We are pleased to announce transit routing to Oracle Cloud Infrastructure services. With this enhancement, you can access services hosted in the Oracle Services Network from your on-premises network by using Oracle Cloud Infrastructure private access technologies, such as FastConnect private peering and VPN Connect.
This feature addresses customer requirements for security, privacy, and encryption for Oracle services traffic. Your on-premises network no longer needs public access technologies with a public IP address, internet access, or FastConnect public peering to access business-critical services in the Oracle Services Network. Transit routing is available in all regions, at no additional cost. For more information, see Transit Routing: Private Access to Oracle Services.
The Oracle Services Network is a conceptual network in Oracle Cloud Infrastructure that is reserved for Oracle services. The Oracle Services Network provides access to over 25 services today, with other Oracle services being constantly added. These services include customer favorites such as Object Storage and Autonomous Database, along with many other foundation services provided with Oracle Cloud Infrastructure.
Sample Topologies
Here are some sample topologies for how you can use this feature from your on-premises environment. If you add transit routing to the Oracle Services Network to an existing FastConnect private peering or VPN Connect session, you can achieve these topologies by taking any private connectivity setup to Oracle Cloud Infrastructure and performing the following four actions.
For detailed instructions, see Setting Up Private Access to Oracle Services.
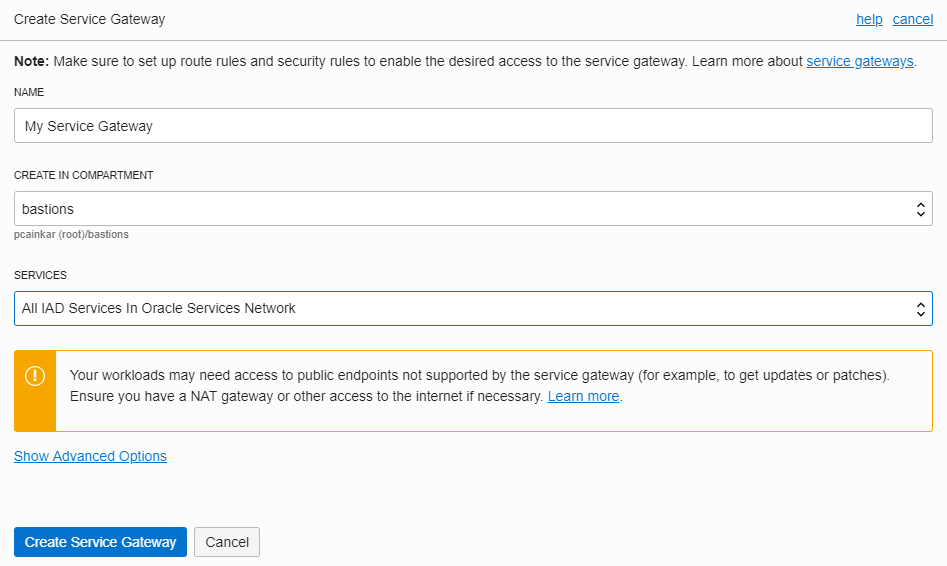
1. Add a Service Gateway to Your VCN
In the Oracle Cloud Infrastructure Console, go to Networking > Virtual Cloud Networks.
Select the virtual cloud network (VCN) to see the details page.
Click Service Gateways, and then create a service gateway.
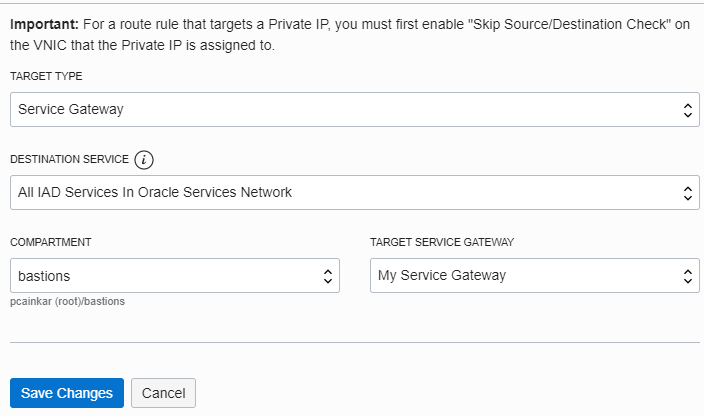
2. Enable Routing of the Oracle Services Network CIDR Alias on your DRG with a Route Target of the Service Gateway
On the details page of the VCN, click Route Tables.
Select your dynamic routing gateway (DRG) route table.
Add a route rule, and specify Service Gateway as the target type.
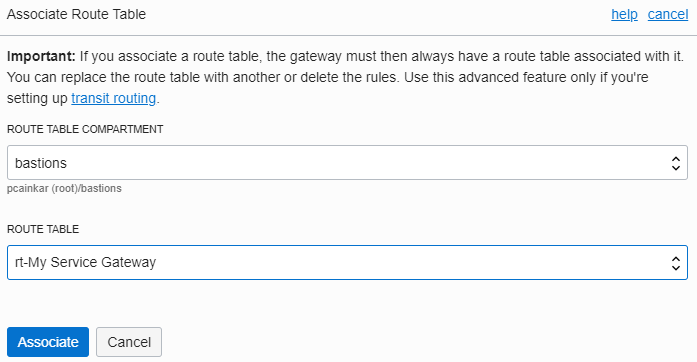
3. Associate a New Route Table with Your Service Gateway
On the details page of the VCN, click Service Gateways.
For the service gateway, click the actions icon (three dots), and then click Associate With Route Table.
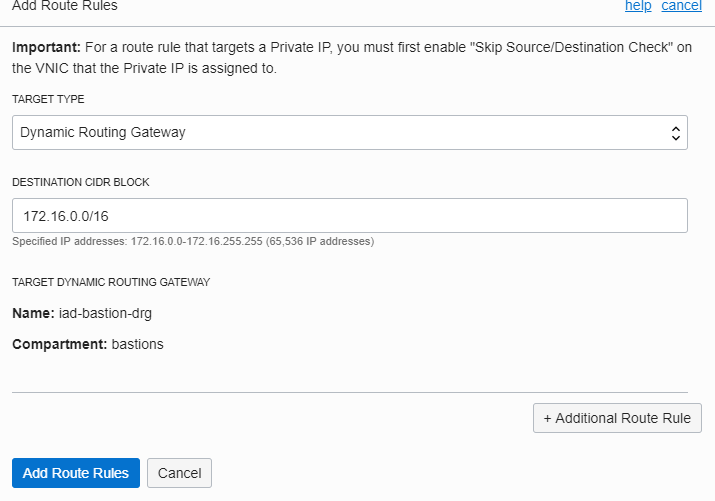
4. Enable Routing of Your On-Premises CIDR with a Route Table Entry on the Service Gateway’s Route Table
On the details page of the VCN, click Route Tables.
Select your service gateway route table.
Add a route rule, and specify Dynamic Routing Gateway as the target type.
Access from On-Premises with FastConnect Private Peering or VPN Connect
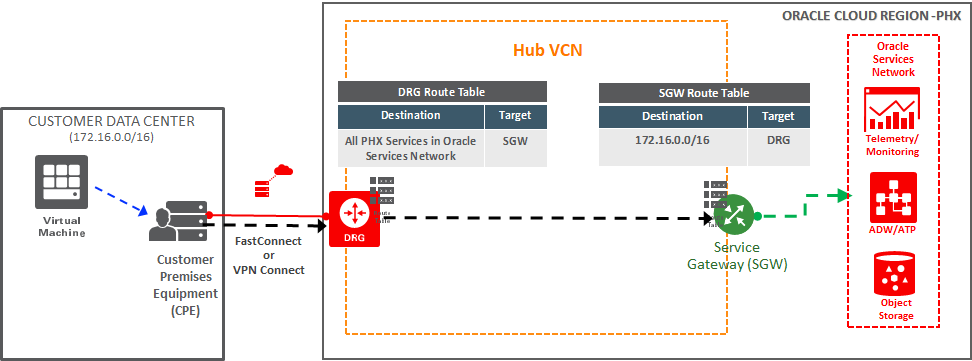
The following diagram shows a primary FastConnect private peering connection combined with a backup VPN Connect accessing Autonomous Database and Object Storage on the Oracle Services Network. Although this topology shows the combination of both access technologies, any combination or one or both can be used with minimal variance.
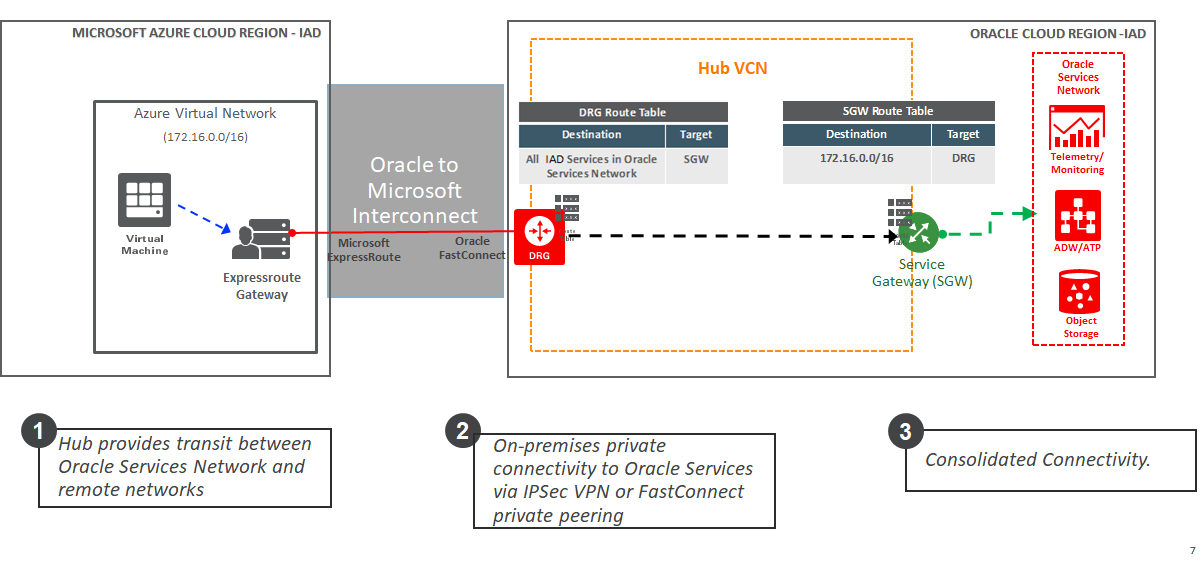
Access from Microsoft Azure to the Oracle Services Network Through Cloud Interconnectivity
Earlier this year, Oracle Cloud Infrastructure and Microsoft Azure enabled connectivity between our clouds to provide customers with low-latency, high-speed access to our joint products and services. The following topology shows a customer using an application hosted on Microsoft Azure to access Autonomous Database on Oracle Cloud Infrastructure.
We expect to publish a tech note showing detailed configuration steps for this topology in the coming months. Until then, from a provisioning perspective, this connectivity lands on the Oracle Cloud Infrastructure as a FastConnect private peering connection, and therefore the setup process is the same as shown previously for on-premises networks.
We also have a detailed step by step write-up on this process in my colleagues “Building Multicloud Apps on Microsoft Azure and Oracle Cloud Infrastructure” blog.
Conclusion
You can now use private connectivity to Oracle to access the Oracle Services Network. We encourage you to read more about this feature in the documentation and release notes.
Remember, all Oracle Cloud Infrastructure tenants have enterprise-grade support services included free of charge, and customers can open a service request to access these services. If you want to share any feedback with the product team, we would love to hear from you. Send an email to feedback_oci_virtual_networking_us_grp@oracle.com.
