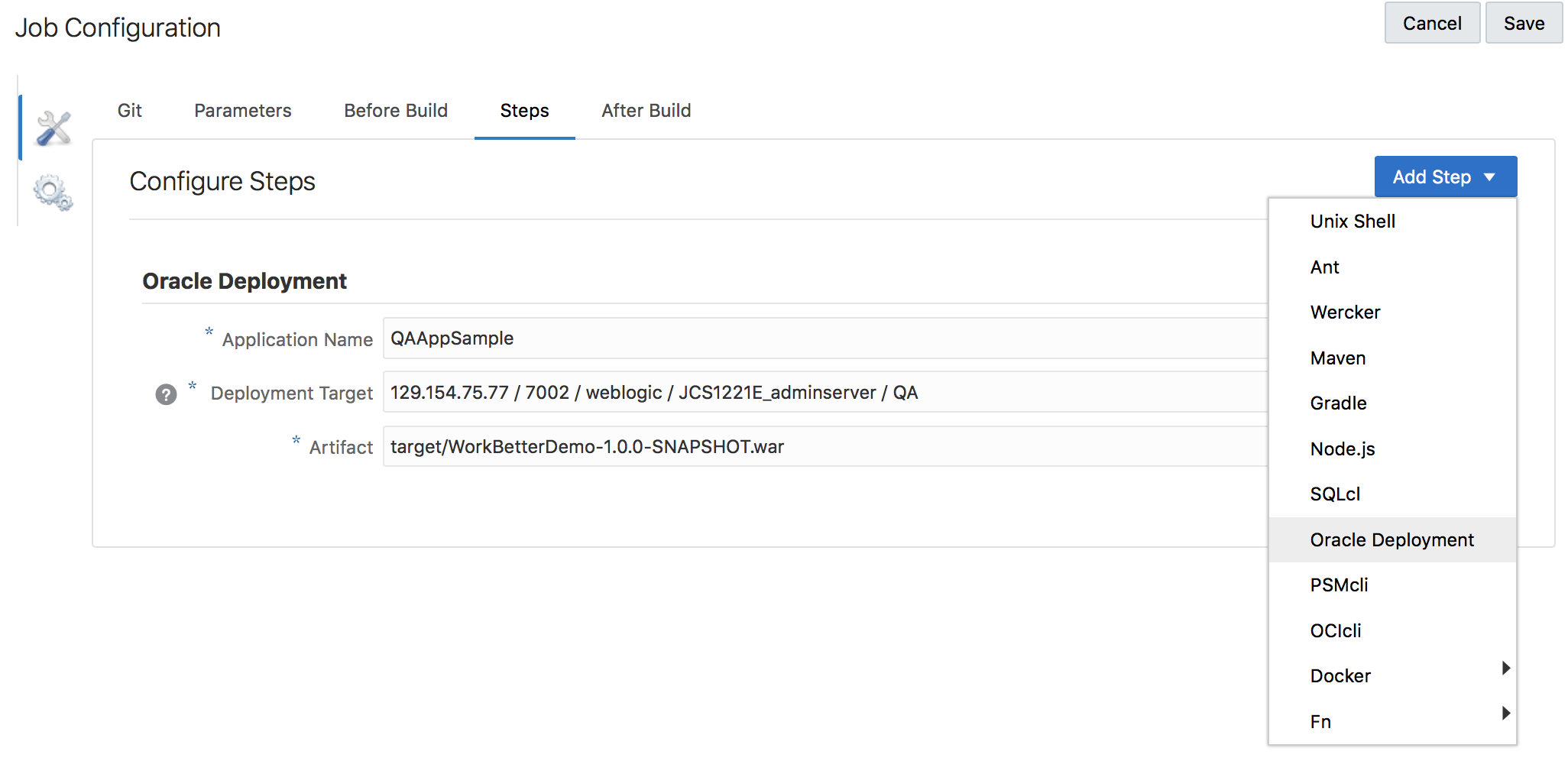
Deployment Build Step
Up until this release deployment was a separate part from our build pipelines. In the new release we are introducing a new step type in your build jobs that can do deployment to Oracle Cloud services. This allows you to add these deployment-jobs to pipelines in an easier way. In addition we connected our deployment step with the environment feature in DevCS. This way you define the connections to your cloud services only once, and then you are able to reuse them in various jobs.
To learn more about these and other new features have a look at the “What’s New” document and the links it provide for our product documentation. If you have further questions, reach us on the Developer Cloud slack channel or the online forum.
