Original Publish Date : 7/5/2019
Service Provider Configuration at JCS :
Last updated: 16-Aug-2022
Click on the following hyperlink to download the sample application :
JCS_SSO_Test_application.zip (Unzip this file and deploy)
NOTE: Please modify the <principal-name> tag in weblogic.xml file (of this application) with your group name OR username.
Example:
.
.
<security-role-assignment>
<role-name>SamlTrainee</role-name>
<principal-name>puneeth</principal-name> ===> Username
<principal-name>Administrators</principal-name> ===> Group Name
<principal-name>abc@xyz.com</principal-name> ===> emailID
</security-role-assignment>
.
.
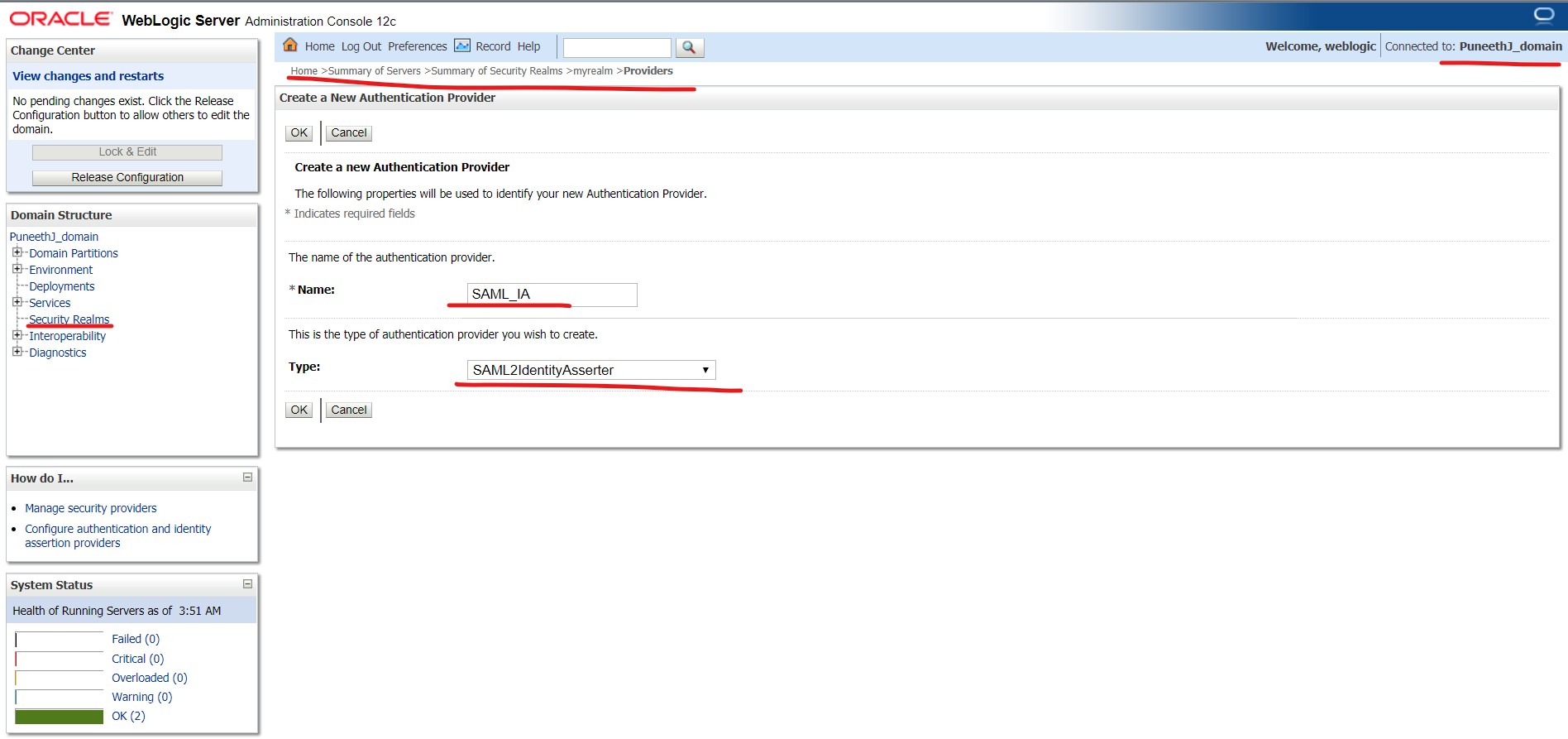
Step 1a :
Since JCS is the Service Provider (which accepts a token), we need to create a SAML Identity Asserter provider from the console :
Login to console -> Security Realms -> myrealm -> Providers -> Authentication -> new :
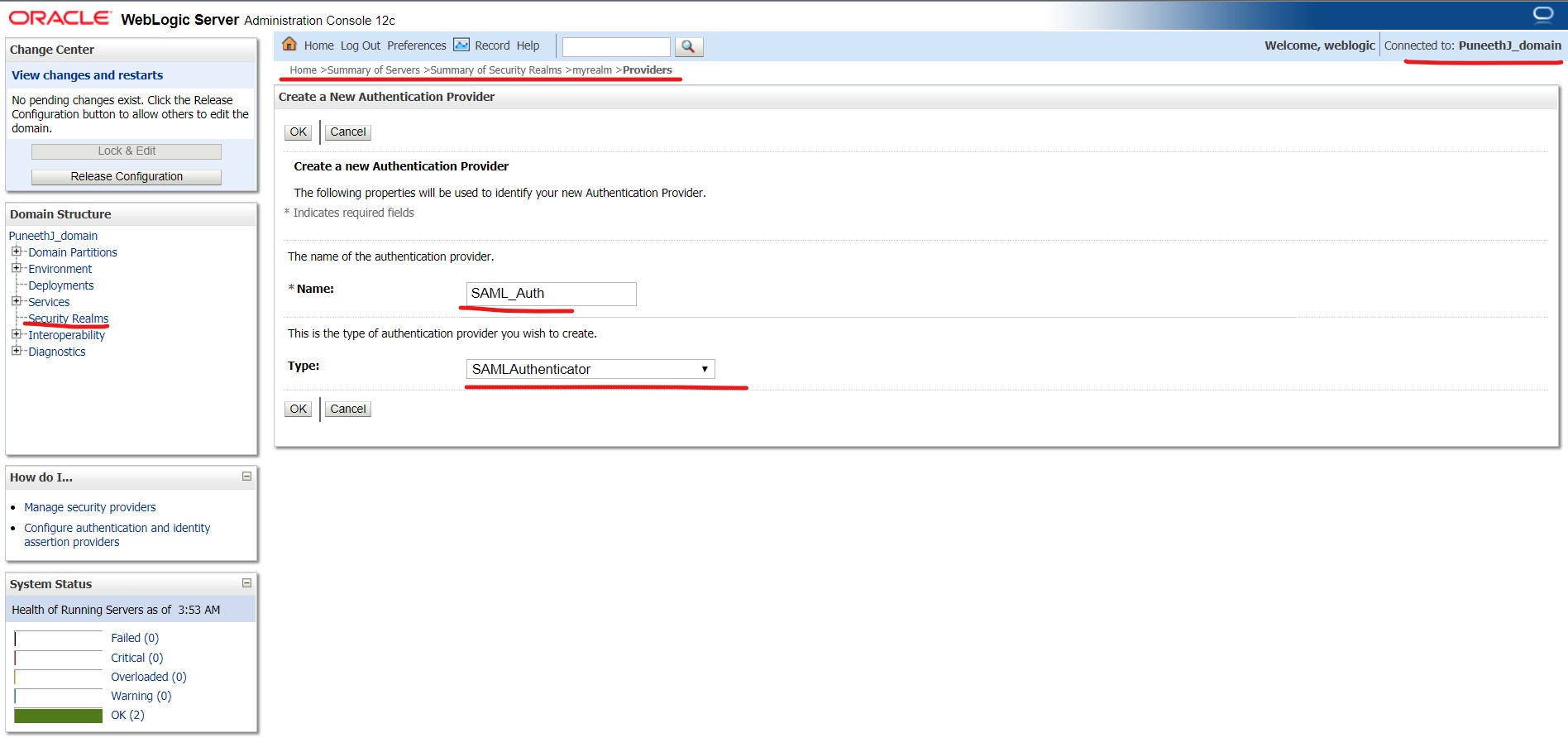
In this scenario, all the users will be present in IDCS and not in JCS, so we need to create a SAML Authenticator to enable a virtual user (a user that does not correspond to any locally-known user) to log in via SAML.
Have a look at the following doc for more info on the same :
Link: https://docs.oracle.com/middleware/12213/wls/SECMG/saml_atn.htm#SECMG205
Login to console -> Security Realms -> myrealm -> Providers -> Authentication -> new :
Now that we have multiple Authentication Providers configured in Weblogic(DefaultAuthenticator and SAML Authenticator), we need to set the Control Flags to either “OPTIONAL” or “SUFFICIENT” for both the providers.
Change the Control Flag to OPTIONAL for the DefaultAuthenticator
Login to console -> Security Realms -> myrealm -> Providers -> DefaultAuthenticator -> Control flag
Now restart all the servers in this domain.
Step 2a :
Select the server where SSO application will be deployed and navigate to “Federation Services” as shown below :
Login to console -> +Environment -> Servers -> <server_where_SSO_application_will_be_deployed> -> Federation Services -> SAML 2.0 General :
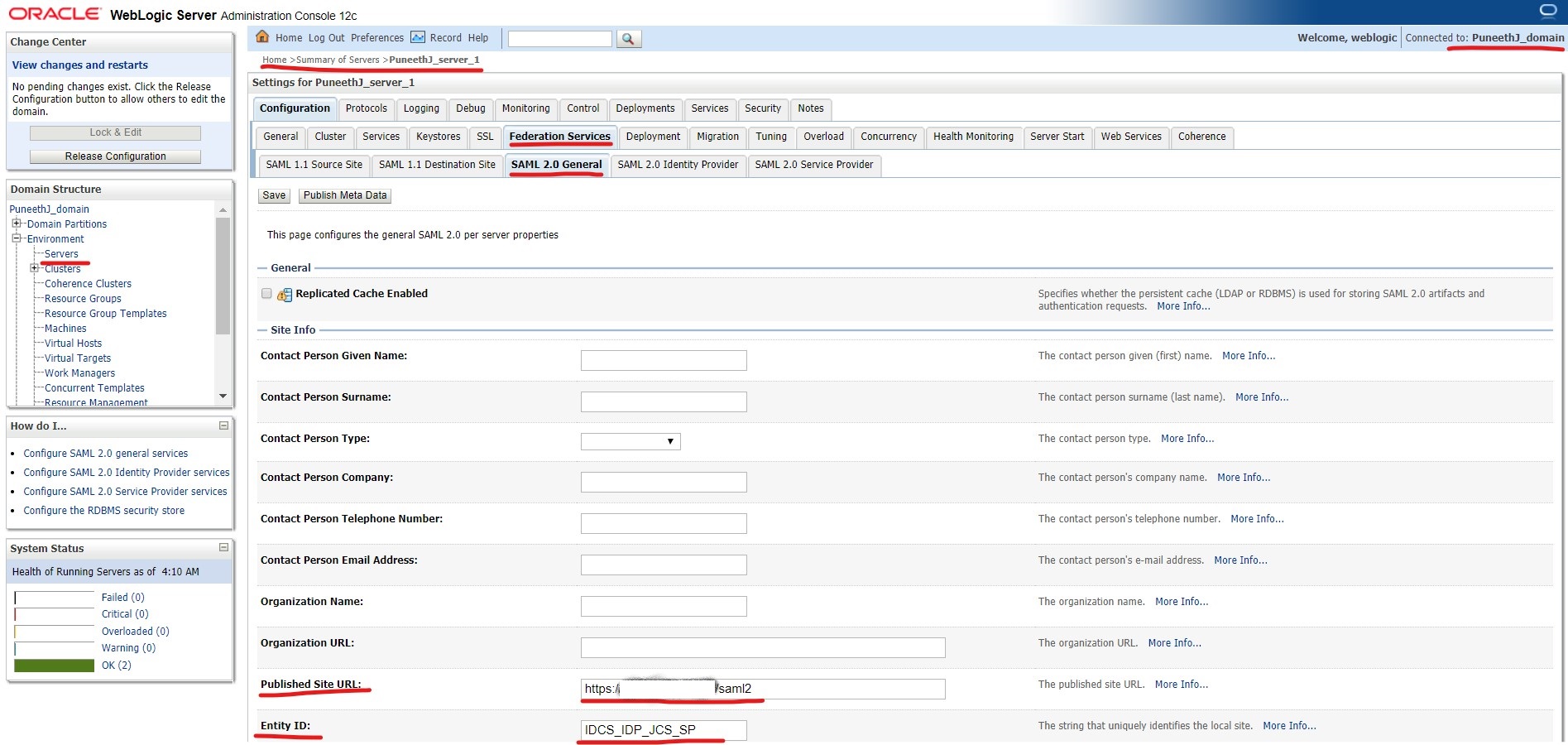
Two most important fields here are :
– Published Site URL : <protocol>://<public_host>:<public_port>/saml2
// This URL should always contain an external host:port.
// Protocol can be http or https.
// URL should always contain “/saml2” at the end. (This is an internal application deployed in WLS and cannot be changed).
– Entity ID : <Any_name> (This is a Unique identifier)
Other fields are optional and can be left blank.
Step 3a :
Navigate to SAML 2.0 Service Provider tab :
Login to console -> +Environment -> Servers -> <server_where_SSO_application_will_be_deployed> -> Federation Services -> SAML 2.0 Service Provider :
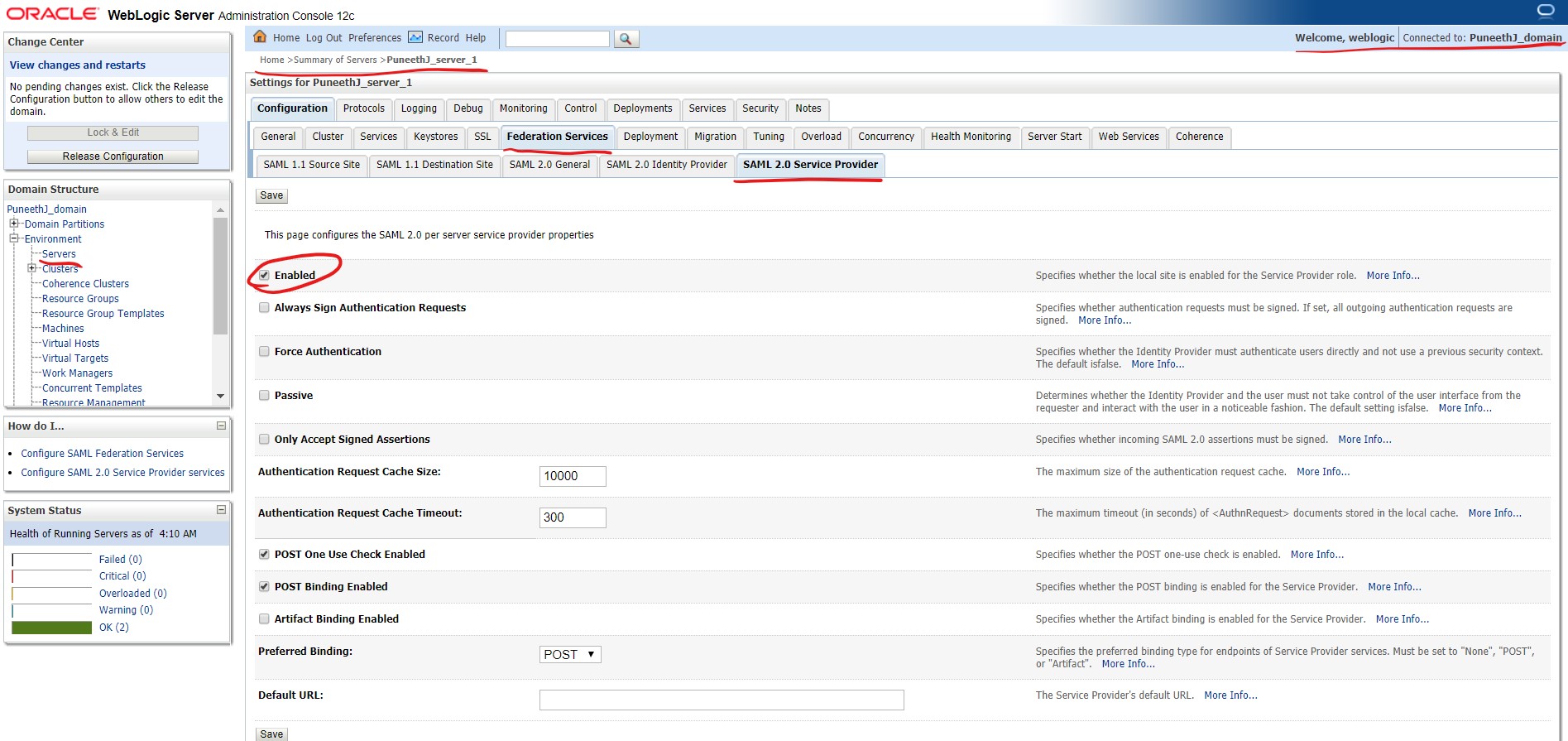
Make sure that “Enabled” checkbox is checked.
Identity Provider Configuration at IDCS :
Step 1b :
Open the Identity Console from your cloud Dashboard -> User Management page
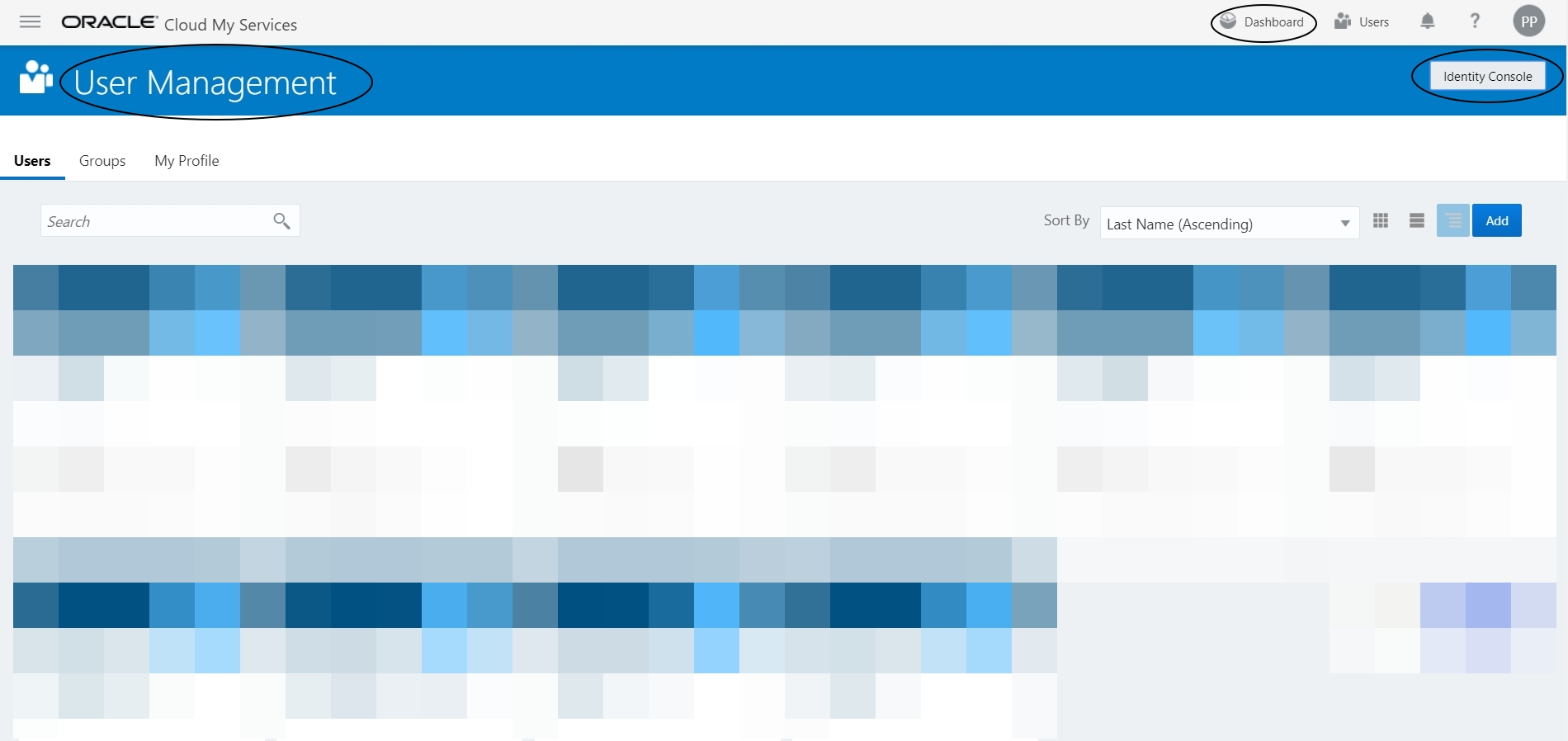
We need to create a new SAML application in IDCS :
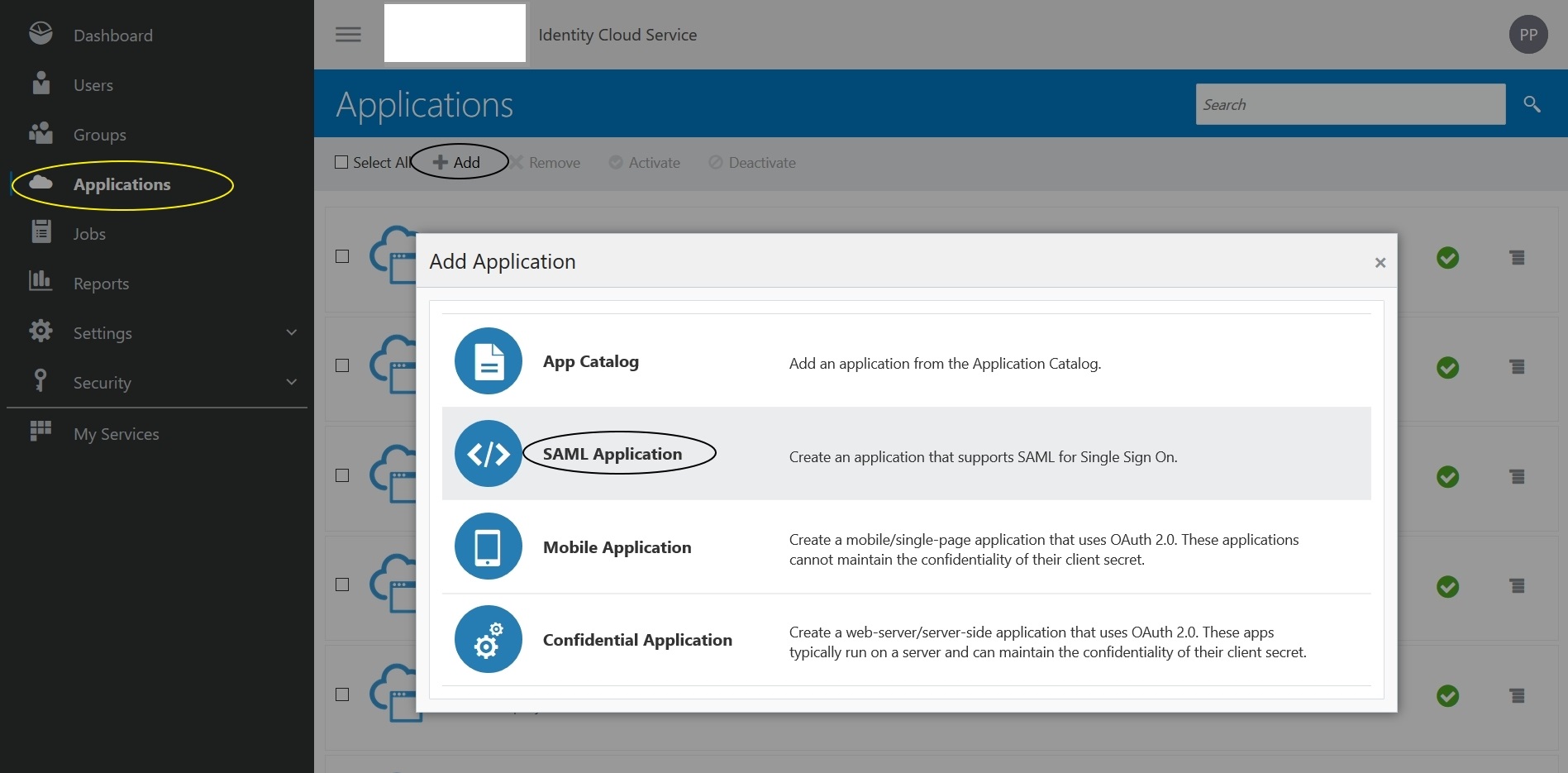
Step 2b :
Name : IDCS_IDP_JCS_SP (can be any name)
Application URL/Relay State : https://<publicly_accessible_hostname/IP>:<port>/JCS_SSO_Test_application
// This can be your application URL deployed in JCS.
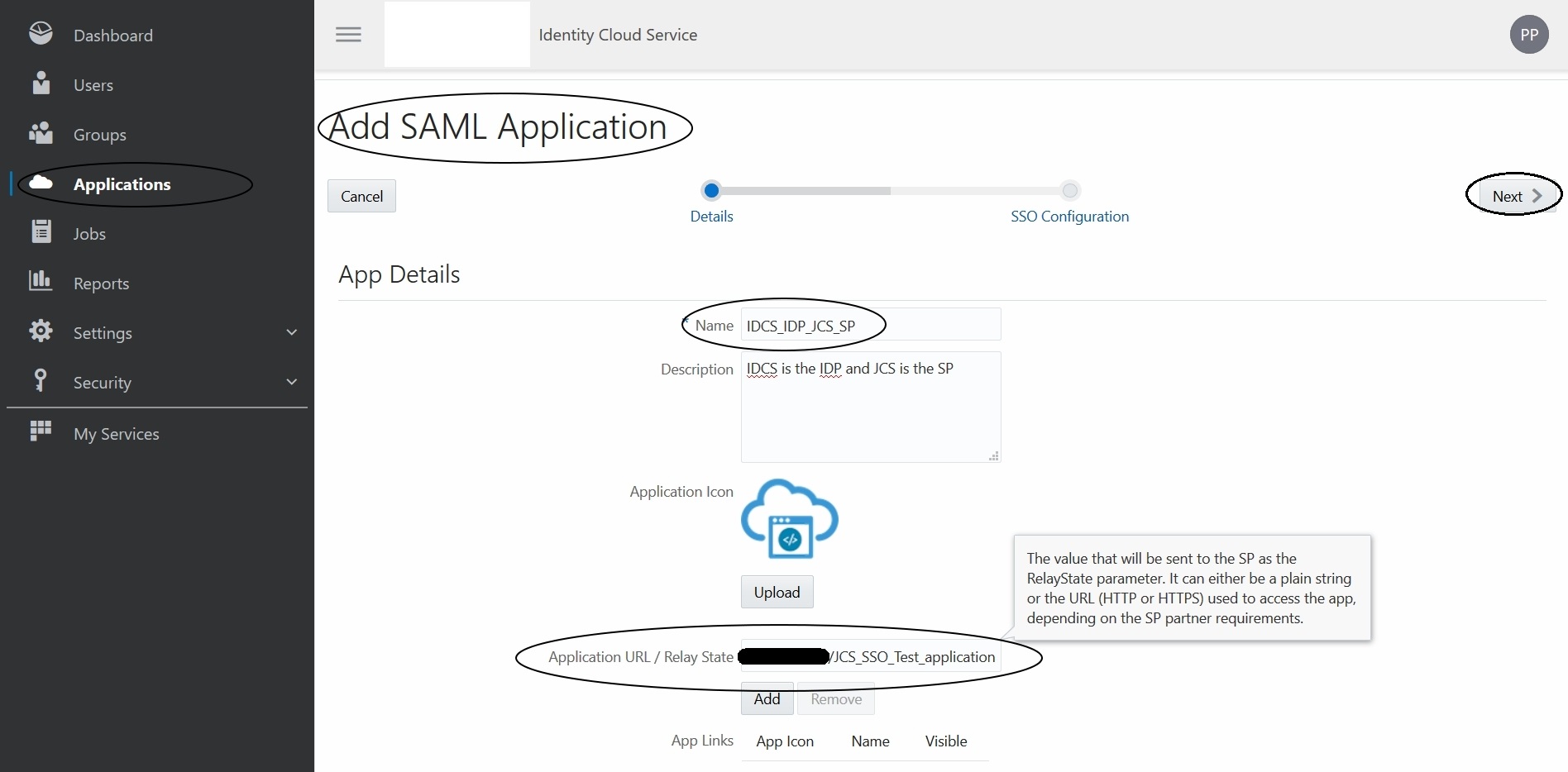
Click Next and update the following info
+General
Entity ID: IDCS_IDP_JCS_SP
// Entity ID specified here should be the same as the one provided in Step 2a in JCS WLS console.
Assertion Consumer URL: https://<publicly_accessible_hostname/IP>:<port>/saml2/sp/acs/post
// NOTE – this URL should always contain “/saml2/sp/acs/post”
NameID Format: Unspecified
// In this example I am using Format as Unspecified.
NameID Value: Primary Email
// In this example, I am using email ID, but you can select any value from the drop-down.
+Advanced Settings
Enable Single Logout (Uncheck)
// In this example, I am not using a single Logout URL
+Attribute Configuration
Name: Groups
Format: Basic
Type: User Attribute
Value: Group Membership
Condition: All Groups
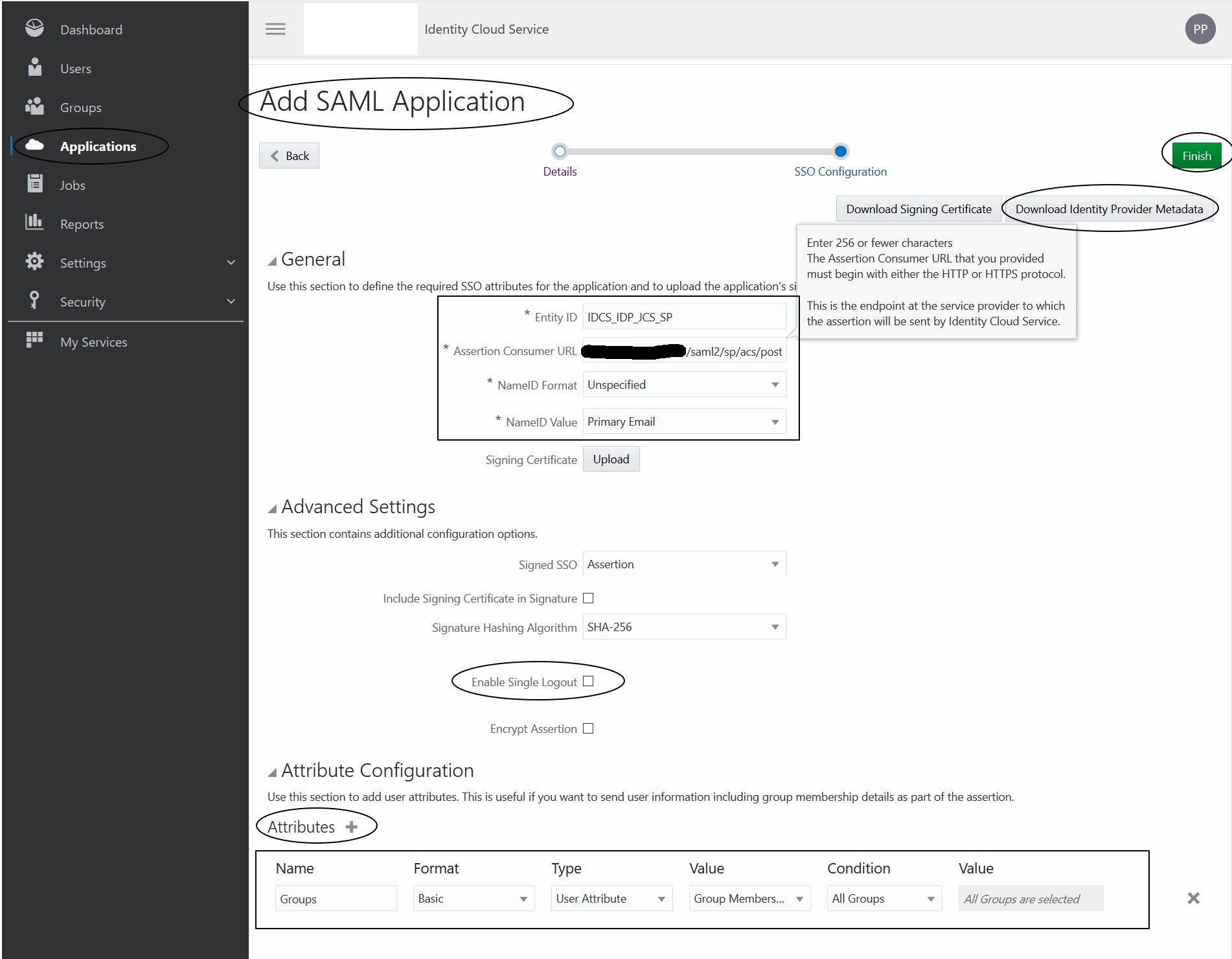
Download the IDP metadata -> Click on “Download Identity Provider Metadata” button on the right top of the screen.
We will use this to create an IDP partner in JCS WLS console.
Then click Finish.
Copy the IDP metadata downloaded from IDCS console to JCS.
Step 3b :
Search for the application you created by selecting the “Applications” option and activate your application.
Then assign any user to this application.
If you don’t have any users/groups then you can create it by selecting the “Users” or “Groups” option in the menu and then you can assign them to your application.
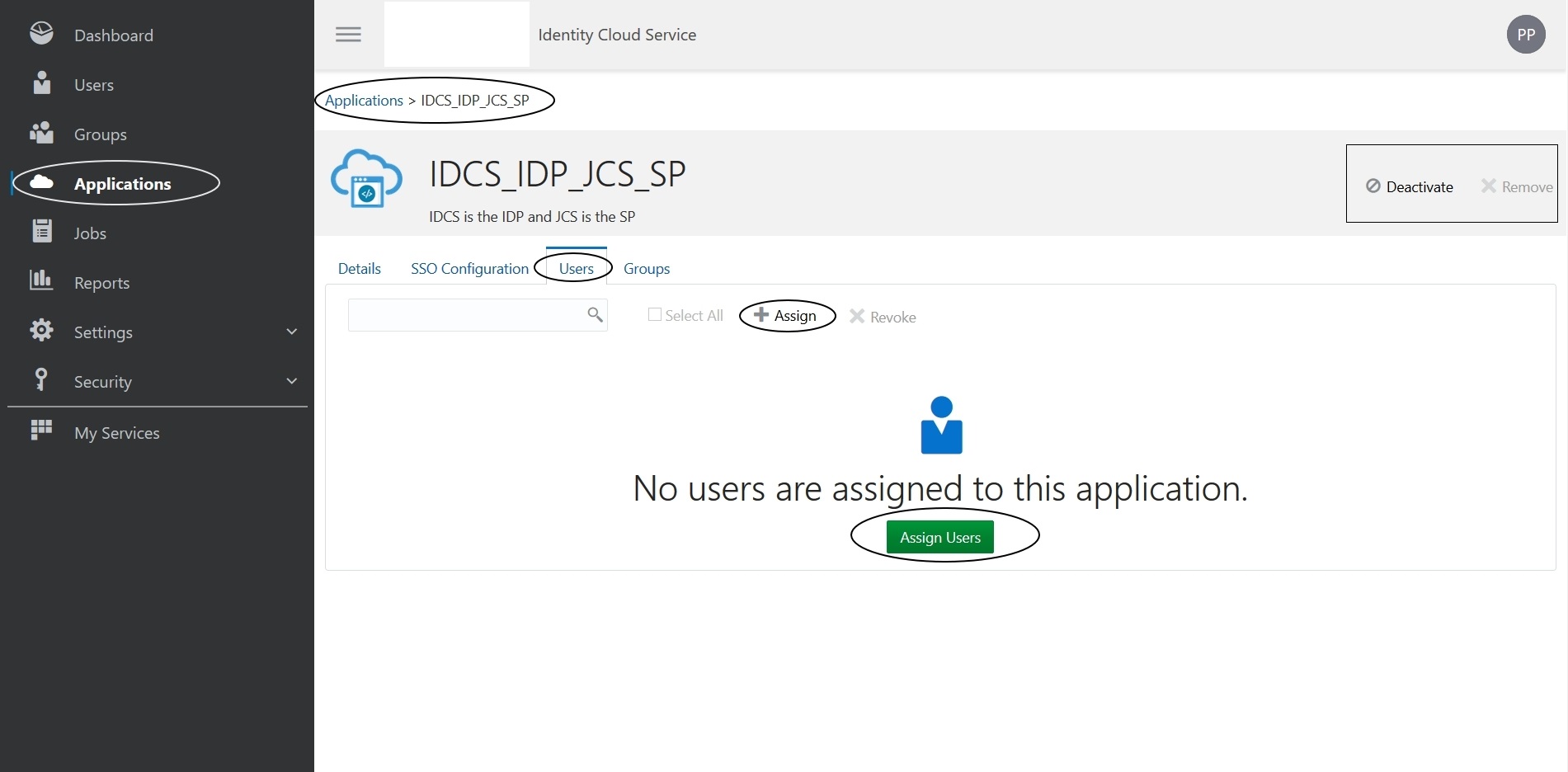
NOTE: Make sure you activate your application -> Select your application and click on the activate button on the right.
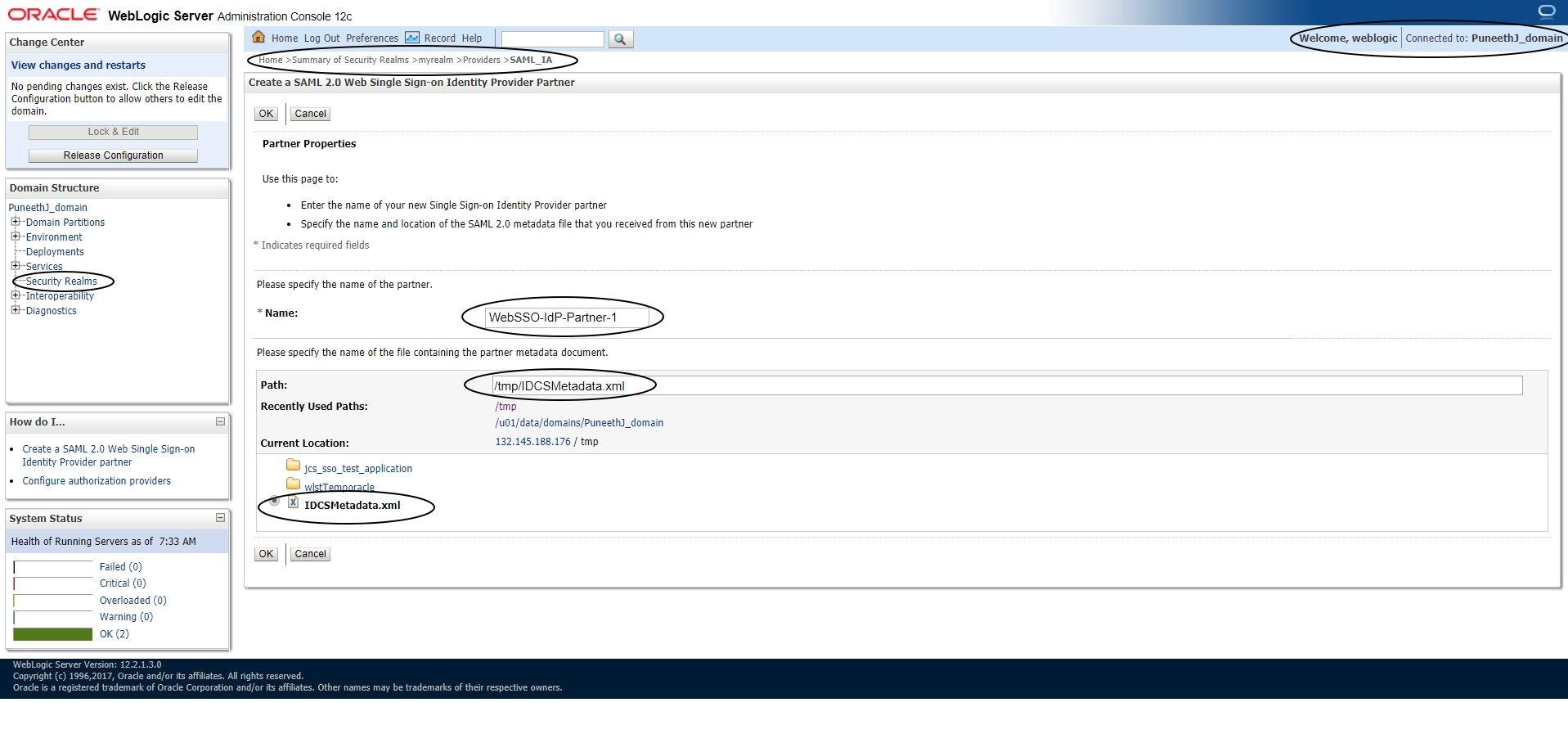
Let’s go back to JCS WLS console and create an IDP partner
Step 4a :
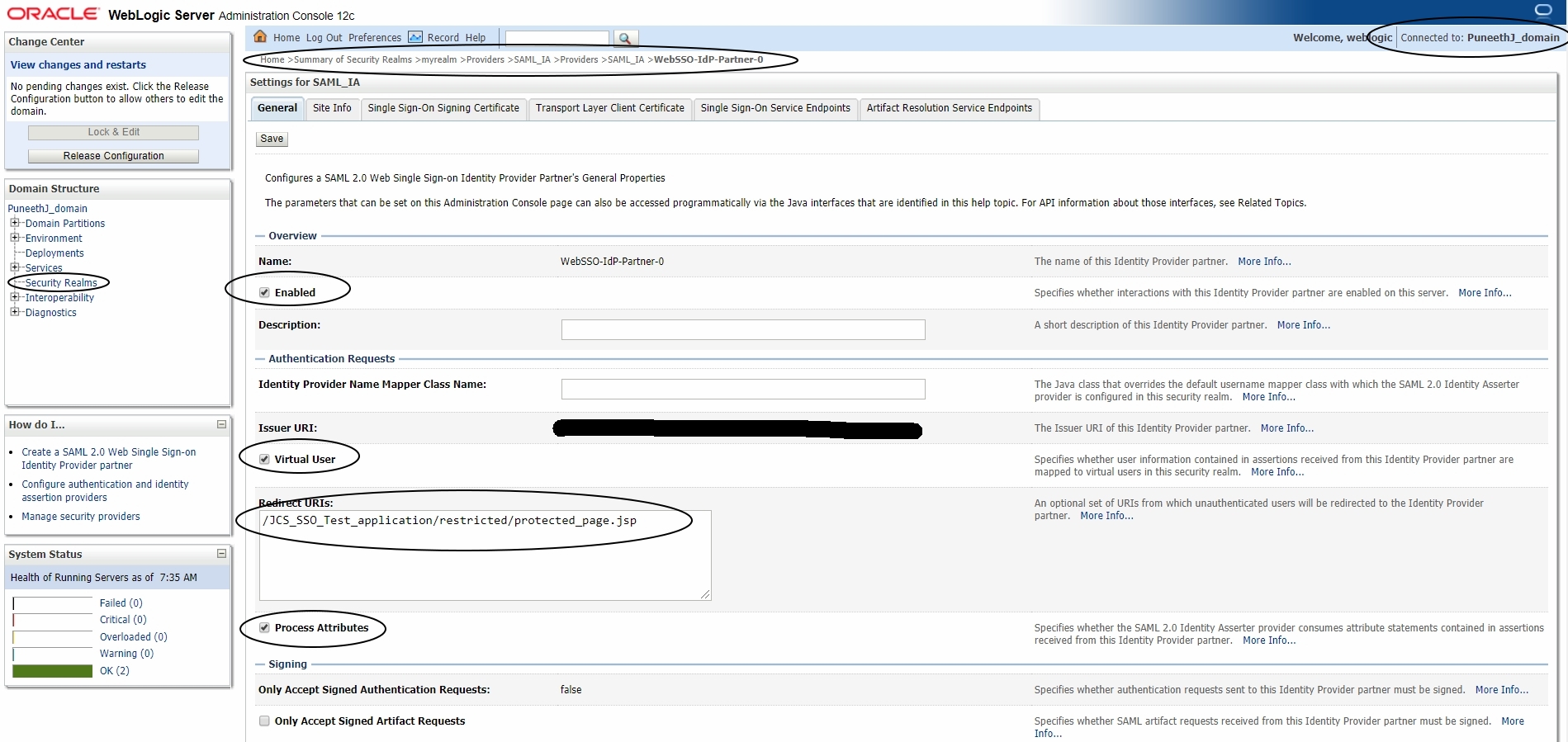
Navigate to the Identity Asserter you created earlier and create the partner :
Login to console -> Security Realms -> myrealm -> Providers -> Authentication ->SAML_IA -> Management -> New -> “New Web Single Sign-On Identity Provider Partner”
Select the IDP metadata and click OK.
Click on the newly created partner and enter the following info :
Enabled: Check
Virtual User: Check
Redirect URI: /JCS_SSO_Test_application/restricted/protected_page.jsp
// This should be the URI of protected page of your application.
Process Attributes: Check
Deploy the sample application provided at the start of this blog to the server where SSO is configured (This is the same server used for Step 2a configuration)
Restart all servers.
Now you can access the following URL to initiate an SP-Initiated SSO :
https://<publicly_accessible_hostname/IP>/JCS_SSO_Test_application/restricted/protected_page.jsp
You will get redirected to IDP login page for a challenge
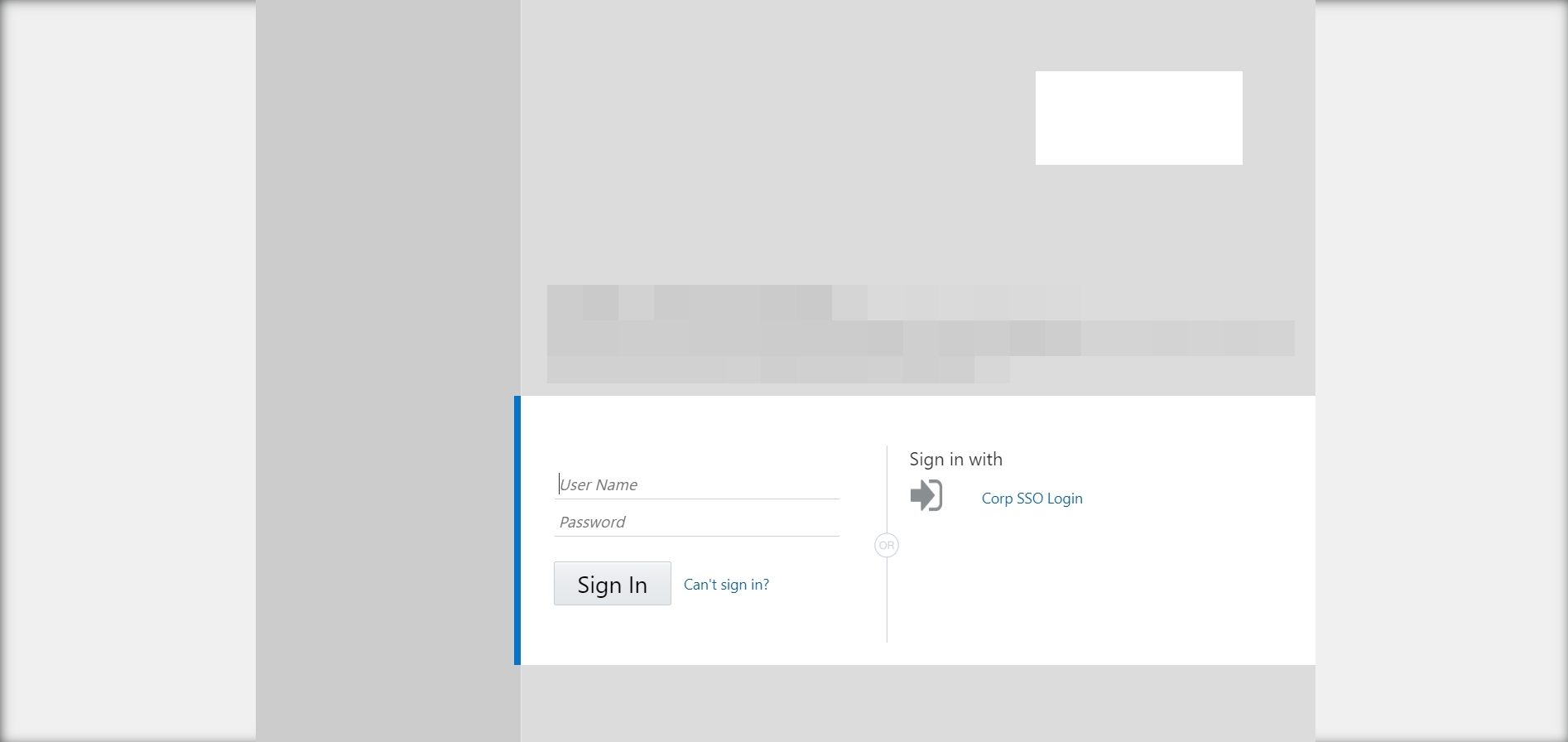
Enter the email ID and password of the user in IDCS.
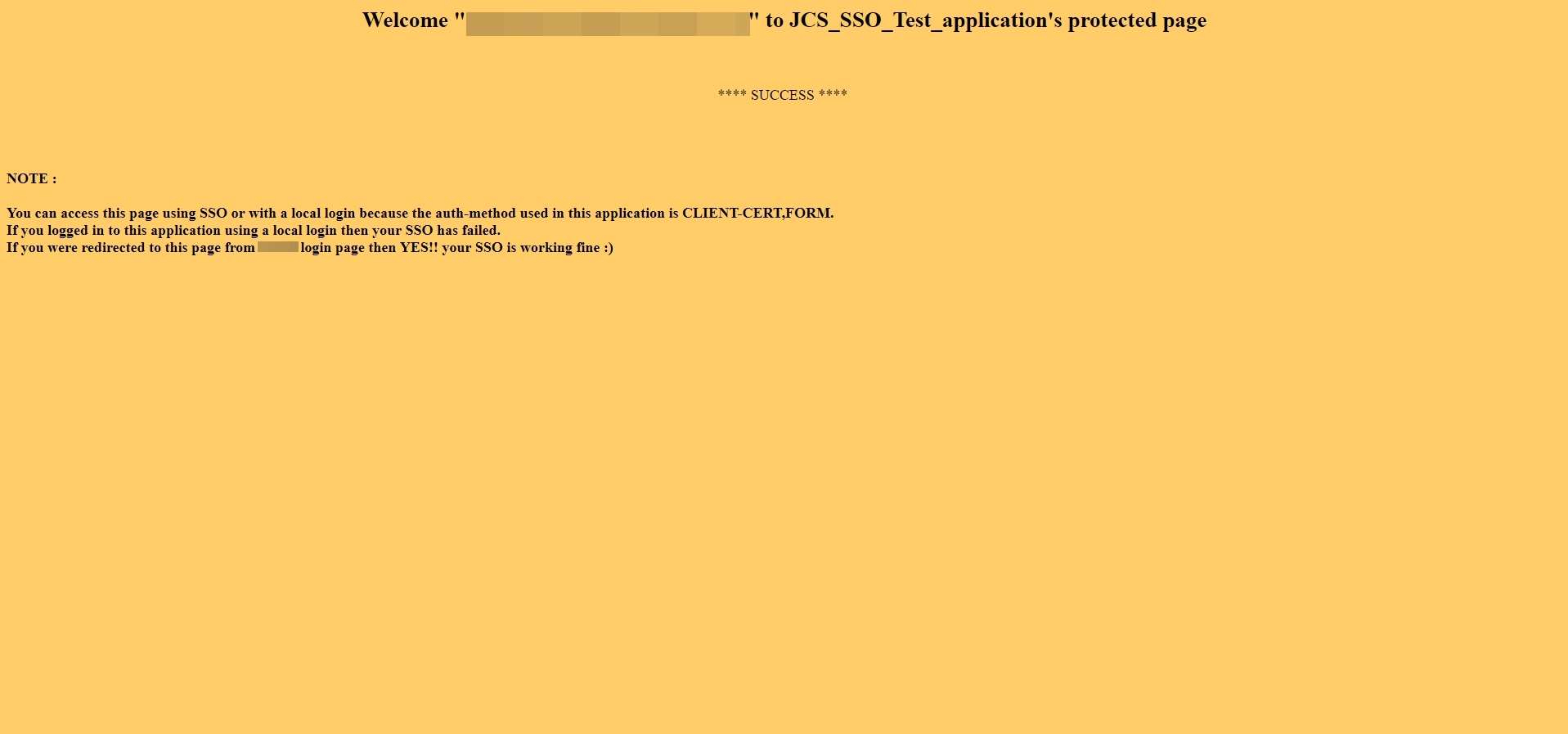
After you are authenticated in IDCS successfully, you will be redirected to the protected page of your application :