Oracle Cloud Infrastructure is proud to announce the general availability of Speedle, an open source policy management and enforcement solution developed by Oracle. This general-purpose policy engine enables unified, context-aware policy enforcement across applications. Speedle dramatically simplifies the configuration, management, and enforcement of security and authorization policies within cloud native environments.
The Current State
Many companies are modernizing their existing applications to become more agile and innovate faster. Microservices-based architecture enables teams to independently test services and continuously deliver changes to applications. The number of applications developed and used within an enterprise is continuing to grow rapidly.
Cloud native and DevSecOps are about reducing variability and human-error, increasing repeatability, and implementing practices underpinned by policies to deliver applications and features reliably and efficiently. To truly operate at cloud scale, policy-based automation is a key requirement. Administrators and developers spend many hours authoring security policies within each application, and this is a repetitive effort for every application developed within the organization. Managing and maintaining these application-specific policies is another key concern.
Existing access control and authorization solutions have the following shortcomings:
- They offer only basic authorization capabilities. They require manual intervention every time a policy must be configured, they are limited to roles, and in certain cases, they create maintenance challenges.
- They don’t handle heterogeneous environment scenarios well.
- They are designed for traditional environments and don’t handle cloud native environments effectively.
Benefits of Speedle
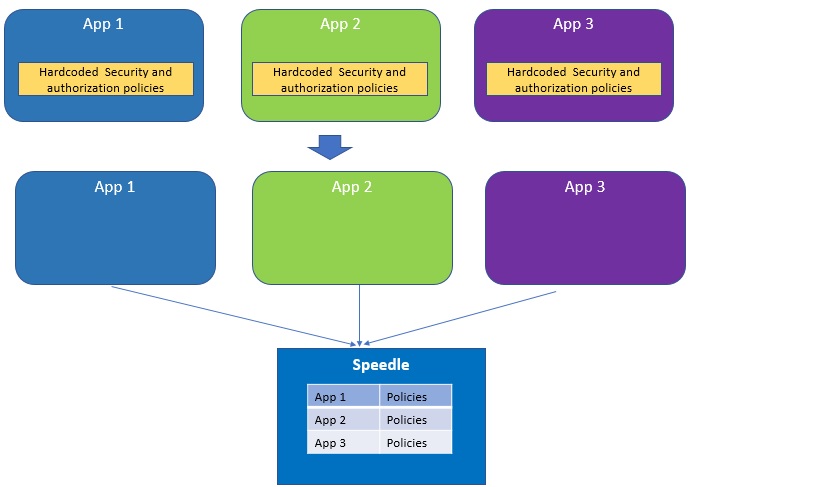
Speedle solves these shortcomings by providing powerful and dynamic access control capabilities that are decoupled from the application. It offers several capabilities to handle complex policies, such as who can access what under what conditions. It provides these capabilities in a centralized and domain-agnostic way, managing and maintaining policies across several applications. These policies can be created and evaluated as needed, reducing costs and saving time.
In a setting with one or more cloud native applications, application developers no longer need to hardcode policies within the application. Speedle provides a high-level declarative language for authoring policies and simple APIs to answer policy queries. Speedle is licensed under the Universal Permissive License (UPL) version 1.0, so you can integrate Speedle with your own systems.
Using Speedle, developers can offload policy decisions such as the following ones from the core service or application:
- Should API calls be allowed?
- Should access be restricted to certain application resources and operations?
- Is service A allowed to invoke or use service B?
- Is a particular user allowed to view or click a button on a web page?
- Which hosts can these containers be deployed on?
Before Speedle, the policy effort for each application included:
- Policy grammar
- Policy compiler
- Security
- Interactive queries
With Speedle, the policy effort for each application is simply integration with Speedle.
Speedle: Before and After
Speedle has the following components:
- SPDL policy definition language
- Policy management service
- Authorization decision service
- Command line tool (spctl)
Use Case: Implementing Admission Control Policies in Kubernetes
Implementing admission control policies in Kubernetes is a key use case of Speedle. Here is one policy example: prevent images with known vulnerabilities from getting deployed onto Kubernetes. Speedle can intercept requests to the Kubernetes API server before the relative objects, providing intent for the desired cluster state, and can be persisted to the etcd key/value object store.
Additional sample use cases:
- Evaluate the JSON payload of many API server events. Multiple policies can be used to evaluate the same API event.
- Use policies to apply rules-based control of resources, which is a dynamic approach to managing Kubernetes configuration.
- Evaluate API server event payloads to ensure that new and reconfigured objects are properly labeled. This ensures that no workloads are introduced into the cluster without the correct labeling scheme (governance and compliance within a cluster).
- Given its domain-agnostic nature, deploy Speedle into a Kubernetes cluster to provide services to other workloads that need data validation, beyond the use case of validating Kubernetes resources.
Call to Action
I encourage all of you to try Speedle. Please let us know if you have questions or comments. There are also opportunities to further contribute and enhance Speedle. Please feel free to reach me at ram.kailasanathan@oracle.com.
Here are some key links to project Speedle:
