![]()
If your Oracle Business Intelligence Enterprise Edition (OBIEE) environment still uses the initialization block security model, you’ll have issues when you migrate to Oracle Analytics Server (OAS). Initialization blocks for authentication and authorization that set values for USER, ROLES, GROUP, GROUPS, are deprecated in OAS. See the Security section in Feature Availability in Oracle Analytics Server.
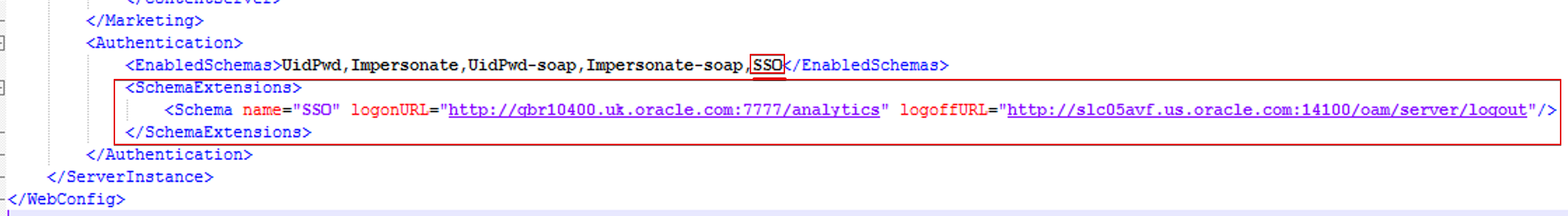
Similarly, the use of authenticationschemas.xml to define Single Sign-On (SSO) using a cookie or header is deprecated in OAS, so you can’t use this method for SSO.
This blog describes how to migrate your initialization block security model to the Fusion Middleware Security Model, which is suitable for OAS.
Solution
- Disable authentication and authorization initialization blocks in the RPD that set values for USER, ROLES, and GROUPS session variables.
Note: You can still use initialization blocks to set data-level security and other operations. - Since the users and groups used for authentication and authorization are in a database, configure either SQLAuthenticator or ReadOnlySQLAuthenticator in the WebLogic administration console.
- Configure OAMIdentityAsserter in the WebLogic administration console for SSO integrations.
- Restore the authenticationschemas.xml file to its original out-of-the-box state.
- Remove the EnabledSchema (that is SSO) and the SchemaExtensions section in the instanceconfig.xml file.
- Configure a supported SSO approach, such as Oracle Access Manager or SSO Custom Solutions (SAML and Kerberos SSO), as described in the OAS documentation.
Authentication Providers
Manage users, groups, and their memberships in an LDAP server. Move to LDAP as the authentication provider, such as Oracle Internet Directory, Microsoft Active Directory, and so on. Refer to the OAS documentation, Configure Oracle Analytics Server to Use Alternative Authentication Providers.
If you can’t move users, groups, and their memberships to LDAP and still use database tables, configure SQLAuthenticator or ReadOnlySQLAuthenticator.
Configure a data source for the database that contains users and groups in tables. Configure ReadOnlySQLAuthenticator and use the data source to configure it. Refer to the OAS documentation, Configure a Database as the Authentication Provider.
Enable Single Sign-On Authentication
Refer to the OAS documentation, Enable SSO Authentication.
Use Oracle Access Manager (OAM) for SSO authentication, see Configure SSO in an Oracle Access Manager Environment.
If you don’t have an OAM license but have another third-party SSO provider that supports HTTP header authentication, configure SSO using that provider.
Configure WebLogic Identity Asserter, such as OAMIdentityAsserter, to support third-party HTTP header providers in the WebLogic administration console. OAMIdentityAsserter supports the OAM_REMOTE_USER, SM_USER, and iv-user HTTP headers to receive the SSO provider-sent username in the HTTP header.
If your SSO provider can’t send the authenticated username in any of the given HTTP header names, you can develop and use your own custom identity asserter in WebLogic. See How to Develop a Custom Identity Assertion Provider.
If you want to move to SAML or Kerberos SSO authentication, explore Configure Custom SSO Environments in the OAS documentation.
Also, refer to this blog that describes various SSO approaches for OAS: Single Sign-On Solutions for Oracle Analytics Server on On-Premise and on Oracle Cloud.
Re-Order Authentication Providers
- OAMIdentityAsserter must be first in the list.
- Set the Control Flag of OAMIdentityAsserter to “REQUIRED“.
- Set the Other LDAP or ReadOnlySQLAuthenticator Control Flag to “SUFFICIENT“.
- Set the DefaultAuthenticator Control Flag to “SUFFICIENT“.
Manage Application Roles
In OBIEE 10g and 11g, you can use initialization blocks to set application roles and groups. Users who are members of groups attain the application roles. This approach doesn’t work in OBIEE 12c or OAS.
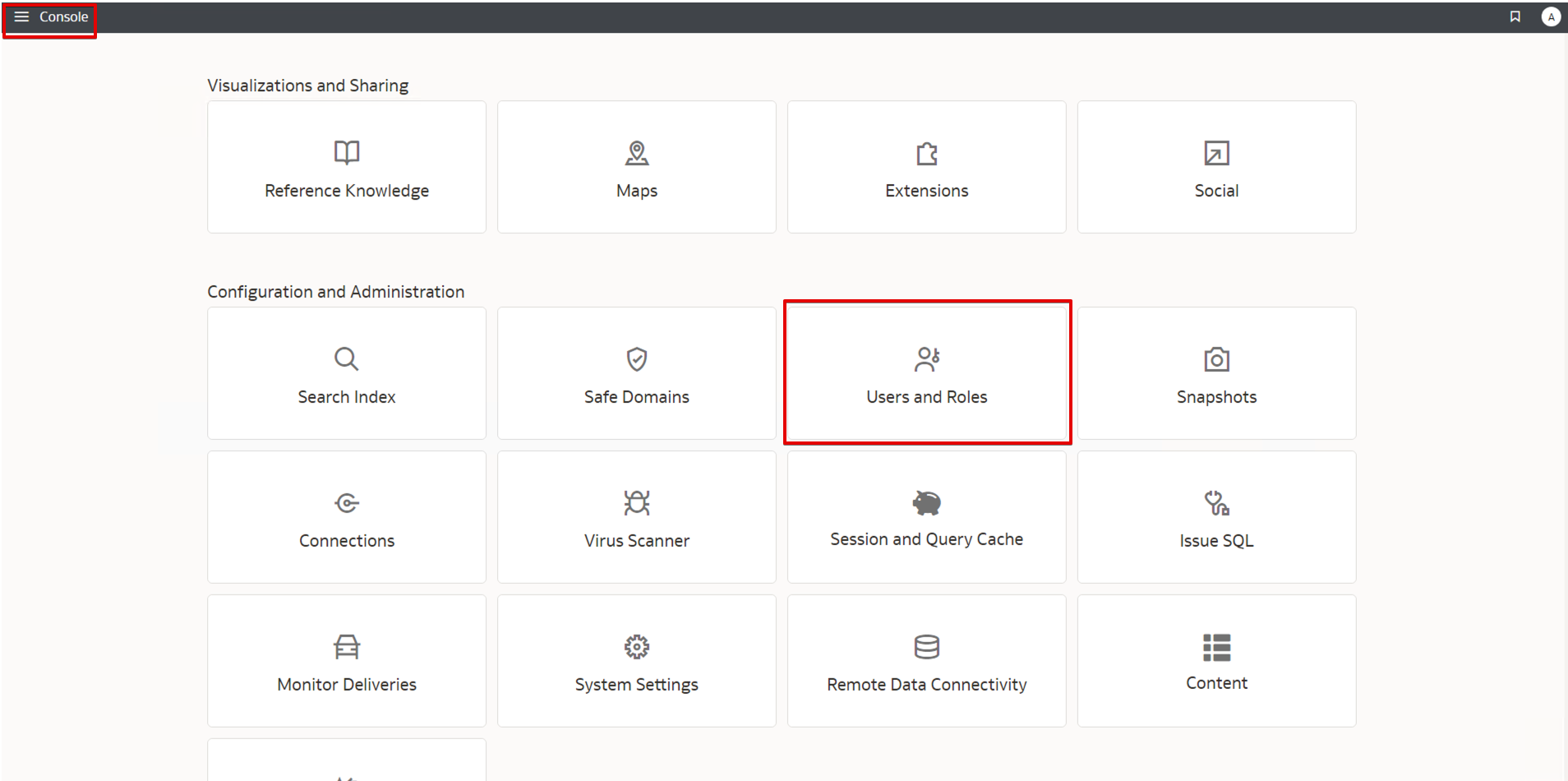
To assign a user (or group) to an application role in OAS, you must add the user (or group) directly to the application role. In OAS, administrators manage application role assignments in the Console (Users and Roles page). Refer to the OAS documentation, Manage Application Roles.
Call to Action
This blog describes how to migrate from the OBIEE initialization block security model to the Fusion Middleware Security Model.
If you have questions, post them in the Oracle Analytics Community and we’ll follow up with answers.
![]()
