We’re pleased to announce that you can now specify custom cipher selections of Transport Layer Security (TLS) cipher suites TLS 1.0, TLS 1.1, and TLS 1.2 in Oracle Cloud Infrastructure Load Balancing service. Oracle Cloud Load Balancing service, by default, supports TLS 1.2. In some situations, this version is not enough. It’s important to understand that the Secure Sockets Layer (SSL) ciphers that are enabled depend on the type of application and the business requirements of the application.
Some organizations want to widen their TLS versions and allow different versions based on the requirements. Some applications require more control over which TLS versions and ciphers are used for their HTTPS or TLS connections to meet next generation or legacy application requirements. Oracle Cloud’s load balancer supports multiple cipher suites that allow you to enforce the connections that meet their security requirements.
This post discusses how to control the TLS policy and provides configuration details on the Oracle Cloud Infrastructure Load Balancing service for a successful deployment.
Background
TLS is a widely used protocol across the internet. Its cryptographic protocol provides authentication and data encryption between different endpoints, such as a client connecting to a load balancer.
Cipher suites include key exchange algorithms, such as RSA, DHE and ECDHE, encryption algorithms, such as 3DES, RC4 and variants of AES, and authentication algorithms, such as MD5 and SHA variants. Oracle Cloud Load Balancing service supports multiple cipher suites and allows you to use the suites that meet your security requirements. You can choose whether to allow or reject the handshake that doesn’t meet your specified cipher suites.
Solution
Various ciphers and options can be set on the load balancer. You can configure TLS versions and ciphers on the load balancer in the following ways:
-
Predefined templates: Templates already pre-defined for common TLS version and cipher configurations. Predefined protocol policy from Oracle Cloud is often the simplest policy to use.
-
Custom templates: Allow definition of custom user-defined policy and cipher settings.
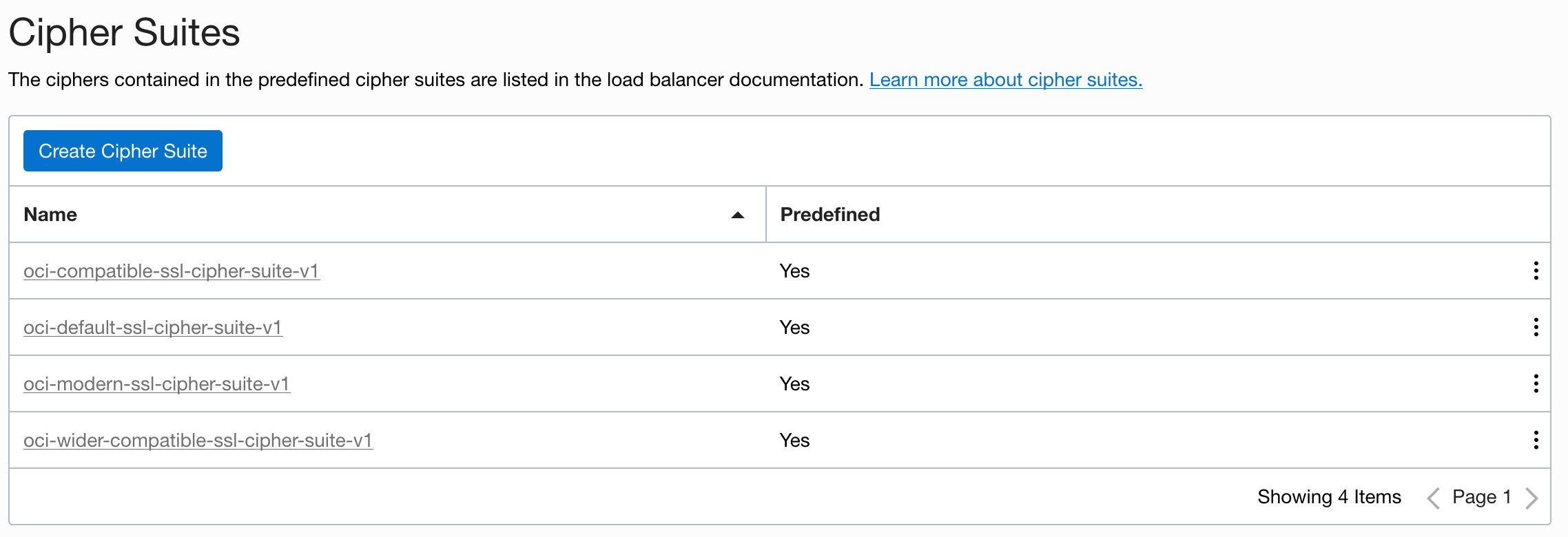
Predefined Templates
Predefined templates include the following preconfigured profiles:
-
Compatible: Allows the larger set of clients, including clients that support the broadest set of SSL features, to negotiate SSL with the load balancer.
-
Default: Supports a reduced set of SSL features, intended to meet stricter compliance requirements.
-
Modern: Supports a wide set of SSL features, allowing modern clients to negotiate SSL.
-
Wider compatible: Contains all supported ciphers.
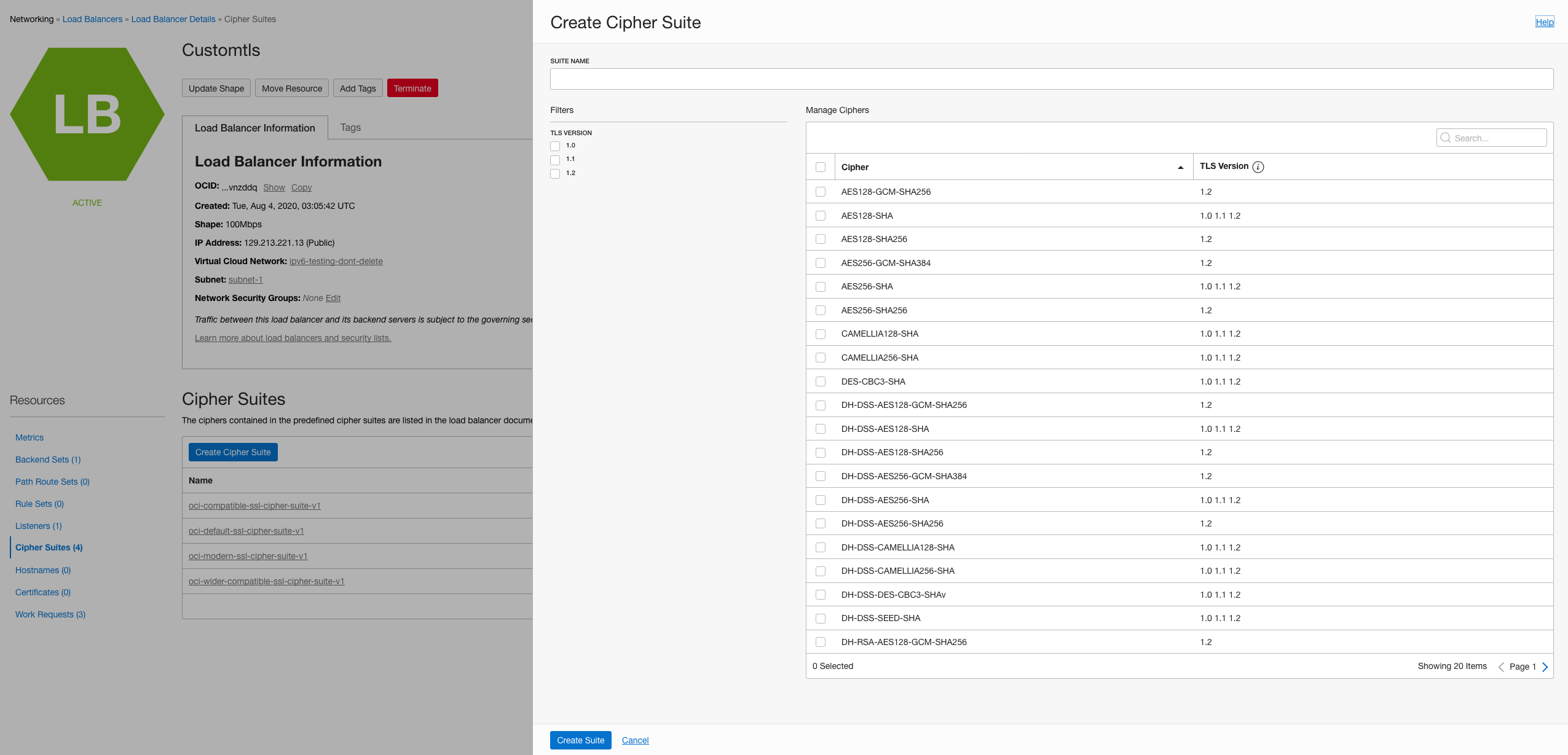
Custom Templates
If you want to specify your own cipher choices, click Create Cipher Suites. This option helps when you have to comply with an information security policy that requires enabling or disabling specific ciphers and TLS version levels. You can easily write a custom policy listing only the ciphers that are acceptable to your requirements.
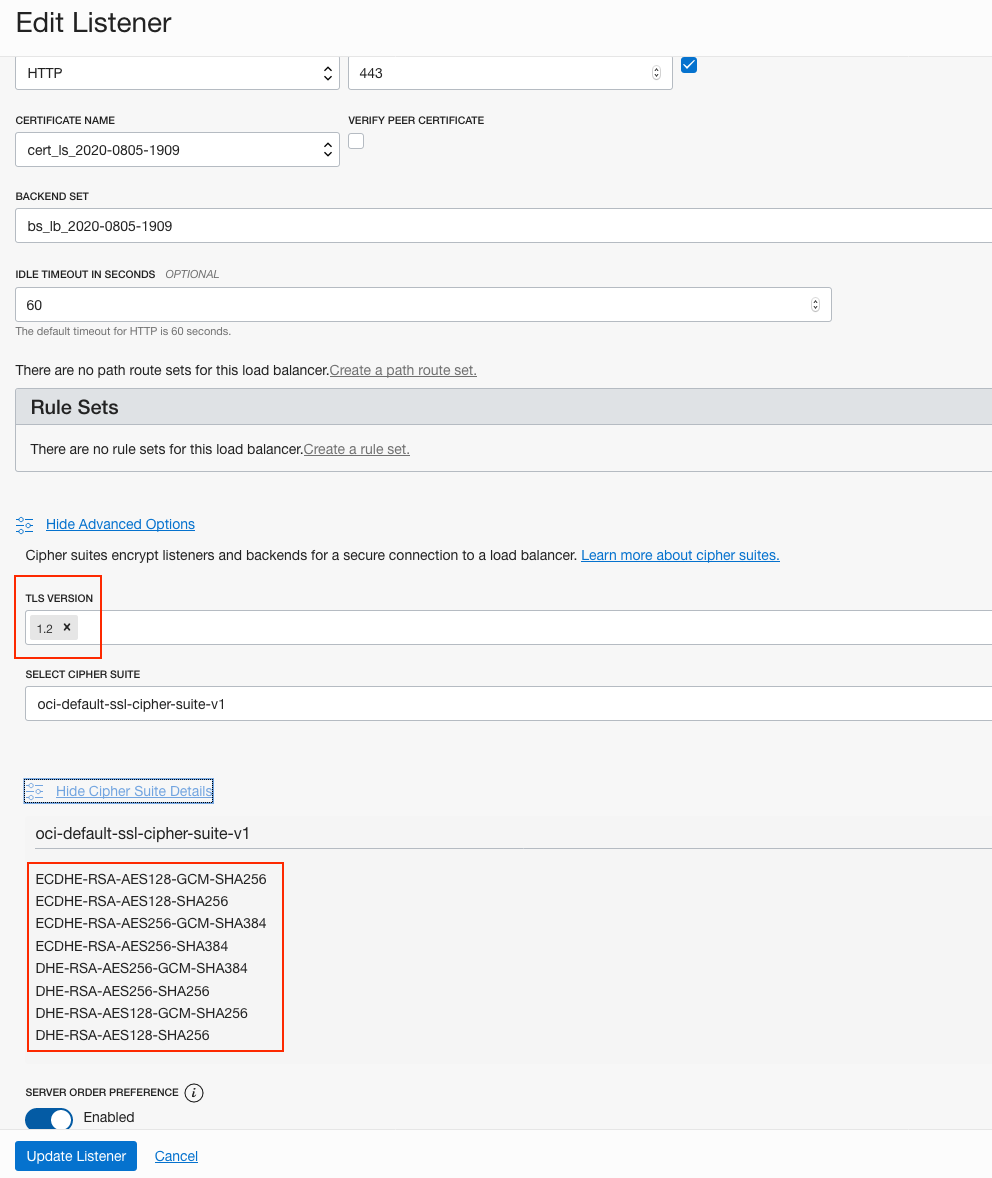
Association on the Listener
In the following example, the administrator needs to explicitly associate the TLS version and cipher suites to the listener.
Verify Custom TLS
You can check that the load balancer is using the required ciphers that we chose by entering the URL of the load balancer in the form on SSL Labs’ SSL Server Test page.
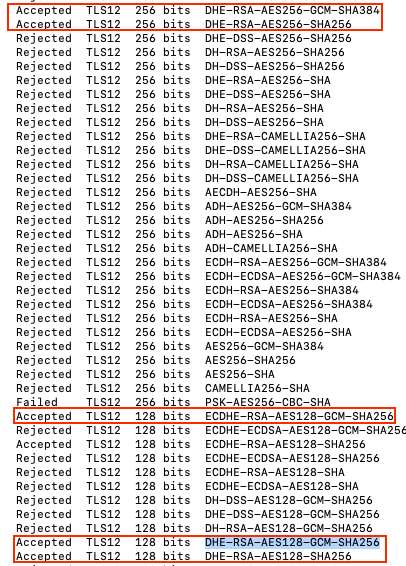
SSL Scan
If you want to test the security of your load balancer’s configuration privately, you can use an open source command line tool, such as sslscan.
The following sample output shows a small subset of the total output of the sslscan tool. You see either accepted connections, or failed or rejected connections. For more details, see the SSLscan documentation.
Conclusion
This post shows various ways to configure a custom TLS cipher with minimal configuration and easy steps. I hope that you enjoyed reading this blog to configure and test custom versions of TLS on Oracle Cloud Infrastructure Load Balancing service. Now, when you design your website on Oracle Cloud Infrastructure, you can use this feature to let you smartly select TLS cipher suites. To learn more about the load balancer feature, see Managing Cipher Suites.
