When enterprises run their applications in public clouds like Oracle Cloud Infrastructure (OCI), their developers, security teams, and other employees need secure and private access to their resources. Some popular services that grant that connectivity are VPN solutions (directly into the cloud or through the data center) and bastion (jump) hosts.
Bastion hosts are the go-to approach for many enterprises. Why? Infrastructure provisioning cycles can turn in minutes and hours, and bastion hosts and NAT are the straightforward solution, quick to deploy. They’re placed in environments to provide access to cloud engineering, development teams, and DBAs for expediency. Unfortunately, bastion hosts also introduce risk and friction as the environment fluctuates throughout its normal lifecycle and scales out. Some common challenges:
-
Inability to revoke access without eliminating the entire bastion host, generating new keys, and redistributing them
-
Lack of granular access controls
-
Lack of user auditing and observability
-
Friction for DBAs and developers who need to use the tools and workflows they’re already familiar with
-
Without proper hardening, presents a target and entry point for bad actors
VPN solution from Aviatrix
Aviatrix is a multicloud networking and security platform that works with OCI to solve the challenges related to cloud networking (including cloud access). One of the most popular services offered by Aviatrix is the VPN service, which provides a cloud-first and cloud-aware approach. The solution takes only a few minutes to deploy, all the elements run in OCI (no dependency on the data center), and the user experience is first class.
Two main components of the platform are the Aviatrix Controller and gateways. The Aviatrix Controller (available through Oracle Cloud Marketplace) is a VM that you can launch into your virtual cloud network (VCN) with a few clicks from the Oracle Cloud Infrastructure Console or with Terraform.
After the Controller is deployed, you use it to deploy one or more Aviatrix gateways (through the controller UI or using Terraform). These gateways are VMs that run in your VCNs and can have various roles, one of which is the role of a VPN “concentrator.” From the Controller, you create your VPN user accounts and group profiles, or integrate the platform with an external identity provider for user authentication and authorization. After this is done, you distribute the VPN configurations to your users, and they can start connecting to the resources in OCI via Aviatrix VPN gateways.
The following figure shows an example of the Aviatrix platform deployed for databases in OCI.
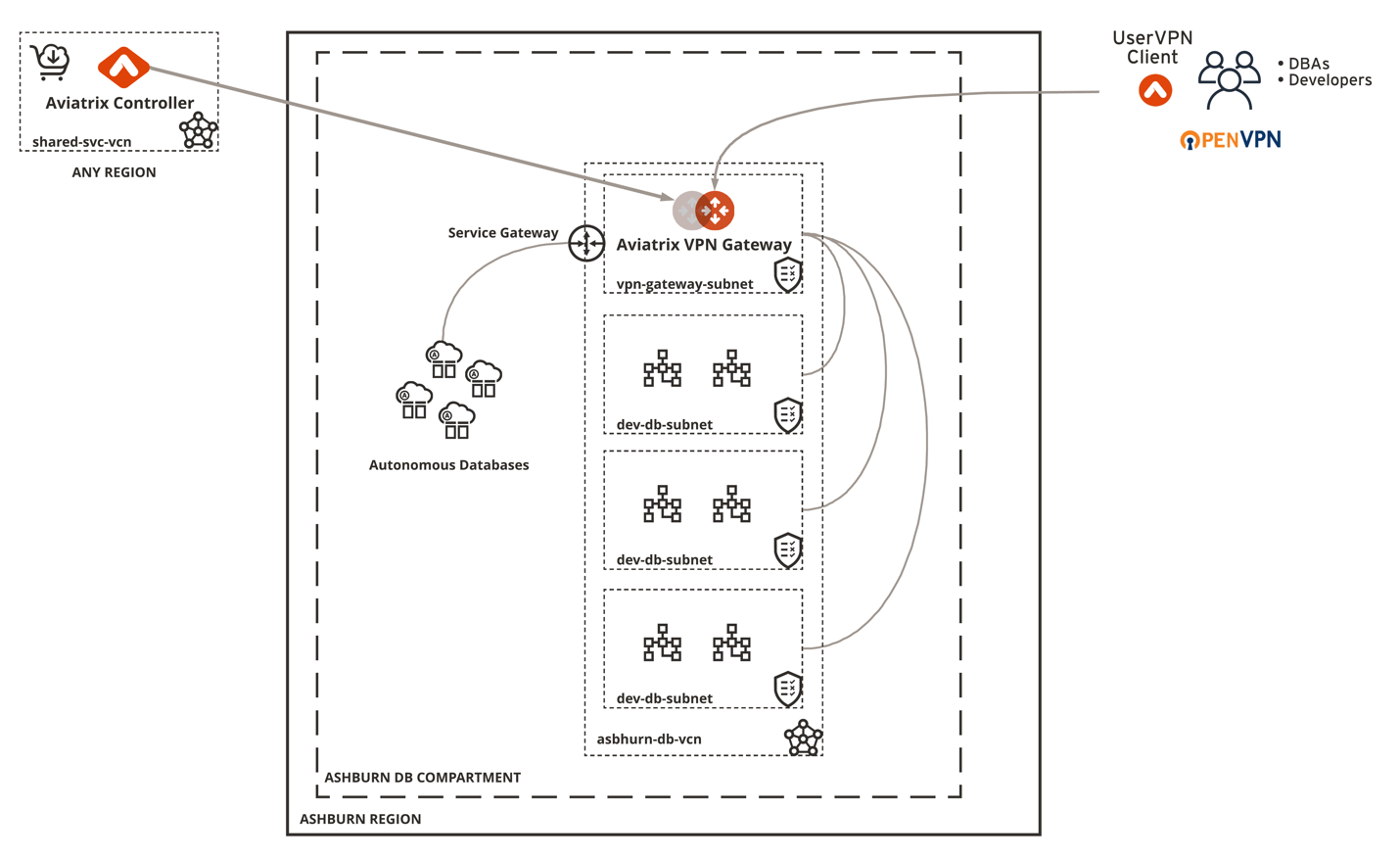
Figure 1: Example deployment for databases
Apart from the VPN solution, Aviatrix enables Oracle Cloud customers to easily and securely address common cloud networking use cases while providing full visibility of and analytics for the cloud network (multicloud connectivity, segmentation, secure transit, site-to-cloud, and more).
Aviatrix VPN solution features
The Aviatrix VPN solution includes the following features:
VPN management
-
Centrally managed: A single interface lets you manage all VPN users, VPN certificates, and VPN user visibility.
-
OpenVPN compatible: The solution is built on OpenVPN and is compatible with all OpenVPN client software.
-
Force disconnect: Any admin can force disconnect a VPN user from the Controller console.
-
Dashboard view: All active VPN users and their connection history are visible from the Controller console dashboard.
-
API: Support API is available for all management activities.
Authentication options
-
LDAP/Active Directory integration: Authenticates a VPN user from Aviatrix gateways in addition to VPN certificate authentication.
-
DUO integration: Authenticates a VPN user from Aviatrix gateways in addition to VPN certificate authentication.
-
Okta integration: Authenticates a VPN user from Aviatrix gateways in addition to VPN certificate authentication.
-
MFA integration: Combines LDAP and DUO for multifactor authentication.
-
Client SAML integration: Authenticates a VPN user directly from the Aviatrix VPN client to any identity provider via SAML protocol.
Authorization
-
Profile-based access control: Each VPN user can be assigned to a profile that is defined by access privileges to network, host, protocol, and ports. The access control is dynamically enforced when a VPN user connects to the public cloud through an Aviatrix VPN gateway.
Logging integration
-
VPN user: VPN user connection history and bandwidth usage can be logged to Splunk, SumoLogic, ELK, Remote Syslog, and DataDog.
-
User activity: Each VPN user TCP/UDP session can be logged to Splunk, SumoLogic, ELK, Remote Syslog, and DataDog.
Client software
-
OpenVPN client software: All OpenVPN client software is supported. The supported clients are macOS, Windows, iOS, Android, Chromebook, Linux, and BSD.
-
Aviatrix VPN client: The Aviatrix VPN client supports macOS, Windows, and Linux Debian distribution and BSD distribution. Choose the Aviatrix VPN client if you require SAML authentication directly from VPN client software.
Ready to learn more?
Explore the Aviatrix listing on Oracle Cloud Marketplace today:
