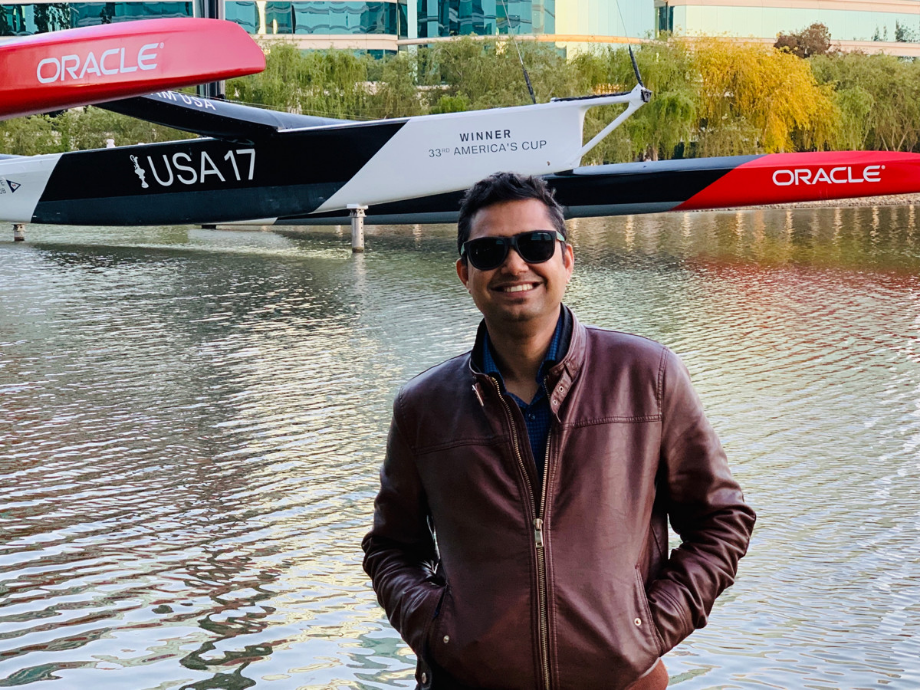
This blog post is co-written by Vinay Rao and Samir Shah.
As the multicloud story unfolds, enterprises want to build applications that span infrastructures and cloud providers. Oracle and Microsoft recently announced a cloud partnership that enables cross-cloud networking, unified identity and access management, and a collaborative and integrated support model across Microsoft Azure and Oracle Cloud Infrastructure. The cross-cloud networking is a secure, dedicated link that provides high bandwidth and low latency between the two cloud providers. Customers don’t have to work with third-party network providers to set up the cross-cloud connectivity.
The power of cross-cloud connectivity enables many use cases, including:
- Web application on Azure, Autonomous Database on Oracle
- Java and Oracle apps on Oracle, .NET/SQL Server applications on Azure
- Data mining in Autonomous Database from Azure
- App-to-app interoperability across the clouds
- High availability across multiple cloud vendors
Jamal Arif recently published a blog post that walks users through the simplicity of creating an end-to-end cloud interconnect between Microsoft Azure and Oracle Cloud Infrastructure. As a continuation to the series, in this post, we (Samir Shah and Vinay Rao) walk you through the process of building a simple two-tier, multicloud application that helps enterprises envision applications that leverage the best services from both these cloud providers.
Before we start building the application, let’s take a quick glance at the architecture. In the following diagram, the app tier resides on a Azure compute instance and the database tier is the Oracle Autonomous Database offering. The app tier writes and queries data to and from the database tier over a secure private connection by using transit routing.

Prerequisites
Before you start deploying your application, follow the steps in the How to set up the interconnect between Oracle Cloud Infrastructure and Microsoft Azure post.
Step 1: Set Up the Autonomous Database on Oracle
-
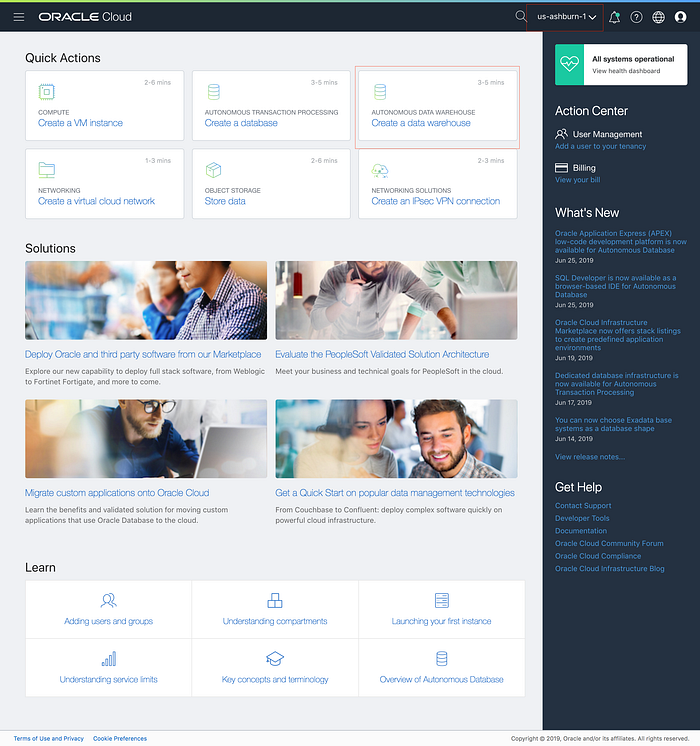
Sign in to the Oracle Cloud Infrastructure Console and select the us-ashburn-1 region.
-
In the Quick Actions menu, click Create a data warehouse to create an Autonomous Data Warehouse instance.
-
Follow the wizard to set up all the required parameters for your Autonomous Data Warehouse instance, and then click Create Autonomous Database.

It takes 3–5 minutes for the database to be provisioned.
-
Download the wallet file (client credentials).
-
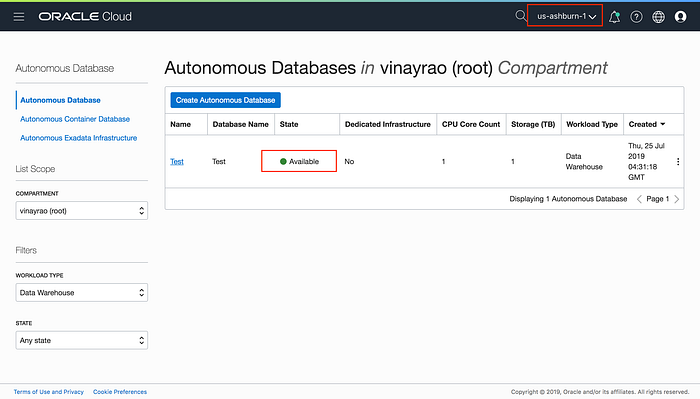
From the Autonomous Database page, click the actions icon (three dots) next to the database and select Service Console.
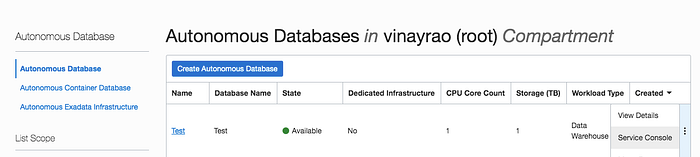
-
Navigate to the Administration section and download the wallet file.

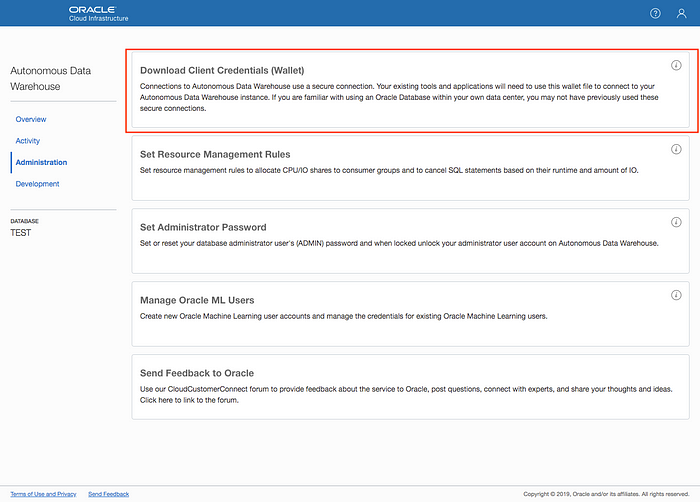
We’ll use the wallet file in a later step.
-
Step 2: Set up the Application Tier on Azure
-
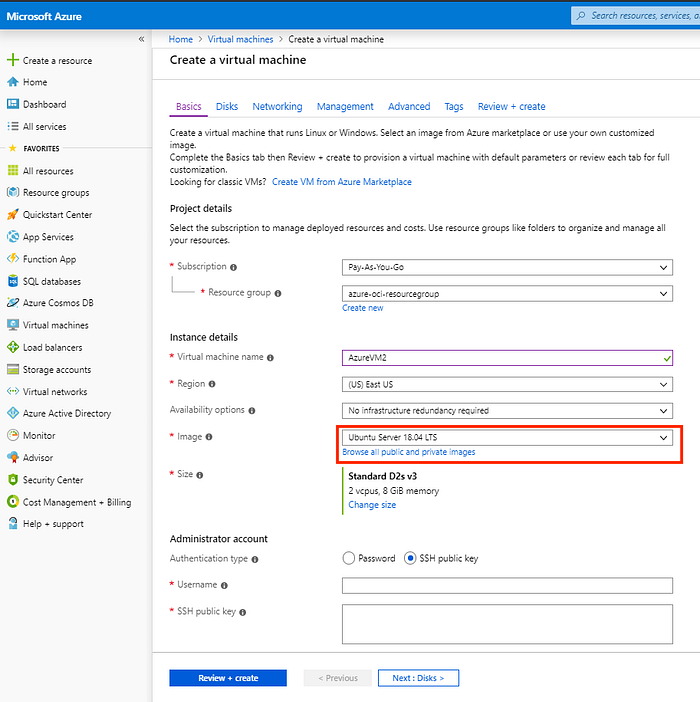
Log in to the Azure portal.
-
Create an Ubuntu virtual machine (VM) in the network that you created when following the prerequisite steps.
-
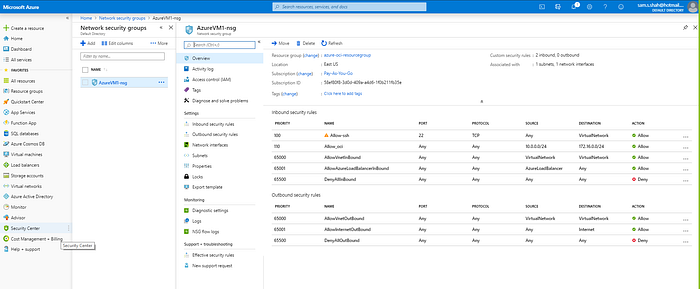
Configure the network security groups to allow the required database port and other connections.
-
After the VM is up and running, use SSH to connect to the VM and ensure that the connectivity is working.
Step 3: Set Up Private Peering Routes to Oracle Services
If you followed the prerequisite steps and have a private peering link set up between Oracle Cloud Infrastructure and Microsoft Azure, the VMs in the two infrastructures can now reach each other securely.
To access the database over the secure private connection, we’ll leverage the recently announced transit routing feature. To enable this feature, create a service gateway by using the instructions in the Access Oracle Services Privately with a Service Gateway blog post.
-
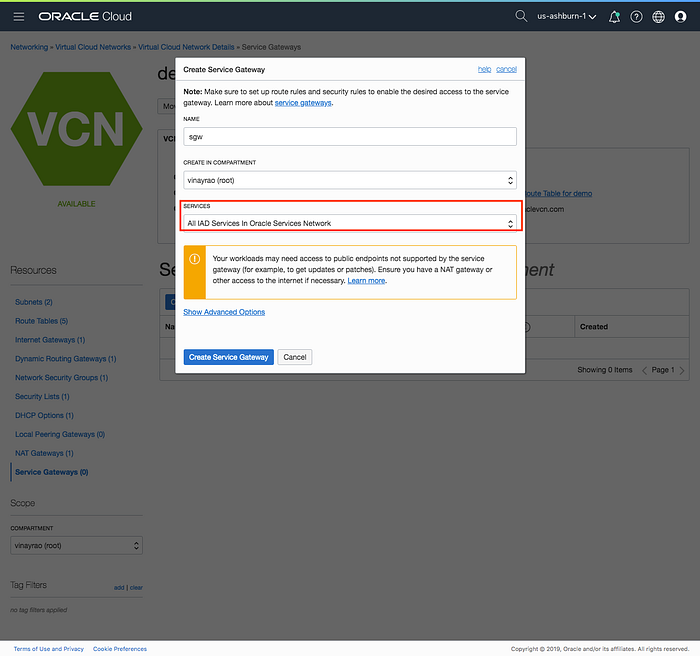
In the Oracle Cloud Infrastructure Console, navigate to Networking > Virtual Cloud Network, and select the VCN.
-
Under Resources, click Service Gateways, and create a service gateway.

-
Create a service gateway to reach All IAD Services in Oracle Services Network.
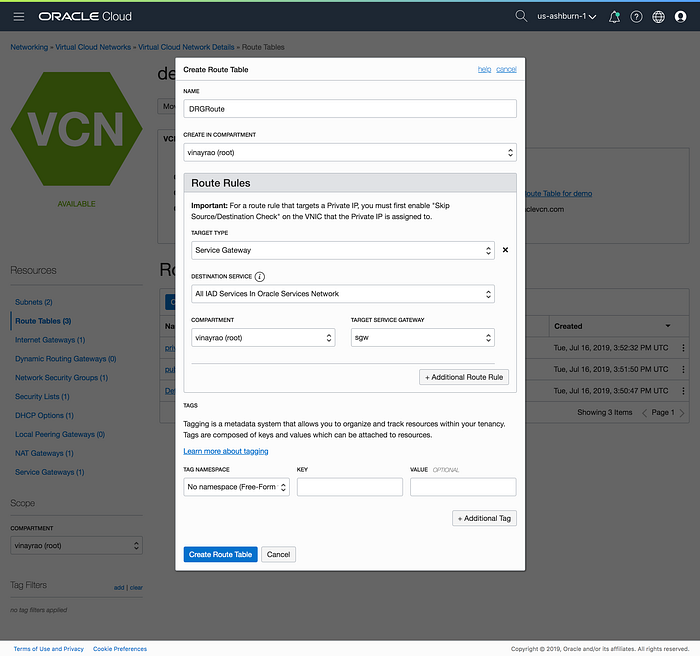
After the service gateway is created, create two route tables: a DRG route table and an SGW route table.
-
Create a DRG route table.
-
Under Resources, click Route Tables, and create a new route table.
-
Specify the target type as Service Gateway and the destination service as All IAD Services in Oracle Services Network.
-
-
Associate this route table with the DRG to ensure that all Oracle services routes are advertised by the DRG.
-
Under Resources, click Dynamic Routing Gateways.
-
Click the DRG attached to the VCN with the route table.
-
Click the actions icon (three dots), and then click Associate With Route Table.
-
Select the route table and click Associate.
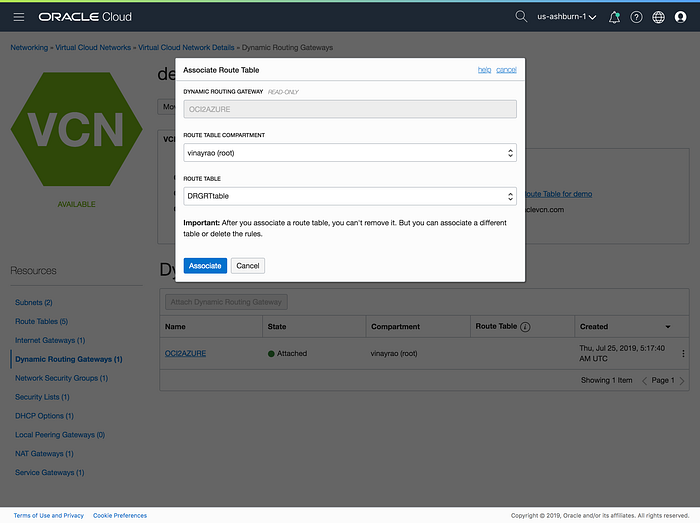
Now that the route table is associated with the DRG, the DRG will advertise the Oracle Services Network routes over the Azure Express route, and these routes are visible on the VM’s route table.
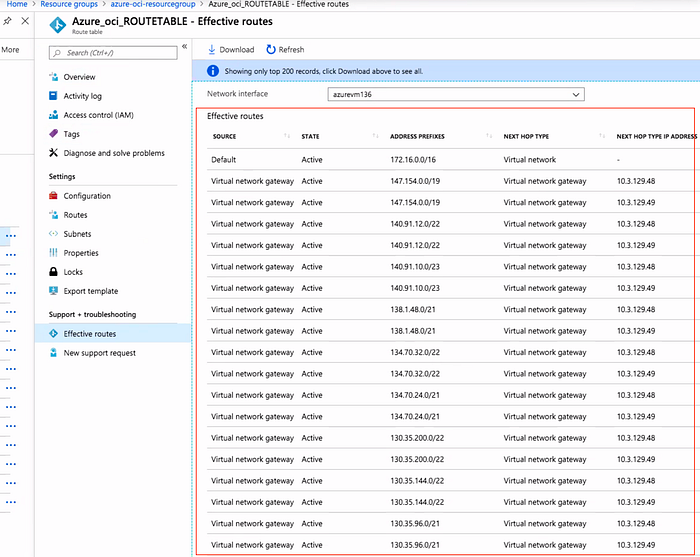
-
-
To ensure that the traffic from the Oracle Services Network can reach the remote Azure application, create an SGW route table. Specify the target type as Dynamic Routing Gateway and the destination CIDR block as the address of the Azure Express route.
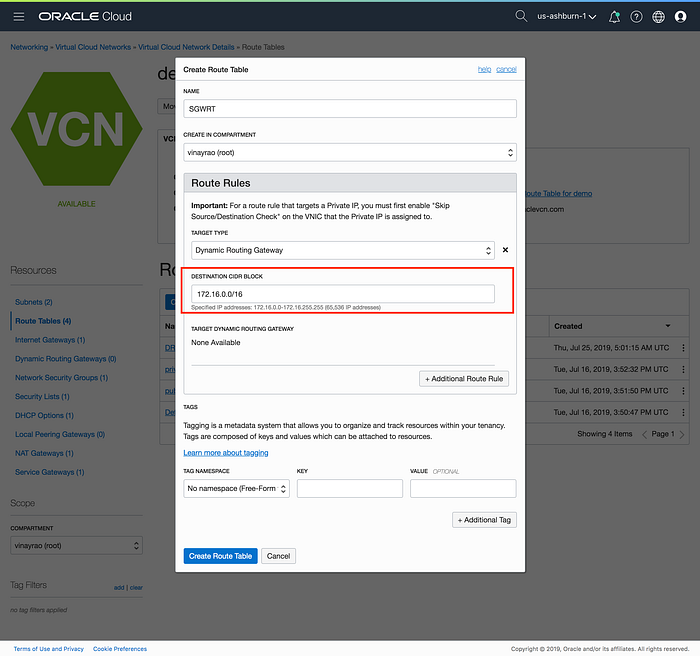
-
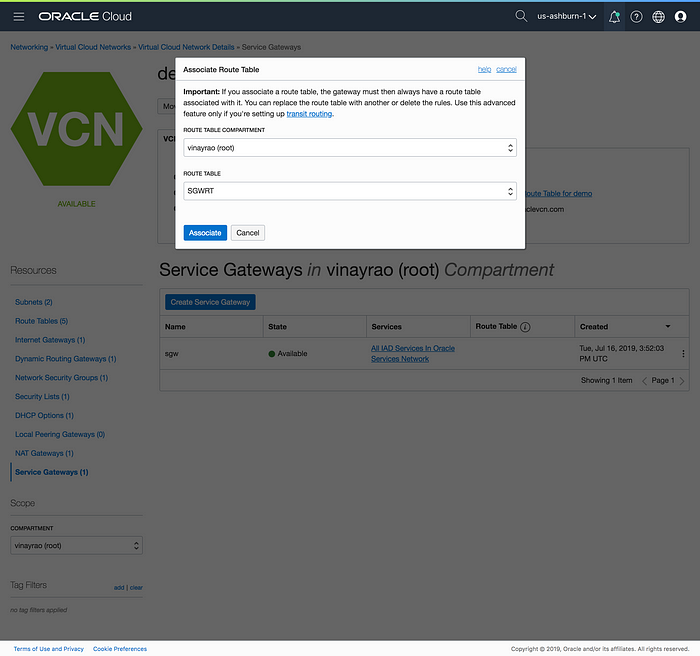
Associate the SGW route table with the service gateway.
-
Under Resources, click Service Gateways.
-
Click the actions icon (three dots) next to the service gateway, and then click Associate With Route Table.
-
Select the route table, and then click Associate.
-
Step 4: Install the Application
Now that the connectivity has been set up, let’s install the application that will mine data from the database.
-
Install the Oracle instance client in the Azure VM.
-
Upload the wallet file that you downloaded in Step 1, unzip the folder, and use the files to access the data in the Autonomous Data Warehouse database.
-
Clone the application code from this repo.
-
Run the application.
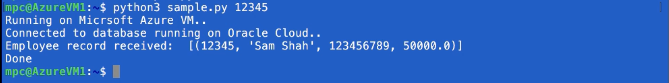
That’s it! The simple Python app residing in Azure VNET can privately and securely mine data from the Autonomous Data Warehouse database.
Conclusion
We hope you enjoyed reading this post. The sample two-tier application is just a proof of concept to help you build your ideas and applications across Azure and Oracle Cloud Infrastructure.