We’re pleased to announce the General Availability of the JSON Web Token (JWT) Validator in Oracle Cloud Infrastructure API Gateway!
Use Case
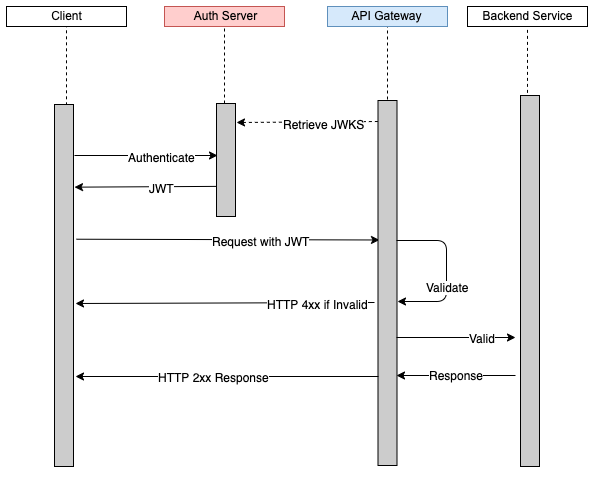
When you protect APIs with OAuth 2.0, JSON Web Tokens (JWT) provide a way for the client to send a signed token to the resource server. The resource server can validate the token by using a signing certificate from the authorization server. Using a JWT increases performance by performing the validation at the resource server instead of calling back to the authorization server for validation.
The following diagram shows the validation flow using JWT.
Benefits of This Feature
Oracle Cloud Infrastructure API Gateway was released with a “custom authorizer” capability that uses the power of Oracle Functions. Using the custom authorizer, the API developer can write a function to perform the authentication or authorization of the API requests. This feature provides great flexibility in supporting multiple methods such as Basic Auth, OAuth 2.0, and API Keys. The trade-off is that it requires a bit of code to write the function. Some of our customers asked that we provide the capability to support JSON Web Token validation through configuration rather than code.
This new policy allows members such as the security architect to define the configuration of the authorization server to easily allow JWT validation.
Using this policy, the API development team can include their configurations in their Terraform environment to deploy security policies to their APIs in a repeatable way without maintaining authorization functions. With this policy, customers can choose either a code approach or a configuration approach to securing their APIs!
Learn More
See the documentation for Using JSON Web Tokens to Add Authentication and Authorization to API Deployments.
