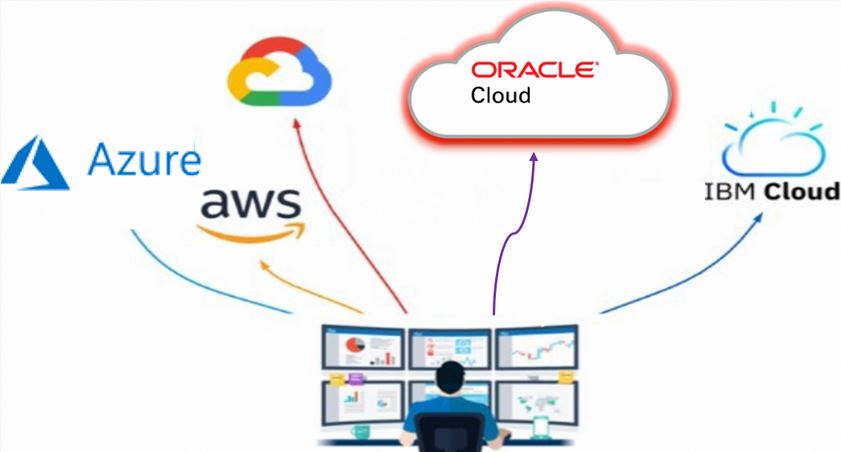
As more companies come to the cloud, what type of deployment strategy are they deciding is best for them? For most, it’s multicloud.
A multicloud strategy is the use of two or more cloud-based compute services. Multicloud can refer to any deployment of multiple software-as-a-service (SaaS) or platform-as-a-service (PaaS) cloud offerings. However, it usually refers to a mix of public infrastructure-as-a-service (IaaS) environments.
Multicloud’s benefits and challenges
Organizations adopt a multicloud strategy for the following benefits:
-
Economics: Choosing among different cloud service providers allows customers to reduce costs and optimize the overall IT expenditure.
-
Capabilities: As enterprises develop different needs, they’re likely to discover differences in cloud offerings.
-
Availability: Distributing applications among multiple cloud service providers (CSPs) offers greater availability and resiliency to cloud failures.
The following multicloud use cases are the most common:
-
Support multicloud split tier architecture
-
Migrate data across different public clouds
-
Running hybrid cloud environments
-
Migrating from on-premises to the cloud
On June 5, 2019, Oracle announced a cloud interoperability partnership with Microsoft that enables organizations to migrate and run mission-critical enterprise workloads across Oracle Cloud Infrastructure and Microsoft Azure.
While using multiple clouds offers many benefits, it also brings various challenges in the following areas:
-
Providing visibility across environments
-
Using consistent tooling and processes to limit complexity
-
Security
-
Ensuring consistent authentication
-
Authorization
-
Auditing and governance across CSPs
-
Connectivity
While multicloud is primarily a solution to an operational problem, there’s still an underlying need to connect and secure resources of different CSPs seamlessly. The decision about which workloads to run on which CSP has a profound impact on the effectiveness of a hybrid and multicloud strategy.
If you have a multicloud strategy and want to use Oracle Cloud Infrastructure (OCI) as one of the cloud service providers, You can use the following multicloud framework as a foundation architecture reference. OCI can mitigate risks and challenges that come with setting up a multicloud environment.

Cloud core services
OCI provides infrastructure and platform services for a wide range of enterprise workloads. In each service, you can choose from a rich array of features based on your goals. Oracle recommends a set of best practices to design and operate cloud topologies that deliver the maximum business value.
The best practices for OCI services are organized under the following business goals:
-
Security and compliance: Secure and protect your systems and information assets in the cloud.
-
Reliability and resilience: Build reliable applications by architecting resilient cloud infrastructure.
-
Performance and cost optimization: Utilize infrastructure resources efficiently and derive the best performance at the lowest cost.
-
Operational efficiency: To deliver the maximum business value, operate and monitor your applications and infrastructure resources.
Cloud physical access
One of the most crucial elements that cloud usage depends on is the ease and consistency of connectivity to cloud services. Users of the cloud need to know how to connect to the different cloud providers.
Encryption through the internet
The first type of connectivity that we look at is direct connectivity to a cloud service through the internet. Most cloud service providers use HTTP and SSL, via port 443, to enable access. In those HTTP sessions, they encapsulate different protocols, such as the Remote Desktop Protocol (RDP), mail traffic, API access, or regular website access.
Virtual private network tunnels through the internet
A virtual private network (VPN) extends a private network across the internet and other public networks and enables companies to send and receive data across those shared networks. Devices connected to a VPN are directly connected to the private network of the organisation. When we look at VPN tunnels over the internet, we can see that these tunnels have high limitations to their SLA, routing, performance, or high availability.
Private network interconnect through ethernet, MPLS, or an IPVPN provider
The primary service that all cloud providers offer is a private WAN connection through a network, possibly also including exchange providers. These private connections offer a direct connection to cloud services and cloud applications. These connections are mostly based on layer-2 Ethernet, layer-3 MPLS, or IPVPN connections to the cloud data center of the provider. When working with an enterprise-grade cloud environment, these direct connections are necessary to provide low latency and highly available network connections to cloud resources. Some examples of these services include Oracle Cloud Infrastructure FastConnect, Microsoft ExpressRoute, and AWS Direct Connect.
Many small network providers prefer connecting to a cloud provider through an exchange provider because exchange providers scale much faster than the network providers. Some examples of exchange providers include Equinix and Megaport. The following diagram shows a graphical representation of the interconnect model:

Latency and bandwidth (what matters the most)
When working in a hosted environment or with cloud providers, some factors matter more than others: latency and bandwidth. They define how many cloud services you can consume and how fast you can reach your data. Another factor is the data that’s stored and the data in transit. This information describes where your data is right now.

With connectivity, speed is equally salient. High latency can drag down an application’s performance.
Connectivity terms
Autonomous systems are collections of connected IP routing prefixes under the control of one or more network providers or operators.
The border gateway protocol (BGP) is the successor to the exterior gateway protocol. BGP is designed for routing between autonomous systems. BGP supports a metric, can make intelligent routing decisions, and can work with the internal routing protocol OSPF. Route aggregation is mostly used and supported in classless inter-domain routing (CIDR).
Private peering is the direct interconnection between two networks. This connection uses a medium OSI, layer 1 or 2, with dedicated bandwidth. No other network or third party shares private peering. Nowadays, most private interconnections are established at carrier hotels or carrier-neutral collocation facilities called meet-me rooms. These facilities provide a direct cross-connection between participants in the same building or the same data center campus. These network-to-network interconnects usually have much lower costs than telecommunication circuits.
A telco circuit is any line or provider that information or data is transmitted through.
Public peering is accomplished across an exchange point, internet exchange, or a layer 2 access technology called a network access point. At these locations, multiple providers interconnect with one or more other carriers across a single physical port. Public peering allows networks to interconnect or peer with many other networks. Public peering is often seen as offering a lower capacity than private peering because third parties charge for the internet exchange. But it allows for the connection to a larger number of networks and allows new network or content providers to send traffic to other networks without private peering.
Cloud operations
Cloud operations provide best practices regarding how to reduce challenges around providing visibility and across environments, using consistent tooling, such as Terraform, and processes to limit complexity.
Visibility and manageability
You can manage multicloud and on-premises environments with Oracle Observability and Management. As a complete, integrated, standards-based platform, it provides end-to-end machine learning-driven actionable insights. This option provides a better way to manage customers’ IT technology stacks wherever deployed, on-premises or any cloud.
Watch Oracle Executive Vice President Clay Magouyrk describe how companies, including Integra LifeSciences and Kingold, are benefitting from this technology.
Automation
-
Adopt an infrastructure as code methodology: When you adopt an infrastructure as code methodology in the CSP, you can define your entire application infrastructure in the form of code. You can perform operational procedures as code and implement them in response to events-based notifications.
Consider adopting management tools, such as Ansible modules and Chef Knife, to help you with provisioning, orchestration, and configuration management. Ansible modules enable you to automate configuring and provisioning your cloud infrastructure, deploying and updating software assets, and orchestrating your complex operational processes.
-
Build and deployment management systems: Improve efficiency by using build and deployment management systems. These systems reduce errors caused by manual processes and reduce the level of effort to deploy changes.
-
Test and validate changes: To detect errors, always track, test, and validate changes. You can use a version control system to track changes in your code. Consider using a deployment management system to automate your testing process.
Cloud security and governance
All cloud models are susceptible to threats. Cloud security involves the procedures and technology that secure cloud environments against both external and insider cybersecurity threats. Organizations need complete confidence in their cloud security and that all data, systems, and applications across CSPs are protected from data leakage, theft, corruption, and deletion. Consider the following needs for securing multicloud environments:
Data control
-
Data classification: Sensitive, regulated, or public. When classified, data can be stopped from entering or leaving the cloud service.
-
Data loss prevention (DLP): Protect data from unauthorized access and automatically disable access and transport of data when suspicious activity is detected.
-
Manage data controls: In each CSP, such as folder permissions for specified users to editor or viewer, and removing permissions.
-
Encryption: Cloud data encryption (at rest and in transit) can be used to prevent unauthorized access to data, even if that data is exfiltrated or stolen.
Cloud secure access
-
User access control: You can use a cloud access security broker (CASB) to enforce access controls.
-
Device access control: Block access when a personal or unauthorized device tries to access cloud data.
-
Privileged access: Allow access to your data and applications only to privileged accounts and implement controls to mitigate exposure.
-
Identify malicious behavior: Detect compromised accounts and insider threats with user behavior analytics (UBA) so that malicious data exfiltration doesn’t occur.
Compliance
-
Risk assessment: Identify and address risk factors introduced by cloud environments and providers.
-
Compliance assessments: Review and update compliance assessments for PCI, HIPAA, and other application regulatory requirements.
Identity federation
-
Identity federation is a mechanism to delegate user management to an identity provider or IdP. Companies with an existing identity system that they want to use can implement federation instead of creating and maintaining a new set of users. Federation requires a one-time configuration between the relying party and the IdP, known as a federation trust.
Conclusion
This article covers a multicloud framework that you can use as a foundation architecture reference. This method offers many benefits for organizations that have a hybrid or a multicloud strategy, use Oracle Cloud Infrastructure as their main CSP, and want to mitigate risks and reduce challenges that occur when setting up and managing hybrid multicloud environments.
Thank you for your interest in reading.
