Identity and Access Management (IAM) solutions and services have been traditional goals for most organizations because they aim to meet their security and compliance requirements. As the organizations evolve and try to build their cloud journey, it helps in assessing the identity platform too.
In the world of compliance, cloud posture management, and infrastructure entitlement management, identity remains the common denominator. As we continually assess the risk and strengthen the security baseline, identities become the important aspect that can put organizations at risk. So, how do we secure and strengthen the identity baseline with evolving on-premises and cloud landscape? Could IAM platform modernization be the answer?

Identity and security posture
To increase the identity security posture Oracle has built cloud native services, including OCI IAM and Access Governance. We have many blog posts written for OCI IAM’s in-depth capabilities around single sign-on, multifactor authentication (MFA), and adaptive access, which you can read on the IAM blog page.
In this blog post, we walk you through the world of access governance from the Oracle’s Access Governance platform perspective, for all customers who are looking at starting or expanding their existing Identity journey. As identities are evolving way beyond on-premises applications and going in the arena of cloud software and platform as a service (SaaS and PaaS), knowing who has what access in terms of applications access is critical, as well as the cloud infrastructure entitlements.

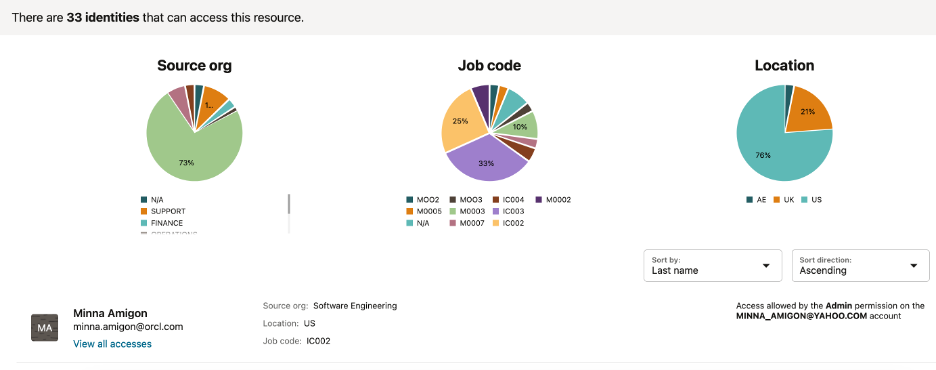
Oracle Access Governance is a cloud native Identity Governance and Administration (IGA) service. Given the large enterprise landscape of customers distributed across on-premises and cloud, Oracle Access Governance offers a simplified view of individuals’ resource access to determine whether to allow or revoke these access privileges. Organizations’ security and compliance teams can use Oracle Access Governance to meet regulatory requirements.
Oracle Access Governance provides dashboards for business owners, IT administrators, and chief information security officers (CISOs) to get a consolidated access profile of identities across the enterprise. It offers both a bottom-up view of what resources and services that an identity can access and a top-down view of an identity and what resources and services it can access.

As the field of access governance expands and manual certifications become less favorable among managers, Oracle Access Governance accommodates more proactive ways to stay on top of organizations’ compliance objectives. Oracle Access Governance also offers event-based microcertifications for access reviews triggered by specific events, times, or activities. For example, a change in employee location can automatically invoke certification and approvals for reviews. Access reviews can be more focused, including specific dates, such as anniversary dates, which aid in building the overall security and compliance baseline in the organization.
As organizations strive to meet compliance requirements, Access Governance detects unmatched accounts across all integrated applications and systems, notifying business owners about orphaned, rogue, or service accounts.
Oracle Access Governance provides the following key features and functionalities:
- Continuous discovery of users, groups, roles, applications, permissions, and policies
- Visibility into user access privileges for any resource across the organization
- Crosscloud and crossenterprise access correlation
- Spontaneous, periodic, and event-based access review campaigns to govern the access privileges assigned to users, including employees, contractors, and partners
- Prescriptive analytics and recommendations, enabling access reviewers to efficiently review and limit user access
- Automated fulfillment of access decisions
For more details, refer to the Access Governance Integrations product documentation .
Access Governance for OCI

Oracle Access Governance for OCI IAM provides the key capability of identifying who has access to which infrastructure resource. This feature is particularly crucial as workloads move to the cloud. Security of tenancy users and administrators is paramount because compromised access can lead to tenancy breaches. In principle, Oracle Access Governance for OCI provides the following capabilities:
- Who has access to which OCI resources?
- Which policy statement granted access?
- Which statements should be modified?
- Which policy hasn’t been used in years?
- Which PaaS and SaaS Service App roles map to OCI IAM roles?
Conclusion
Oracle Access Governance enables IAM modernization platforms to achieve identity governance across the enterprise. This cloud native platform establishes a centralized view of a user’s access across on-premises and cloud applications. Oracle Access Governance’s advanced machine learning serves as a key enabler to identify outliers in terms of access compared to peers in the same organization or job role. Oracle Access Governance facilitates a fast switch-on approach for monitoring identities and cloud infrastructure entitlements. This adaptability facilitates organizations to stay on top of continuously evolving compliance requirements and addressing the needs for IAM platform modernization.
Experience the capabilities of Oracle Access Governance for yourself with our hands-on LiveLab. To learn more about Access Governance, review the product documentation. To get started with Oracle Cloud Infrastructure, why not explore the Oracle Cloud Free Tier with a 30-day free trial?
For more information, see the following resources:
