We’re pleased to announce the general availability of Oracle Cloud Infrastructure Private DNS. With Private DNS, you can create private domain name system (DNS) zones in your virtual cloud network (VCN) and interconnect DNS between your on-premises and cloud networks.
Overview
Private DNS provides DNS resolution of custom DNS domains within your VCN. These domains include domains that reference internal infrastructure within your Oracle Cloud Infrastructure (OCI) tenancy or private IP addresses elsewhere on your network. You can use any domain name that you want in private DNS, and it’s resolvable only through your DNS resolver.
Private DNS also introduces support for connecting DNS resolvers across VCNs, on-premises networks, and trusted companies. Many customers will also appreciate its ability to seamlessly extend your cloud DNS infrastructure to on-premises and vice versa.
Private DNS is available at no additional cost in all cloud regions starting today.
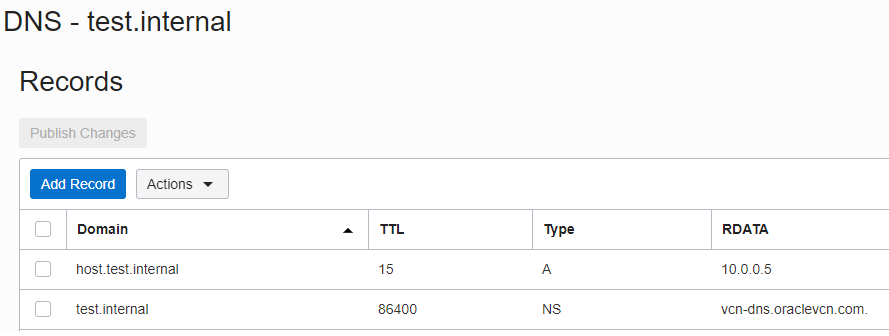
Figure 1: DNS records in private DNS
Getting started
You can get started with private DNS immediately in all regions. To learn more, see the documentation and reference architecture:
Also view our new private DNS hands-on lab, where you can get experience by using a free tier account.
Use cases
Private DNS supports the following use cases.
Private DNS zones
You can now create private DNS zones on OCI and provide DNS resolution services to your cloud applications and services. These zones can be a custom private name of your choosing (such as ocizone.internal, shown in the following diagram) or an external domain that you optionally own through a registrar. For private DNS zones, the domain records are resolvable only by resources within your VCN.
Whether you need more domain names for your enterprise applications, DNS support for seamless cloud migration, or greater control over the domain name used for your private DNS, we have you covered.
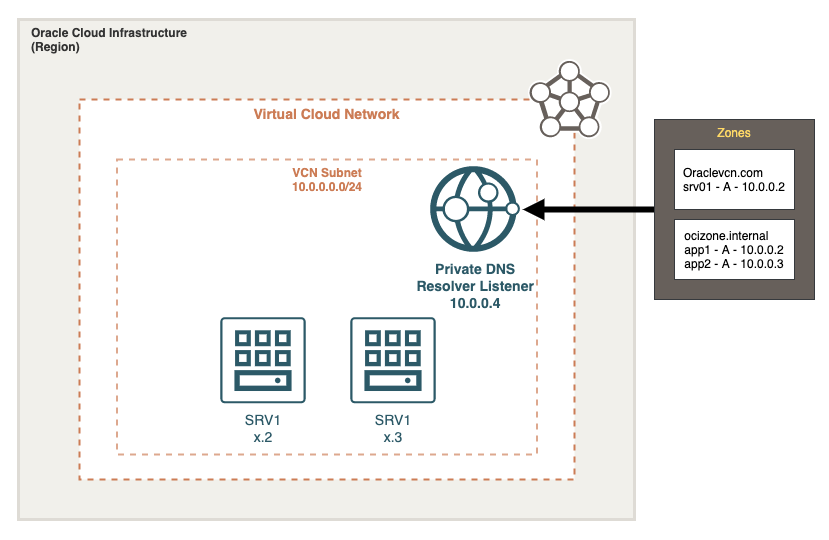
Figure 2: Private DNS zone in OCI
Seamless DNS resolution between OCI and on-premises infrastructure (hybrid DNS and conditional forwarding)
We’ve also added support for conditional forwarding, which lets you take a policy-driven approach to name resolution across multiple DNS services, both on and off OCI. With this enhancement, even if your DNS architecture is split between on-premises and OCI, you can experience seamless name resolutions as a native cloud service.
In addition to supporting on-premises hybrid DNS scenarios, you can also use this functionality to integrate DNS across multiple VCNs or OCI tenancies.
This solution is provided by exposing a new private DNS resolver listening and forwarding endpoint in your VCN, which can be reached in the same way as your compute instances. We provide a flexible forwarding policy engine that supports domain and CIDR as optional filters to a DNS forwarding endpoint:
- Domain name: Conditionally forward DNS requests based on domain names to a specific DNS server IP address.
- CIDR: Forward requests originating from specific IP addresses to a specific DNS server IP address.
- None: Forward all DNS requests to a specific DNS server IP address.
Hybrid DNS and conditional forwarding example
The following example shows a customer who has configured private DNS resolvers on their VCN. They configured the domain name onprem.internal as a filter for their private DNS resolver and pointed it to the on-premises DNS server with the IP address 10.0.1.5. When their OCI instance asks for resolution of the domain app4.onprem.internal, it achieves resolution through their on-premises DNS server.
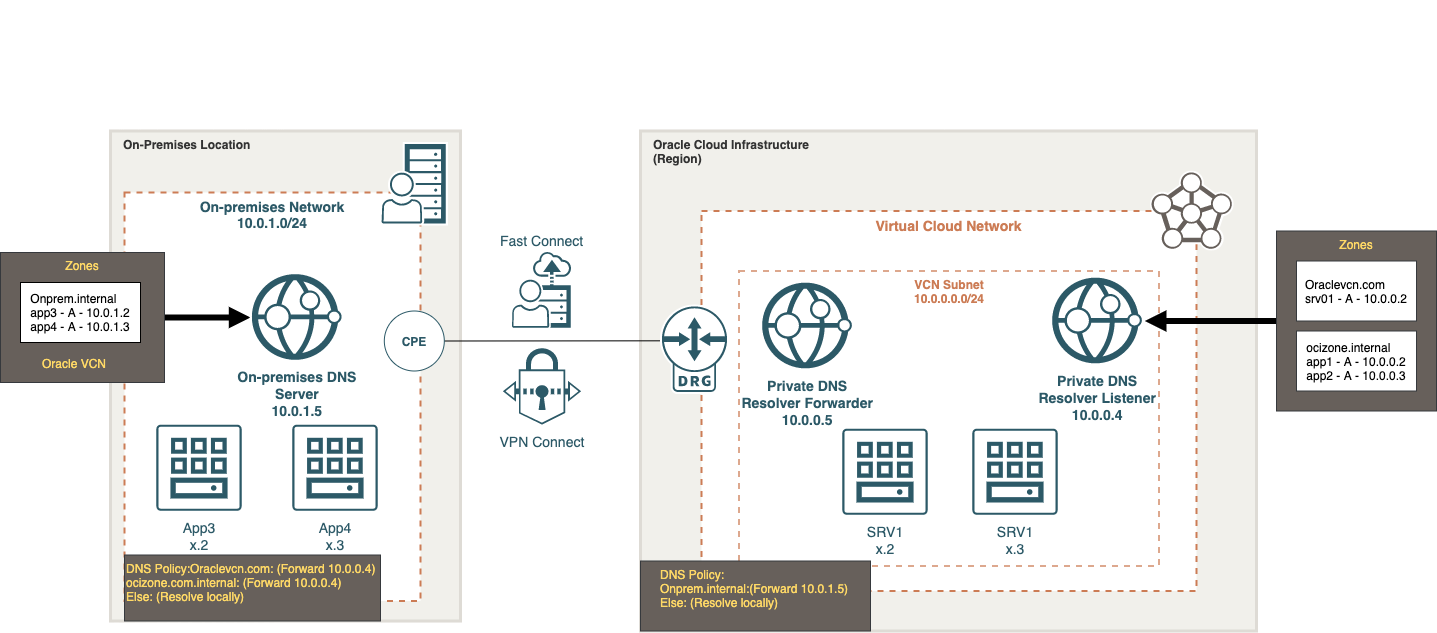
Figure 3: Example of hybrid DNS and conditional forwarding
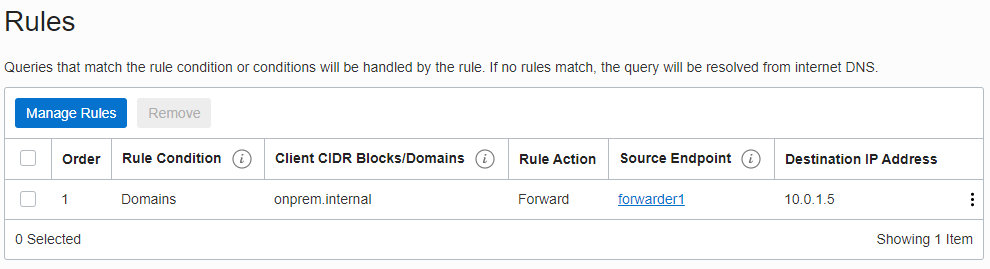
Figure 4: Conditional forwarding rule
Conclusion
Thank you for interest in Oracle Cloud Infrastructure Private DNS. On behalf of the DNS team, we encourage you to share any product feedback that you have in the comments.
