SQL injection attacks and compromised accounts are the two most common techniques that adversaries use to gain full access to sensitive data stored in databases. While user and developer education has helped, success remains limited. In certain cases, fixing application code might be unfeasible, especially for packaged or legacy applications. Web application firewalls (WAFs) claim to mitigate SQL injection attacks, but attacker can bypass these pattern-matching approaches. Allowlist-based and network-based SQL firewalls offer stronger mitigation, but not for local and encrypted traffic. Moreover, they don’t have a full run-time context required for fully analyzing SQL queries.
Considering the high value of the data stored in the database, we need an SQL firewall that comprehensively scans all SQL traffic irrespective of where it comes from, without exceptions. Enforcement hinges on the firewall’s ability to understand the SQL with its full context. This context is what the database builds while running any SQL statement, including steps to resolve synonyms, object names, or dynamically generated names, and current user context. For any security to be practical, the firewall must ideally run at wire speed and facilitate easy management and monitoring of not just one database but a fleet of databases.
Oracle Database 23ai’s SQL Firewall integration
It was precisely this challenge that the Oracle database security team undertook. We’re thrilled to announce the integration of a powerful SQL Firewall directly into Oracle Database 23ai to effectively address both SQL injection attacks and compromised account issues. What’s equally exciting is that we offer an easy solution that can have minimal impact on performance.
The new Oracle SQL Firewall offers the following features and benefits:
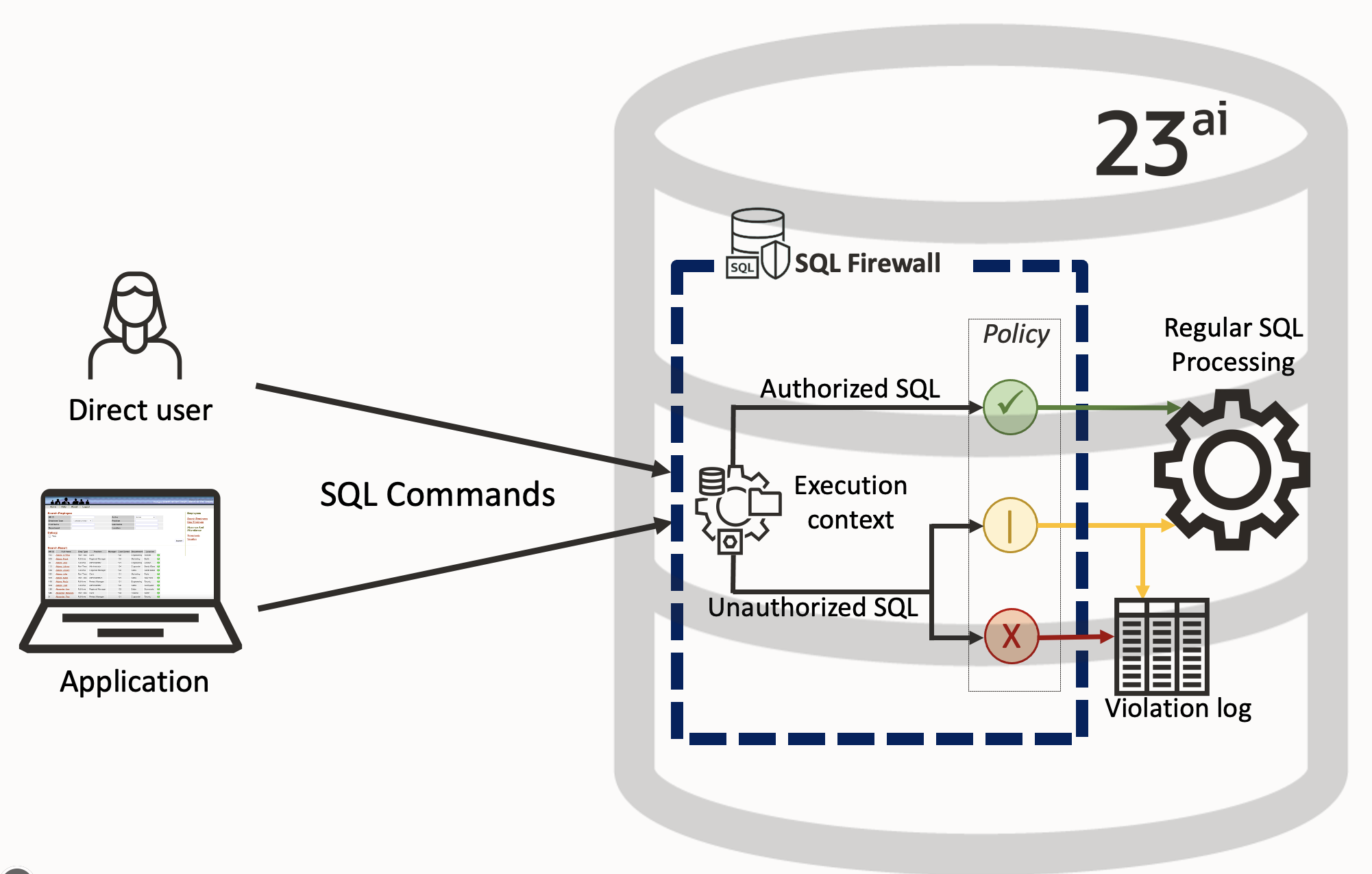
- Oracle SQL Firewall inspects all incoming database connections and SQL statements, including those from PL/SQL (Oracle’s procedural extension to SQL), whether local or over the network, encrypted or clear text. It only allows explicitly authorized SQL. For all other SQL, it logs the offending statements and raises violations. This statement could have been a SQL injection attack or a new SQL statement that the authorized user hasn’t run before.
- Customers can decide whether they want to block unauthorized SQL or only log it, giving them the flexibility on how to handle attacks.
- Oracle SQL Firewall evaluates the complete SQL and the processing context. By running inside the Oracle database server, the firewall easily handles encoding of the SQL statement, synonyms, dynamically generated object names, and any SQL statements dynamically generated in PL/SQL units.
- Oracle SQL Firewall relies on the allowlisting of the authorized SQL statements and associated trusted database connection paths while blocking the rest. You train the SQL Firewall by simply capturing authorized SQL statements for an application account. Subsequently, the firewall detects and prevents unauthorized SQL and potential SQL injection attacks.
- Oracle SQL Firewall can also block connections not coming from trusted IP addresses, operating system usernames, or program names. This function is useful when you want to put some protection in place immediately, while you create the allowlist for your applications. This feature ensures that any direct access to your databases is coming exclusively from trusted endpoints.
By building Oracle SQL Firewall inside the database and streamlining its implementation, the performance overhead of Oracle SQL Firewall is negligible, making it suitable for all production workloads. Because Oracle SQL Firewall is inside the database, you don’t need to deploy or manage any external components, greatly simplifying deployment.
Figure 1 shows how Oracle SQL Firewall operates inline within the Oracle Database 23ai kernel, evaluating every incoming SQL statement, regardless of origin. Oracle SQL Firewall always generates a violation log when it detects a violation of its rules. However, you can configure SQL Firewall to either allow or block violating SQL statements.
Managing Oracle SQL Firewall
Oracle SQL Firewall policies work at a database account level, whether of an application account or a direct database user, such as a reporting user or a database administrator. This flexibility allows you to gradually build up the protection level of the database, starting from either the database administrators or the application accounts.
You can manage Oracle SQL Firewall in multiple ways. We recommend PL/SQL procedures in the SYS.DBMS_SQL_FIREWALL package if you have a standalone implementation and are proficient in managing through commands.
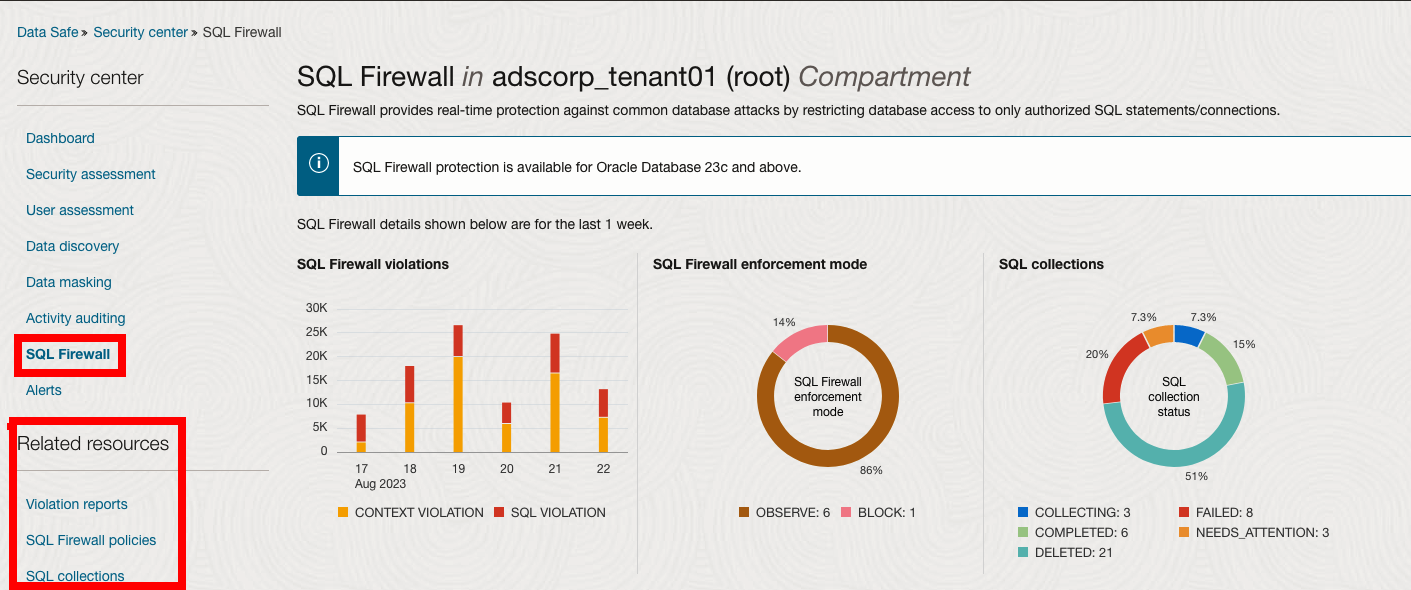
If you’re looking for UI-based management or to manage multiple Oracle SQL firewalls centrally, Oracle Data Safe is your answer. If you’re already an Oracle Data Safe customer using it for user and security assessment, activity auditing, sensitive data discovery, and data masking, you can now use the same Data Safe cloud service for managing Oracle SQL Firewall and preserve your investment.
The Data Safe unified console has been extended to manage SQL Firewall. Administrators can use the console to collect SQL activities of application accounts, monitor the collection progress, create Oracle SQL Firewall policies with allowlist rules (allowed contexts, allowed SQL statements) from the captured SQL activities, and enable SQL Firewall policies. When a firewall policy is enabled, Data Safe automatically collects the firewall violation logs from the database and stores them in Data Safe. Those logs are then available for online analysis and reporting across your database fleet, as shown in Figure 2.
You can use the Data Safe REST APIs, software developer kits (SDKs), CLI, and Terraform for further automation and integration. You can also utilize the larger Oracle Cloud Infrastructure (OCI) ecosystem for integrating Oracle SQL Firewall violations with its alerts and notifications.
Complementing industry-leading database security features within the Oracle database for authentication, access control, encryption, and auditing, Oracle SQL Firewall inspects all incoming SQL statements and allows only authorized SQL statements. Oracle SQL Firewall solution provides unmatched security and administrative convenience through Data Safe.
Get started today
We invite you to join the Oracle Data Safe limited availability program for managing Oracle SQL Firewall in your Oracle Database 23ai. To try it out before it’s generally available, open a service request with Oracle Data Safe with the title “Oracle SQL Firewall Limited Availability Program.”
For a demo of Oracle SQL Firewall in Oracle Database 23ai, see Using SQL Firewall with Oracle Database 23ai Free. You can also manage SQL Firewall using PL/SQL or Oracle Data Safe. For a demo of using Data Safe to manage SQL Firewall, see Introducing SQL Firewall – a new security capability in Oracle Database 23ai.
To learn more, see to the following resources:
- GitHub SQL Firewall sample demo script
- Chapter 13 Using SQL Firewall of Oracle Database 23ai Security Guide
- Oracle Database Free – Developer Release forum
