![]()
As you might already know, you can’t use the SAML Single Sign-On (SSO) configuration steps documented for Oracle Business Intelligence Enterprise Edition (OBIEE) 12c to configure SAML SSO for Oracle Analytics Server (OAS).
Various blogs describe the custom SSO solution approach suitable for OAS. For example, Single Sign-On Solutions for Oracle Analytics Server on On-Premises and on Oracle Cloud.
Specifically, the blog SAML 2.0 and Kerberos Single Sign-On Configuration for Oracle Analytics Server and Oracle Support Doc ID 2761678.1, covers the solution that uses Apache HTTP Server and Shibboleth-SP inside a docker (or podman) container. This blog follows a similar approach, using the Oracle HTTP Server (OHS) and Shibboleth-SP without a container and automates the SAML SSO configuration.
About the Solution
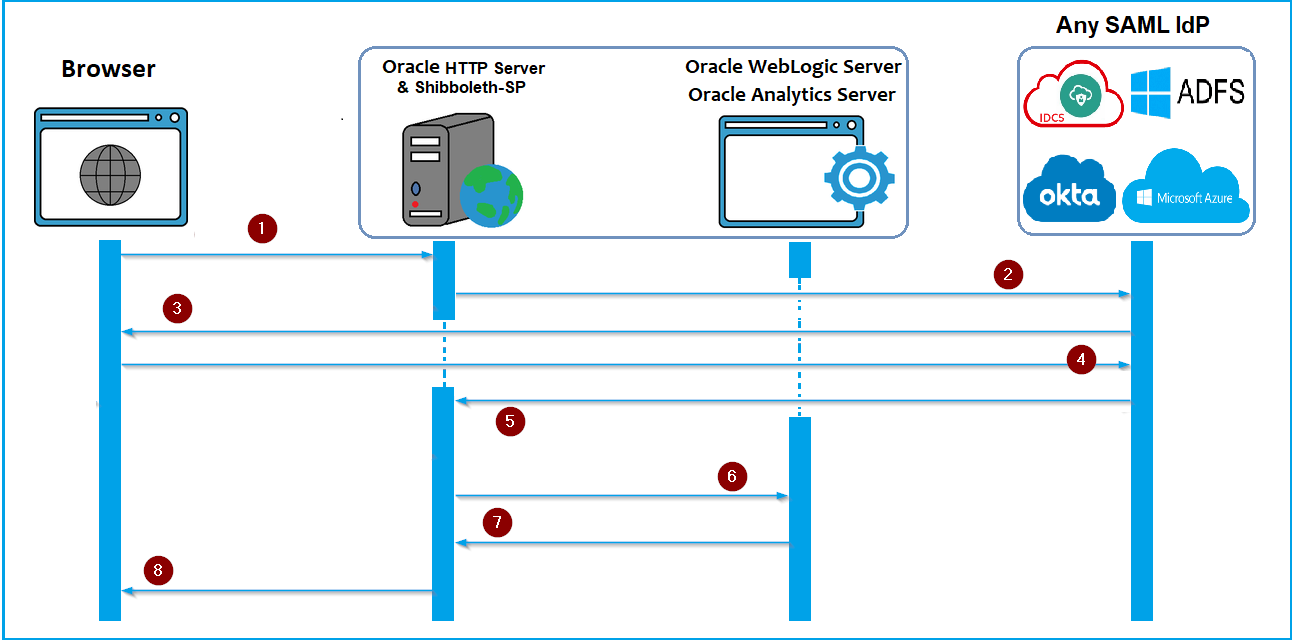
- Configure the OHS server as a proxy server (with the Shibboleth SAML Service Provider plugin) in front of OAS, and define the protected, public, and excluded resources.
- This is a hybrid solution. OHS with Shibboleth-SP to SAML IDP is a SAML SSO approach.
- OHS with Shibboleth-SP to OAS WebLogic Server is an HTTP Header-based SSO approach.
- Block the bi_serverN 9502 port for public access and allow only the OHS server.
- Install OHS on the same OAS server (recommended).
SAML Authentication Flow
Architecture
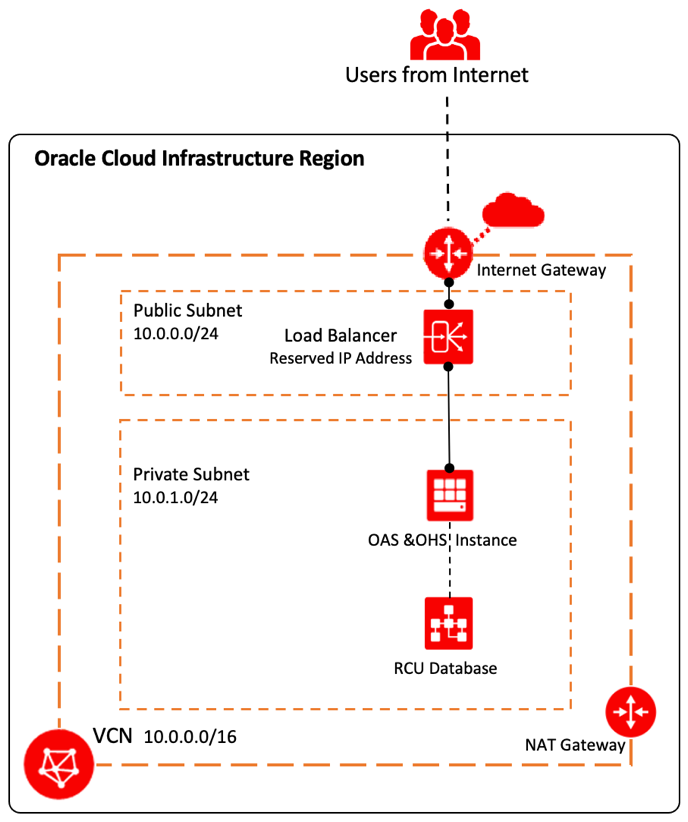
Architecture 1
Here’s an example of the environment on Oracle Cloud where OHS and OAS are on the same, single-node compute.
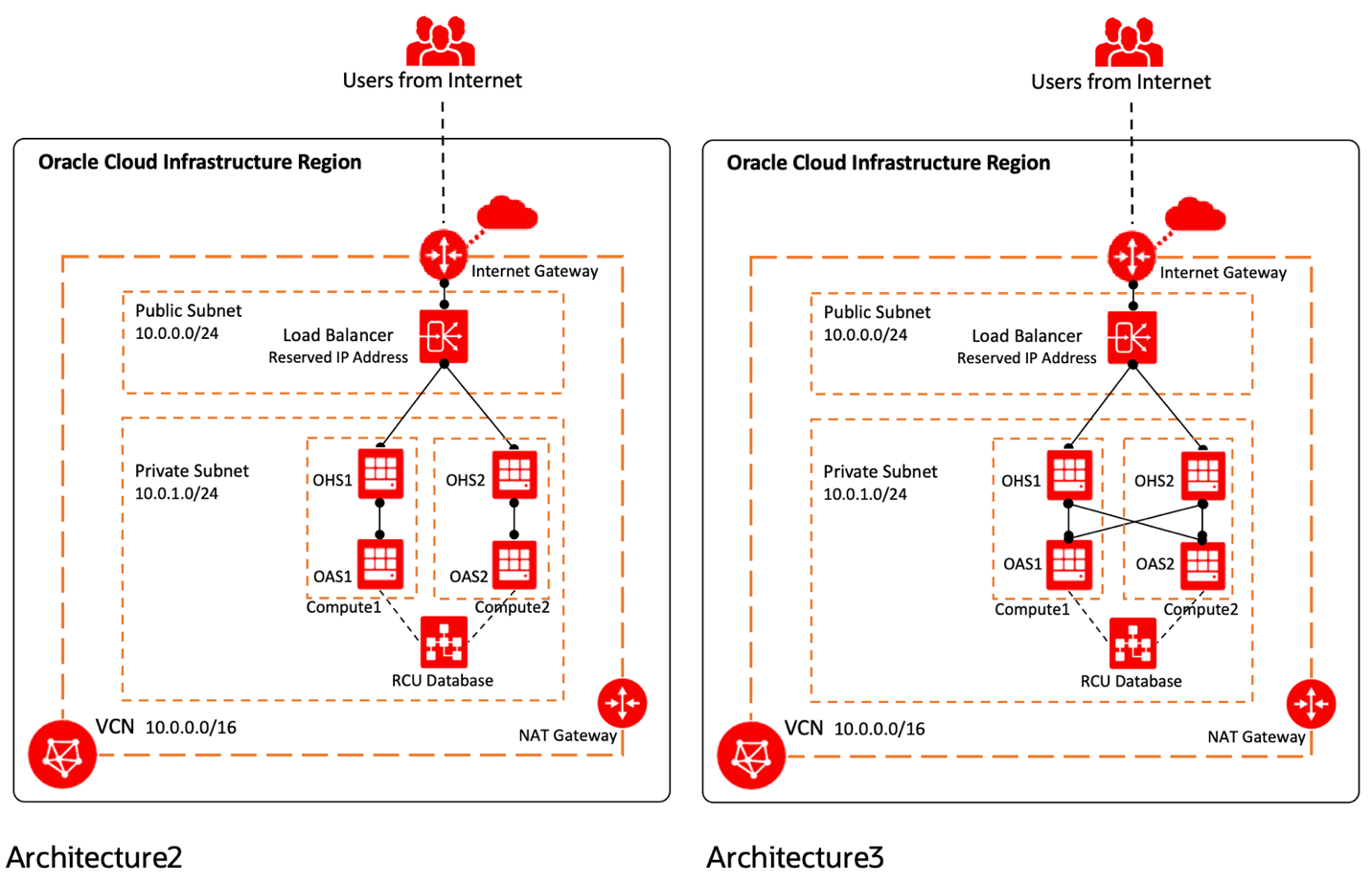
Architecture 2
Use Architecture 2 for the automation to configure SAML SSO for OAS. Here’s an example of the environment on Oracle Cloud where OHS and OAS are on the same computer. OHS1 is configured as the front end to OAS1, and OHS2 as the front end to OAS2.
The load balancer does the load balancing between OHS1 and OHS2.
Architecture 3
In Architecture 3, each OHS load balances between OAS1 and OAS 2. Furthermore, the load balancer load balances between OHS1 and OHS2.
Prerequisites
- Download the latest JDK 8 binaries: https://www.oracle.com/java/technologies/downloads/#java8
- Download the Oracle WebTier 12.2.1.4.0 for OHS: https://www.oracle.com/in/middleware/technologies/webtier-downloads.html
- Place the load balancer SSL Certificates (load balancer certificate, private key, CA Intermediate, and CA Root Certificates) in the automation script folders as described in the script README file.
- Place the SAML IDP Metadata XML file in the automation script folders as described in the script README file.
- Ensure non-root users, such as “Oracle”, have sudo privileges without a password prompt.
- Root access is required to install Shibboleth-SP.
- Ensure OHS has access to the internet (when the computer is on Oracle Cloud, NAT Gateway is required).
- Configure OAS with the same user store (LDAP) as the SAML IDP. Ensure that the same username and attribute sent by the SAML IDP in the NameID format exists in OAS. Set the User Store (LDAP) control flag to “SUFFICIENT“.
SAML Identity Provider
Supports any SAML 2.0 compatible identity provider (IDP).
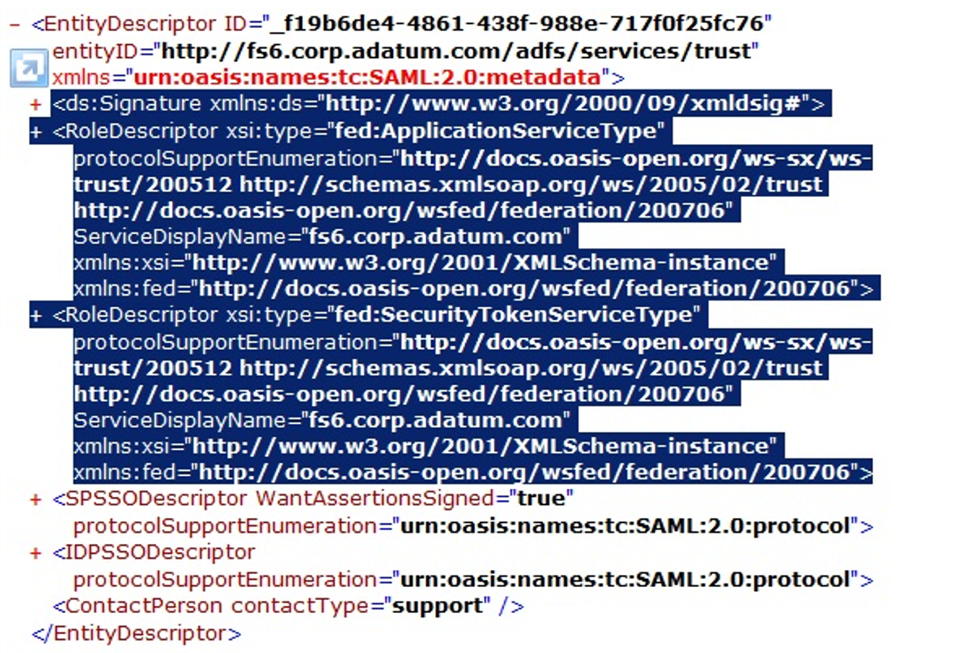
If the SAML IDP is Microsoft Active Directory Federation Services (ADFS), you must edit FederationMetadata.xml to remove the Signature, Role Descriptors, and SPSSODescriptor from the EntityDescriptor.
FederationMetadata.xml must include only IDPSSODescriptor in the EntityDescriptor.
Ensure that you delete the SPSSODescriptor.
Automation Scripts
The automation scripts perform the following tasks:- Script1 creates non-root users such as Oracle and its group with sudo privilege (run as root user).
- Script2 installs JDK and OHS (run as a non-root user, for example, Oracle).
- Script3 configures OHS with basic configuration (run as a non-root user, for example, Oracle).
- Script4 installs and configures Shibboleth-SP (run as root user).
- Script5 configures OHS with SSO configuration and performs SSL OffLoading (run as a non-root user, for example, Oracle).
- Script6 enables the WebLogic Plugin at the domain level, sets the SSO Logoff URL, and configures OAMIdentityAsserter (run as a non-root user, for example, Oracle).
NOTE: Read the respective README files and set up the content and variable values required to run the automation scripts.
Generate the Shibboleth SP Metadata XML File
Download the Shibboleth SP Metadata file using the URL:
https://{LoadBalancerDNS}/Shibboleth.sso/Metadata
Before configuring Shibboleth SP, you must place an IDP Metadata xml file along with the scripts. However, some identity providers can’t deliver their Metadata xml file until the service provider is configured with it. To overcome this requirement, you can provide the service provider’s metadata, such as EntityID, AssertionConsumerService, SingleLogoutService, signing, and encryption certificates, before configuring the service provider. Here are the details:
- EntityID: https://{LoadBalancerDNS}/analytics/shibboleth
- AssertionConsumerService: https://{LoadBalancerDNS}/Shibboleth.sso/SAML2/POST
- SingleLogoutService: https://{LoadBalancerDNS}/Shibboleth.sso/SLO/POST
- Signing or Encryption Certificate: Use the front-end certificate as the signing and encryption certificate. The front end can be either a load balancer or Oracle HTTP Server.
Configure OAS WebLogic Server for SSO
- Add “OAMIdentityAsserter” as a Provider and set the Control Flag as “REQUIRED“.
- Change the Control Flag of “Default Authenticator” to “SUFFICIENT“.
- Re-order the list of Authenticators to have OAMIdentityAsserter first, and then the rest to follow.
- Enable WebLogic Plugin at the domain level.
- Config the SSO Logout URL as /logout.html.
- Restart the OAS Services.
Automation script6 performs all these steps.
Automation script5, while configuring OHS for SSO, follows the protected, public, and excluded list of resources for OAS SSO as described in the OAS documentation: Updating the Protected, Public, and Excluded Resources for an Enterprise Deployment
Test the OAS URL’s
- https://ohs-or-LB-hostname.domain.com/dv
- https://ohs-or-LB-hostname.domain.com/analytics
- https://ohs-or-LB-hostname.domain.com/xmlpserver
- https://ohs-or-LB-hostname.domain.com/jbips (for smartview)
Extra Configuration
Extra configuration is needed for specific requirements and if you want to adopt Architecture 3.
1. If the OHS server performs load balancing between the clustered OAS nodes, modify the files accordingly after the automation scripts are run.
In httpd.conf:
- Remove Include “analytics.conf”
- Add below two lines
- Include “analyticsclustered.conf”
- Include “workers.conf”
Edit workers.conf to add the cluster OAS Servers as Balancer Members.
2. If the OAS server is SSL/TLS enabled, modify a few files to reflect the same.
In analytics.conf, modify:
- http protocol to https
- http port (for example, 9502) to https port (for example, 9503)
In ssl.conf, uncomment these four lines:
- #SSLProxyVerify none
- #SSLProxyCheckPeerName off
- #SSLProxyCheckPeerCN off
- #SSLProxyCheckPeerExpire off
3. If you have any custom deployments to the same WebLogic Server, such as custom skins and bicustom, and so on, add the Location tag for each custom resource at the end of analytics.conf or analyticsclustered.conf just before the last line accordingly.
For example:
<Location "/bicustom">
ProxyPass "http://<oas-server-hostname>:<oas-server-port>/bicustom"
ProxyPassReverse "/bicustom"
</Location>
Troubleshooting
If you see this proxy error, updated each ProxyPass in each Location tag in analytics.conf and restart the services.
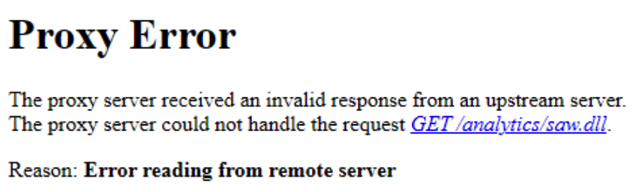
For example:
<Location "/xxxxxxxxxxxx">
ProxyPass "http://<oas-server-hostname>:<oas-server-port>/xxxxxxxxxxxx" connectiontimeout=600 timeout=600
ProxyPassReverse "/xxxxxxxxxxxx"
</Location>
Call to Action
This blog describes how to configure SAML SSO for OAS using OHS and Shibboleth SP through automation without the containers. If you have questions, post them in the Oracle Analytics Community and we’ll follow up with answers.
![]()