Oracle is excited to announce the release of Oracle Cloud Infrastructure (OCI) Bastion service, a new, fully managed service providing secure and ephemeral Secure Shell (SSH) access to the private resources in OCI. OCI Bastion, like the bastion fortress of medieval times, improves security posture by providing an additional layer of defense against external threats.
Oracle knows that an organization’s mission-critical workload in OCI should not be on the public internet. In the past, customers had to resort to complex networking architectures of public and private subnets, jump hosts, or rely on third-party services to access the private resources in OCI. Those methodologies could be costly, difficult to maintain, challenging for compliance, and hard for administrators to maintain a strong security posture. OCI Bastion service eliminates the need for deploying complex networking or jump hosts to easily build SSH access to private resources. The service makes security easier for customers to implement and maintain, which is at the core of Oracle’s approach to cloud security.
Ditch the jump host
The cost, deployment, and management of using a jump host is a huge pain point which can lead to a weaker security posture for the customer. The OCI Bastion service removes the public and private virtual cloud network (VCN) hassle for access to a jump host. No public IP is needed, resulting in no surface attack area or zero-day vulnerabilities with a dedicated jump host. Customers also eliminate shared credentials, broad access limits, and other bad habits of using jump hosts. OCI Bastion integrates with OCI Identity and Access Management (IAM) and allows the organization to control who can access a bastion or a session and what they can do with those resources. In addition, the health, capacity, and performance of OCI Bastion can be monitored using metrics, alarms, and notifications integrated with OCI Events, OCI Audit and Oracle Cloud Guard.
OCI Bastion allows an IT administrator to easily create a bastion with just-in-time access and is included with any OCI tenancy. Overall, OCI Bastion saves the cost and hassle of jump hosts while improving security posture.
Easy for administrators to set up
For security administrators, OCI Bastion provides a faster and simpler way to implement secure access to private resources. The administrator has centralized bastion control, specifying which IAM users or groups have access to which private end point(s). Access to the bastion is restricted to the allowlist of the operator IP range. Connections are also ephemeral; after the user-defined session time-to-live (TTL), admin-defined session TTL, or explicit session termination, the session is terminated.
Security lists also are used on the subnet level to restrict incoming traffic to the IP address that match an allowed Classless Inter-Domain Routing (CIDR) as set by the administrator. Using OCI Bastion, administrators can control access more easily for operators. Set up a bastion with the following steps:
- Grant permissions for controlling bastions to other administrators and use sessions to operators.
- Create a bastion specifying the same VCN as the private end point resource and the allowlist and maximum session TTL restrictions.
- Restrict the VCN target subnet ingress rule to only allow specific port traffic from the private end point of the bastion.
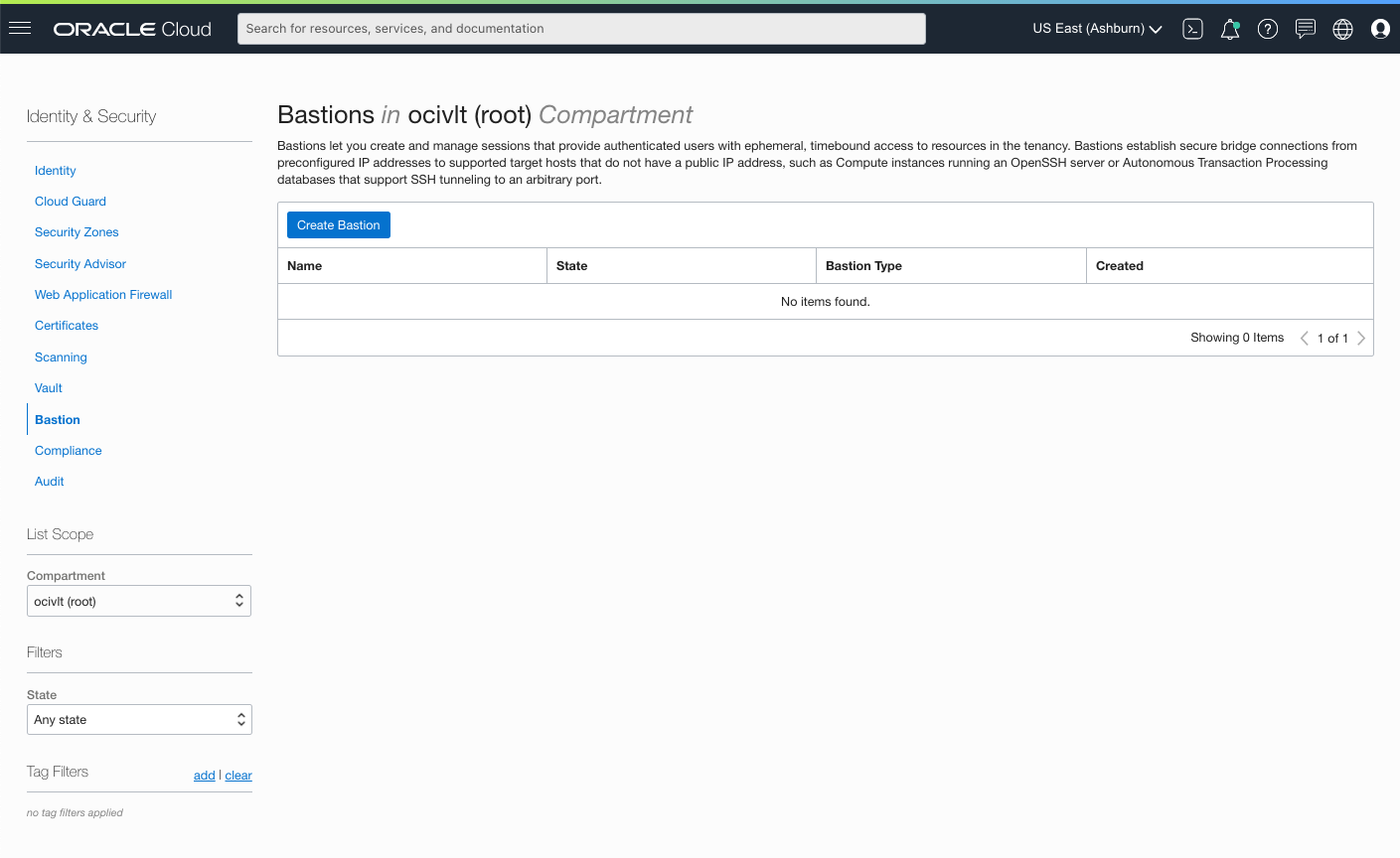
Figure 1: Create a bastion from the Identity and Security menu of Console
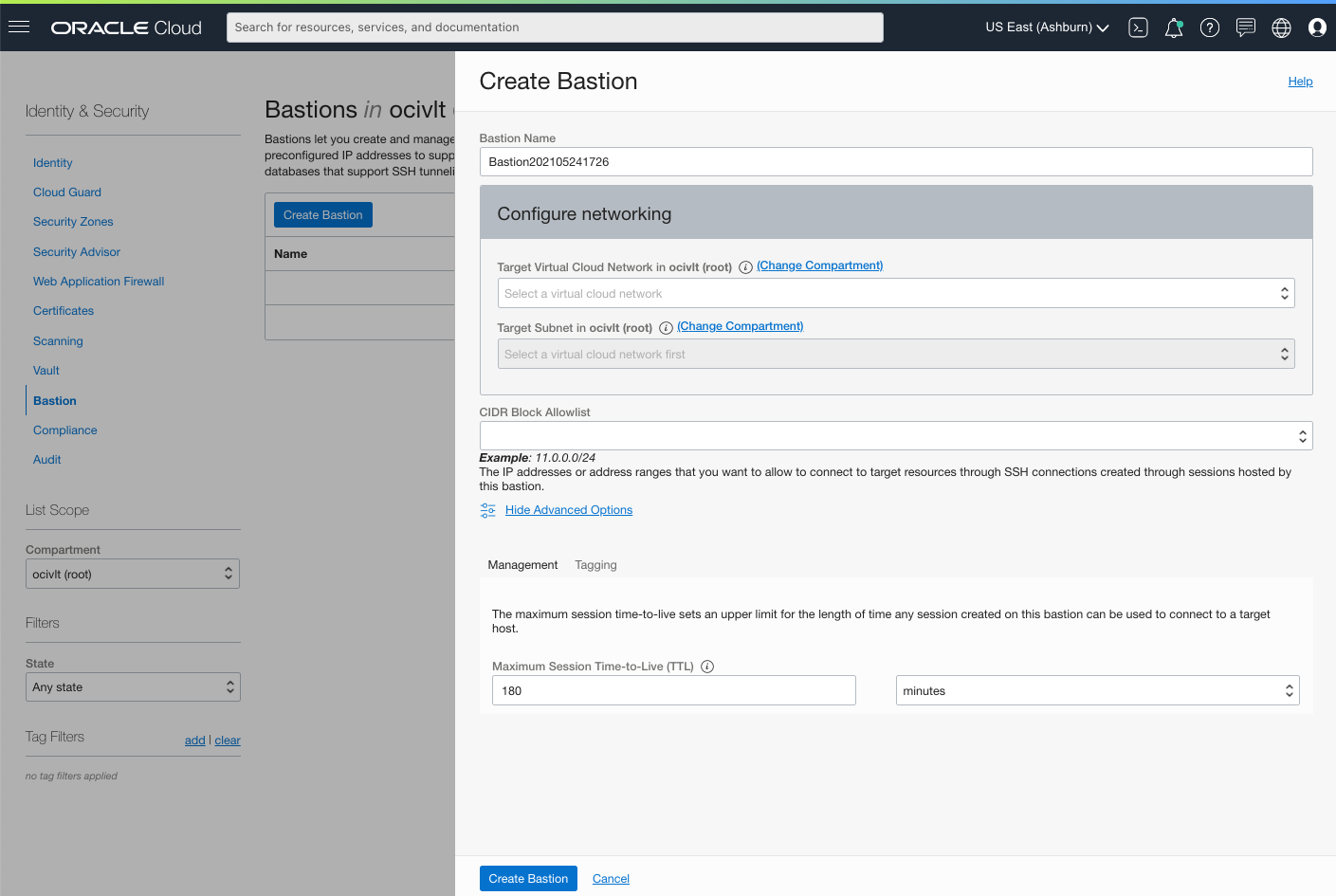
Figure 2: Create a bastion with Allowlist and Time-to-Live control
Easy for operators to use
When an operator needs to access a private end point, they go to OCI Bastion and see only the bastions that they have permissions to see. In creating a session, the operator selects the session parameters, within the restrictions of the bastion. Users can typically use SSH to log into a remote machine, run commands, establish tunneling through forwarded TCP ports, transfer files using the SSH file transfer (SFTP), secure copy protocols (SCP), and establish connections to database.
There are two types of sessions, managed SSH and port forwarding, which depends on the type of target resource.
- Managed SSH sessions simplify SSH access to native Oracle Linux images running Oracle Cloud Agent (OCA) by propagating the key to the host.
- Port forwarding (also known as SSH tunneling) creates a secure connection between a specific port on the client machine and a specific port on the target resource. Using this connection, the user can relay other protocols to such as resources like Windows RDP over SSH, MySQL, ATP, OKE v2 and any other resource which allows Secure Shell Protocol (SSH) access.
With the session type determined, the operator can choose a session target from the private end point resources, made available by the administrator at bastion creation. The operator adds the target resource username, copies over users public SSH key, and creates a session. To connect to a session, the operator copies the SSH session command provided by OCI Bastion into a local terminal window or Cloud Shell to connect.
Bastion sessions let authorized users in possession of the private key in an SSH key pair connect to a target resource for a predetermined amount of time. The public key is provided in the SSH key pair at the time the session is created, and then at the connection, the private key is provided. In addition to presenting the private key, an authorized user must also attempt the SSH connection to the target resource from an IP address within the range allowed by the bastion’s client CIDR block allowlist.
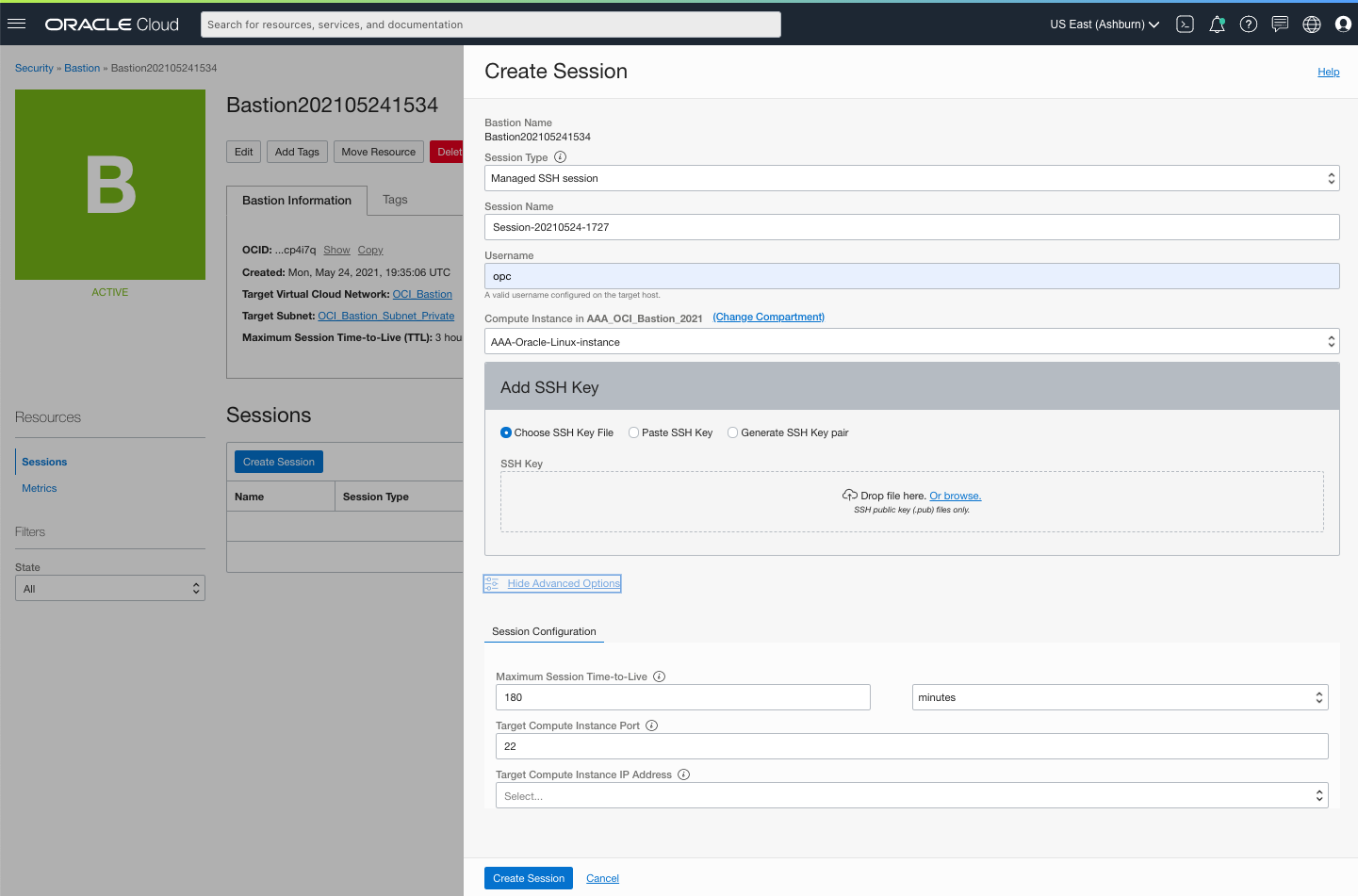
Figure 3: Creating a session
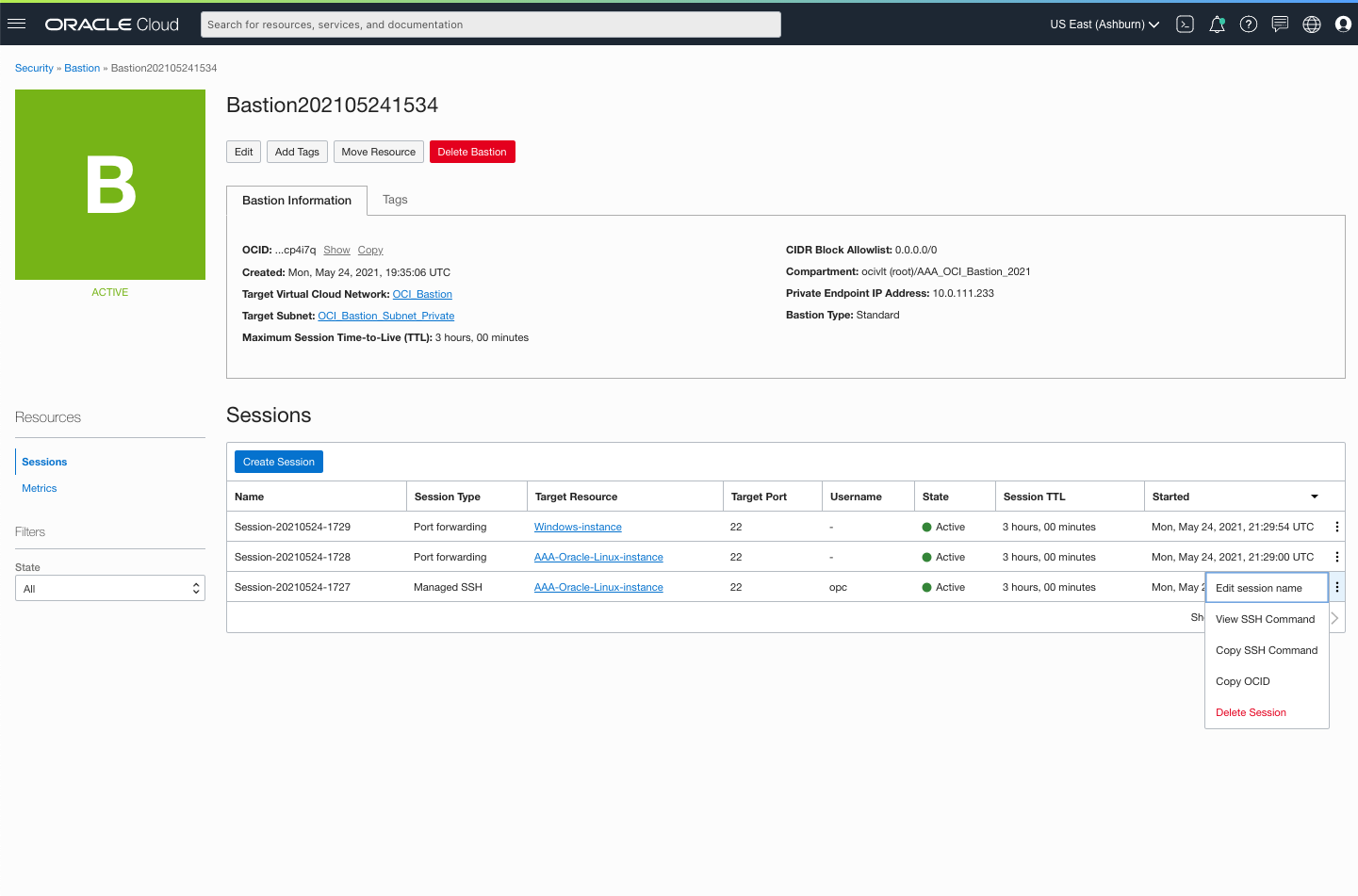
Figure 4: Connecting to a session
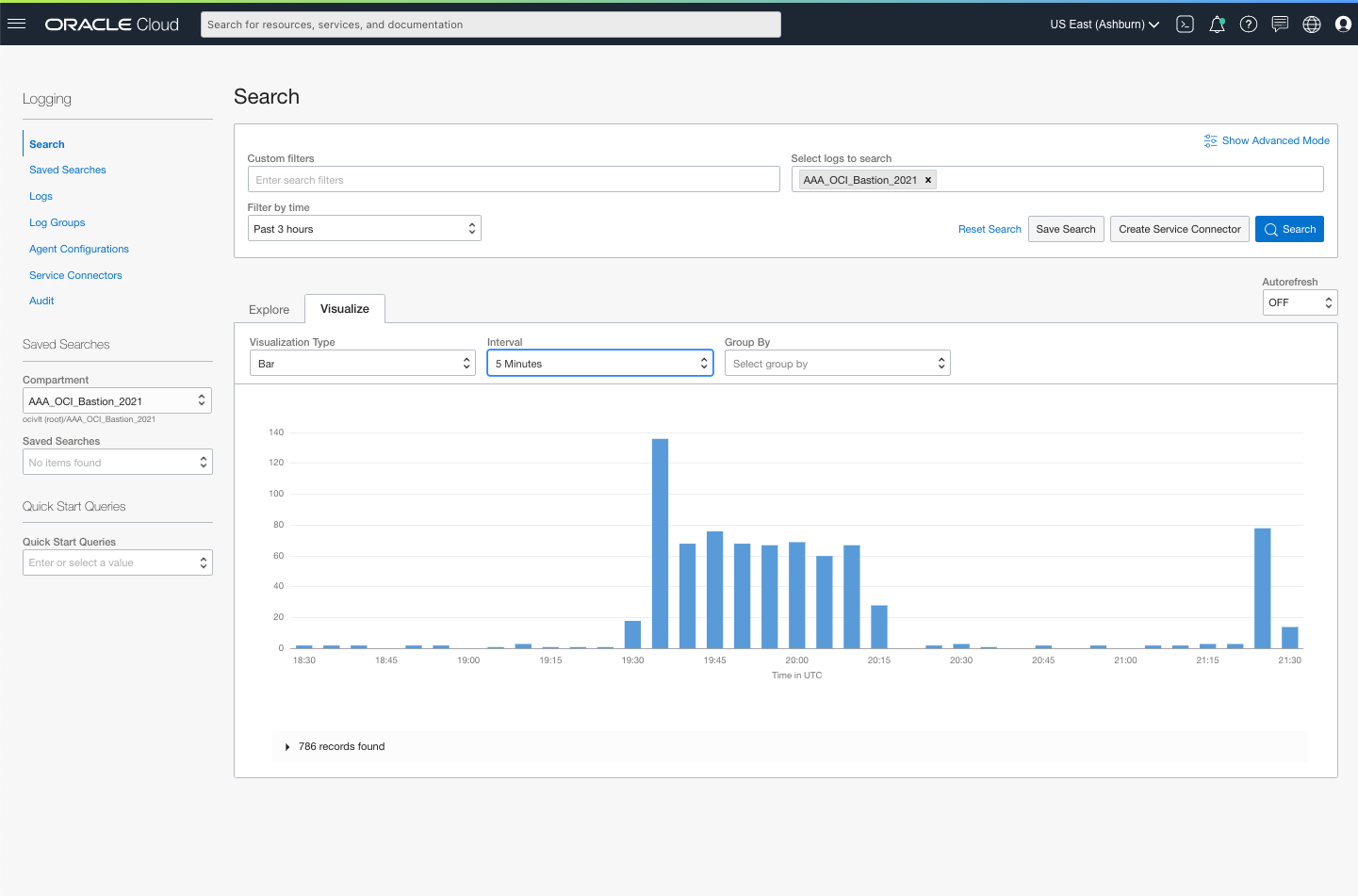
Figure 5: Audit
Summary
In summary, OCI Bastion service simplifies SSH connections to private end points, helping to improve the security posture. The service is easy to implement through the Console, API, or CLI; it’s included with all OCI tenancies, including the always-free Oracle Cloud offering. Learn more to get started today and sign up for the Oracle Cloud free tier to try out Oracle Cloud Infrastructure Bastion service.