Landing zones allow you to rapidly onboard into Oracle Cloud Infrastructure (OCI) by providing a templated deployment of multiple OCI services that contain all our best practice guidance. You can deploy landing zones in both the Quick Start and Oracle Resource Manager sections of the Oracle Cloud Console, allowing you to get up and running quickly within OCI.
Today, we’re delighted to highlight a recent and significant update to the enterprise landing zone that positively enhances your experience when making your move into OCI, known as the workload expansion. Following some excellent feedback, we have taken the workload components of the enterprise landing zone configuration and placed them into a separate stack that you can deploy after the creation of the baseline stack.
This expansion gives you the following benefits:
-
Control over migration: Separating the stack allows you to migrate workloads into the enterprise landing zone when ready and ensures that every necessary element of the stack is provisioned before doing so.
-
Consistent deployments: With this stack being repeatable, we have reduced the potential for configuration drift and afforded a consistent environment to deploy within for each of your workloads
-
Scalable growth: As you decide to migrate more workloads, simply deploy the stack again to make migration smoother over time.
What does the workload expansion deploy?
The workload expansion deploys the following resources into your OCI tenancy, on top of the enterprise landing zone.
Compartments
The workload expansion adds the following Identity and Access Management (IAM) groups and policies to manage your workload.
| Compartment | Location | Description |
|---|---|---|
| Workload A compartment | Common infra compartment | This compartment houses your workload when you’re ready to deploy into the landing zone. |
IAM policies and groups
The workload expansion adds the following IAM groups and policies to manage your workload.
| Group | Policy name | Description |
|---|---|---|
| workload-admins | OCI-LZ-<WorkloadName>-WorkloadAdminPolicy | Compute or workload administrators can manage all compute resources that host workloads. This ability includes creating instances, instance pools, autoscaling configurations, cluster networks, custom images, and images in the Partner Image catalog. |
| workload-users | OCI-LZ-<WorkloadName>-WorkloadUserPolicy | Compute or workload users can use all Compute instances for the workload. Workload users can also create Console connections, launch instances on dedicated virtual machine (VM) hosts, and create images in the partner image catalog. Workload users can’t create custom images or use instance pools, autoscaling, or cluster networks. |
| workload-storage-admins | OCI-LZ-<WorkloadName>-StorageAdminPolicy | Storage administrators can manage storage requirements for the workload. The requirements include OCI Object Storage buckets and objects, File Storage resources, and Block Volume volumes and backups. |
| workload-storage-users | OCI-LZ-<WorkloadName>-StorageUserPolicy | Storage users can write and read from any Object Storage bucket in the associated workload compartment. |
| workload-database-admins | OCI-LZ-<WorkloadName>-Database-Admin-Policy-Network | Database admin users can manage databases, database storage, and networking. |
Virtual cloud network (VCN)
The workload expansion adds the following IAM groups and policies to manage your workload.
| Network Name | Type | Description |
|---|---|---|
| Workload A | Private subnet | Subnet for your workload to reside in that can be used for web and application servers depending on your workload type |
| Workload A – database | Private subnet | Subnet to deploy your database in that has no direct access to the internet for security purposes |
Workload expansion architecture design
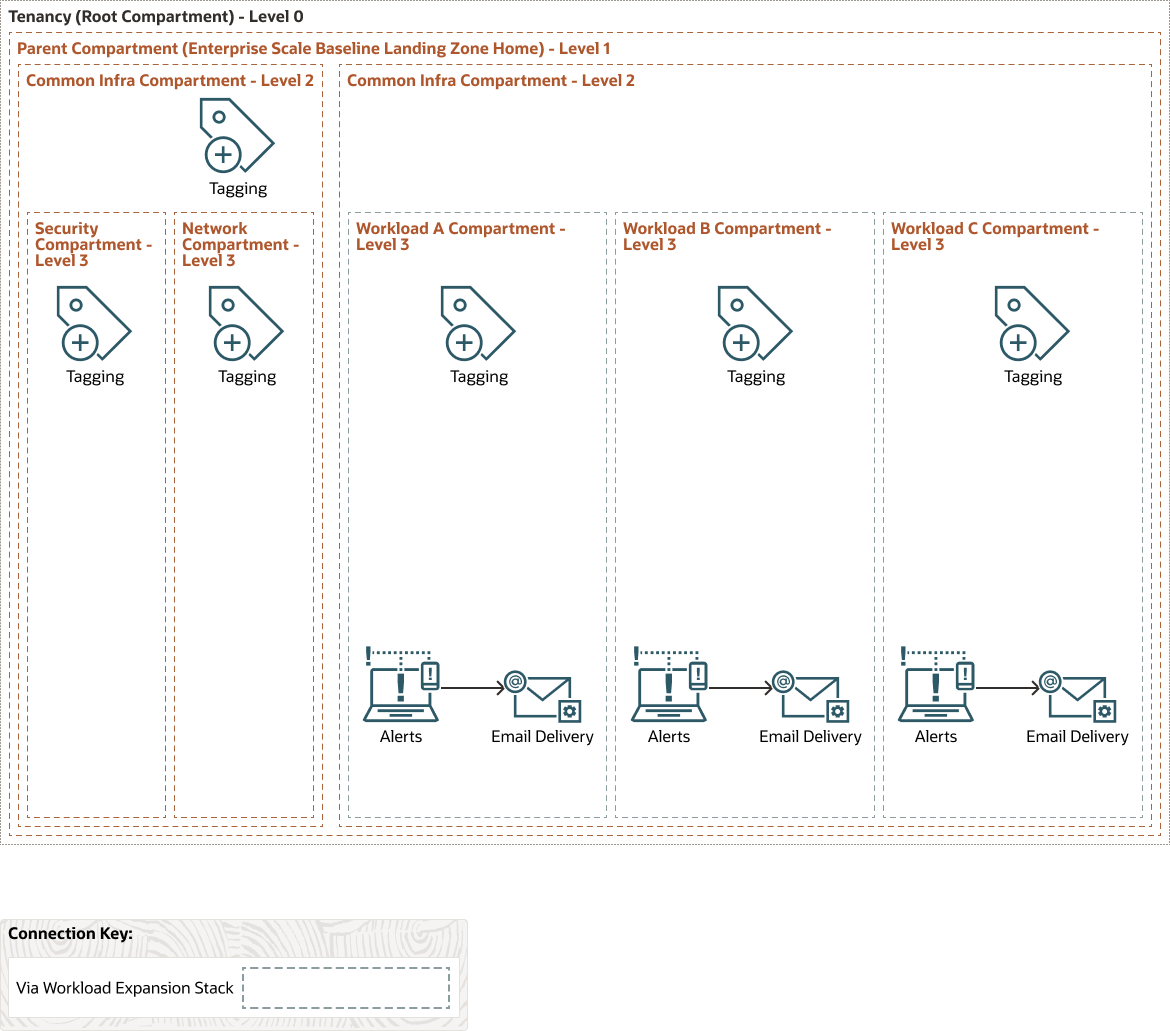
The following diagrams illustrate the workload expansion architecture:
Compartments
The following diagram shows the workload compartments, which are now deployed in the Expansion stack. Each compartment—A, B, and C—are separate runs of the stack designed to house individual workloads.
Identity and Access Management
The workload expansion defines the following policies, specific to workload personas within a typical enterprise tenancy.

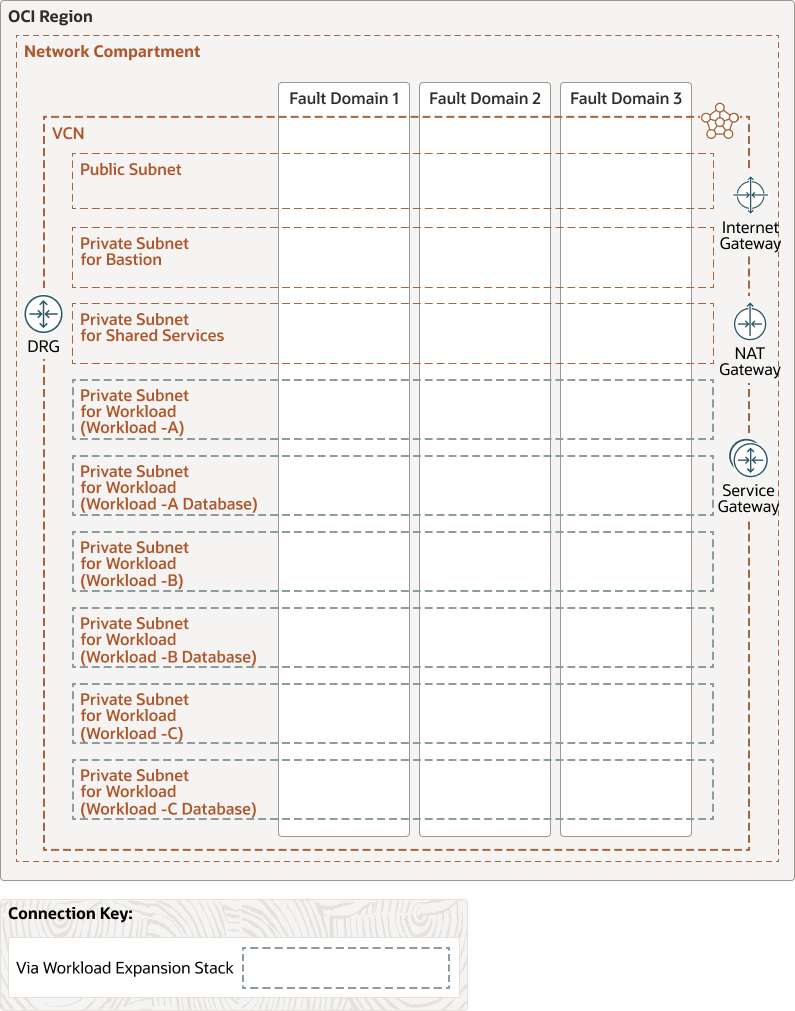
Networking
After the compartments have been deployed, more networks are also provisioned to house the workloads securely.
Prerequisites
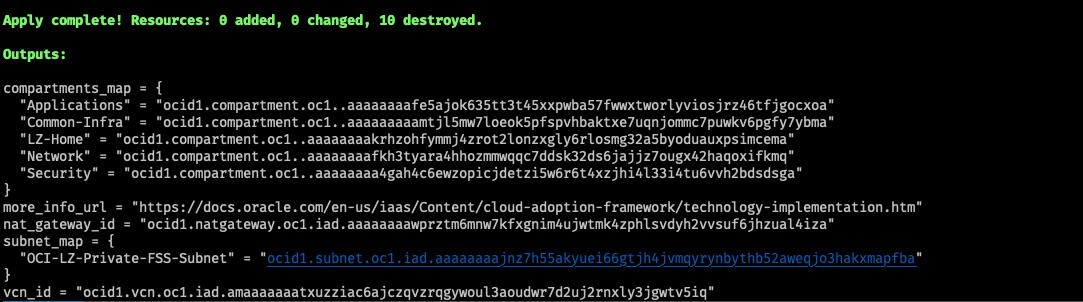
The workload expansion is not a standalone deployment and requires that you deploy the enterprise scale baseline landing zone. After you have deployed the baseline, collect the following information from the baseline stack outputs:
-
Tag values for the CostCenter and GeoLocation tags. Every resource created by the landing zone stack is tagged with the values that you provide.
-
The name of the new workload compartment and the OCID of the parent application compartment to attach the new workload compartment to
-
The name and OCID of the networking compartment in which the virtual cloud network (VCN) resides
-
The VCN and network address translation (NAT) gateways OCIDs to use when you create the workload subnets
-
CIDR blocks for the private and database subnets created within the VCN
Deployment
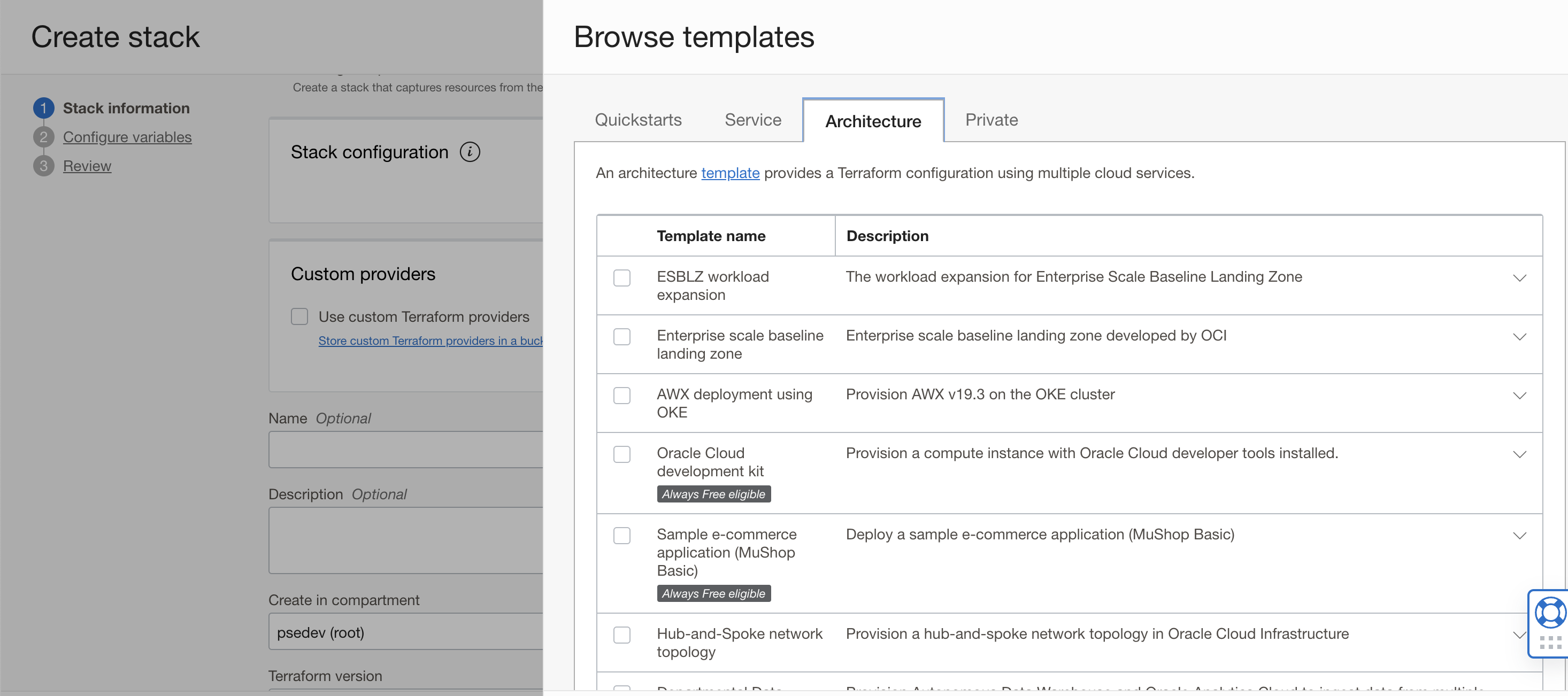
Oracle Cloud Console
You can deploy the workload expansion stack by visiting Oracle Resource Manager and accessing the templates from the Architecture tab. When you have configured the related parameters, you can deploy the stack within 10–15 minutes.
Terraform
The Terraform code for deploying this reference architecture is available in Github.
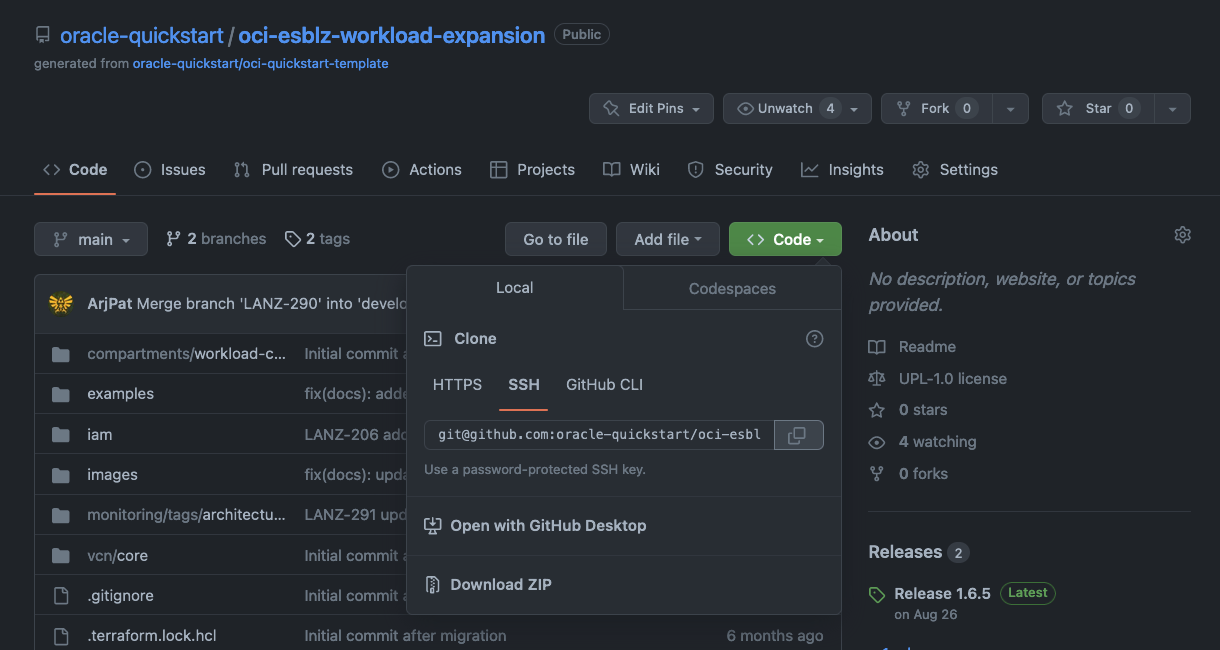
-
Clone the repository on your local machine.
-
Create a
terraform.tfvarsfile and populate with the required variables or override existing variables. An example tfvars file is included for reference. Using this file is the preferred way to run the stack from the command line because of the large number of variables to manage. -
For the following input variables, use the values collected from the prerequisites. These values allow you to use the networking and IAM resources from the base.
-
network_compartment_id -
applications_compartment_id -
network_compartment_name -
nat_gateway_id -
vcn_id
-
-
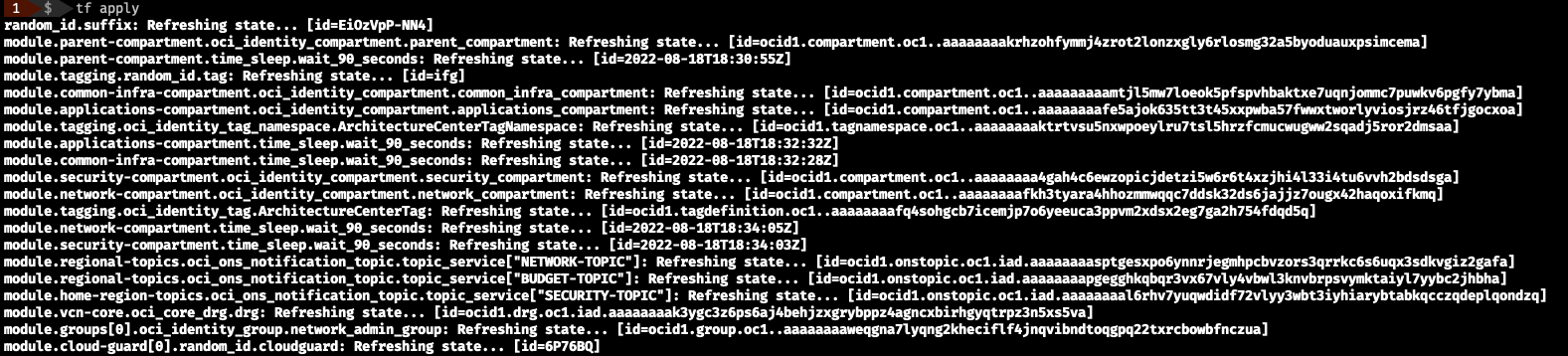
After you supply the required variables in the
terraform.tfvarsfile, run the following commands in the root of the repository:-
terraform init -
terraform plan -
terraform apply
-
After you have followed either of these methods to deploy the stack, you can plan your migration of your first workload into OCI. Any subsequent workloads that you want to bring into your tenancy require more runs of the workload expansion stack so that each environment is provisioned ready for you to migrate into.
Get started
To get started today and begin deploying, use the following table to begin your journey into Oracle Cloud Infrastructure using landing zones:
| To deploy this architecture | Click |
|---|---|
| Enterprise landing zone |  |
| Workload expansion |  |
For more information, see the following resources:
